public_configs = [ "${dir_pigweed}/pw_hdlc:default_config" ]
- deps = [
+ public_deps = [
"$dir_pw_rpc:server",
"$dir_pw_rpc/nanopb:echo_service",
"${chip_root}/examples/platform/efr32/pw_sys_io:pw_sys_io_efr32",
idf_component_register(SRCS chip.c chip.cpp
PRIV_REQUIRES freertos lwip bt mdns mbedtls)
-# Override some build specifications
-set_property(TARGET ${COMPONENT_LIB} PROPERTY CXX_STANDARD 14)
-set(CMAKE_BUILD_TYPE MinSizeRel)
-target_compile_options(${COMPONENT_LIB} PRIVATE "-DLWIP_IPV6_SCOPES=0" "-DCHIP_HAVE_CONFIG_H")
-
# Prepare initial args file (lacking compile flags)
# This will be saved as args.gn.in
set(chip_gn_args "import(\"//args.gni\")\n")
if(CONFIG_ENABLE_PW_RPC)
chip_gn_arg_append("chip_build_pw_rpc_lib" "true")
- chip_gn_arg_append("pw_log_BACKEND" "true")
- chip_gn_arg_append("pw_assert_BACKEND" "true")
- chip_gn_arg_append("pw_sys_io_BACKEND" "true")
- chip_gn_arg_append("dir_pw_third_party_nanopb" "true")
+ chip_gn_arg_append("pw_log_BACKEND" "\"//third_party/connectedhomeip/third_party/pigweed/repo/pw_log_basic\"")
+ chip_gn_arg_append("pw_assert_BACKEND" "\"//third_party/connectedhomeip/third_party/pigweed/repo/pw_assert_log\"")
+ chip_gn_arg_append("pw_sys_io_BACKEND" "\"//third_party/connectedhomeip/examples/platform/esp32/pw_sys_io:pw_sys_io_esp32\"")
+ chip_gn_arg_append("dir_pw_third_party_nanopb" "\"//third_party/connectedhomeip/third_party/nanopb/repo\"")
endif()
set(args_gn_input "${CMAKE_CURRENT_BINARY_DIR}/args.gn.in")
chip_gn
SOURCE_DIR ${CHIP_ROOT}
BINARY_DIR ${CMAKE_CURRENT_BINARY_DIR}
- CONFIGURE_COMMAND gn --root=${GN_ROOT_TARGET} gen --check --fail-on-unused-args ${CMAKE_CURRENT_BINARY_DIR}
+ CONFIGURE_COMMAND ${GN_EXECUTABLE} --root=${GN_ROOT_TARGET} gen --check --fail-on-unused-args ${CMAKE_CURRENT_BINARY_DIR}
BUILD_COMMAND ninja
INSTALL_COMMAND ""
BUILD_BYPRODUCTS ${CHIP_LIBRARIES}
"${CMAKE_CURRENT_BINARY_DIR}/gen/include"
)
-idf_component_get_property(bt_lib bt COMPONENT_LIB)
idf_component_get_property(esp32_mbedtls_lib esp32_mbedtls COMPONENT_LIB)
set(chip_libraries "-lCHIP")
list(APPEND chip_libraries "-lPwRpc")
endif()
+if(CONFIG_BT_ENABLED)
+ idf_component_get_property(bt_lib bt COMPONENT_LIB)
+ list(APPEND chip_libraries $<TARGET_FILE:${bt_lib}> -lbtdm_app)
+endif()
+
target_link_libraries(${COMPONENT_LIB} INTERFACE "-L${CMAKE_CURRENT_BINARY_DIR}/lib")
target_link_libraries(${COMPONENT_LIB} INTERFACE -Wl,--start-group
${chip_libraries}
- $<TARGET_FILE:${bt_lib}> -lbtdm_app
$<TARGET_FILE:mbedcrypto> $<TARGET_FILE:${esp32_mbedtls_lib}>
-Wl,--end-group)
# Make the component dependent on our CHIP build
-add_dependencies(${COMPONENT_LIB} chip_gn)
\ No newline at end of file
+add_dependencies(${COMPONENT_LIB} chip_gn)
may need to be shorter.
config BLE_FAST_ADVERTISING_INTERVAL_MIN
- int "Fast Advertising Interval"
- default 32
+ int "Fast Advertising Min Interval"
+ default 40
depends on ENABLE_CHIPOBLE
help
The minimum interval (in units of 0.625ms) at which the device will send BLE advertisements while
in fast advertising mode.
config BLE_FAST_ADVERTISING_INTERVAL_MAX
- int "Fast Advertising Interval"
- default 96
+ int "Fast Advertising Max Interval"
+ default 40
depends on ENABLE_CHIPOBLE
help
The maximum interval (in units of 0.625ms) at which the device will send BLE advertisements while
in fast advertising mode.
config BLE_SLOW_ADVERTISING_INTERVAL_MIN
- int "Slow Advertising Interval"
- default 240
+ int "Slow Advertising Min Interval"
+ default 800
depends on ENABLE_CHIPOBLE
help
The minimum interval (in units of 0.625ms) at which the device will send BLE advertisements while
in slow advertising mode.
config BLE_SLOW_ADVERTISING_INTERVAL_MAX
- int "Slow Advertising Interval"
- default 1920
+ int "Slow Advertising Max Interval"
+ default 800
depends on ENABLE_CHIPOBLE
help
The maximum interval (in units of 0.625ms) at which the device will send BLE advertisements while
+++ /dev/null
-# Configuring Thread network on a Linux machine
-
-You can use a Project CHIP controller such as
-[Python CHIP Controller](../../src/controller/python/README.md) to control
-Thread devices enabled for Project CHIP from a Linux host.
-
-For this purpose, you must equip the host with a Thread radio device, create a
-new Thread network, and ensure that packets addressed to devices within the
-network are routed through the radio device.
-
-<hr>
-
-- [Overview](#overview)
-- [Requirements](#requirements)
-- [Configuration](#configuration)
-- [Preparing OpenThread Radio Co-Processor device](#preparing-openthread-radio-co-processor)
-- [Configuring OpenThread Border Router](#configuring-openthread-border-router)
-- [Testing](#testing)
-
-<hr>
-
-## Overview
-
-The following figure shows the setup created as a result of configuring Thread
-network on a Linux machine.
-
-
-
-In this setup, the connectivity between Python CHIP Controller and Thread
-devices is ensured in the following way:
-
-- CHIP messages generated by the Project CHIP controller are routed through a
- virtual network interface **otbr0** to
- [OpenThread Border Router container](https://openthread.io/guides/border-router/docker)
- in Docker.
-- The OpenThread Border Router container uses a device with the
- [OpenThread Radio Co-Processor](https://openthread.io/platforms/co-processor)
- firmware to transmit Project CHIP messages to the Thread network.
-- CHIP-enabled Thread devices connected to the same Thread network receive and
- consume Project CHIP messages.
-
-<hr>
-
-## Requirements
-
-You need the following hardware and software for this configuration:
-
-- OpenThread Radio Co-Processor device (for example,
- [nRF52840 Dongle](https://www.nordicsemi.com/Software-and-tools/Development-Kits/nRF52840-Dongle),
- [Thunderboard Sense 2](https://www.silabs.com/development-tools/thunderboard/thunderboard-sense-two-kit))
-- Linux machine with Ubuntu v20.04 or later
-
-<hr>
-
-## Configuration
-
-The configuration process is composed of the following steps:
-
-- Preparing OpenThread Radio Co-Processor (RCP) device
-- Configuring OpenThread Border Router container in Docker
-
-### Configuring OpenThread Radio Co-Processor
-
-#### On Nordic Hardware
-
-> Read
-> [Configuring OpenThread Radio Co-processor on nRF52840 Dongle](openthread_rcp_nrf_dongle.md)
-> to learn how to configure Nordic Semiconductor's
-> [nRF52840 Dongle](https://www.nordicsemi.com/Software-and-tools/Development-Kits/nRF52840-Dongle)
-> as OpenThread Radio Co-Processor.
-
-#### On Silicon Labs Hardware
-
-> Please refer to this
-> [guide](https://www.silabs.com/documents/public/application-notes/an1256-using-sl-rcp-with-openthread-border-router.pdf)
-> to configure the OpenThread Radio Co-Processor on the Thunderboard sense 2.
-
-You can replace the nRF52840 Dongle or the Thunderboard with a variety of
-development boards from different vendors. If you are using a Raspberry Pi as
-your testing platform, you can execute this step on a more powerful Linux
-machine to shorten the firmware build time.
-
-### Configuring OpenThread Border Router
-
-To configure OpenThread Border Router, complete the following steps:
-
-1. Install Docker daemon:
-
- $ sudo apt update && sudo apt install docker.io
-
-2. Start the Docker daemon:
-
- $ sudo systemctl start docker
-
-3. Create an IPv6 network for the OpenThread Border Router container in Docker:
-
- $ sudo docker network create --ipv6 --subnet fd11:db8:1::/64 -o com.docker.network.bridge.name=otbr0 otbr
-
-4. Start the OpenThread Border Router container using the following command (in
- the last line, replace _/dev/ttyACM0_ with the device node name of the
- OpenThread Radio Co-processor):
-
- $ sudo docker run -it --rm --privileged --network otbr -p 8080:80 -e NAT64=0 -e DNS64=0 \
- --sysctl "net.ipv6.conf.all.disable_ipv6=0 net.ipv4.conf.all.forwarding=1 net.ipv6.conf.all.forwarding=1" \
- --volume /dev/ttyACM0:/dev/radio openthread/otbr --radio-url spinel+hdlc+uart:///dev/radio
-
-5. Open the `http://localhost:8080/` address in a web browser. If you are using
- a Raspberry Pi without a screen, but you have a different device in the same
- network, you can start a web browser on that device and use the address of
- the Raspberry Pi instead of `localhost`.
-6. Click **Form** in the menu to the left. The network forming creator window
- appears.
-7. Make sure that the On-Mesh Prefix is set to `fd11:22::`. This value is used
- later to configure the IPv6 packet routing.
-8. Click the **Form** button at the bottom of the window to form a new Thread
- network using the default settings.
-9. To ensure that packets addressed to devices in the Thread network are routed
- through the OpenThread Border Router container in Docker, run the following
- command with the On-Mesh Prefix that you set earlier:
-
- $ sudo ip -6 route add fd11:22::/64 dev otbr0 via fd11:db8:1::2
-
-<hr>
-
-## Testing
-
-After Open Thread Border Router has been configured, complete the steps
-described in the
-[Python CHIP Controller README](../../src/controller/python/README.md) to
-commission a Thread device into the network and control it using the Project
-CHIP protocol.
--- /dev/null
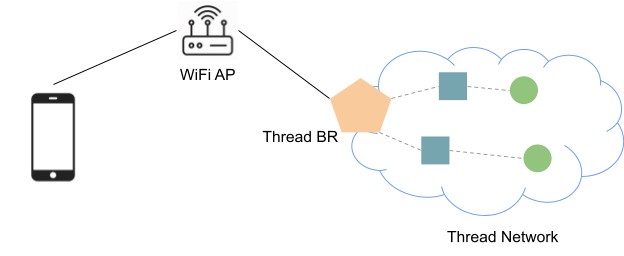
+# Setup OpenThread Border Router on Raspberry Pi
+
+
+
+A Thread Border Router connects a Thread network to other IP-based networks,
+such as Wi-Fi or Ethernet. A Thread network requires a Border Router to connect
+to other networks. A Thread Border Router minimally supports the following
+functions:
+
+- Bidirectional IP connectivity between Thread and Wi-Fi/Ethernet networks.
+- Bidirectional service discovery via mDNS (on Wi-Fi/Ethernet link) and SRP
+ (on Thread network).
+- Thread-over-infrastructure that merges Thread partitions over IP-based
+ links.
+- External Thread Commissioning (for example, a mobile phone) to authenticate
+ and join a Thread device to a Thread network.
+
+[OpenThread Border Router](https://openthread.io/guides/border-router) (OTBR)
+released by Google is an open-source implementation of the Thread Border Router.
+
+## Setup
+
+**Follow [this CodeLab](https://openthread.io/codelabs/openthread-border-router)
+to set up your OpenThread Border Router on a Raspberry Pi 3/4 device!**
+
+> Ubuntu and debian hosts are also supported!
+
+The CodeLab uses a Nordic nRF52840 DK as the Border Router RCP device.
+
+- See [openthread_rcp_nrf_dongle.md](./openthread_rcp_nrf_dongle.md) for using
+ nRF52840 dongle as a RCP device.
+- See this
+ [guide](https://www.silabs.com/documents/public/application-notes/an1256-using-sl-rcp-with-openthread-border-router.pdf)
+ for creating Silicon Labs RCP devices.
+++ /dev/null
-<?xml version="1.0" encoding="UTF-8" standalone="no"?>
-<!-- Generated by Microsoft Visio, SVG Export linux_thread_connectivity.svg Drawing -->
-
-<svg
- xmlns:dc="http://purl.org/dc/elements/1.1/"
- xmlns:cc="http://creativecommons.org/ns#"
- xmlns:rdf="http://www.w3.org/1999/02/22-rdf-syntax-ns#"
- xmlns:svg="http://www.w3.org/2000/svg"
- xmlns="http://www.w3.org/2000/svg"
- xmlns:xlink="http://www.w3.org/1999/xlink"
- xmlns:sodipodi="http://sodipodi.sourceforge.net/DTD/sodipodi-0.dtd"
- xmlns:inkscape="http://www.inkscape.org/namespaces/inkscape"
- width="4.23943in"
- height="5.23793in"
- viewBox="0 0 305.239 377.131"
- xml:space="preserve"
- color-interpolation-filters="sRGB"
- class="st10"
- version="1.1"
- id="svg105"
- sodipodi:docname="linux_thread_connectivity.svg"
- inkscape:version="0.92.5 (2060ec1f9f, 2020-04-08)"><metadata
- id="metadata109"><rdf:RDF><cc:Work
- rdf:about=""><dc:format>image/svg+xml</dc:format><dc:type
- rdf:resource="http://purl.org/dc/dcmitype/StillImage" /></cc:Work></rdf:RDF></metadata><sodipodi:namedview
- pagecolor="#ffffff"
- bordercolor="#666666"
- borderopacity="1"
- objecttolerance="10"
- gridtolerance="10"
- guidetolerance="10"
- inkscape:pageopacity="0"
- inkscape:pageshadow="2"
- inkscape:window-width="1920"
- inkscape:window-height="1163"
- id="namedview107"
- showgrid="false"
- inkscape:zoom="1.3274742"
- inkscape:cx="247.77132"
- inkscape:cy="268.19765"
- inkscape:window-x="0"
- inkscape:window-y="0"
- inkscape:window-maximized="1"
- inkscape:current-layer="g103" />
- <style
- type="text/css"
- id="style2">
- <![CDATA[
- .st1 {fill:#768692;stroke:none;stroke-width:1}
- .st2 {fill:#ffffff;font-family:Gotham Light;font-size:1.00001em}
- .st3 {fill:#d9e1e2;stroke:none;stroke-width:1}
- .st4 {fill:#333f48;font-family:Calibri;font-size:1.00001em}
- .st5 {font-size:1em}
- .st6 {marker-end:url(#mrkr13-19);stroke:#0033a0;stroke-linecap:butt;stroke-width:1}
- .st7 {fill:#0033a0;fill-opacity:1;stroke:#0033a0;stroke-opacity:1;stroke-width:0.28409090909091}
- .st8 {fill:#ffffff;stroke:none;stroke-linecap:butt;stroke-width:7.2}
- .st9 {fill:#0033a0;font-family:Calibri;font-size:1.00001em}
- .st10 {fill:none;fill-rule:evenodd;font-size:12px;overflow:visible;stroke-linecap:square;stroke-miterlimit:3}
- ]]>
- </style>
-
- <defs
- id="Markers">
- <g
- id="lend13">
- <path
- d="M 3 1 L 0 0 L 3 -1 L 3 1 "
- style="stroke:none"
- id="path4" />
- </g>
- <marker
- id="mrkr13-19"
- class="st7"
- refX="-10.56"
- orient="auto"
- markerUnits="strokeWidth"
- overflow="visible">
- <use
- xlink:href="#lend13"
- transform="scale(-3.52,-3.52) "
- id="use7" />
- </marker>
- </defs>
- <g
- id="g103">
- <title
- id="title11">Drawing</title>
- <g
- id="shape6-1"
- transform="translate(19,-143.724)">
- <title
- id="title13">Nordic Middle Grey</title>
- <desc
- id="desc15">Linux machine (Raspberry Pi or other)</desc>
- <rect
- x="0"
- y="162.724"
- width="267.239"
- height="214.407"
- class="st1"
- id="rect17" />
- <text
- x="20.52"
- y="177.52"
- class="st2"
- id="text19">Linux machine (Raspberry Pi or other)</text>
- </g>
- <g
- id="shape7-4"
- transform="translate(32.1469,-293.961)">
- <title
- id="title22">Nordic Light Grey</title>
- <desc
- id="desc24">Controller (Python CHIP Controller)</desc>
- <rect
- x="0"
- y="339.126"
- width="240.945"
- height="38.0053"
- class="st3"
- id="rect26" />
- <text
- x="121.36"
- y="354.53"
- class="st4"
- id="text30"
- style="font-style:normal;font-variant:normal;font-weight:normal;font-stretch:normal;font-size:12.00000191px;font-family:Calibri;-inkscape-font-specification:'Calibri, Normal';font-variant-ligatures:normal;font-variant-caps:normal;font-variant-numeric:normal;font-feature-settings:normal;text-align:center;writing-mode:lr-tb;text-anchor:middle;fill:#333f48"><tspan
- sodipodi:role="line"
- id="tspan111"
- x="121.36"
- y="354.53">Controller</tspan><tspan
- sodipodi:role="line"
- id="tspan113"
- x="121.36"
- y="369.53">(Python CHIP Controller)</tspan></text>
- </g>
- <g
- id="shape8-8"
- transform="translate(32.1469,-227.609)">
- <title
- id="title33">Nordic Light Grey.8</title>
- <desc
- id="desc35">Virtual network interface (otbr0)</desc>
- <rect
- x="0"
- y="339.126"
- width="240.945"
- height="38.0053"
- class="st3"
- id="rect37" />
- <text
- x="27.259998"
- y="361.73001"
- class="st4"
- id="text39"
- style="font-size:12.00012016px;font-family:Calibri;fill:#333f48">Virtual network interface (otbr0)</text>
- </g>
- <g
- id="shape9-11"
- transform="translate(32.1469,-160.732)">
- <title
- id="title42">Nordic Light Grey.9</title>
- <desc
- id="desc44">OpenThread Border Router Docker image</desc>
- <rect
- x="0"
- y="339.126"
- width="240.945"
- height="38.0053"
- class="st3"
- id="rect46" />
- <text
- x="123.24924"
- y="345.42401"
- class="st4"
- id="text48"
- style="font-style:normal;font-variant:normal;font-weight:normal;font-stretch:normal;font-size:12.00000165px;font-family:Calibri;-inkscape-font-specification:'Calibri, Normal';font-variant-ligatures:normal;font-variant-caps:normal;font-variant-numeric:normal;font-feature-settings:normal;text-align:center;writing-mode:lr;text-anchor:middle;fill:#333f48;stroke-width:0.97102857;"
- transform="scale(0.97102858,1.0298358)"><tspan
- sodipodi:role="line"
- id="tspan115"
- x="123.24924"
- y="345.42401">OpenThread Border Router</tspan><tspan
- sodipodi:role="line"
- id="tspan117"
- x="123.24924"
- y="359.98901">Docker container</tspan></text>
- </g>
- <g
- id="shape10-14"
- transform="translate(145.533,-293.961)">
- <title
- id="title51">Dynamic connector</title>
- <path
- d="M7.09 377.13 L7.09 394.92"
- class="st6"
- id="path53" />
- </g>
- <g
- id="shape11-20"
- transform="translate(145.533,-227.609)">
- <title
- id="title56">Dynamic connector.11</title>
- <path
- d="M7.09 377.13 L7.09 395.44"
- class="st6"
- id="path58" />
- </g>
- <g
- id="shape12-25"
- transform="translate(32.1469,-85.0367)">
- <title
- id="title61">Nordic Light Grey.12</title>
- <desc
- id="desc63">OpenThread Radio Co-Processor (on nRF52840 Dongle or other)</desc>
- <rect
- x="0"
- y="339.126"
- width="240.945"
- height="38.0053"
- class="st3"
- id="rect65" />
- <text
- x="23.459999"
- y="354.53"
- class="st4"
- id="text69"
- style="font-size:12.00012016px;font-family:Calibri;fill:#333f48">OpenThread Radio Co-Processor <tspan
- x="26.869999"
- dy="14.400145"
- class="st5"
- id="tspan67"
- style="font-size:12.00012016px">(nRF52840 Dongle/Thunderboard/etc...)</tspan></text>
- </g>
- <g
- id="shape13-29"
- transform="translate(32.1469,-19)">
- <title
- id="title72">Nordic Light Grey.13</title>
- <desc
- id="desc74">Thread device enabled for Project CHIP</desc>
- <rect
- x="0"
- y="339.126"
- width="240.945"
- height="38.0053"
- class="st3"
- id="rect76" />
- <text
- x="121.13"
- y="354.23001"
- class="st4"
- id="text78"
- style="font-style:normal;font-variant:normal;font-weight:normal;font-stretch:normal;font-size:12.00000191px;font-family:Calibri;-inkscape-font-specification:'Calibri, Normal';font-variant-ligatures:normal;font-variant-caps:normal;font-variant-numeric:normal;font-feature-settings:normal;text-align:center;writing-mode:lr-tb;text-anchor:middle;fill:#333f48"><tspan
- sodipodi:role="line"
- id="tspan119"
- x="121.13"
- y="354.23001">Thread device enabled</tspan><tspan
- sodipodi:role="line"
- id="tspan121"
- x="121.13"
- y="369.23001">for Project CHIP</tspan></text>
- </g>
- <g
- id="shape14-32"
- transform="translate(145.533,-85.0367)">
- <title
- id="title81">Dynamic connector.14</title>
- <desc
- id="desc83">Thread</desc>
- <path
- d="M7.09 377.13 L7.09 394.6"
- class="st6"
- id="path85" />
- <rect
- x="18.4487"
- y="383.947"
- width="34.3597"
- height="14.4001"
- class="st8"
- id="rect87" />
- <text
- x="18.45"
- y="394.75"
- class="st9"
- id="text89">Thread</text>
- </g>
- <g
- id="shape15-39"
- transform="translate(145.533,-160.732)">
- <title
- id="title92">Dynamic connector.15</title>
- <desc
- id="desc94">USB</desc>
- <path
- d="M7.09 377.13 L7.09 404.26"
- class="st6"
- id="path96" />
- <rect
- x="17.4499"
- y="397.28"
- width="19.7405"
- height="14.4001"
- class="st8"
- id="rect98" />
- <text
- x="17.45"
- y="408.08"
- class="st9"
- id="text100">USB</text>
- </g>
- </g>
-</svg>
\ No newline at end of file
} // namespace ColorControl
-namespace ContentLaunch {
-
-void DispatchServerCommand(app::Command * command, CommandId commandId, EndpointId endpointId, TLV::TLVReader & dataTlv)
-{
- {
- switch (commandId)
- {
- case ZCL_LAUNCH_CONTENT_COMMAND_ID: {
- // TODO(#5098) We should pass the Command Object and EndpointId to the cluster callbacks.
- emberAfContentLaunchClusterLaunchContentCallback();
- break;
- }
- case ZCL_LAUNCH_URL_COMMAND_ID: {
- // TODO(#5098) We should pass the Command Object and EndpointId to the cluster callbacks.
- emberAfContentLaunchClusterLaunchURLCallback();
- break;
- }
- default: {
- // Unrecognized command ID, error status will apply.
- // TODO: Encode response for command not found
- ChipLogError(Zcl, "Unknown command %" PRIx16 " for cluster %" PRIx16, commandId, ZCL_CONTENT_LAUNCH_CLUSTER_ID);
- break;
- }
- }
- }
-}
-
-} // namespace ContentLaunch
-
namespace DoorLock {
void DispatchServerCommand(app::Command * command, CommandId commandId, EndpointId endpointId, TLV::TLVReader & dataTlv)
} // namespace LowPower
-namespace MediaPlayback {
-
-void DispatchServerCommand(app::Command * command, CommandId commandId, EndpointId endpointId, TLV::TLVReader & dataTlv)
-{
- {
- switch (commandId)
- {
- case ZCL_FAST_FORWARD_REQUEST_COMMAND_ID: {
- // TODO(#5098) We should pass the Command Object and EndpointId to the cluster callbacks.
- emberAfMediaPlaybackClusterFastForwardRequestCallback();
- break;
- }
- case ZCL_NEXT_REQUEST_COMMAND_ID: {
- // TODO(#5098) We should pass the Command Object and EndpointId to the cluster callbacks.
- emberAfMediaPlaybackClusterNextRequestCallback();
- break;
- }
- case ZCL_PAUSE_REQUEST_COMMAND_ID: {
- // TODO(#5098) We should pass the Command Object and EndpointId to the cluster callbacks.
- emberAfMediaPlaybackClusterPauseRequestCallback();
- break;
- }
- case ZCL_PLAY_REQUEST_COMMAND_ID: {
- // TODO(#5098) We should pass the Command Object and EndpointId to the cluster callbacks.
- emberAfMediaPlaybackClusterPlayRequestCallback();
- break;
- }
- case ZCL_PREVIOUS_REQUEST_COMMAND_ID: {
- // TODO(#5098) We should pass the Command Object and EndpointId to the cluster callbacks.
- emberAfMediaPlaybackClusterPreviousRequestCallback();
- break;
- }
- case ZCL_REWIND_REQUEST_COMMAND_ID: {
- // TODO(#5098) We should pass the Command Object and EndpointId to the cluster callbacks.
- emberAfMediaPlaybackClusterRewindRequestCallback();
- break;
- }
- case ZCL_SKIP_BACKWARD_REQUEST_COMMAND_ID: {
- // TODO(#5098) We should pass the Command Object and EndpointId to the cluster callbacks.
- emberAfMediaPlaybackClusterSkipBackwardRequestCallback();
- break;
- }
- case ZCL_SKIP_FORWARD_REQUEST_COMMAND_ID: {
- // TODO(#5098) We should pass the Command Object and EndpointId to the cluster callbacks.
- emberAfMediaPlaybackClusterSkipForwardRequestCallback();
- break;
- }
- case ZCL_START_OVER_REQUEST_COMMAND_ID: {
- // TODO(#5098) We should pass the Command Object and EndpointId to the cluster callbacks.
- emberAfMediaPlaybackClusterStartOverRequestCallback();
- break;
- }
- case ZCL_STOP_REQUEST_COMMAND_ID: {
- // TODO(#5098) We should pass the Command Object and EndpointId to the cluster callbacks.
- emberAfMediaPlaybackClusterStopRequestCallback();
- break;
- }
- default: {
- // Unrecognized command ID, error status will apply.
- // TODO: Encode response for command not found
- ChipLogError(Zcl, "Unknown command %" PRIx16 " for cluster %" PRIx16, commandId, ZCL_MEDIA_PLAYBACK_CLUSTER_ID);
- break;
- }
- }
- }
-}
-
-} // namespace MediaPlayback
-
namespace NetworkCommissioning {
void DispatchServerCommand(app::Command * command, CommandId commandId, EndpointId endpointId, TLV::TLVReader & dataTlv)
case ZCL_COLOR_CONTROL_CLUSTER_ID:
clusters::ColorControl::DispatchServerCommand(apCommandObj, aCommandId, aEndPointId, aReader);
break;
- case ZCL_CONTENT_LAUNCH_CLUSTER_ID:
- clusters::ContentLaunch::DispatchServerCommand(apCommandObj, aCommandId, aEndPointId, aReader);
- break;
case ZCL_DOOR_LOCK_CLUSTER_ID:
clusters::DoorLock::DispatchServerCommand(apCommandObj, aCommandId, aEndPointId, aReader);
break;
case ZCL_LOW_POWER_CLUSTER_ID:
clusters::LowPower::DispatchServerCommand(apCommandObj, aCommandId, aEndPointId, aReader);
break;
- case ZCL_MEDIA_PLAYBACK_CLUSTER_ID:
- clusters::MediaPlayback::DispatchServerCommand(apCommandObj, aCommandId, aEndPointId, aReader);
- break;
case ZCL_NETWORK_COMMISSIONING_CLUSTER_ID:
clusters::NetworkCommissioning::DispatchServerCommand(apCommandObj, aCommandId, aEndPointId, aReader);
break;
// Server attributes
#define ZCL_MAX_DURATION_ATTRIBUTE_ID (0x0000)
+// Attribute ids for cluster: Media Playback
+
+// Client attributes
+
+// Server attributes
+#define ZCL_CURRENT_STATE_ATTRIBUTE_ID (0x0000)
+
// Attribute ids for cluster: Low Power
// Client attributes
// Server attributes
+// Attribute ids for cluster: Content Launch
+
+// Client attributes
+
+// Server attributes
+
// Attribute ids for cluster: Application Basic
// Client attributes
// Server attributes
-// Attribute ids for cluster: Media Playback
-
-// Client attributes
-
-// Server attributes
-#define ZCL_CURRENT_STATE_ATTRIBUTE_ID (0x0000)
-
-// Attribute ids for cluster: Content Launch
-
-// Client attributes
-
-// Server attributes
-
// Attribute ids for cluster: Group Key Management
// Client attributes
EmberAfStatus emberAfBasicClusterServerCommandParse(EmberAfClusterCommand * cmd);
EmberAfStatus emberAfBindingClusterServerCommandParse(EmberAfClusterCommand * cmd);
EmberAfStatus emberAfColorControlClusterServerCommandParse(EmberAfClusterCommand * cmd);
-EmberAfStatus emberAfContentLaunchClusterServerCommandParse(EmberAfClusterCommand * cmd);
EmberAfStatus emberAfDoorLockClusterServerCommandParse(EmberAfClusterCommand * cmd);
EmberAfStatus emberAfGeneralCommissioningClusterServerCommandParse(EmberAfClusterCommand * cmd);
EmberAfStatus emberAfGroupKeyManagementClusterServerCommandParse(EmberAfClusterCommand * cmd);
EmberAfStatus emberAfIdentifyClusterServerCommandParse(EmberAfClusterCommand * cmd);
EmberAfStatus emberAfLevelControlClusterServerCommandParse(EmberAfClusterCommand * cmd);
EmberAfStatus emberAfLowPowerClusterServerCommandParse(EmberAfClusterCommand * cmd);
-EmberAfStatus emberAfMediaPlaybackClusterServerCommandParse(EmberAfClusterCommand * cmd);
EmberAfStatus emberAfNetworkCommissioningClusterServerCommandParse(EmberAfClusterCommand * cmd);
EmberAfStatus emberAfOnOffClusterServerCommandParse(EmberAfClusterCommand * cmd);
EmberAfStatus emberAfScenesClusterServerCommandParse(EmberAfClusterCommand * cmd);
case ZCL_COLOR_CONTROL_CLUSTER_ID:
result = emberAfColorControlClusterServerCommandParse(cmd);
break;
- case ZCL_CONTENT_LAUNCH_CLUSTER_ID:
- result = emberAfContentLaunchClusterServerCommandParse(cmd);
- break;
case ZCL_DOOR_LOCK_CLUSTER_ID:
result = emberAfDoorLockClusterServerCommandParse(cmd);
break;
case ZCL_LOW_POWER_CLUSTER_ID:
result = emberAfLowPowerClusterServerCommandParse(cmd);
break;
- case ZCL_MEDIA_PLAYBACK_CLUSTER_ID:
- result = emberAfMediaPlaybackClusterServerCommandParse(cmd);
- break;
case ZCL_NETWORK_COMMISSIONING_CLUSTER_ID:
result = emberAfNetworkCommissioningClusterServerCommandParse(cmd);
break;
}
return status(wasHandled, true, cmd->mfgSpecific);
}
-EmberAfStatus emberAfContentLaunchClusterServerCommandParse(EmberAfClusterCommand * cmd)
-{
- bool wasHandled = false;
-
- if (!cmd->mfgSpecific)
- {
- switch (cmd->commandId)
- {
- case ZCL_LAUNCH_CONTENT_COMMAND_ID: {
- wasHandled = emberAfContentLaunchClusterLaunchContentCallback();
- break;
- }
- case ZCL_LAUNCH_URL_COMMAND_ID: {
- wasHandled = emberAfContentLaunchClusterLaunchURLCallback();
- break;
- }
- default: {
- // Unrecognized command ID, error status will apply.
- break;
- }
- }
- }
- return status(wasHandled, true, cmd->mfgSpecific);
-}
EmberAfStatus emberAfDoorLockClusterServerCommandParse(EmberAfClusterCommand * cmd)
{
bool wasHandled = false;
}
return status(wasHandled, true, cmd->mfgSpecific);
}
-EmberAfStatus emberAfMediaPlaybackClusterServerCommandParse(EmberAfClusterCommand * cmd)
-{
- bool wasHandled = false;
-
- if (!cmd->mfgSpecific)
- {
- switch (cmd->commandId)
- {
- case ZCL_FAST_FORWARD_REQUEST_COMMAND_ID: {
- wasHandled = emberAfMediaPlaybackClusterFastForwardRequestCallback();
- break;
- }
- case ZCL_NEXT_REQUEST_COMMAND_ID: {
- wasHandled = emberAfMediaPlaybackClusterNextRequestCallback();
- break;
- }
- case ZCL_PAUSE_REQUEST_COMMAND_ID: {
- wasHandled = emberAfMediaPlaybackClusterPauseRequestCallback();
- break;
- }
- case ZCL_PLAY_REQUEST_COMMAND_ID: {
- wasHandled = emberAfMediaPlaybackClusterPlayRequestCallback();
- break;
- }
- case ZCL_PREVIOUS_REQUEST_COMMAND_ID: {
- wasHandled = emberAfMediaPlaybackClusterPreviousRequestCallback();
- break;
- }
- case ZCL_REWIND_REQUEST_COMMAND_ID: {
- wasHandled = emberAfMediaPlaybackClusterRewindRequestCallback();
- break;
- }
- case ZCL_SKIP_BACKWARD_REQUEST_COMMAND_ID: {
- wasHandled = emberAfMediaPlaybackClusterSkipBackwardRequestCallback();
- break;
- }
- case ZCL_SKIP_FORWARD_REQUEST_COMMAND_ID: {
- wasHandled = emberAfMediaPlaybackClusterSkipForwardRequestCallback();
- break;
- }
- case ZCL_START_OVER_REQUEST_COMMAND_ID: {
- wasHandled = emberAfMediaPlaybackClusterStartOverRequestCallback();
- break;
- }
- case ZCL_STOP_REQUEST_COMMAND_ID: {
- wasHandled = emberAfMediaPlaybackClusterStopRequestCallback();
- break;
- }
- default: {
- // Unrecognized command ID, error status will apply.
- break;
- }
- }
- }
- return status(wasHandled, true, cmd->mfgSpecific);
-}
EmberAfStatus emberAfNetworkCommissioningClusterServerCommandParse(EmberAfClusterCommand * cmd)
{
bool wasHandled = false;
case ZCL_COLOR_CONTROL_CLUSTER_ID:
emberAfColorControlClusterInitCallback(endpoint);
break;
- case ZCL_CONTENT_LAUNCH_CLUSTER_ID:
- emberAfContentLaunchClusterInitCallback(endpoint);
- break;
case ZCL_DOOR_LOCK_CLUSTER_ID:
emberAfDoorLockClusterInitCallback(endpoint);
break;
case ZCL_LOW_POWER_CLUSTER_ID:
emberAfLowPowerClusterInitCallback(endpoint);
break;
- case ZCL_MEDIA_PLAYBACK_CLUSTER_ID:
- emberAfMediaPlaybackClusterInitCallback(endpoint);
- break;
case ZCL_NETWORK_COMMISSIONING_CLUSTER_ID:
emberAfNetworkCommissioningClusterInitCallback(endpoint);
break;
// To prevent warning
(void) endpoint;
}
-void __attribute__((weak)) emberAfContentLaunchClusterInitCallback(EndpointId endpoint)
-{
- // To prevent warning
- (void) endpoint;
-}
void __attribute__((weak)) emberAfDoorLockClusterInitCallback(EndpointId endpoint)
{
// To prevent warning
// To prevent warning
(void) endpoint;
}
-void __attribute__((weak)) emberAfMediaPlaybackClusterInitCallback(EndpointId endpoint)
-{
- // To prevent warning
- (void) endpoint;
-}
void __attribute__((weak)) emberAfNetworkCommissioningClusterInitCallback(EndpointId endpoint)
{
// To prevent warning
*/
void emberAfColorControlClusterInitCallback(chip::EndpointId endpoint);
-/** @brief Content Launch Cluster Init
- *
- * Cluster Init
- *
- * @param endpoint Endpoint that is being initialized
- */
-void emberAfContentLaunchClusterInitCallback(chip::EndpointId endpoint);
-
/** @brief Door Lock Cluster Init
*
* Cluster Init
*/
void emberAfLowPowerClusterInitCallback(chip::EndpointId endpoint);
-/** @brief Media Playback Cluster Init
- *
- * Cluster Init
- *
- * @param endpoint Endpoint that is being initialized
- */
-void emberAfMediaPlaybackClusterInitCallback(chip::EndpointId endpoint);
-
/** @brief Network Commissioning Cluster Init
*
* Cluster Init
void emberAfColorControlClusterServerTickCallback(chip::EndpointId endpoint);
//
-// Content Launch Cluster server
-//
-
-/** @brief Content Launch Cluster Server Init
- *
- * Server Init
- *
- * @param endpoint Endpoint that is being initialized
- */
-void emberAfContentLaunchClusterServerInitCallback(chip::EndpointId endpoint);
-
-/** @brief Content Launch Cluster Server Attribute Changed
- *
- * Server Attribute Changed
- *
- * @param endpoint Endpoint that is being initialized
- * @param attributeId Attribute that changed
- */
-void emberAfContentLaunchClusterServerAttributeChangedCallback(chip::EndpointId endpoint, chip::AttributeId attributeId);
-
-/** @brief Content Launch Cluster Server Manufacturer Specific Attribute Changed
- *
- * Server Manufacturer Specific Attribute Changed
- *
- * @param endpoint Endpoint that is being initialized
- * @param attributeId Attribute that changed
- * @param manufacturerCode Manufacturer Code of the attribute that changed
- */
-void emberAfContentLaunchClusterServerManufacturerSpecificAttributeChangedCallback(chip::EndpointId endpoint,
- chip::AttributeId attributeId,
- uint16_t manufacturerCode);
-
-/** @brief Content Launch Cluster Server Message Sent
- *
- * Server Message Sent
- *
- * @param type The type of message sent
- * @param indexOrDestination The destination or address to which the message was sent
- * @param apsFrame The APS frame for the message
- * @param msgLen The length of the message
- * @param message The message that was sent
- * @param status The status of the sent message
- */
-void emberAfContentLaunchClusterServerMessageSentCallback(EmberOutgoingMessageType type, uint64_t indexOrDestination,
- EmberApsFrame * apsFrame, uint16_t msgLen, uint8_t * message,
- EmberStatus status);
-
-/** @brief Content Launch Cluster Server Pre Attribute Changed
- *
- * server Pre Attribute Changed
- *
- * @param endpoint Endpoint that is being initialized
- * @param attributeId Attribute to be changed
- * @param attributeType Attribute type
- * @param size Attribute size
- * @param value Attribute value
- */
-EmberAfStatus emberAfContentLaunchClusterServerPreAttributeChangedCallback(chip::EndpointId endpoint, chip::AttributeId attributeId,
- EmberAfAttributeType attributeType, uint8_t size,
- uint8_t * value);
-
-/** @brief Content Launch Cluster Server Tick
- *
- * server Tick
- *
- * @param endpoint Endpoint that is being served
- */
-void emberAfContentLaunchClusterServerTickCallback(chip::EndpointId endpoint);
-
-//
// Door Lock Cluster server
//
void emberAfLowPowerClusterServerTickCallback(chip::EndpointId endpoint);
//
-// Media Playback Cluster server
-//
-
-/** @brief Media Playback Cluster Server Init
- *
- * Server Init
- *
- * @param endpoint Endpoint that is being initialized
- */
-void emberAfMediaPlaybackClusterServerInitCallback(chip::EndpointId endpoint);
-
-/** @brief Media Playback Cluster Server Attribute Changed
- *
- * Server Attribute Changed
- *
- * @param endpoint Endpoint that is being initialized
- * @param attributeId Attribute that changed
- */
-void emberAfMediaPlaybackClusterServerAttributeChangedCallback(chip::EndpointId endpoint, chip::AttributeId attributeId);
-
-/** @brief Media Playback Cluster Server Manufacturer Specific Attribute Changed
- *
- * Server Manufacturer Specific Attribute Changed
- *
- * @param endpoint Endpoint that is being initialized
- * @param attributeId Attribute that changed
- * @param manufacturerCode Manufacturer Code of the attribute that changed
- */
-void emberAfMediaPlaybackClusterServerManufacturerSpecificAttributeChangedCallback(chip::EndpointId endpoint,
- chip::AttributeId attributeId,
- uint16_t manufacturerCode);
-
-/** @brief Media Playback Cluster Server Message Sent
- *
- * Server Message Sent
- *
- * @param type The type of message sent
- * @param indexOrDestination The destination or address to which the message was sent
- * @param apsFrame The APS frame for the message
- * @param msgLen The length of the message
- * @param message The message that was sent
- * @param status The status of the sent message
- */
-void emberAfMediaPlaybackClusterServerMessageSentCallback(EmberOutgoingMessageType type, uint64_t indexOrDestination,
- EmberApsFrame * apsFrame, uint16_t msgLen, uint8_t * message,
- EmberStatus status);
-
-/** @brief Media Playback Cluster Server Pre Attribute Changed
- *
- * server Pre Attribute Changed
- *
- * @param endpoint Endpoint that is being initialized
- * @param attributeId Attribute to be changed
- * @param attributeType Attribute type
- * @param size Attribute size
- * @param value Attribute value
- */
-EmberAfStatus emberAfMediaPlaybackClusterServerPreAttributeChangedCallback(chip::EndpointId endpoint, chip::AttributeId attributeId,
- EmberAfAttributeType attributeType, uint8_t size,
- uint8_t * value);
-
-/** @brief Media Playback Cluster Server Tick
- *
- * server Tick
- *
- * @param endpoint Endpoint that is being served
- */
-void emberAfMediaPlaybackClusterServerTickCallback(chip::EndpointId endpoint);
-
-//
// Network Commissioning Cluster server
//
bool emberAfColorControlClusterStopMoveStepCallback(uint8_t optionsMask, uint8_t optionsOverride);
/**
- * @brief Content Launch Cluster LaunchContent Command callback
- */
-
-bool emberAfContentLaunchClusterLaunchContentCallback();
-
-/**
- * @brief Content Launch Cluster LaunchURL Command callback
- */
-
-bool emberAfContentLaunchClusterLaunchURLCallback();
-
-/**
* @brief Door Lock Cluster ClearAllPins Command callback
*/
bool emberAfLowPowerClusterSleepCallback();
/**
- * @brief Media Playback Cluster FastForwardRequest Command callback
- */
-
-bool emberAfMediaPlaybackClusterFastForwardRequestCallback();
-
-/**
- * @brief Media Playback Cluster NextRequest Command callback
- */
-
-bool emberAfMediaPlaybackClusterNextRequestCallback();
-
-/**
- * @brief Media Playback Cluster PauseRequest Command callback
- */
-
-bool emberAfMediaPlaybackClusterPauseRequestCallback();
-
-/**
- * @brief Media Playback Cluster PlayRequest Command callback
- */
-
-bool emberAfMediaPlaybackClusterPlayRequestCallback();
-
-/**
- * @brief Media Playback Cluster PreviousRequest Command callback
- */
-
-bool emberAfMediaPlaybackClusterPreviousRequestCallback();
-
-/**
- * @brief Media Playback Cluster RewindRequest Command callback
- */
-
-bool emberAfMediaPlaybackClusterRewindRequestCallback();
-
-/**
- * @brief Media Playback Cluster SkipBackwardRequest Command callback
- */
-
-bool emberAfMediaPlaybackClusterSkipBackwardRequestCallback();
-
-/**
- * @brief Media Playback Cluster SkipForwardRequest Command callback
- */
-
-bool emberAfMediaPlaybackClusterSkipForwardRequestCallback();
-
-/**
- * @brief Media Playback Cluster StartOverRequest Command callback
- */
-
-bool emberAfMediaPlaybackClusterStartOverRequestCallback();
-
-/**
- * @brief Media Playback Cluster StopRequest Command callback
- */
-
-bool emberAfMediaPlaybackClusterStopRequestCallback();
-
-/**
* @brief Network Commissioning Cluster AddThreadNetwork Command callback
* @param operationalDataset
* @param breadcrumb
\
ZCL_SQUAWK_COMMAND_ID, "u", squawkInfo);
+/** @brief Command description for PlayRequest
+ *
+ * Command: PlayRequest
+ */
+#define emberAfFillCommandMedia \
+ PlaybackClusterPlayRequest() emberAfFillExternalBuffer(mask, \
+ \
+ ZCL_PLAY_REQUEST_COMMAND_ID, "", );
+
+/** @brief Command description for PauseRequest
+ *
+ * Command: PauseRequest
+ */
+#define emberAfFillCommandMedia \
+ PlaybackClusterPauseRequest() emberAfFillExternalBuffer(mask, \
+ \
+ ZCL_PAUSE_REQUEST_COMMAND_ID, "", );
+
+/** @brief Command description for StopRequest
+ *
+ * Command: StopRequest
+ */
+#define emberAfFillCommandMedia \
+ PlaybackClusterStopRequest() emberAfFillExternalBuffer(mask, \
+ \
+ ZCL_STOP_REQUEST_COMMAND_ID, "", );
+
+/** @brief Command description for StartOverRequest
+ *
+ * Command: StartOverRequest
+ */
+#define emberAfFillCommandMedia \
+ PlaybackClusterStartOverRequest() emberAfFillExternalBuffer(mask, \
+ \
+ ZCL_START_OVER_REQUEST_COMMAND_ID, "", );
+
+/** @brief Command description for PreviousRequest
+ *
+ * Command: PreviousRequest
+ */
+#define emberAfFillCommandMedia \
+ PlaybackClusterPreviousRequest() emberAfFillExternalBuffer(mask, \
+ \
+ ZCL_PREVIOUS_REQUEST_COMMAND_ID, "", );
+
+/** @brief Command description for NextRequest
+ *
+ * Command: NextRequest
+ */
+#define emberAfFillCommandMedia \
+ PlaybackClusterNextRequest() emberAfFillExternalBuffer(mask, \
+ \
+ ZCL_NEXT_REQUEST_COMMAND_ID, "", );
+
+/** @brief Command description for RewindRequest
+ *
+ * Command: RewindRequest
+ */
+#define emberAfFillCommandMedia \
+ PlaybackClusterRewindRequest() emberAfFillExternalBuffer(mask, \
+ \
+ ZCL_REWIND_REQUEST_COMMAND_ID, "", );
+
+/** @brief Command description for FastForwardRequest
+ *
+ * Command: FastForwardRequest
+ */
+#define emberAfFillCommandMedia \
+ PlaybackClusterFastForwardRequest() emberAfFillExternalBuffer(mask, \
+ \
+ ZCL_FAST_FORWARD_REQUEST_COMMAND_ID, "", );
+
+/** @brief Command description for SkipForwardRequest
+ *
+ * Command: SkipForwardRequest
+ */
+#define emberAfFillCommandMedia \
+ PlaybackClusterSkipForwardRequest() emberAfFillExternalBuffer(mask, \
+ \
+ ZCL_SKIP_FORWARD_REQUEST_COMMAND_ID, "", );
+
+/** @brief Command description for SkipBackwardRequest
+ *
+ * Command: SkipBackwardRequest
+ */
+#define emberAfFillCommandMedia \
+ PlaybackClusterSkipBackwardRequest() emberAfFillExternalBuffer(mask, \
+ \
+ ZCL_SKIP_BACKWARD_REQUEST_COMMAND_ID, "", );
+
/** @brief Command description for Sleep
*
* Command: Sleep
\
ZCL_SLEEP_COMMAND_ID, "", );
+/** @brief Command description for LaunchContent
+ *
+ * Command: LaunchContent
+ * @param contentLaunchStatus ContentLaunchStatus
+ */
+#define emberAfFillCommandContent \
+ LaunchClusterLaunchContent(contentLaunchStatus) \
+ emberAfFillExternalBuffer(mask, \
+ \
+ ZCL_LAUNCH_CONTENT_COMMAND_ID, "u", contentLaunchStatus);
+
+/** @brief Command description for LaunchURL
+ *
+ * Command: LaunchURL
+ * @param contentLaunchStatus ContentLaunchStatus
+ */
+#define emberAfFillCommandContent \
+ LaunchClusterLaunchURL(contentLaunchStatus) emberAfFillExternalBuffer(mask, \
+ \
+ ZCL_LAUNCH_URL_COMMAND_ID, "u", contentLaunchStatus);
+
/** @brief Command description for MatchProtocolAddress
*
* Command: MatchProtocolAddress
\
ZCL_UNBIND_COMMAND_ID, "uuuu", nodeId, groupId, endpointId, clusterId);
-/** @brief Command description for PlayRequest
- *
- * Command: PlayRequest
- */
-#define emberAfFillCommandMedia \
- PlaybackClusterPlayRequest() emberAfFillExternalBuffer(mask, \
- \
- ZCL_PLAY_REQUEST_COMMAND_ID, "", );
-
-/** @brief Command description for PauseRequest
- *
- * Command: PauseRequest
- */
-#define emberAfFillCommandMedia \
- PlaybackClusterPauseRequest() emberAfFillExternalBuffer(mask, \
- \
- ZCL_PAUSE_REQUEST_COMMAND_ID, "", );
-
-/** @brief Command description for StopRequest
- *
- * Command: StopRequest
- */
-#define emberAfFillCommandMedia \
- PlaybackClusterStopRequest() emberAfFillExternalBuffer(mask, \
- \
- ZCL_STOP_REQUEST_COMMAND_ID, "", );
-
-/** @brief Command description for StartOverRequest
- *
- * Command: StartOverRequest
- */
-#define emberAfFillCommandMedia \
- PlaybackClusterStartOverRequest() emberAfFillExternalBuffer(mask, \
- \
- ZCL_START_OVER_REQUEST_COMMAND_ID, "", );
-
-/** @brief Command description for PreviousRequest
- *
- * Command: PreviousRequest
- */
-#define emberAfFillCommandMedia \
- PlaybackClusterPreviousRequest() emberAfFillExternalBuffer(mask, \
- \
- ZCL_PREVIOUS_REQUEST_COMMAND_ID, "", );
-
-/** @brief Command description for NextRequest
- *
- * Command: NextRequest
- */
-#define emberAfFillCommandMedia \
- PlaybackClusterNextRequest() emberAfFillExternalBuffer(mask, \
- \
- ZCL_NEXT_REQUEST_COMMAND_ID, "", );
-
-/** @brief Command description for RewindRequest
- *
- * Command: RewindRequest
- */
-#define emberAfFillCommandMedia \
- PlaybackClusterRewindRequest() emberAfFillExternalBuffer(mask, \
- \
- ZCL_REWIND_REQUEST_COMMAND_ID, "", );
-
-/** @brief Command description for FastForwardRequest
- *
- * Command: FastForwardRequest
- */
-#define emberAfFillCommandMedia \
- PlaybackClusterFastForwardRequest() emberAfFillExternalBuffer(mask, \
- \
- ZCL_FAST_FORWARD_REQUEST_COMMAND_ID, "", );
-
-/** @brief Command description for SkipForwardRequest
- *
- * Command: SkipForwardRequest
- */
-#define emberAfFillCommandMedia \
- PlaybackClusterSkipForwardRequest() emberAfFillExternalBuffer(mask, \
- \
- ZCL_SKIP_FORWARD_REQUEST_COMMAND_ID, "", );
-
-/** @brief Command description for SkipBackwardRequest
- *
- * Command: SkipBackwardRequest
- */
-#define emberAfFillCommandMedia \
- PlaybackClusterSkipBackwardRequest() emberAfFillExternalBuffer(mask, \
- \
- ZCL_SKIP_BACKWARD_REQUEST_COMMAND_ID, "", );
-
-/** @brief Command description for LaunchContent
- *
- * Command: LaunchContent
- * @param contentLaunchStatus ContentLaunchStatus
- */
-#define emberAfFillCommandContent \
- LaunchClusterLaunchContent(contentLaunchStatus) \
- emberAfFillExternalBuffer(mask, \
- \
- ZCL_LAUNCH_CONTENT_COMMAND_ID, "u", contentLaunchStatus);
-
-/** @brief Command description for LaunchURL
- *
- * Command: LaunchURL
- * @param contentLaunchStatus ContentLaunchStatus
- */
-#define emberAfFillCommandContent \
- LaunchClusterLaunchURL(contentLaunchStatus) emberAfFillExternalBuffer(mask, \
- \
- ZCL_LAUNCH_URL_COMMAND_ID, "u", contentLaunchStatus);
-
/** @brief Command description for CommandOne
*
* Command: CommandOne
// Definitions for cluster: IAS WD
#define ZCL_IAS_WD_CLUSTER_ID (0x0502)
+// Definitions for cluster: Media Playback
+#define ZCL_MEDIA_PLAYBACK_CLUSTER_ID (0x0506)
+
// Definitions for cluster: Low Power
#define ZCL_LOW_POWER_CLUSTER_ID (0x0508)
+// Definitions for cluster: Content Launch
+#define ZCL_CONTENT_LAUNCH_CLUSTER_ID (0x050A)
+
// Definitions for cluster: Application Basic
#define ZCL_APPLICATION_BASIC_CLUSTER_ID (0x050D)
// Definitions for cluster: Binding
#define ZCL_BINDING_CLUSTER_ID (0xF000)
-// Definitions for cluster: Media Playback
-#define ZCL_MEDIA_PLAYBACK_CLUSTER_ID (0xF001)
-
-// Definitions for cluster: Content Launch
-#define ZCL_CONTENT_LAUNCH_CLUSTER_ID (0xF002)
-
// Definitions for cluster: Group Key Management
#define ZCL_GROUP_KEY_MANAGEMENT_CLUSTER_ID (0xF004)
#define ZCL_START_WARNING_COMMAND_ID (0x00)
#define ZCL_SQUAWK_COMMAND_ID (0x01)
+// Commands for cluster: Media Playback
+#define ZCL_PLAY_REQUEST_COMMAND_ID (0x00)
+#define ZCL_PLAYBACK_COMMAND_ID (0x00)
+#define ZCL_PAUSE_REQUEST_COMMAND_ID (0x01)
+#define ZCL_STOP_REQUEST_COMMAND_ID (0x02)
+#define ZCL_START_OVER_REQUEST_COMMAND_ID (0x03)
+#define ZCL_PREVIOUS_REQUEST_COMMAND_ID (0x04)
+#define ZCL_NEXT_REQUEST_COMMAND_ID (0x05)
+#define ZCL_REWIND_REQUEST_COMMAND_ID (0x06)
+#define ZCL_FAST_FORWARD_REQUEST_COMMAND_ID (0x07)
+#define ZCL_SKIP_FORWARD_REQUEST_COMMAND_ID (0x08)
+#define ZCL_SKIP_BACKWARD_REQUEST_COMMAND_ID (0x09)
+
// Commands for cluster: Low Power
#define ZCL_SLEEP_COMMAND_ID (0x00)
+// Commands for cluster: Content Launch
+#define ZCL_LAUNCH_CONTENT_COMMAND_ID (0x00)
+#define ZCL_LAUNCH_CONTENT_RESPONSE_COMMAND_ID (0x00)
+#define ZCL_LAUNCH_URL_COMMAND_ID (0x01)
+#define ZCL_LAUNCH_URL_RESPONSE_COMMAND_ID (0x01)
+
// Commands for cluster: Generic Tunnel
#define ZCL_MATCH_PROTOCOL_ADDRESS_COMMAND_ID (0x00)
#define ZCL_MATCH_PROTOCOL_ADDRESS_RESPONSE_COMMAND_ID (0x00)
#define ZCL_BIND_COMMAND_ID (0x00)
#define ZCL_UNBIND_COMMAND_ID (0x01)
-// Commands for cluster: Media Playback
-#define ZCL_PLAY_REQUEST_COMMAND_ID (0x00)
-#define ZCL_PLAYBACK_COMMAND_ID (0x00)
-#define ZCL_PAUSE_REQUEST_COMMAND_ID (0x01)
-#define ZCL_STOP_REQUEST_COMMAND_ID (0x02)
-#define ZCL_START_OVER_REQUEST_COMMAND_ID (0x03)
-#define ZCL_PREVIOUS_REQUEST_COMMAND_ID (0x04)
-#define ZCL_NEXT_REQUEST_COMMAND_ID (0x05)
-#define ZCL_REWIND_REQUEST_COMMAND_ID (0x06)
-#define ZCL_FAST_FORWARD_REQUEST_COMMAND_ID (0x07)
-#define ZCL_SKIP_FORWARD_REQUEST_COMMAND_ID (0x08)
-#define ZCL_SKIP_BACKWARD_REQUEST_COMMAND_ID (0x09)
-
-// Commands for cluster: Content Launch
-#define ZCL_LAUNCH_CONTENT_COMMAND_ID (0x00)
-#define ZCL_LAUNCH_CONTENT_RESPONSE_COMMAND_ID (0x00)
-#define ZCL_LAUNCH_URL_COMMAND_ID (0x01)
-#define ZCL_LAUNCH_URL_RESPONSE_COMMAND_ID (0x01)
-
// Commands for cluster: Sample Mfg Specific Cluster
#define ZCL_COMMAND_ONE_COMMAND_ID (0x00)
#define ZAP_ATTRIBUTE_MASK(mask) ATTRIBUTE_MASK_##mask
// This is an array of EmberAfAttributeMetadata structures.
-#define GENERATED_ATTRIBUTE_COUNT 130
+#define GENERATED_ATTRIBUTE_COUNT 127
#define GENERATED_ATTRIBUTES \
{ \
{ 0xFFFD, ZAP_TYPE(INT16U), 2, 0, ZAP_SIMPLE_DEFAULT(2) }, /* Identify (server): cluster revision */ \
{ 0x0001, ZAP_TYPE(INT16U), 2, 0, ZAP_EMPTY_DEFAULT() }, /* Application Basic (server): vendor id */ \
{ 0x0002, ZAP_TYPE(OCTET_STRING), 32, 0, \
ZAP_LONG_DEFAULTS_INDEX(554) }, /* Application Basic (server): application name */ \
- { 0xFFFD, ZAP_TYPE(INT16U), 2, 0, ZAP_SIMPLE_DEFAULT(0x0001) }, /* Application Basic (server): cluster revision */ \
{ 0x0003, ZAP_TYPE(INT16U), 2, 0, ZAP_EMPTY_DEFAULT() }, /* Application Basic (server): product id */ \
+ { 0xFFFD, ZAP_TYPE(INT16U), 2, 0, ZAP_SIMPLE_DEFAULT(0x0001) }, /* Application Basic (server): cluster revision */ \
{ 0x0005, ZAP_TYPE(OCTET_STRING), 32, 0, \
ZAP_LONG_DEFAULTS_INDEX(586) }, /* Application Basic (server): application id */ \
{ 0x0006, ZAP_TYPE(INT16U), 2, 0, ZAP_EMPTY_DEFAULT() }, /* Application Basic (server): catalog vendor id */ \
{ 0x0007, ZAP_TYPE(ENUM8), 1, 0, ZAP_SIMPLE_DEFAULT(0x01) }, /* Application Basic (server): application satus */ \
{ 0xFFFD, ZAP_TYPE(INT16U), 2, 0, ZAP_SIMPLE_DEFAULT(0x0001) }, /* Binding (server): cluster revision */ \
- { 0x0000, ZAP_TYPE(INT16U), 2, 0, ZAP_EMPTY_DEFAULT() }, /* Media Playback (server): current state */ \
- { 0xFFFD, ZAP_TYPE(INT16U), 2, 0, ZAP_SIMPLE_DEFAULT(0x0001) }, /* Media Playback (server): cluster revision */ \
- { 0xFFFD, ZAP_TYPE(INT16U), 2, 0, ZAP_SIMPLE_DEFAULT(0x0001) }, /* Content Launch (server): cluster revision */ \
{ 0x0000, ZAP_TYPE(ARRAY), 254, 0, ZAP_LONG_DEFAULTS_INDEX(618) }, /* Group Key Management (server): groups */ \
{ 0x0001, ZAP_TYPE(ARRAY), 254, 0, ZAP_LONG_DEFAULTS_INDEX(872) }, /* Group Key Management (server): group keys */ \
{ 0xFFFD, ZAP_TYPE(INT16U), 2, 0, ZAP_SIMPLE_DEFAULT(0x0001) }, /* Group Key Management (server): cluster revision */ \
};
#define ZAP_CLUSTER_MASK(mask) CLUSTER_MASK_##mask
-#define GENERATED_CLUSTER_COUNT 21
+#define GENERATED_CLUSTER_COUNT 19
#define GENERATED_CLUSTERS \
{ \
{ 0x0003, \
0xF000, ZAP_ATTRIBUTE_INDEX(109), 1, 2, ZAP_CLUSTER_MASK(SERVER), NULL \
}, /* Endpoint: 1, Cluster: Binding (server) */ \
{ \
- 0xF001, ZAP_ATTRIBUTE_INDEX(110), 2, 4, ZAP_CLUSTER_MASK(SERVER), NULL \
- }, /* Endpoint: 1, Cluster: Media Playback (server) */ \
- { \
- 0xF002, ZAP_ATTRIBUTE_INDEX(112), 1, 2, ZAP_CLUSTER_MASK(SERVER), NULL \
- }, /* Endpoint: 1, Cluster: Content Launch (server) */ \
- { \
- 0xF004, ZAP_ATTRIBUTE_INDEX(113), 3, 510, ZAP_CLUSTER_MASK(SERVER), NULL \
+ 0xF004, ZAP_ATTRIBUTE_INDEX(110), 3, 510, ZAP_CLUSTER_MASK(SERVER), NULL \
}, /* Endpoint: 1, Cluster: Group Key Management (server) */ \
{ 0x0006, \
- ZAP_ATTRIBUTE_INDEX(116), \
+ ZAP_ATTRIBUTE_INDEX(113), \
2, \
3, \
ZAP_CLUSTER_MASK(SERVER) | ZAP_CLUSTER_MASK(INIT_FUNCTION), \
chipFuncArrayOnOffServer }, /* Endpoint: 2, Cluster: On/off (server) */ \
{ \
- 0x0028, ZAP_ATTRIBUTE_INDEX(118), 12, 254, ZAP_CLUSTER_MASK(SERVER), NULL \
+ 0x0028, ZAP_ATTRIBUTE_INDEX(115), 12, 254, ZAP_CLUSTER_MASK(SERVER), NULL \
}, /* Endpoint: 2, Cluster: Basic (server) */ \
}
// This is an array of EmberAfEndpointType structures.
#define GENERATED_ENDPOINT_TYPES \
{ \
- { ZAP_CLUSTER_INDEX(0), 19, 1292 }, { ZAP_CLUSTER_INDEX(19), 2, 257 }, \
+ { ZAP_CLUSTER_INDEX(0), 17, 1286 }, { ZAP_CLUSTER_INDEX(17), 2, 257 }, \
}
// Largest attribute size is needed for various buffers
#define ATTRIBUTE_SINGLETONS_SIZE (508)
// Total size of attribute storage
-#define ATTRIBUTE_MAX_SIZE (1549)
+#define ATTRIBUTE_MAX_SIZE (1543)
// Number of fixed endpoints
#define FIXED_ENDPOINT_COUNT (2)
// Array of EmberAfCommandMetadata structs.
#define ZAP_COMMAND_MASK(mask) COMMAND_MASK_##mask
-#define EMBER_AF_GENERATED_COMMAND_COUNT (132)
+#define EMBER_AF_GENERATED_COMMAND_COUNT (117)
#define GENERATED_COMMANDS \
{ \
{ 0x0003, 0x00, ZAP_COMMAND_MASK(INCOMING_SERVER) }, /* Identify (server): Identify */ \
{ 0x0508, 0x00, ZAP_COMMAND_MASK(INCOMING_SERVER) }, /* Low Power (server): Sleep */ \
{ 0xF000, 0x00, ZAP_COMMAND_MASK(INCOMING_SERVER) }, /* Binding (server): Bind */ \
{ 0xF000, 0x01, ZAP_COMMAND_MASK(INCOMING_SERVER) }, /* Binding (server): Unbind */ \
- { 0xF001, 0x00, ZAP_COMMAND_MASK(INCOMING_SERVER) }, /* Media Playback (server): PlayRequest */ \
- { 0xF001, 0x00, ZAP_COMMAND_MASK(INCOMING_CLIENT) }, /* Media Playback (server): Playback */ \
- { 0xF001, 0x01, ZAP_COMMAND_MASK(INCOMING_SERVER) }, /* Media Playback (server): PauseRequest */ \
- { 0xF001, 0x02, ZAP_COMMAND_MASK(INCOMING_SERVER) }, /* Media Playback (server): StopRequest */ \
- { 0xF001, 0x03, ZAP_COMMAND_MASK(INCOMING_SERVER) }, /* Media Playback (server): StartOverRequest */ \
- { 0xF001, 0x04, ZAP_COMMAND_MASK(INCOMING_SERVER) }, /* Media Playback (server): PreviousRequest */ \
- { 0xF001, 0x05, ZAP_COMMAND_MASK(INCOMING_SERVER) }, /* Media Playback (server): NextRequest */ \
- { 0xF001, 0x06, ZAP_COMMAND_MASK(INCOMING_SERVER) }, /* Media Playback (server): RewindRequest */ \
- { 0xF001, 0x07, ZAP_COMMAND_MASK(INCOMING_SERVER) }, /* Media Playback (server): FastForwardRequest */ \
- { 0xF001, 0x08, ZAP_COMMAND_MASK(INCOMING_SERVER) }, /* Media Playback (server): SkipForwardRequest */ \
- { 0xF001, 0x09, ZAP_COMMAND_MASK(INCOMING_SERVER) }, /* Media Playback (server): SkipBackwardRequest */ \
- { 0xF002, 0x00, ZAP_COMMAND_MASK(INCOMING_SERVER) }, /* Content Launch (server): LaunchContent */ \
- { 0xF002, 0x00, ZAP_COMMAND_MASK(INCOMING_CLIENT) }, /* Content Launch (server): LaunchContentResponse */ \
- { 0xF002, 0x01, ZAP_COMMAND_MASK(INCOMING_SERVER) }, /* Content Launch (server): LaunchURL */ \
- { 0xF002, 0x01, ZAP_COMMAND_MASK(INCOMING_CLIENT) }, /* Content Launch (server): LaunchURLResponse */ \
}
// Array of EmberAfManufacturerCodeEntry structures for commands.
#define EMBER_AF_BASIC_CLUSTER_SERVER_ENDPOINT_COUNT (2)
#define EMBER_AF_BINDING_CLUSTER_SERVER_ENDPOINT_COUNT (1)
#define EMBER_AF_COLOR_CONTROL_CLUSTER_SERVER_ENDPOINT_COUNT (1)
-#define EMBER_AF_CONTENT_LAUNCH_CLUSTER_SERVER_ENDPOINT_COUNT (1)
#define EMBER_AF_DOOR_LOCK_CLUSTER_SERVER_ENDPOINT_COUNT (1)
#define EMBER_AF_GENERAL_COMMISSIONING_CLUSTER_SERVER_ENDPOINT_COUNT (1)
#define EMBER_AF_GROUP_KEY_MANAGEMENT_CLUSTER_SERVER_ENDPOINT_COUNT (1)
#define EMBER_AF_IDENTIFY_CLUSTER_SERVER_ENDPOINT_COUNT (1)
#define EMBER_AF_LEVEL_CONTROL_CLUSTER_SERVER_ENDPOINT_COUNT (1)
#define EMBER_AF_LOW_POWER_CLUSTER_SERVER_ENDPOINT_COUNT (1)
-#define EMBER_AF_MEDIA_PLAYBACK_CLUSTER_SERVER_ENDPOINT_COUNT (1)
#define EMBER_AF_NETWORK_COMMISSIONING_CLUSTER_SERVER_ENDPOINT_COUNT (1)
#define EMBER_AF_ON_OFF_CLUSTER_SERVER_ENDPOINT_COUNT (2)
#define EMBER_AF_SCENES_CLUSTER_SERVER_ENDPOINT_COUNT (1)
#define EMBER_AF_PLUGIN_COLOR_CONTROL_SERVER_TEMP
#define EMBER_AF_PLUGIN_COLOR_CONTROL_SERVER_HSV
-// Use this macro to check if the server side of the Content Launch cluster is included
-#define ZCL_USING_CONTENT_LAUNCH_CLUSTER_SERVER
-#define EMBER_AF_PLUGIN_CONTENT_LAUNCH_SERVER
-#define EMBER_AF_PLUGIN_CONTENT_LAUNCH
-
// Use this macro to check if the server side of the Door Lock cluster is included
#define ZCL_USING_DOOR_LOCK_CLUSTER_SERVER
#define EMBER_AF_PLUGIN_DOOR_LOCK_SERVER
#define EMBER_AF_PLUGIN_LOW_POWER_SERVER
#define EMBER_AF_PLUGIN_LOW_POWER
-// Use this macro to check if the server side of the Media Playback cluster is included
-#define ZCL_USING_MEDIA_PLAYBACK_CLUSTER_SERVER
-#define EMBER_AF_PLUGIN_MEDIA_PLAYBACK_SERVER
-#define EMBER_AF_PLUGIN_MEDIA_PLAYBACK
-
// Use this macro to check if the server side of the Network Commissioning cluster is included
#define ZCL_USING_NETWORK_COMMISSIONING_CLUSTER_SERVER
#define EMBER_AF_PLUGIN_NETWORK_COMMISSIONING_SERVER
#define CHIP_PRINTCLUSTER_IAS_WD_CLUSTER
#endif
+#if defined(ZCL_USING_MEDIA_PLAYBACK_CLUSTER_SERVER) || defined(ZCL_USING_MEDIA_PLAYBACK_CLUSTER_CLIENT)
+#define CHIP_PRINTCLUSTER_MEDIA_PLAYBACK_CLUSTER { ZCL_MEDIA_PLAYBACK_CLUSTER_ID, 1286, "Media Playback" },
+#else
+#define CHIP_PRINTCLUSTER_MEDIA_PLAYBACK_CLUSTER
+#endif
+
#if defined(ZCL_USING_LOW_POWER_CLUSTER_SERVER) || defined(ZCL_USING_LOW_POWER_CLUSTER_CLIENT)
#define CHIP_PRINTCLUSTER_LOW_POWER_CLUSTER { ZCL_LOW_POWER_CLUSTER_ID, 1288, "Low Power" },
#else
#define CHIP_PRINTCLUSTER_LOW_POWER_CLUSTER
#endif
+#if defined(ZCL_USING_CONTENT_LAUNCH_CLUSTER_SERVER) || defined(ZCL_USING_CONTENT_LAUNCH_CLUSTER_CLIENT)
+#define CHIP_PRINTCLUSTER_CONTENT_LAUNCH_CLUSTER { ZCL_CONTENT_LAUNCH_CLUSTER_ID, 1290, "Content Launch" },
+#else
+#define CHIP_PRINTCLUSTER_CONTENT_LAUNCH_CLUSTER
+#endif
+
#if defined(ZCL_USING_APPLICATION_BASIC_CLUSTER_SERVER) || defined(ZCL_USING_APPLICATION_BASIC_CLUSTER_CLIENT)
#define CHIP_PRINTCLUSTER_APPLICATION_BASIC_CLUSTER { ZCL_APPLICATION_BASIC_CLUSTER_ID, 1293, "Application Basic" },
#else
#define CHIP_PRINTCLUSTER_BINDING_CLUSTER
#endif
-#if defined(ZCL_USING_MEDIA_PLAYBACK_CLUSTER_SERVER) || defined(ZCL_USING_MEDIA_PLAYBACK_CLUSTER_CLIENT)
-#define CHIP_PRINTCLUSTER_MEDIA_PLAYBACK_CLUSTER { ZCL_MEDIA_PLAYBACK_CLUSTER_ID, 61441, "Media Playback" },
-#else
-#define CHIP_PRINTCLUSTER_MEDIA_PLAYBACK_CLUSTER
-#endif
-
-#if defined(ZCL_USING_CONTENT_LAUNCH_CLUSTER_SERVER) || defined(ZCL_USING_CONTENT_LAUNCH_CLUSTER_CLIENT)
-#define CHIP_PRINTCLUSTER_CONTENT_LAUNCH_CLUSTER { ZCL_CONTENT_LAUNCH_CLUSTER_ID, 61442, "Content Launch" },
-#else
-#define CHIP_PRINTCLUSTER_CONTENT_LAUNCH_CLUSTER
-#endif
-
#if defined(ZCL_USING_GROUP_KEY_MANAGEMENT_CLUSTER_SERVER) || defined(ZCL_USING_GROUP_KEY_MANAGEMENT_CLUSTER_CLIENT)
#define CHIP_PRINTCLUSTER_GROUP_KEY_MANAGEMENT_CLUSTER { ZCL_GROUP_KEY_MANAGEMENT_CLUSTER_ID, 61444, "Group Key Management" },
#else
CHIP_PRINTCLUSTER_IAS_ZONE_CLUSTER \
CHIP_PRINTCLUSTER_IAS_ACE_CLUSTER \
CHIP_PRINTCLUSTER_IAS_WD_CLUSTER \
+ CHIP_PRINTCLUSTER_MEDIA_PLAYBACK_CLUSTER \
CHIP_PRINTCLUSTER_LOW_POWER_CLUSTER \
+ CHIP_PRINTCLUSTER_CONTENT_LAUNCH_CLUSTER \
CHIP_PRINTCLUSTER_APPLICATION_BASIC_CLUSTER \
CHIP_PRINTCLUSTER_GENERIC_TUNNEL_CLUSTER \
CHIP_PRINTCLUSTER_BACNET_PROTOCOL_TUNNEL_CLUSTER \
CHIP_PRINTCLUSTER_DIAGNOSTICS_CLUSTER \
CHIP_PRINTCLUSTER_ZLL_COMMISSIONING_CLUSTER \
CHIP_PRINTCLUSTER_BINDING_CLUSTER \
- CHIP_PRINTCLUSTER_MEDIA_PLAYBACK_CLUSTER \
- CHIP_PRINTCLUSTER_CONTENT_LAUNCH_CLUSTER \
CHIP_PRINTCLUSTER_GROUP_KEY_MANAGEMENT_CLUSTER \
CHIP_PRINTCLUSTER_SAMPLE_MFG_SPECIFIC_CLUSTER \
CHIP_PRINTCLUSTER_SAMPLE_MFG_SPECIFIC_CLUSTER_2 \
# See the License for the specific language governing permissions and
# limitations under the License.
-#
-# This is a project Makefile. It is assumed the directory this Makefile resides in is a
-# project subdirectory.
-#
-
# The following lines of boilerplate have to be in your project's
# CMakeLists in this exact order for cmake to work correctly
cmake_minimum_required(VERSION 3.5)
)
project(chip-all-clusters-app)
+idf_build_set_property(CXX_COMPILE_OPTIONS "-std=c++14;-Os;-DLWIP_IPV6_SCOPES=0;-DCHIP_HAVE_CONFIG_H" APPEND)
+idf_build_set_property(C_COMPILE_OPTIONS "-Os;-DLWIP_IPV6_SCOPES=0" APPEND)
Currently building in VSCode _and_ deploying from native is not supported, so
make sure the IDF_PATH has been exported(See the manual setup steps above).
-- In the root of the example directory, sync the CHIP tree's submodules and
- source `idf.sh`. Note: This does not have to be repeated for incremental
- builds.
+- Setting up the environment
- $ source idf.sh
+To download and install packages.
+
+ $ cd ${HOME}/tools/esp-idf
+ $ ./install.sh
+ $ . ./export.sh
+ $ cd {path-to-connectedhomeip}
+ $ source ./scripts/bootstrap.sh
+ $ source ./scripts/activate.sh
+ $ cd {path-to-connectedhomeip-examples}
+
+If packages are already installed then simply activate it.
+
+ $ cd ${HOME}/tools/esp-idf
+ $ ./install.sh
+ $ . ./export.sh
+ $ cd {path-to-connectedhomeip}
+ $ source ./scripts/activate.sh
+ $ cd {path-to-connectedhomeip-examples}
- Configuration Options
To choose from the different configuration options, run menuconfig
- $ idf make menuconfig
+ $ idf.py menuconfig
Select ESP32 based `Device Type` through `Demo`->`Device Type`.
The device types that are currently supported include `ESP32-DevKitC` (default),
`Component config`->`CHIP Device Layer`->`WiFi Station Options`->`Default WiFi SSID` and
`Default WiFi Password` respectively.
- To use the default configuration options, run the default config
+- To build the demo application.
- $ idf make defconfig
-
-- Run make to build the demo application.
-
- $ idf make
+ $ idf.py build
- After building the application, to flash it outside of VSCode, connect your
device via USB. Then run the following command to flash the demo application
before flashing. For ESP32-DevKitC devices this is labeled in the
[functional description diagram](https://docs.espressif.com/projects/esp-idf/en/latest/esp32/hw-reference/esp32/get-started-devkitc.html#functional-description).
- $ idf make flash monitor ESPPORT=/dev/tty.SLAB_USBtoUART
+ $ idf.py flash monitor ESPPORT=/dev/tty.SLAB_USBtoUART
Note: Some users might have to install the
[VCP driver](https://www.silabs.com/products/development-tools/software/usb-to-uart-bridge-vcp-drivers)
- If desired, the monitor can be run again like so:
- $ idf make monitor ESPPORT=/dev/tty.SLAB_USBtoUART
+ $ idf.py monitor ESPPORT=/dev/tty.SLAB_USBtoUART
## Using the Echo Server
# See the License for the specific language governing permissions and
# limitations under the License.
#
-# Description:
-# Component makefile for the ESP32 demo application.
-#
+
# (Uses default behaviour of compiling all source files in directory, adding 'include' to include path.)
# The list of src and include dirs must be in sync with that in all-clusters-app/esp32/main/component.mk
idf_component_register(PRIV_INCLUDE_DIRS
"${CMAKE_SOURCE_DIR}/third_party/connectedhomeip/src/app/clusters/identify"
"${CMAKE_SOURCE_DIR}/third_party/connectedhomeip/src/app/clusters/barrier-control-server"
"${CMAKE_SOURCE_DIR}/third_party/connectedhomeip/src/app/clusters/general-commissioning-server"
+ "${CMAKE_SOURCE_DIR}/third_party/connectedhomeip/src/app/clusters/network-commissioning"
"${CMAKE_SOURCE_DIR}/third_party/connectedhomeip/src/app/clusters/groups-server"
"${CMAKE_SOURCE_DIR}/third_party/connectedhomeip/src/app/clusters/color-control-server"
"${CMAKE_SOURCE_DIR}/third_party/connectedhomeip/src/app/clusters/content-launch-server"
+ "${CMAKE_SOURCE_DIR}/third_party/connectedhomeip/src/app/clusters/low-power-server"
"${CMAKE_SOURCE_DIR}/third_party/connectedhomeip/src/app/clusters/media-playback-server"
"${CMAKE_SOURCE_DIR}/third_party/connectedhomeip/src/app/clusters/temperature-measurement-server"
"${CMAKE_SOURCE_DIR}/third_party/connectedhomeip/src/app/clusters/scenes"
# Use a custom partition table
CONFIG_PARTITION_TABLE_CUSTOM=y
CONFIG_PARTITION_TABLE_FILENAME="partitions.csv"
+
+# Vendor and product id
+CONFIG_DEVICE_VENDOR_ID=0x235A
+CONFIG_DEVICE_PRODUCT_ID=0x4541
#### QR Code with optional Vendor Info
- $ chip-tool chip-tool payload parse-setup-payload "CH:#####"
+ $ chip-tool payload parse-setup-payload "CH:#####"
#### Manual Setup Code
command->SetCommandExitStatus(true);
}
-static void OnContentLaunchClusterLaunchContentResponse(void * context, uint8_t contentLaunchStatus)
-{
- ChipLogProgress(chipTool, "ContentLaunchClusterLaunchContentResponse");
-
- ModelCommand * command = reinterpret_cast<ModelCommand *>(context);
- command->SetCommandExitStatus(true);
-}
-
-static void OnContentLaunchClusterLaunchURLResponse(void * context, uint8_t contentLaunchStatus)
-{
- ChipLogProgress(chipTool, "ContentLaunchClusterLaunchURLResponse");
-
- ModelCommand * command = reinterpret_cast<ModelCommand *>(context);
- command->SetCommandExitStatus(true);
-}
-
static void OnDoorLockClusterClearAllPinsResponse(void * context)
{
ChipLogProgress(chipTool, "DoorLockClusterClearAllPinsResponse");
| Basic | 0x0028 |
| Binding | 0xF000 |
| ColorControl | 0x0300 |
-| ContentLaunch | 0xF002 |
| DoorLock | 0x0101 |
| GeneralCommissioning | 0x0030 |
| Groups | 0x0004 |
| Identify | 0x0003 |
| LevelControl | 0x0008 |
| LowPower | 0x0508 |
-| MediaPlayback | 0xF001 |
| OnOff | 0x0006 |
| Scenes | 0x0005 |
| TemperatureMeasurement | 0x0402 |
constexpr chip::ClusterId kBasicClusterId = 0x0028;
constexpr chip::ClusterId kBindingClusterId = 0xF000;
constexpr chip::ClusterId kColorControlClusterId = 0x0300;
-constexpr chip::ClusterId kContentLaunchClusterId = 0xF002;
constexpr chip::ClusterId kDoorLockClusterId = 0x0101;
constexpr chip::ClusterId kGeneralCommissioningClusterId = 0x0030;
constexpr chip::ClusterId kGroupsClusterId = 0x0004;
constexpr chip::ClusterId kIdentifyClusterId = 0x0003;
constexpr chip::ClusterId kLevelControlClusterId = 0x0008;
constexpr chip::ClusterId kLowPowerClusterId = 0x0508;
-constexpr chip::ClusterId kMediaPlaybackClusterId = 0xF001;
constexpr chip::ClusterId kOnOffClusterId = 0x0006;
constexpr chip::ClusterId kScenesClusterId = 0x0005;
constexpr chip::ClusterId kTemperatureMeasurementClusterId = 0x0402;
public:
DiscoverApplicationBasicAttributes() : ModelCommand("discover") { ModelCommand::AddArguments(); }
+ ~DiscoverApplicationBasicAttributes()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
+
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
ChipLogProgress(chipTool, "Sending cluster (0x0000) command (0x0C) on endpoint %" PRIu16, endpointId);
ModelCommand::AddArguments();
}
+ ~ReadApplicationBasicVendorName()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
+
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
ChipLogProgress(chipTool, "Sending cluster (0x050D) command (0x00) on endpoint %" PRIu16, endpointId);
ModelCommand::AddArguments();
}
+ ~ReadApplicationBasicVendorId()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
+
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
ChipLogProgress(chipTool, "Sending cluster (0x050D) command (0x00) on endpoint %" PRIu16, endpointId);
ModelCommand::AddArguments();
}
+ ~ReadApplicationBasicApplicationName()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
+
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
ChipLogProgress(chipTool, "Sending cluster (0x050D) command (0x00) on endpoint %" PRIu16, endpointId);
ModelCommand::AddArguments();
}
+ ~ReadApplicationBasicProductId()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
+
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
ChipLogProgress(chipTool, "Sending cluster (0x050D) command (0x00) on endpoint %" PRIu16, endpointId);
ModelCommand::AddArguments();
}
+ ~ReadApplicationBasicApplicationId()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
+
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
ChipLogProgress(chipTool, "Sending cluster (0x050D) command (0x00) on endpoint %" PRIu16, endpointId);
ModelCommand::AddArguments();
}
+ ~ReadApplicationBasicCatalogVendorId()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
+
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
ChipLogProgress(chipTool, "Sending cluster (0x050D) command (0x00) on endpoint %" PRIu16, endpointId);
ModelCommand::AddArguments();
}
+ ~ReadApplicationBasicApplicationSatus()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
+
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
ChipLogProgress(chipTool, "Sending cluster (0x050D) command (0x00) on endpoint %" PRIu16, endpointId);
ModelCommand::AddArguments();
}
+ ~ReadApplicationBasicClusterRevision()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
+
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
ChipLogProgress(chipTool, "Sending cluster (0x050D) command (0x00) on endpoint %" PRIu16, endpointId);
AddArgument("percentOpen", 0, UINT8_MAX, &mPercentOpen);
ModelCommand::AddArguments();
}
+ ~BarrierControlBarrierControlGoToPercent()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
{
public:
BarrierControlBarrierControlStop() : ModelCommand("barrier-control-stop") { ModelCommand::AddArguments(); }
+ ~BarrierControlBarrierControlStop()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
public:
DiscoverBarrierControlAttributes() : ModelCommand("discover") { ModelCommand::AddArguments(); }
+ ~DiscoverBarrierControlAttributes()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
+
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
ChipLogProgress(chipTool, "Sending cluster (0x0000) command (0x0C) on endpoint %" PRIu16, endpointId);
ModelCommand::AddArguments();
}
+ ~ReadBarrierControlBarrierMovingState()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
+
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
ChipLogProgress(chipTool, "Sending cluster (0x0103) command (0x00) on endpoint %" PRIu16, endpointId);
ModelCommand::AddArguments();
}
+ ~ReadBarrierControlBarrierSafetyStatus()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
+
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
ChipLogProgress(chipTool, "Sending cluster (0x0103) command (0x00) on endpoint %" PRIu16, endpointId);
ModelCommand::AddArguments();
}
+ ~ReadBarrierControlBarrierCapabilities()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
+
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
ChipLogProgress(chipTool, "Sending cluster (0x0103) command (0x00) on endpoint %" PRIu16, endpointId);
ModelCommand::AddArguments();
}
+ ~ReadBarrierControlBarrierPosition()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
+
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
ChipLogProgress(chipTool, "Sending cluster (0x0103) command (0x00) on endpoint %" PRIu16, endpointId);
ModelCommand::AddArguments();
}
+ ~ReadBarrierControlClusterRevision()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
+
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
ChipLogProgress(chipTool, "Sending cluster (0x0103) command (0x00) on endpoint %" PRIu16, endpointId);
{
public:
BasicMfgSpecificPing() : ModelCommand("mfg-specific-ping") { ModelCommand::AddArguments(); }
+ ~BasicMfgSpecificPing()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
public:
DiscoverBasicAttributes() : ModelCommand("discover") { ModelCommand::AddArguments(); }
+ ~DiscoverBasicAttributes()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
+
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
ChipLogProgress(chipTool, "Sending cluster (0x0000) command (0x0C) on endpoint %" PRIu16, endpointId);
ModelCommand::AddArguments();
}
+ ~ReadBasicInteractionModelVersion()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
+
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
ChipLogProgress(chipTool, "Sending cluster (0x0028) command (0x00) on endpoint %" PRIu16, endpointId);
ModelCommand::AddArguments();
}
+ ~ReadBasicVendorName()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
+
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
ChipLogProgress(chipTool, "Sending cluster (0x0028) command (0x00) on endpoint %" PRIu16, endpointId);
ModelCommand::AddArguments();
}
+ ~ReadBasicVendorID()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
+
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
ChipLogProgress(chipTool, "Sending cluster (0x0028) command (0x00) on endpoint %" PRIu16, endpointId);
ModelCommand::AddArguments();
}
+ ~ReadBasicProductName()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
+
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
ChipLogProgress(chipTool, "Sending cluster (0x0028) command (0x00) on endpoint %" PRIu16, endpointId);
ModelCommand::AddArguments();
}
+ ~ReadBasicProductID()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
+
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
ChipLogProgress(chipTool, "Sending cluster (0x0028) command (0x00) on endpoint %" PRIu16, endpointId);
ModelCommand::AddArguments();
}
+ ~ReadBasicUserLabel()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
+
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
ChipLogProgress(chipTool, "Sending cluster (0x0028) command (0x00) on endpoint %" PRIu16, endpointId);
ModelCommand::AddArguments();
}
+ ~WriteBasicUserLabel()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
+
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
ChipLogProgress(chipTool, "Sending cluster (0x0028) command (0x01) on endpoint %" PRIu16, endpointId);
ModelCommand::AddArguments();
}
+ ~ReadBasicLocation()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
+
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
ChipLogProgress(chipTool, "Sending cluster (0x0028) command (0x00) on endpoint %" PRIu16, endpointId);
ModelCommand::AddArguments();
}
+ ~WriteBasicLocation()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
+
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
ChipLogProgress(chipTool, "Sending cluster (0x0028) command (0x01) on endpoint %" PRIu16, endpointId);
ModelCommand::AddArguments();
}
+ ~ReadBasicHardwareVersion()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
+
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
ChipLogProgress(chipTool, "Sending cluster (0x0028) command (0x00) on endpoint %" PRIu16, endpointId);
ModelCommand::AddArguments();
}
+ ~ReadBasicHardwareVersionString()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
+
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
ChipLogProgress(chipTool, "Sending cluster (0x0028) command (0x00) on endpoint %" PRIu16, endpointId);
ModelCommand::AddArguments();
}
+ ~ReadBasicSoftwareVersion()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
+
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
ChipLogProgress(chipTool, "Sending cluster (0x0028) command (0x00) on endpoint %" PRIu16, endpointId);
ModelCommand::AddArguments();
}
+ ~ReadBasicSoftwareVersionString()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
+
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
ChipLogProgress(chipTool, "Sending cluster (0x0028) command (0x00) on endpoint %" PRIu16, endpointId);
ModelCommand::AddArguments();
}
+ ~ReadBasicClusterRevision()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
+
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
ChipLogProgress(chipTool, "Sending cluster (0x0028) command (0x00) on endpoint %" PRIu16, endpointId);
AddArgument("clusterId", 0, UINT16_MAX, &mClusterId);
ModelCommand::AddArguments();
}
+ ~BindingBind()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
AddArgument("clusterId", 0, UINT16_MAX, &mClusterId);
ModelCommand::AddArguments();
}
+ ~BindingUnbind()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
public:
DiscoverBindingAttributes() : ModelCommand("discover") { ModelCommand::AddArguments(); }
+ ~DiscoverBindingAttributes()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
+
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
ChipLogProgress(chipTool, "Sending cluster (0x0000) command (0x0C) on endpoint %" PRIu16, endpointId);
ModelCommand::AddArguments();
}
+ ~ReadBindingClusterRevision()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
+
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
ChipLogProgress(chipTool, "Sending cluster (0xF000) command (0x00) on endpoint %" PRIu16, endpointId);
AddArgument("optionsOverride", 0, UINT8_MAX, &mOptionsOverride);
ModelCommand::AddArguments();
}
+ ~ColorControlMoveColor()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
AddArgument("optionsOverride", 0, UINT8_MAX, &mOptionsOverride);
ModelCommand::AddArguments();
}
+ ~ColorControlMoveColorTemperature()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
AddArgument("optionsOverride", 0, UINT8_MAX, &mOptionsOverride);
ModelCommand::AddArguments();
}
+ ~ColorControlMoveHue()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
AddArgument("optionsOverride", 0, UINT8_MAX, &mOptionsOverride);
ModelCommand::AddArguments();
}
+ ~ColorControlMoveSaturation()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
AddArgument("optionsOverride", 0, UINT8_MAX, &mOptionsOverride);
ModelCommand::AddArguments();
}
+ ~ColorControlMoveToColor()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
AddArgument("optionsOverride", 0, UINT8_MAX, &mOptionsOverride);
ModelCommand::AddArguments();
}
+ ~ColorControlMoveToColorTemperature()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
AddArgument("optionsOverride", 0, UINT8_MAX, &mOptionsOverride);
ModelCommand::AddArguments();
}
+ ~ColorControlMoveToHue()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
AddArgument("optionsOverride", 0, UINT8_MAX, &mOptionsOverride);
ModelCommand::AddArguments();
}
+ ~ColorControlMoveToHueAndSaturation()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
AddArgument("optionsOverride", 0, UINT8_MAX, &mOptionsOverride);
ModelCommand::AddArguments();
}
+ ~ColorControlMoveToSaturation()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
AddArgument("optionsOverride", 0, UINT8_MAX, &mOptionsOverride);
ModelCommand::AddArguments();
}
+ ~ColorControlStepColor()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
AddArgument("optionsOverride", 0, UINT8_MAX, &mOptionsOverride);
ModelCommand::AddArguments();
}
+ ~ColorControlStepColorTemperature()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
AddArgument("optionsOverride", 0, UINT8_MAX, &mOptionsOverride);
ModelCommand::AddArguments();
}
+ ~ColorControlStepHue()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
AddArgument("optionsOverride", 0, UINT8_MAX, &mOptionsOverride);
ModelCommand::AddArguments();
}
+ ~ColorControlStepSaturation()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
AddArgument("optionsOverride", 0, UINT8_MAX, &mOptionsOverride);
ModelCommand::AddArguments();
}
+ ~ColorControlStopMoveStep()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
public:
DiscoverColorControlAttributes() : ModelCommand("discover") { ModelCommand::AddArguments(); }
+ ~DiscoverColorControlAttributes()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
+
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
ChipLogProgress(chipTool, "Sending cluster (0x0000) command (0x0C) on endpoint %" PRIu16, endpointId);
ModelCommand::AddArguments();
}
+ ~ReadColorControlCurrentHue()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
+
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
ChipLogProgress(chipTool, "Sending cluster (0x0300) command (0x00) on endpoint %" PRIu16, endpointId);
ModelCommand::AddArguments();
}
+ ~ReportColorControlCurrentHue()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ delete onReportCallback;
+ }
+
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
ChipLogProgress(chipTool, "Sending cluster (0x0300) command (0x06) on endpoint %" PRIu16, endpointId);
ModelCommand::AddArguments();
}
+ ~ReadColorControlCurrentSaturation()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
+
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
ChipLogProgress(chipTool, "Sending cluster (0x0300) command (0x00) on endpoint %" PRIu16, endpointId);
ModelCommand::AddArguments();
}
+ ~ReportColorControlCurrentSaturation()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ delete onReportCallback;
+ }
+
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
ChipLogProgress(chipTool, "Sending cluster (0x0300) command (0x06) on endpoint %" PRIu16, endpointId);
ModelCommand::AddArguments();
}
+ ~ReadColorControlRemainingTime()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
+
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
ChipLogProgress(chipTool, "Sending cluster (0x0300) command (0x00) on endpoint %" PRIu16, endpointId);
ModelCommand::AddArguments();
}
+ ~ReadColorControlCurrentX()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
+
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
ChipLogProgress(chipTool, "Sending cluster (0x0300) command (0x00) on endpoint %" PRIu16, endpointId);
ModelCommand::AddArguments();
}
+ ~ReportColorControlCurrentX()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ delete onReportCallback;
+ }
+
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
ChipLogProgress(chipTool, "Sending cluster (0x0300) command (0x06) on endpoint %" PRIu16, endpointId);
ModelCommand::AddArguments();
}
+ ~ReadColorControlCurrentY()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
+
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
ChipLogProgress(chipTool, "Sending cluster (0x0300) command (0x00) on endpoint %" PRIu16, endpointId);
ModelCommand::AddArguments();
}
+ ~ReportColorControlCurrentY()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ delete onReportCallback;
+ }
+
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
ChipLogProgress(chipTool, "Sending cluster (0x0300) command (0x06) on endpoint %" PRIu16, endpointId);
ModelCommand::AddArguments();
}
+ ~ReadColorControlDriftCompensation()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
+
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
ChipLogProgress(chipTool, "Sending cluster (0x0300) command (0x00) on endpoint %" PRIu16, endpointId);
ModelCommand::AddArguments();
}
+ ~ReadColorControlCompensationText()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
+
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
ChipLogProgress(chipTool, "Sending cluster (0x0300) command (0x00) on endpoint %" PRIu16, endpointId);
ModelCommand::AddArguments();
}
+ ~ReadColorControlColorTemperature()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
+
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
ChipLogProgress(chipTool, "Sending cluster (0x0300) command (0x00) on endpoint %" PRIu16, endpointId);
ModelCommand::AddArguments();
}
+ ~ReportColorControlColorTemperature()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ delete onReportCallback;
+ }
+
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
ChipLogProgress(chipTool, "Sending cluster (0x0300) command (0x06) on endpoint %" PRIu16, endpointId);
ModelCommand::AddArguments();
}
+ ~ReadColorControlColorMode()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
+
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
ChipLogProgress(chipTool, "Sending cluster (0x0300) command (0x00) on endpoint %" PRIu16, endpointId);
ModelCommand::AddArguments();
}
+ ~ReadColorControlColorControlOptions()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
+
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
ChipLogProgress(chipTool, "Sending cluster (0x0300) command (0x00) on endpoint %" PRIu16, endpointId);
ModelCommand::AddArguments();
}
+ ~WriteColorControlColorControlOptions()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
+
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
ChipLogProgress(chipTool, "Sending cluster (0x0300) command (0x01) on endpoint %" PRIu16, endpointId);
ModelCommand::AddArguments();
}
+ ~ReadColorControlNumberOfPrimaries()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
+
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
ChipLogProgress(chipTool, "Sending cluster (0x0300) command (0x00) on endpoint %" PRIu16, endpointId);
ModelCommand::AddArguments();
}
+ ~ReadColorControlPrimary1X()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
+
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
ChipLogProgress(chipTool, "Sending cluster (0x0300) command (0x00) on endpoint %" PRIu16, endpointId);
ModelCommand::AddArguments();
}
+ ~ReadColorControlPrimary1Y()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
+
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
ChipLogProgress(chipTool, "Sending cluster (0x0300) command (0x00) on endpoint %" PRIu16, endpointId);
ModelCommand::AddArguments();
}
+ ~ReadColorControlPrimary1Intensity()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
+
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
ChipLogProgress(chipTool, "Sending cluster (0x0300) command (0x00) on endpoint %" PRIu16, endpointId);
ModelCommand::AddArguments();
}
+ ~ReadColorControlPrimary2X()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
+
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
ChipLogProgress(chipTool, "Sending cluster (0x0300) command (0x00) on endpoint %" PRIu16, endpointId);
ModelCommand::AddArguments();
}
+ ~ReadColorControlPrimary2Y()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
+
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
ChipLogProgress(chipTool, "Sending cluster (0x0300) command (0x00) on endpoint %" PRIu16, endpointId);
ModelCommand::AddArguments();
}
+ ~ReadColorControlPrimary2Intensity()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
+
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
ChipLogProgress(chipTool, "Sending cluster (0x0300) command (0x00) on endpoint %" PRIu16, endpointId);
ModelCommand::AddArguments();
}
+ ~ReadColorControlPrimary3X()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
+
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
ChipLogProgress(chipTool, "Sending cluster (0x0300) command (0x00) on endpoint %" PRIu16, endpointId);
ModelCommand::AddArguments();
}
+ ~ReadColorControlPrimary3Y()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
+
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
ChipLogProgress(chipTool, "Sending cluster (0x0300) command (0x00) on endpoint %" PRIu16, endpointId);
ModelCommand::AddArguments();
}
+ ~ReadColorControlPrimary3Intensity()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
+
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
ChipLogProgress(chipTool, "Sending cluster (0x0300) command (0x00) on endpoint %" PRIu16, endpointId);
ModelCommand::AddArguments();
}
+ ~ReadColorControlPrimary4X()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
+
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
ChipLogProgress(chipTool, "Sending cluster (0x0300) command (0x00) on endpoint %" PRIu16, endpointId);
ModelCommand::AddArguments();
}
+ ~ReadColorControlPrimary4Y()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
+
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
ChipLogProgress(chipTool, "Sending cluster (0x0300) command (0x00) on endpoint %" PRIu16, endpointId);
ModelCommand::AddArguments();
}
+ ~ReadColorControlPrimary4Intensity()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
+
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
ChipLogProgress(chipTool, "Sending cluster (0x0300) command (0x00) on endpoint %" PRIu16, endpointId);
ModelCommand::AddArguments();
}
+ ~ReadColorControlPrimary5X()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
+
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
ChipLogProgress(chipTool, "Sending cluster (0x0300) command (0x00) on endpoint %" PRIu16, endpointId);
ModelCommand::AddArguments();
}
+ ~ReadColorControlPrimary5Y()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
+
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
ChipLogProgress(chipTool, "Sending cluster (0x0300) command (0x00) on endpoint %" PRIu16, endpointId);
ModelCommand::AddArguments();
}
+ ~ReadColorControlPrimary5Intensity()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
+
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
ChipLogProgress(chipTool, "Sending cluster (0x0300) command (0x00) on endpoint %" PRIu16, endpointId);
ModelCommand::AddArguments();
}
+ ~ReadColorControlPrimary6X()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
+
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
ChipLogProgress(chipTool, "Sending cluster (0x0300) command (0x00) on endpoint %" PRIu16, endpointId);
ModelCommand::AddArguments();
}
+ ~ReadColorControlPrimary6Y()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
+
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
ChipLogProgress(chipTool, "Sending cluster (0x0300) command (0x00) on endpoint %" PRIu16, endpointId);
ModelCommand::AddArguments();
}
+ ~ReadColorControlPrimary6Intensity()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
+
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
ChipLogProgress(chipTool, "Sending cluster (0x0300) command (0x00) on endpoint %" PRIu16, endpointId);
ModelCommand::AddArguments();
}
- CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
+ ~ReadColorControlWhitePointX()
{
- ChipLogProgress(chipTool, "Sending cluster (0x0300) command (0x00) on endpoint %" PRIu16, endpointId);
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
+
+ CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
+ {
+ ChipLogProgress(chipTool, "Sending cluster (0x0300) command (0x00) on endpoint %" PRIu16, endpointId);
chip::Controller::ColorControlCluster cluster;
cluster.Associate(device, endpointId);
ModelCommand::AddArguments();
}
+ ~WriteColorControlWhitePointX()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
+
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
ChipLogProgress(chipTool, "Sending cluster (0x0300) command (0x01) on endpoint %" PRIu16, endpointId);
ModelCommand::AddArguments();
}
+ ~ReadColorControlWhitePointY()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
+
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
ChipLogProgress(chipTool, "Sending cluster (0x0300) command (0x00) on endpoint %" PRIu16, endpointId);
ModelCommand::AddArguments();
}
+ ~WriteColorControlWhitePointY()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
+
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
ChipLogProgress(chipTool, "Sending cluster (0x0300) command (0x01) on endpoint %" PRIu16, endpointId);
ModelCommand::AddArguments();
}
+ ~ReadColorControlColorPointRX()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
+
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
ChipLogProgress(chipTool, "Sending cluster (0x0300) command (0x00) on endpoint %" PRIu16, endpointId);
ModelCommand::AddArguments();
}
+ ~WriteColorControlColorPointRX()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
+
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
ChipLogProgress(chipTool, "Sending cluster (0x0300) command (0x01) on endpoint %" PRIu16, endpointId);
ModelCommand::AddArguments();
}
+ ~ReadColorControlColorPointRY()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
+
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
ChipLogProgress(chipTool, "Sending cluster (0x0300) command (0x00) on endpoint %" PRIu16, endpointId);
ModelCommand::AddArguments();
}
+ ~WriteColorControlColorPointRY()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
+
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
ChipLogProgress(chipTool, "Sending cluster (0x0300) command (0x01) on endpoint %" PRIu16, endpointId);
ModelCommand::AddArguments();
}
+ ~ReadColorControlColorPointRIntensity()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
+
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
ChipLogProgress(chipTool, "Sending cluster (0x0300) command (0x00) on endpoint %" PRIu16, endpointId);
ModelCommand::AddArguments();
}
+ ~WriteColorControlColorPointRIntensity()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
+
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
ChipLogProgress(chipTool, "Sending cluster (0x0300) command (0x01) on endpoint %" PRIu16, endpointId);
ModelCommand::AddArguments();
}
+ ~ReadColorControlColorPointGX()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
+
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
ChipLogProgress(chipTool, "Sending cluster (0x0300) command (0x00) on endpoint %" PRIu16, endpointId);
ModelCommand::AddArguments();
}
+ ~WriteColorControlColorPointGX()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
+
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
ChipLogProgress(chipTool, "Sending cluster (0x0300) command (0x01) on endpoint %" PRIu16, endpointId);
ModelCommand::AddArguments();
}
+ ~ReadColorControlColorPointGY()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
+
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
ChipLogProgress(chipTool, "Sending cluster (0x0300) command (0x00) on endpoint %" PRIu16, endpointId);
ModelCommand::AddArguments();
}
+ ~WriteColorControlColorPointGY()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
+
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
ChipLogProgress(chipTool, "Sending cluster (0x0300) command (0x01) on endpoint %" PRIu16, endpointId);
ModelCommand::AddArguments();
}
+ ~ReadColorControlColorPointGIntensity()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
+
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
ChipLogProgress(chipTool, "Sending cluster (0x0300) command (0x00) on endpoint %" PRIu16, endpointId);
ModelCommand::AddArguments();
}
+ ~WriteColorControlColorPointGIntensity()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
+
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
ChipLogProgress(chipTool, "Sending cluster (0x0300) command (0x01) on endpoint %" PRIu16, endpointId);
ModelCommand::AddArguments();
}
+ ~ReadColorControlColorPointBX()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
+
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
ChipLogProgress(chipTool, "Sending cluster (0x0300) command (0x00) on endpoint %" PRIu16, endpointId);
ModelCommand::AddArguments();
}
+ ~WriteColorControlColorPointBX()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
+
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
ChipLogProgress(chipTool, "Sending cluster (0x0300) command (0x01) on endpoint %" PRIu16, endpointId);
ModelCommand::AddArguments();
}
+ ~ReadColorControlColorPointBY()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
+
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
ChipLogProgress(chipTool, "Sending cluster (0x0300) command (0x00) on endpoint %" PRIu16, endpointId);
ModelCommand::AddArguments();
}
+ ~WriteColorControlColorPointBY()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
+
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
ChipLogProgress(chipTool, "Sending cluster (0x0300) command (0x01) on endpoint %" PRIu16, endpointId);
ModelCommand::AddArguments();
}
+ ~ReadColorControlColorPointBIntensity()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
+
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
ChipLogProgress(chipTool, "Sending cluster (0x0300) command (0x00) on endpoint %" PRIu16, endpointId);
ModelCommand::AddArguments();
}
+ ~WriteColorControlColorPointBIntensity()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
+
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
ChipLogProgress(chipTool, "Sending cluster (0x0300) command (0x01) on endpoint %" PRIu16, endpointId);
ModelCommand::AddArguments();
}
+ ~ReadColorControlEnhancedCurrentHue()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
+
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
ChipLogProgress(chipTool, "Sending cluster (0x0300) command (0x00) on endpoint %" PRIu16, endpointId);
ModelCommand::AddArguments();
}
+ ~ReadColorControlEnhancedColorMode()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
+
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
ChipLogProgress(chipTool, "Sending cluster (0x0300) command (0x00) on endpoint %" PRIu16, endpointId);
ModelCommand::AddArguments();
}
+ ~ReadColorControlColorLoopActive()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
+
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
ChipLogProgress(chipTool, "Sending cluster (0x0300) command (0x00) on endpoint %" PRIu16, endpointId);
ModelCommand::AddArguments();
}
+ ~ReadColorControlColorLoopDirection()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
+
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
ChipLogProgress(chipTool, "Sending cluster (0x0300) command (0x00) on endpoint %" PRIu16, endpointId);
ModelCommand::AddArguments();
}
+ ~ReadColorControlColorLoopTime()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
+
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
ChipLogProgress(chipTool, "Sending cluster (0x0300) command (0x00) on endpoint %" PRIu16, endpointId);
ModelCommand::AddArguments();
}
+ ~ReadColorControlColorCapabilities()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
+
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
ChipLogProgress(chipTool, "Sending cluster (0x0300) command (0x00) on endpoint %" PRIu16, endpointId);
ModelCommand::AddArguments();
}
+ ~ReadColorControlColorTempPhysicalMin()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
+
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
ChipLogProgress(chipTool, "Sending cluster (0x0300) command (0x00) on endpoint %" PRIu16, endpointId);
ModelCommand::AddArguments();
}
+ ~ReadColorControlColorTempPhysicalMax()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
+
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
ChipLogProgress(chipTool, "Sending cluster (0x0300) command (0x00) on endpoint %" PRIu16, endpointId);
ModelCommand::AddArguments();
}
+ ~ReadColorControlCoupleColorTempToLevelMinMireds()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
+
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
ChipLogProgress(chipTool, "Sending cluster (0x0300) command (0x00) on endpoint %" PRIu16, endpointId);
ModelCommand::AddArguments();
}
+ ~ReadColorControlStartUpColorTemperatureMireds()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
+
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
ChipLogProgress(chipTool, "Sending cluster (0x0300) command (0x00) on endpoint %" PRIu16, endpointId);
ModelCommand::AddArguments();
}
+ ~WriteColorControlStartUpColorTemperatureMireds()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
+
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
ChipLogProgress(chipTool, "Sending cluster (0x0300) command (0x01) on endpoint %" PRIu16, endpointId);
ModelCommand::AddArguments();
}
- CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
- {
- ChipLogProgress(chipTool, "Sending cluster (0x0300) command (0x00) on endpoint %" PRIu16, endpointId);
-
- chip::Controller::ColorControlCluster cluster;
- cluster.Associate(device, endpointId);
- return cluster.ReadAttributeClusterRevision(onSuccessCallback->Cancel(), onFailureCallback->Cancel());
- }
-
-private:
- chip::Callback::Callback<Int16uAttributeCallback> * onSuccessCallback =
- new chip::Callback::Callback<Int16uAttributeCallback>(OnInt16uAttributeResponse, this);
- chip::Callback::Callback<DefaultFailureCallback> * onFailureCallback =
- new chip::Callback::Callback<DefaultFailureCallback>(OnDefaultFailureResponse, this);
-};
-
-/*----------------------------------------------------------------------------*\
-| Cluster ContentLaunch | 0xF002 |
-|------------------------------------------------------------------------------|
-| Commands: | |
-| * LaunchContent | 0x00 |
-| * LaunchURL | 0x01 |
-|------------------------------------------------------------------------------|
-| Attributes: | |
-| * ClusterRevision | 0xFFFD |
-\*----------------------------------------------------------------------------*/
-
-/*
- * Command LaunchContent
- */
-class ContentLaunchLaunchContent : public ModelCommand
-{
-public:
- ContentLaunchLaunchContent() : ModelCommand("launch-content") { ModelCommand::AddArguments(); }
-
- CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
- {
- ChipLogProgress(chipTool, "Sending cluster (0xF002) command (0x00) on endpoint %" PRIu16, endpointId);
-
- chip::Controller::ContentLaunchCluster cluster;
- cluster.Associate(device, endpointId);
- return cluster.LaunchContent(onSuccessCallback->Cancel(), onFailureCallback->Cancel());
- }
-
-private:
- chip::Callback::Callback<ContentLaunchClusterLaunchContentResponseCallback> * onSuccessCallback =
- new chip::Callback::Callback<ContentLaunchClusterLaunchContentResponseCallback>(OnContentLaunchClusterLaunchContentResponse,
- this);
- chip::Callback::Callback<DefaultFailureCallback> * onFailureCallback =
- new chip::Callback::Callback<DefaultFailureCallback>(OnDefaultFailureResponse, this);
-};
-
-/*
- * Command LaunchURL
- */
-class ContentLaunchLaunchURL : public ModelCommand
-{
-public:
- ContentLaunchLaunchURL() : ModelCommand("launch-url") { ModelCommand::AddArguments(); }
-
- CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
- {
- ChipLogProgress(chipTool, "Sending cluster (0xF002) command (0x01) on endpoint %" PRIu16, endpointId);
-
- chip::Controller::ContentLaunchCluster cluster;
- cluster.Associate(device, endpointId);
- return cluster.LaunchURL(onSuccessCallback->Cancel(), onFailureCallback->Cancel());
- }
-
-private:
- chip::Callback::Callback<ContentLaunchClusterLaunchURLResponseCallback> * onSuccessCallback =
- new chip::Callback::Callback<ContentLaunchClusterLaunchURLResponseCallback>(OnContentLaunchClusterLaunchURLResponse, this);
- chip::Callback::Callback<DefaultFailureCallback> * onFailureCallback =
- new chip::Callback::Callback<DefaultFailureCallback>(OnDefaultFailureResponse, this);
-};
-
-/*
- * Discover Attributes
- */
-class DiscoverContentLaunchAttributes : public ModelCommand
-{
-public:
- DiscoverContentLaunchAttributes() : ModelCommand("discover") { ModelCommand::AddArguments(); }
-
- CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
- {
- ChipLogProgress(chipTool, "Sending cluster (0x0000) command (0x0C) on endpoint %" PRIu16, endpointId);
-
- chip::Controller::ContentLaunchCluster cluster;
- cluster.Associate(device, endpointId);
- return cluster.DiscoverAttributes(onSuccessCallback->Cancel(), onFailureCallback->Cancel());
- }
-
-private:
- chip::Callback::Callback<DefaultSuccessCallback> * onSuccessCallback =
- new chip::Callback::Callback<DefaultSuccessCallback>(OnDefaultSuccessResponse, this);
- chip::Callback::Callback<DefaultFailureCallback> * onFailureCallback =
- new chip::Callback::Callback<DefaultFailureCallback>(OnDefaultFailureResponse, this);
-};
-
-/*
- * Attribute ClusterRevision
- */
-class ReadContentLaunchClusterRevision : public ModelCommand
-{
-public:
- ReadContentLaunchClusterRevision() : ModelCommand("read")
+ ~ReadColorControlClusterRevision()
{
- AddArgument("attr-name", "cluster-revision");
- ModelCommand::AddArguments();
+ delete onSuccessCallback;
+ delete onFailureCallback;
}
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
- ChipLogProgress(chipTool, "Sending cluster (0xF002) command (0x00) on endpoint %" PRIu16, endpointId);
+ ChipLogProgress(chipTool, "Sending cluster (0x0300) command (0x00) on endpoint %" PRIu16, endpointId);
- chip::Controller::ContentLaunchCluster cluster;
+ chip::Controller::ColorControlCluster cluster;
cluster.Associate(device, endpointId);
return cluster.ReadAttributeClusterRevision(onSuccessCallback->Cancel(), onFailureCallback->Cancel());
}
{
public:
DoorLockClearAllPins() : ModelCommand("clear-all-pins") { ModelCommand::AddArguments(); }
+ ~DoorLockClearAllPins()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
{
public:
DoorLockClearAllRfids() : ModelCommand("clear-all-rfids") { ModelCommand::AddArguments(); }
+ ~DoorLockClearAllRfids()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
AddArgument("scheduleId", 0, UINT8_MAX, &mScheduleId);
ModelCommand::AddArguments();
}
+ ~DoorLockClearHolidaySchedule()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
AddArgument("userId", 0, UINT16_MAX, &mUserId);
ModelCommand::AddArguments();
}
+ ~DoorLockClearPin()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
AddArgument("userId", 0, UINT16_MAX, &mUserId);
ModelCommand::AddArguments();
}
+ ~DoorLockClearRfid()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
AddArgument("userId", 0, UINT16_MAX, &mUserId);
ModelCommand::AddArguments();
}
+ ~DoorLockClearWeekdaySchedule()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
AddArgument("userId", 0, UINT16_MAX, &mUserId);
ModelCommand::AddArguments();
}
+ ~DoorLockClearYeardaySchedule()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
AddArgument("scheduleId", 0, UINT8_MAX, &mScheduleId);
ModelCommand::AddArguments();
}
+ ~DoorLockGetHolidaySchedule()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
AddArgument("logIndex", 0, UINT16_MAX, &mLogIndex);
ModelCommand::AddArguments();
}
+ ~DoorLockGetLogRecord()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
AddArgument("userId", 0, UINT16_MAX, &mUserId);
ModelCommand::AddArguments();
}
+ ~DoorLockGetPin()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
AddArgument("userId", 0, UINT16_MAX, &mUserId);
ModelCommand::AddArguments();
}
+ ~DoorLockGetRfid()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
AddArgument("userId", 0, UINT16_MAX, &mUserId);
ModelCommand::AddArguments();
}
+ ~DoorLockGetUserType()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
AddArgument("userId", 0, UINT16_MAX, &mUserId);
ModelCommand::AddArguments();
}
+ ~DoorLockGetWeekdaySchedule()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
AddArgument("userId", 0, UINT16_MAX, &mUserId);
ModelCommand::AddArguments();
}
+ ~DoorLockGetYeardaySchedule()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
AddArgument("pin", &mPin);
ModelCommand::AddArguments();
}
+ ~DoorLockLockDoor()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
AddArgument("operatingModeDuringHoliday", 0, UINT8_MAX, &mOperatingModeDuringHoliday);
ModelCommand::AddArguments();
}
+ ~DoorLockSetHolidaySchedule()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
AddArgument("pin", &mPin);
ModelCommand::AddArguments();
}
+ ~DoorLockSetPin()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
AddArgument("id", &mId);
ModelCommand::AddArguments();
}
+ ~DoorLockSetRfid()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
AddArgument("userType", 0, UINT8_MAX, &mUserType);
ModelCommand::AddArguments();
}
+ ~DoorLockSetUserType()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
AddArgument("endMinute", 0, UINT8_MAX, &mEndMinute);
ModelCommand::AddArguments();
}
+ ~DoorLockSetWeekdaySchedule()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
AddArgument("localEndTime", 0, UINT32_MAX, &mLocalEndTime);
ModelCommand::AddArguments();
}
+ ~DoorLockSetYeardaySchedule()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
AddArgument("pin", &mPin);
ModelCommand::AddArguments();
}
+ ~DoorLockUnlockDoor()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
AddArgument("pin", &mPin);
ModelCommand::AddArguments();
}
+ ~DoorLockUnlockWithTimeout()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
public:
DiscoverDoorLockAttributes() : ModelCommand("discover") { ModelCommand::AddArguments(); }
+ ~DiscoverDoorLockAttributes()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
+
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
ChipLogProgress(chipTool, "Sending cluster (0x0000) command (0x0C) on endpoint %" PRIu16, endpointId);
ModelCommand::AddArguments();
}
+ ~ReadDoorLockLockState()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
+
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
ChipLogProgress(chipTool, "Sending cluster (0x0101) command (0x00) on endpoint %" PRIu16, endpointId);
ModelCommand::AddArguments();
}
+ ~ReportDoorLockLockState()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ delete onReportCallback;
+ }
+
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
ChipLogProgress(chipTool, "Sending cluster (0x0101) command (0x06) on endpoint %" PRIu16, endpointId);
ModelCommand::AddArguments();
}
+ ~ReadDoorLockLockType()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
+
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
ChipLogProgress(chipTool, "Sending cluster (0x0101) command (0x00) on endpoint %" PRIu16, endpointId);
ModelCommand::AddArguments();
}
+ ~ReadDoorLockActuatorEnabled()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
+
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
ChipLogProgress(chipTool, "Sending cluster (0x0101) command (0x00) on endpoint %" PRIu16, endpointId);
ModelCommand::AddArguments();
}
+ ~ReadDoorLockClusterRevision()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
+
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
ChipLogProgress(chipTool, "Sending cluster (0x0101) command (0x00) on endpoint %" PRIu16, endpointId);
AddArgument("timeoutMs", 0, UINT32_MAX, &mTimeoutMs);
ModelCommand::AddArguments();
}
+ ~GeneralCommissioningArmFailSafe()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
{
public:
GeneralCommissioningCommissioningComplete() : ModelCommand("commissioning-complete") { ModelCommand::AddArguments(); }
+ ~GeneralCommissioningCommissioningComplete()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
AddArgument("timeoutMs", 0, UINT32_MAX, &mTimeoutMs);
ModelCommand::AddArguments();
}
+ ~GeneralCommissioningSetFabric()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
public:
DiscoverGeneralCommissioningAttributes() : ModelCommand("discover") { ModelCommand::AddArguments(); }
+ ~DiscoverGeneralCommissioningAttributes()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
+
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
ChipLogProgress(chipTool, "Sending cluster (0x0000) command (0x0C) on endpoint %" PRIu16, endpointId);
ModelCommand::AddArguments();
}
+ ~ReadGeneralCommissioningFabricId()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
+
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
ChipLogProgress(chipTool, "Sending cluster (0x0030) command (0x00) on endpoint %" PRIu16, endpointId);
ModelCommand::AddArguments();
}
+ ~ReadGeneralCommissioningBreadcrumb()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
+
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
ChipLogProgress(chipTool, "Sending cluster (0x0030) command (0x00) on endpoint %" PRIu16, endpointId);
ModelCommand::AddArguments();
}
+ ~WriteGeneralCommissioningBreadcrumb()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
+
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
ChipLogProgress(chipTool, "Sending cluster (0x0030) command (0x01) on endpoint %" PRIu16, endpointId);
ModelCommand::AddArguments();
}
+ ~ReadGeneralCommissioningClusterRevision()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
+
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
ChipLogProgress(chipTool, "Sending cluster (0x0030) command (0x00) on endpoint %" PRIu16, endpointId);
AddArgument("groupName", &mGroupName);
ModelCommand::AddArguments();
}
+ ~GroupsAddGroup()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
AddArgument("groupName", &mGroupName);
ModelCommand::AddArguments();
}
+ ~GroupsAddGroupIfIdentifying()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
AddArgument("groupList", 0, UINT16_MAX, &mGroupList);
ModelCommand::AddArguments();
}
+ ~GroupsGetGroupMembership()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
{
public:
GroupsRemoveAllGroups() : ModelCommand("remove-all-groups") { ModelCommand::AddArguments(); }
+ ~GroupsRemoveAllGroups()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
AddArgument("groupId", 0, UINT16_MAX, &mGroupId);
ModelCommand::AddArguments();
}
+ ~GroupsRemoveGroup()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
AddArgument("groupId", 0, UINT16_MAX, &mGroupId);
ModelCommand::AddArguments();
}
+ ~GroupsViewGroup()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
public:
DiscoverGroupsAttributes() : ModelCommand("discover") { ModelCommand::AddArguments(); }
+ ~DiscoverGroupsAttributes()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
+
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
ChipLogProgress(chipTool, "Sending cluster (0x0000) command (0x0C) on endpoint %" PRIu16, endpointId);
ModelCommand::AddArguments();
}
+ ~ReadGroupsNameSupport()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
+
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
ChipLogProgress(chipTool, "Sending cluster (0x0004) command (0x00) on endpoint %" PRIu16, endpointId);
ModelCommand::AddArguments();
}
+ ~ReadGroupsClusterRevision()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
+
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
ChipLogProgress(chipTool, "Sending cluster (0x0004) command (0x00) on endpoint %" PRIu16, endpointId);
AddArgument("identifyTime", 0, UINT16_MAX, &mIdentifyTime);
ModelCommand::AddArguments();
}
+ ~IdentifyIdentify()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
{
public:
IdentifyIdentifyQuery() : ModelCommand("identify-query") { ModelCommand::AddArguments(); }
+ ~IdentifyIdentifyQuery()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
public:
DiscoverIdentifyAttributes() : ModelCommand("discover") { ModelCommand::AddArguments(); }
+ ~DiscoverIdentifyAttributes()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
+
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
ChipLogProgress(chipTool, "Sending cluster (0x0000) command (0x0C) on endpoint %" PRIu16, endpointId);
ModelCommand::AddArguments();
}
+ ~ReadIdentifyIdentifyTime()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
+
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
ChipLogProgress(chipTool, "Sending cluster (0x0003) command (0x00) on endpoint %" PRIu16, endpointId);
ModelCommand::AddArguments();
}
+ ~WriteIdentifyIdentifyTime()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
+
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
ChipLogProgress(chipTool, "Sending cluster (0x0003) command (0x01) on endpoint %" PRIu16, endpointId);
ModelCommand::AddArguments();
}
+ ~ReadIdentifyClusterRevision()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
+
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
ChipLogProgress(chipTool, "Sending cluster (0x0003) command (0x00) on endpoint %" PRIu16, endpointId);
AddArgument("optionOverride", 0, UINT8_MAX, &mOptionOverride);
ModelCommand::AddArguments();
}
+ ~LevelControlMove()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
AddArgument("optionOverride", 0, UINT8_MAX, &mOptionOverride);
ModelCommand::AddArguments();
}
+ ~LevelControlMoveToLevel()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
AddArgument("transitionTime", 0, UINT16_MAX, &mTransitionTime);
ModelCommand::AddArguments();
}
+ ~LevelControlMoveToLevelWithOnOff()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
AddArgument("rate", 0, UINT8_MAX, &mRate);
ModelCommand::AddArguments();
}
+ ~LevelControlMoveWithOnOff()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
AddArgument("optionOverride", 0, UINT8_MAX, &mOptionOverride);
ModelCommand::AddArguments();
}
+ ~LevelControlStep()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
AddArgument("transitionTime", 0, UINT16_MAX, &mTransitionTime);
ModelCommand::AddArguments();
}
+ ~LevelControlStepWithOnOff()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
AddArgument("optionOverride", 0, UINT8_MAX, &mOptionOverride);
ModelCommand::AddArguments();
}
+ ~LevelControlStop()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
{
public:
LevelControlStopWithOnOff() : ModelCommand("stop-with-on-off") { ModelCommand::AddArguments(); }
+ ~LevelControlStopWithOnOff()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
public:
DiscoverLevelControlAttributes() : ModelCommand("discover") { ModelCommand::AddArguments(); }
+ ~DiscoverLevelControlAttributes()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
+
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
ChipLogProgress(chipTool, "Sending cluster (0x0000) command (0x0C) on endpoint %" PRIu16, endpointId);
ModelCommand::AddArguments();
}
+ ~ReadLevelControlCurrentLevel()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
+
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
ChipLogProgress(chipTool, "Sending cluster (0x0008) command (0x00) on endpoint %" PRIu16, endpointId);
ModelCommand::AddArguments();
}
+ ~ReportLevelControlCurrentLevel()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ delete onReportCallback;
+ }
+
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
ChipLogProgress(chipTool, "Sending cluster (0x0008) command (0x06) on endpoint %" PRIu16, endpointId);
ModelCommand::AddArguments();
}
+ ~ReadLevelControlClusterRevision()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
+
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
ChipLogProgress(chipTool, "Sending cluster (0x0008) command (0x00) on endpoint %" PRIu16, endpointId);
{
public:
LowPowerSleep() : ModelCommand("sleep") { ModelCommand::AddArguments(); }
+ ~LowPowerSleep()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
public:
DiscoverLowPowerAttributes() : ModelCommand("discover") { ModelCommand::AddArguments(); }
+ ~DiscoverLowPowerAttributes()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
+
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
ChipLogProgress(chipTool, "Sending cluster (0x0000) command (0x0C) on endpoint %" PRIu16, endpointId);
ModelCommand::AddArguments();
}
- CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
- {
- ChipLogProgress(chipTool, "Sending cluster (0x0508) command (0x00) on endpoint %" PRIu16, endpointId);
-
- chip::Controller::LowPowerCluster cluster;
- cluster.Associate(device, endpointId);
- return cluster.ReadAttributeClusterRevision(onSuccessCallback->Cancel(), onFailureCallback->Cancel());
- }
-
-private:
- chip::Callback::Callback<Int16uAttributeCallback> * onSuccessCallback =
- new chip::Callback::Callback<Int16uAttributeCallback>(OnInt16uAttributeResponse, this);
- chip::Callback::Callback<DefaultFailureCallback> * onFailureCallback =
- new chip::Callback::Callback<DefaultFailureCallback>(OnDefaultFailureResponse, this);
-};
-
-/*----------------------------------------------------------------------------*\
-| Cluster MediaPlayback | 0xF001 |
-|------------------------------------------------------------------------------|
-| Commands: | |
-| * FastForwardRequest | 0x07 |
-| * NextRequest | 0x05 |
-| * PauseRequest | 0x01 |
-| * PlayRequest | 0x00 |
-| * PreviousRequest | 0x04 |
-| * RewindRequest | 0x06 |
-| * SkipBackwardRequest | 0x09 |
-| * SkipForwardRequest | 0x08 |
-| * StartOverRequest | 0x03 |
-| * StopRequest | 0x02 |
-|------------------------------------------------------------------------------|
-| Attributes: | |
-| * CurrentState | 0x0000 |
-| * ClusterRevision | 0xFFFD |
-\*----------------------------------------------------------------------------*/
-
-/*
- * Command FastForwardRequest
- */
-class MediaPlaybackFastForwardRequest : public ModelCommand
-{
-public:
- MediaPlaybackFastForwardRequest() : ModelCommand("fast-forward-request") { ModelCommand::AddArguments(); }
-
- CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
- {
- ChipLogProgress(chipTool, "Sending cluster (0xF001) command (0x07) on endpoint %" PRIu16, endpointId);
-
- chip::Controller::MediaPlaybackCluster cluster;
- cluster.Associate(device, endpointId);
- return cluster.FastForwardRequest(onSuccessCallback->Cancel(), onFailureCallback->Cancel());
- }
-
-private:
- chip::Callback::Callback<DefaultSuccessCallback> * onSuccessCallback =
- new chip::Callback::Callback<DefaultSuccessCallback>(OnDefaultSuccessResponse, this);
- chip::Callback::Callback<DefaultFailureCallback> * onFailureCallback =
- new chip::Callback::Callback<DefaultFailureCallback>(OnDefaultFailureResponse, this);
-};
-
-/*
- * Command NextRequest
- */
-class MediaPlaybackNextRequest : public ModelCommand
-{
-public:
- MediaPlaybackNextRequest() : ModelCommand("next-request") { ModelCommand::AddArguments(); }
-
- CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
+ ~ReadLowPowerClusterRevision()
{
- ChipLogProgress(chipTool, "Sending cluster (0xF001) command (0x05) on endpoint %" PRIu16, endpointId);
-
- chip::Controller::MediaPlaybackCluster cluster;
- cluster.Associate(device, endpointId);
- return cluster.NextRequest(onSuccessCallback->Cancel(), onFailureCallback->Cancel());
+ delete onSuccessCallback;
+ delete onFailureCallback;
}
-private:
- chip::Callback::Callback<DefaultSuccessCallback> * onSuccessCallback =
- new chip::Callback::Callback<DefaultSuccessCallback>(OnDefaultSuccessResponse, this);
- chip::Callback::Callback<DefaultFailureCallback> * onFailureCallback =
- new chip::Callback::Callback<DefaultFailureCallback>(OnDefaultFailureResponse, this);
-};
-
-/*
- * Command PauseRequest
- */
-class MediaPlaybackPauseRequest : public ModelCommand
-{
-public:
- MediaPlaybackPauseRequest() : ModelCommand("pause-request") { ModelCommand::AddArguments(); }
-
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
- ChipLogProgress(chipTool, "Sending cluster (0xF001) command (0x01) on endpoint %" PRIu16, endpointId);
-
- chip::Controller::MediaPlaybackCluster cluster;
- cluster.Associate(device, endpointId);
- return cluster.PauseRequest(onSuccessCallback->Cancel(), onFailureCallback->Cancel());
- }
-
-private:
- chip::Callback::Callback<DefaultSuccessCallback> * onSuccessCallback =
- new chip::Callback::Callback<DefaultSuccessCallback>(OnDefaultSuccessResponse, this);
- chip::Callback::Callback<DefaultFailureCallback> * onFailureCallback =
- new chip::Callback::Callback<DefaultFailureCallback>(OnDefaultFailureResponse, this);
-};
-
-/*
- * Command PlayRequest
- */
-class MediaPlaybackPlayRequest : public ModelCommand
-{
-public:
- MediaPlaybackPlayRequest() : ModelCommand("play-request") { ModelCommand::AddArguments(); }
-
- CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
- {
- ChipLogProgress(chipTool, "Sending cluster (0xF001) command (0x00) on endpoint %" PRIu16, endpointId);
-
- chip::Controller::MediaPlaybackCluster cluster;
- cluster.Associate(device, endpointId);
- return cluster.PlayRequest(onSuccessCallback->Cancel(), onFailureCallback->Cancel());
- }
-
-private:
- chip::Callback::Callback<DefaultSuccessCallback> * onSuccessCallback =
- new chip::Callback::Callback<DefaultSuccessCallback>(OnDefaultSuccessResponse, this);
- chip::Callback::Callback<DefaultFailureCallback> * onFailureCallback =
- new chip::Callback::Callback<DefaultFailureCallback>(OnDefaultFailureResponse, this);
-};
-
-/*
- * Command PreviousRequest
- */
-class MediaPlaybackPreviousRequest : public ModelCommand
-{
-public:
- MediaPlaybackPreviousRequest() : ModelCommand("previous-request") { ModelCommand::AddArguments(); }
-
- CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
- {
- ChipLogProgress(chipTool, "Sending cluster (0xF001) command (0x04) on endpoint %" PRIu16, endpointId);
-
- chip::Controller::MediaPlaybackCluster cluster;
- cluster.Associate(device, endpointId);
- return cluster.PreviousRequest(onSuccessCallback->Cancel(), onFailureCallback->Cancel());
- }
-
-private:
- chip::Callback::Callback<DefaultSuccessCallback> * onSuccessCallback =
- new chip::Callback::Callback<DefaultSuccessCallback>(OnDefaultSuccessResponse, this);
- chip::Callback::Callback<DefaultFailureCallback> * onFailureCallback =
- new chip::Callback::Callback<DefaultFailureCallback>(OnDefaultFailureResponse, this);
-};
-
-/*
- * Command RewindRequest
- */
-class MediaPlaybackRewindRequest : public ModelCommand
-{
-public:
- MediaPlaybackRewindRequest() : ModelCommand("rewind-request") { ModelCommand::AddArguments(); }
-
- CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
- {
- ChipLogProgress(chipTool, "Sending cluster (0xF001) command (0x06) on endpoint %" PRIu16, endpointId);
-
- chip::Controller::MediaPlaybackCluster cluster;
- cluster.Associate(device, endpointId);
- return cluster.RewindRequest(onSuccessCallback->Cancel(), onFailureCallback->Cancel());
- }
-
-private:
- chip::Callback::Callback<DefaultSuccessCallback> * onSuccessCallback =
- new chip::Callback::Callback<DefaultSuccessCallback>(OnDefaultSuccessResponse, this);
- chip::Callback::Callback<DefaultFailureCallback> * onFailureCallback =
- new chip::Callback::Callback<DefaultFailureCallback>(OnDefaultFailureResponse, this);
-};
-
-/*
- * Command SkipBackwardRequest
- */
-class MediaPlaybackSkipBackwardRequest : public ModelCommand
-{
-public:
- MediaPlaybackSkipBackwardRequest() : ModelCommand("skip-backward-request") { ModelCommand::AddArguments(); }
-
- CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
- {
- ChipLogProgress(chipTool, "Sending cluster (0xF001) command (0x09) on endpoint %" PRIu16, endpointId);
-
- chip::Controller::MediaPlaybackCluster cluster;
- cluster.Associate(device, endpointId);
- return cluster.SkipBackwardRequest(onSuccessCallback->Cancel(), onFailureCallback->Cancel());
- }
-
-private:
- chip::Callback::Callback<DefaultSuccessCallback> * onSuccessCallback =
- new chip::Callback::Callback<DefaultSuccessCallback>(OnDefaultSuccessResponse, this);
- chip::Callback::Callback<DefaultFailureCallback> * onFailureCallback =
- new chip::Callback::Callback<DefaultFailureCallback>(OnDefaultFailureResponse, this);
-};
-
-/*
- * Command SkipForwardRequest
- */
-class MediaPlaybackSkipForwardRequest : public ModelCommand
-{
-public:
- MediaPlaybackSkipForwardRequest() : ModelCommand("skip-forward-request") { ModelCommand::AddArguments(); }
-
- CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
- {
- ChipLogProgress(chipTool, "Sending cluster (0xF001) command (0x08) on endpoint %" PRIu16, endpointId);
-
- chip::Controller::MediaPlaybackCluster cluster;
- cluster.Associate(device, endpointId);
- return cluster.SkipForwardRequest(onSuccessCallback->Cancel(), onFailureCallback->Cancel());
- }
-
-private:
- chip::Callback::Callback<DefaultSuccessCallback> * onSuccessCallback =
- new chip::Callback::Callback<DefaultSuccessCallback>(OnDefaultSuccessResponse, this);
- chip::Callback::Callback<DefaultFailureCallback> * onFailureCallback =
- new chip::Callback::Callback<DefaultFailureCallback>(OnDefaultFailureResponse, this);
-};
-
-/*
- * Command StartOverRequest
- */
-class MediaPlaybackStartOverRequest : public ModelCommand
-{
-public:
- MediaPlaybackStartOverRequest() : ModelCommand("start-over-request") { ModelCommand::AddArguments(); }
-
- CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
- {
- ChipLogProgress(chipTool, "Sending cluster (0xF001) command (0x03) on endpoint %" PRIu16, endpointId);
-
- chip::Controller::MediaPlaybackCluster cluster;
- cluster.Associate(device, endpointId);
- return cluster.StartOverRequest(onSuccessCallback->Cancel(), onFailureCallback->Cancel());
- }
-
-private:
- chip::Callback::Callback<DefaultSuccessCallback> * onSuccessCallback =
- new chip::Callback::Callback<DefaultSuccessCallback>(OnDefaultSuccessResponse, this);
- chip::Callback::Callback<DefaultFailureCallback> * onFailureCallback =
- new chip::Callback::Callback<DefaultFailureCallback>(OnDefaultFailureResponse, this);
-};
-
-/*
- * Command StopRequest
- */
-class MediaPlaybackStopRequest : public ModelCommand
-{
-public:
- MediaPlaybackStopRequest() : ModelCommand("stop-request") { ModelCommand::AddArguments(); }
-
- CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
- {
- ChipLogProgress(chipTool, "Sending cluster (0xF001) command (0x02) on endpoint %" PRIu16, endpointId);
-
- chip::Controller::MediaPlaybackCluster cluster;
- cluster.Associate(device, endpointId);
- return cluster.StopRequest(onSuccessCallback->Cancel(), onFailureCallback->Cancel());
- }
-
-private:
- chip::Callback::Callback<DefaultSuccessCallback> * onSuccessCallback =
- new chip::Callback::Callback<DefaultSuccessCallback>(OnDefaultSuccessResponse, this);
- chip::Callback::Callback<DefaultFailureCallback> * onFailureCallback =
- new chip::Callback::Callback<DefaultFailureCallback>(OnDefaultFailureResponse, this);
-};
-
-/*
- * Discover Attributes
- */
-class DiscoverMediaPlaybackAttributes : public ModelCommand
-{
-public:
- DiscoverMediaPlaybackAttributes() : ModelCommand("discover") { ModelCommand::AddArguments(); }
-
- CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
- {
- ChipLogProgress(chipTool, "Sending cluster (0x0000) command (0x0C) on endpoint %" PRIu16, endpointId);
-
- chip::Controller::MediaPlaybackCluster cluster;
- cluster.Associate(device, endpointId);
- return cluster.DiscoverAttributes(onSuccessCallback->Cancel(), onFailureCallback->Cancel());
- }
-
-private:
- chip::Callback::Callback<DefaultSuccessCallback> * onSuccessCallback =
- new chip::Callback::Callback<DefaultSuccessCallback>(OnDefaultSuccessResponse, this);
- chip::Callback::Callback<DefaultFailureCallback> * onFailureCallback =
- new chip::Callback::Callback<DefaultFailureCallback>(OnDefaultFailureResponse, this);
-};
-
-/*
- * Attribute CurrentState
- */
-class ReadMediaPlaybackCurrentState : public ModelCommand
-{
-public:
- ReadMediaPlaybackCurrentState() : ModelCommand("read")
- {
- AddArgument("attr-name", "current-state");
- ModelCommand::AddArguments();
- }
-
- CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
- {
- ChipLogProgress(chipTool, "Sending cluster (0xF001) command (0x00) on endpoint %" PRIu16, endpointId);
-
- chip::Controller::MediaPlaybackCluster cluster;
- cluster.Associate(device, endpointId);
- return cluster.ReadAttributeCurrentState(onSuccessCallback->Cancel(), onFailureCallback->Cancel());
- }
-
-private:
- chip::Callback::Callback<Int16uAttributeCallback> * onSuccessCallback =
- new chip::Callback::Callback<Int16uAttributeCallback>(OnInt16uAttributeResponse, this);
- chip::Callback::Callback<DefaultFailureCallback> * onFailureCallback =
- new chip::Callback::Callback<DefaultFailureCallback>(OnDefaultFailureResponse, this);
-};
-
-/*
- * Attribute ClusterRevision
- */
-class ReadMediaPlaybackClusterRevision : public ModelCommand
-{
-public:
- ReadMediaPlaybackClusterRevision() : ModelCommand("read")
- {
- AddArgument("attr-name", "cluster-revision");
- ModelCommand::AddArguments();
- }
-
- CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
- {
- ChipLogProgress(chipTool, "Sending cluster (0xF001) command (0x00) on endpoint %" PRIu16, endpointId);
+ ChipLogProgress(chipTool, "Sending cluster (0x0508) command (0x00) on endpoint %" PRIu16, endpointId);
- chip::Controller::MediaPlaybackCluster cluster;
+ chip::Controller::LowPowerCluster cluster;
cluster.Associate(device, endpointId);
return cluster.ReadAttributeClusterRevision(onSuccessCallback->Cancel(), onFailureCallback->Cancel());
}
{
public:
OnOffOff() : ModelCommand("off") { ModelCommand::AddArguments(); }
+ ~OnOffOff()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
{
public:
OnOffOn() : ModelCommand("on") { ModelCommand::AddArguments(); }
+ ~OnOffOn()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
{
public:
OnOffToggle() : ModelCommand("toggle") { ModelCommand::AddArguments(); }
+ ~OnOffToggle()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
public:
DiscoverOnOffAttributes() : ModelCommand("discover") { ModelCommand::AddArguments(); }
+ ~DiscoverOnOffAttributes()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
+
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
ChipLogProgress(chipTool, "Sending cluster (0x0000) command (0x0C) on endpoint %" PRIu16, endpointId);
ModelCommand::AddArguments();
}
+ ~ReadOnOffOnOff()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
+
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
ChipLogProgress(chipTool, "Sending cluster (0x0006) command (0x00) on endpoint %" PRIu16, endpointId);
ModelCommand::AddArguments();
}
+ ~ReportOnOffOnOff()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ delete onReportCallback;
+ }
+
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
ChipLogProgress(chipTool, "Sending cluster (0x0006) command (0x06) on endpoint %" PRIu16, endpointId);
ModelCommand::AddArguments();
}
+ ~ReadOnOffClusterRevision()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
+
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
ChipLogProgress(chipTool, "Sending cluster (0x0006) command (0x00) on endpoint %" PRIu16, endpointId);
AddArgument("value", 0, UINT8_MAX, &mValue);
ModelCommand::AddArguments();
}
+ ~ScenesAddScene()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
AddArgument("groupId", 0, UINT16_MAX, &mGroupId);
ModelCommand::AddArguments();
}
+ ~ScenesGetSceneMembership()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
AddArgument("transitionTime", 0, UINT16_MAX, &mTransitionTime);
ModelCommand::AddArguments();
}
+ ~ScenesRecallScene()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
AddArgument("groupId", 0, UINT16_MAX, &mGroupId);
ModelCommand::AddArguments();
}
+ ~ScenesRemoveAllScenes()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
AddArgument("sceneId", 0, UINT8_MAX, &mSceneId);
ModelCommand::AddArguments();
}
+ ~ScenesRemoveScene()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
AddArgument("sceneId", 0, UINT8_MAX, &mSceneId);
ModelCommand::AddArguments();
}
+ ~ScenesStoreScene()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
AddArgument("sceneId", 0, UINT8_MAX, &mSceneId);
ModelCommand::AddArguments();
}
+ ~ScenesViewScene()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
public:
DiscoverScenesAttributes() : ModelCommand("discover") { ModelCommand::AddArguments(); }
+ ~DiscoverScenesAttributes()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
+
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
ChipLogProgress(chipTool, "Sending cluster (0x0000) command (0x0C) on endpoint %" PRIu16, endpointId);
ModelCommand::AddArguments();
}
+ ~ReadScenesSceneCount()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
+
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
ChipLogProgress(chipTool, "Sending cluster (0x0005) command (0x00) on endpoint %" PRIu16, endpointId);
ModelCommand::AddArguments();
}
+ ~ReadScenesCurrentScene()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
+
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
ChipLogProgress(chipTool, "Sending cluster (0x0005) command (0x00) on endpoint %" PRIu16, endpointId);
ModelCommand::AddArguments();
}
+ ~ReadScenesCurrentGroup()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
+
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
ChipLogProgress(chipTool, "Sending cluster (0x0005) command (0x00) on endpoint %" PRIu16, endpointId);
ModelCommand::AddArguments();
}
+ ~ReadScenesSceneValid()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
+
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
ChipLogProgress(chipTool, "Sending cluster (0x0005) command (0x00) on endpoint %" PRIu16, endpointId);
ModelCommand::AddArguments();
}
+ ~ReadScenesNameSupport()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
+
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
ChipLogProgress(chipTool, "Sending cluster (0x0005) command (0x00) on endpoint %" PRIu16, endpointId);
ModelCommand::AddArguments();
}
+ ~ReadScenesClusterRevision()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
+
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
ChipLogProgress(chipTool, "Sending cluster (0x0005) command (0x00) on endpoint %" PRIu16, endpointId);
public:
DiscoverTemperatureMeasurementAttributes() : ModelCommand("discover") { ModelCommand::AddArguments(); }
+ ~DiscoverTemperatureMeasurementAttributes()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
+
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
ChipLogProgress(chipTool, "Sending cluster (0x0000) command (0x0C) on endpoint %" PRIu16, endpointId);
ModelCommand::AddArguments();
}
+ ~ReadTemperatureMeasurementMeasuredValue()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
+
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
ChipLogProgress(chipTool, "Sending cluster (0x0402) command (0x00) on endpoint %" PRIu16, endpointId);
ModelCommand::AddArguments();
}
+ ~ReportTemperatureMeasurementMeasuredValue()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ delete onReportCallback;
+ }
+
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
ChipLogProgress(chipTool, "Sending cluster (0x0402) command (0x06) on endpoint %" PRIu16, endpointId);
ModelCommand::AddArguments();
}
+ ~ReadTemperatureMeasurementMinMeasuredValue()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
+
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
ChipLogProgress(chipTool, "Sending cluster (0x0402) command (0x00) on endpoint %" PRIu16, endpointId);
ModelCommand::AddArguments();
}
+ ~ReadTemperatureMeasurementMaxMeasuredValue()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
+
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
ChipLogProgress(chipTool, "Sending cluster (0x0402) command (0x00) on endpoint %" PRIu16, endpointId);
ModelCommand::AddArguments();
}
+ ~ReadTemperatureMeasurementClusterRevision()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
+
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
ChipLogProgress(chipTool, "Sending cluster (0x0402) command (0x00) on endpoint %" PRIu16, endpointId);
commands.Register(clusterName, clusterCommands);
}
-void registerClusterContentLaunch(Commands & commands)
-{
- const char * clusterName = "ContentLaunch";
-
- commands_list clusterCommands = {
- make_unique<ContentLaunchLaunchContent>(),
- make_unique<ContentLaunchLaunchURL>(),
- make_unique<DiscoverContentLaunchAttributes>(),
- make_unique<ReadContentLaunchClusterRevision>(),
- };
-
- commands.Register(clusterName, clusterCommands);
-}
void registerClusterDoorLock(Commands & commands)
{
const char * clusterName = "DoorLock";
commands.Register(clusterName, clusterCommands);
}
-void registerClusterMediaPlayback(Commands & commands)
-{
- const char * clusterName = "MediaPlayback";
-
- commands_list clusterCommands = {
- make_unique<MediaPlaybackFastForwardRequest>(), make_unique<MediaPlaybackNextRequest>(),
- make_unique<MediaPlaybackPauseRequest>(), make_unique<MediaPlaybackPlayRequest>(),
- make_unique<MediaPlaybackPreviousRequest>(), make_unique<MediaPlaybackRewindRequest>(),
- make_unique<MediaPlaybackSkipBackwardRequest>(), make_unique<MediaPlaybackSkipForwardRequest>(),
- make_unique<MediaPlaybackStartOverRequest>(), make_unique<MediaPlaybackStopRequest>(),
- make_unique<DiscoverMediaPlaybackAttributes>(), make_unique<ReadMediaPlaybackCurrentState>(),
- make_unique<ReadMediaPlaybackClusterRevision>(),
- };
-
- commands.Register(clusterName, clusterCommands);
-}
void registerClusterOnOff(Commands & commands)
{
const char * clusterName = "OnOff";
registerClusterBasic(commands);
registerClusterBinding(commands);
registerClusterColorControl(commands);
- registerClusterContentLaunch(commands);
registerClusterDoorLock(commands);
registerClusterGeneralCommissioning(commands);
registerClusterGroups(commands);
registerClusterIdentify(commands);
registerClusterLevelControl(commands);
registerClusterLowPower(commands);
- registerClusterMediaPlayback(commands);
registerClusterOnOff(commands);
registerClusterScenes(commands);
registerClusterTemperatureMeasurement(commands);
public:
Listen() : ReportingCommand("listen") {}
+ ~Listen()
+ {
+ delete onReportColorControlCurrentHueCallback;
+ delete onReportColorControlCurrentSaturationCallback;
+ delete onReportColorControlCurrentXCallback;
+ delete onReportColorControlCurrentYCallback;
+ delete onReportColorControlColorTemperatureCallback;
+ delete onReportDoorLockLockStateCallback;
+ delete onReportLevelControlCurrentLevelCallback;
+ delete onReportOnOffOnOffCallback;
+ delete onReportTemperatureMeasurementMeasuredValueCallback;
+ }
+
void AddReportCallbacks(uint8_t endpointId) override
{
chip::app::CHIPDeviceCallbacksMgr & callbacksMgr = chip::app::CHIPDeviceCallbacksMgr::GetInstance();
void PersistentStorage::SetStorageDelegate(PersistentStorageResultDelegate * delegate) {}
-void PersistentStorage::AsyncGetKeyValue(const char * key) {}
-
CHIP_ERROR PersistentStorage::SyncGetKeyValue(const char * key, char * value, uint16_t & size)
{
CHIP_ERROR err = CHIP_NO_ERROR;
/////////// PersistentStorageDelegate Interface /////////
void SetStorageDelegate(chip::PersistentStorageResultDelegate * delegate) override;
- void AsyncGetKeyValue(const char * key) override;
CHIP_ERROR SyncGetKeyValue(const char * key, char * value, uint16_t & size) override;
void AsyncSetKeyValue(const char * key, const char * value) override;
void AsyncDeleteKeyValue(const char * key) override;
return true;
}
-bool emberAfContentLaunchClusterLaunchContentResponseCallback(uint8_t contentLaunchStatus)
-{
- ChipLogProgress(Zcl, "LaunchContentResponse:");
- ChipLogProgress(Zcl, " contentLaunchStatus: %" PRIu8 "", contentLaunchStatus);
-
- GET_RESPONSE_CALLBACKS("ContentLaunchClusterLaunchContentResponseCallback");
-
- Callback::Callback<ContentLaunchClusterLaunchContentResponseCallback> * cb =
- Callback::Callback<ContentLaunchClusterLaunchContentResponseCallback>::FromCancelable(onSuccessCallback);
- cb->mCall(cb->mContext, contentLaunchStatus);
- return true;
-}
-
-bool emberAfContentLaunchClusterLaunchURLResponseCallback(uint8_t contentLaunchStatus)
-{
- ChipLogProgress(Zcl, "LaunchURLResponse:");
- ChipLogProgress(Zcl, " contentLaunchStatus: %" PRIu8 "", contentLaunchStatus);
-
- GET_RESPONSE_CALLBACKS("ContentLaunchClusterLaunchURLResponseCallback");
-
- Callback::Callback<ContentLaunchClusterLaunchURLResponseCallback> * cb =
- Callback::Callback<ContentLaunchClusterLaunchURLResponseCallback>::FromCancelable(onSuccessCallback);
- cb->mCall(cb->mContext, contentLaunchStatus);
- return true;
-}
-
bool emberAfDoorLockClusterClearAllPinsResponseCallback(uint8_t status)
{
ChipLogProgress(Zcl, "ClearAllPinsResponse:");
typedef void (*ReadReportingConfigurationReceivedCallback)(void * context, uint16_t timeout);
// Cluster Specific Response Callbacks
-typedef void (*ContentLaunchClusterLaunchContentResponseCallback)(void * context, uint8_t contentLaunchStatus);
-typedef void (*ContentLaunchClusterLaunchURLResponseCallback)(void * context, uint8_t contentLaunchStatus);
typedef void (*DoorLockClusterClearAllPinsResponseCallback)(void * context);
typedef void (*DoorLockClusterClearAllRfidsResponseCallback)(void * context);
typedef void (*DoorLockClusterClearHolidayScheduleResponseCallback)(void * context);
typedef void (*GroupsClusterRemoveGroupResponseCallback)(void * context, uint16_t groupId);
typedef void (*GroupsClusterViewGroupResponseCallback)(void * context, uint16_t groupId, uint8_t * groupName);
typedef void (*IdentifyClusterIdentifyQueryResponseCallback)(void * context, uint16_t timeout);
-typedef void (*MediaPlaybackClusterPlaybackCallback)(void * context);
typedef void (*ScenesClusterAddSceneResponseCallback)(void * context, uint16_t groupId, uint8_t sceneId);
typedef void (*ScenesClusterGetSceneMembershipResponseCallback)(void * context, uint8_t capacity, uint16_t groupId,
uint8_t sceneCount,
@end
/**
- * Cluster Content Launch
- *
- */
-@interface CHIPContentLaunch : CHIPCluster
-
-- (void)launchContent:(ResponseHandler)completionHandler;
-- (void)launchURL:(ResponseHandler)completionHandler;
-
-- (void)readAttributeClusterRevision:(ResponseHandler)completionHandler;
-
-@end
-
-/**
* Cluster Door Lock
*
*/
@end
/**
- * Cluster Media Playback
- *
- */
-@interface CHIPMediaPlayback : CHIPCluster
-
-- (void)fastForwardRequest:(ResponseHandler)completionHandler;
-- (void)nextRequest:(ResponseHandler)completionHandler;
-- (void)pauseRequest:(ResponseHandler)completionHandler;
-- (void)playRequest:(ResponseHandler)completionHandler;
-- (void)previousRequest:(ResponseHandler)completionHandler;
-- (void)rewindRequest:(ResponseHandler)completionHandler;
-- (void)skipBackwardRequest:(ResponseHandler)completionHandler;
-- (void)skipForwardRequest:(ResponseHandler)completionHandler;
-- (void)startOverRequest:(ResponseHandler)completionHandler;
-- (void)stopRequest:(ResponseHandler)completionHandler;
-
-- (void)readAttributeCurrentState:(ResponseHandler)completionHandler;
-- (void)readAttributeClusterRevision:(ResponseHandler)completionHandler;
-
-@end
-
-/**
* Cluster On/off
*
*/
CHIPDefaultFailureCallbackBridge * callback = reinterpret_cast<CHIPDefaultFailureCallbackBridge *>(context);
if (callback && callback->mQueue) {
dispatch_async(callback->mQueue, ^{
- NSError * error = [NSError errorWithDomain:CHIPErrorDomain
- code:status
- userInfo:@ { NSLocalizedDescriptionKey : @"" }];
+ NSError * error = [CHIPError errorForCHIPErrorCode:status];
callback->mHandler(error, nil);
callback->Cancel();
delete callback;
bool mKeepAlive;
};
-class CHIPContentLaunchClusterLaunchContentResponseCallbackBridge
- : public Callback::Callback<ContentLaunchClusterLaunchContentResponseCallback> {
-public:
- CHIPContentLaunchClusterLaunchContentResponseCallbackBridge(ResponseHandler handler, dispatch_queue_t queue)
- : Callback::Callback<ContentLaunchClusterLaunchContentResponseCallback>(CallbackFn, this)
- , mHandler(handler)
- , mQueue(queue)
- {
- }
-
- ~CHIPContentLaunchClusterLaunchContentResponseCallbackBridge() {};
-
- static void CallbackFn(void * context, uint8_t contentLaunchStatus)
- {
- CHIPContentLaunchClusterLaunchContentResponseCallbackBridge * callback
- = reinterpret_cast<CHIPContentLaunchClusterLaunchContentResponseCallbackBridge *>(context);
- if (callback && callback->mQueue) {
- dispatch_async(callback->mQueue, ^{
- callback->mHandler(nil, @ {
- @"contentLaunchStatus" : [NSNumber numberWithUnsignedChar:contentLaunchStatus],
- });
- callback->Cancel();
- delete callback;
- });
- }
- };
-
-private:
- ResponseHandler mHandler;
- dispatch_queue_t mQueue;
-};
-
-class CHIPContentLaunchClusterLaunchURLResponseCallbackBridge
- : public Callback::Callback<ContentLaunchClusterLaunchURLResponseCallback> {
-public:
- CHIPContentLaunchClusterLaunchURLResponseCallbackBridge(ResponseHandler handler, dispatch_queue_t queue)
- : Callback::Callback<ContentLaunchClusterLaunchURLResponseCallback>(CallbackFn, this)
- , mHandler(handler)
- , mQueue(queue)
- {
- }
-
- ~CHIPContentLaunchClusterLaunchURLResponseCallbackBridge() {};
-
- static void CallbackFn(void * context, uint8_t contentLaunchStatus)
- {
- CHIPContentLaunchClusterLaunchURLResponseCallbackBridge * callback
- = reinterpret_cast<CHIPContentLaunchClusterLaunchURLResponseCallbackBridge *>(context);
- if (callback && callback->mQueue) {
- dispatch_async(callback->mQueue, ^{
- callback->mHandler(nil, @ {
- @"contentLaunchStatus" : [NSNumber numberWithUnsignedChar:contentLaunchStatus],
- });
- callback->Cancel();
- delete callback;
- });
- }
- };
-
-private:
- ResponseHandler mHandler;
- dispatch_queue_t mQueue;
-};
-
class CHIPDoorLockClusterClearAllPinsResponseCallbackBridge
: public Callback::Callback<DoorLockClusterClearAllPinsResponseCallback> {
public:
dispatch_queue_t mQueue;
};
-class CHIPMediaPlaybackClusterPlaybackCallbackBridge : public Callback::Callback<MediaPlaybackClusterPlaybackCallback> {
-public:
- CHIPMediaPlaybackClusterPlaybackCallbackBridge(ResponseHandler handler, dispatch_queue_t queue)
- : Callback::Callback<MediaPlaybackClusterPlaybackCallback>(CallbackFn, this)
- , mHandler(handler)
- , mQueue(queue)
- {
- }
-
- ~CHIPMediaPlaybackClusterPlaybackCallbackBridge() {};
-
- static void CallbackFn(void * context)
- {
- CHIPMediaPlaybackClusterPlaybackCallbackBridge * callback
- = reinterpret_cast<CHIPMediaPlaybackClusterPlaybackCallbackBridge *>(context);
- if (callback && callback->mQueue) {
- dispatch_async(callback->mQueue, ^{
- callback->mHandler(nil, @ {});
- callback->Cancel();
- delete callback;
- });
- }
- };
-
-private:
- ResponseHandler mHandler;
- dispatch_queue_t mQueue;
-};
-
class CHIPScenesClusterAddSceneResponseCallbackBridge : public Callback::Callback<ScenesClusterAddSceneResponseCallback> {
public:
CHIPScenesClusterAddSceneResponseCallbackBridge(ResponseHandler handler, dispatch_queue_t queue)
@end
-@interface CHIPContentLaunch ()
-@property (readonly) Controller::ContentLaunchCluster cppCluster;
-@end
-
-@implementation CHIPContentLaunch
-
-- (Controller::ClusterBase *)getCluster
-{
- return &_cppCluster;
-}
-
-- (void)launchContent:(ResponseHandler)completionHandler
-{
- CHIPContentLaunchClusterLaunchContentResponseCallbackBridge * onSuccess
- = new CHIPContentLaunchClusterLaunchContentResponseCallbackBridge(completionHandler, [self callbackQueue]);
- if (!onSuccess) {
- completionHandler([CHIPError errorForCHIPErrorCode:CHIP_ERROR_INCORRECT_STATE], nil);
- return;
- }
-
- CHIPDefaultFailureCallbackBridge * onFailure = new CHIPDefaultFailureCallbackBridge(completionHandler, [self callbackQueue]);
- if (!onFailure) {
- delete onSuccess;
- completionHandler([CHIPError errorForCHIPErrorCode:CHIP_ERROR_INCORRECT_STATE], nil);
- return;
- }
-
- CHIP_ERROR err = self.cppCluster.LaunchContent(onSuccess->Cancel(), onFailure->Cancel());
- if (err != CHIP_NO_ERROR) {
- delete onSuccess;
- delete onFailure;
- completionHandler([CHIPError errorForCHIPErrorCode:err], nil);
- }
-}
-- (void)launchURL:(ResponseHandler)completionHandler
-{
- CHIPContentLaunchClusterLaunchURLResponseCallbackBridge * onSuccess
- = new CHIPContentLaunchClusterLaunchURLResponseCallbackBridge(completionHandler, [self callbackQueue]);
- if (!onSuccess) {
- completionHandler([CHIPError errorForCHIPErrorCode:CHIP_ERROR_INCORRECT_STATE], nil);
- return;
- }
-
- CHIPDefaultFailureCallbackBridge * onFailure = new CHIPDefaultFailureCallbackBridge(completionHandler, [self callbackQueue]);
- if (!onFailure) {
- delete onSuccess;
- completionHandler([CHIPError errorForCHIPErrorCode:CHIP_ERROR_INCORRECT_STATE], nil);
- return;
- }
-
- CHIP_ERROR err = self.cppCluster.LaunchURL(onSuccess->Cancel(), onFailure->Cancel());
- if (err != CHIP_NO_ERROR) {
- delete onSuccess;
- delete onFailure;
- completionHandler([CHIPError errorForCHIPErrorCode:err], nil);
- }
-}
-
-- (void)readAttributeClusterRevision:(ResponseHandler)completionHandler
-{
- CHIPInt16uAttributeCallbackBridge * onSuccess = new CHIPInt16uAttributeCallbackBridge(completionHandler, [self callbackQueue]);
- if (!onSuccess) {
- completionHandler([CHIPError errorForCHIPErrorCode:CHIP_ERROR_INCORRECT_STATE], nil);
- return;
- }
-
- CHIPDefaultFailureCallbackBridge * onFailure = new CHIPDefaultFailureCallbackBridge(completionHandler, [self callbackQueue]);
- if (!onFailure) {
- delete onSuccess;
- completionHandler([CHIPError errorForCHIPErrorCode:CHIP_ERROR_INCORRECT_STATE], nil);
- return;
- }
-
- CHIP_ERROR err = self.cppCluster.ReadAttributeClusterRevision(onSuccess->Cancel(), onFailure->Cancel());
- if (err != CHIP_NO_ERROR) {
- delete onSuccess;
- delete onFailure;
- completionHandler([CHIPError errorForCHIPErrorCode:err], nil);
- }
-}
-
-@end
-
@interface CHIPDoorLock ()
@property (readonly) Controller::DoorLockCluster cppCluster;
@end
@end
-@interface CHIPMediaPlayback ()
-@property (readonly) Controller::MediaPlaybackCluster cppCluster;
-@end
-
-@implementation CHIPMediaPlayback
-
-- (Controller::ClusterBase *)getCluster
-{
- return &_cppCluster;
-}
-
-- (void)fastForwardRequest:(ResponseHandler)completionHandler
-{
- CHIPDefaultSuccessCallbackBridge * onSuccess = new CHIPDefaultSuccessCallbackBridge(completionHandler, [self callbackQueue]);
- if (!onSuccess) {
- completionHandler([CHIPError errorForCHIPErrorCode:CHIP_ERROR_INCORRECT_STATE], nil);
- return;
- }
-
- CHIPDefaultFailureCallbackBridge * onFailure = new CHIPDefaultFailureCallbackBridge(completionHandler, [self callbackQueue]);
- if (!onFailure) {
- delete onSuccess;
- completionHandler([CHIPError errorForCHIPErrorCode:CHIP_ERROR_INCORRECT_STATE], nil);
- return;
- }
-
- CHIP_ERROR err = self.cppCluster.FastForwardRequest(onSuccess->Cancel(), onFailure->Cancel());
- if (err != CHIP_NO_ERROR) {
- delete onSuccess;
- delete onFailure;
- completionHandler([CHIPError errorForCHIPErrorCode:err], nil);
- }
-}
-- (void)nextRequest:(ResponseHandler)completionHandler
-{
- CHIPDefaultSuccessCallbackBridge * onSuccess = new CHIPDefaultSuccessCallbackBridge(completionHandler, [self callbackQueue]);
- if (!onSuccess) {
- completionHandler([CHIPError errorForCHIPErrorCode:CHIP_ERROR_INCORRECT_STATE], nil);
- return;
- }
-
- CHIPDefaultFailureCallbackBridge * onFailure = new CHIPDefaultFailureCallbackBridge(completionHandler, [self callbackQueue]);
- if (!onFailure) {
- delete onSuccess;
- completionHandler([CHIPError errorForCHIPErrorCode:CHIP_ERROR_INCORRECT_STATE], nil);
- return;
- }
-
- CHIP_ERROR err = self.cppCluster.NextRequest(onSuccess->Cancel(), onFailure->Cancel());
- if (err != CHIP_NO_ERROR) {
- delete onSuccess;
- delete onFailure;
- completionHandler([CHIPError errorForCHIPErrorCode:err], nil);
- }
-}
-- (void)pauseRequest:(ResponseHandler)completionHandler
-{
- CHIPDefaultSuccessCallbackBridge * onSuccess = new CHIPDefaultSuccessCallbackBridge(completionHandler, [self callbackQueue]);
- if (!onSuccess) {
- completionHandler([CHIPError errorForCHIPErrorCode:CHIP_ERROR_INCORRECT_STATE], nil);
- return;
- }
-
- CHIPDefaultFailureCallbackBridge * onFailure = new CHIPDefaultFailureCallbackBridge(completionHandler, [self callbackQueue]);
- if (!onFailure) {
- delete onSuccess;
- completionHandler([CHIPError errorForCHIPErrorCode:CHIP_ERROR_INCORRECT_STATE], nil);
- return;
- }
-
- CHIP_ERROR err = self.cppCluster.PauseRequest(onSuccess->Cancel(), onFailure->Cancel());
- if (err != CHIP_NO_ERROR) {
- delete onSuccess;
- delete onFailure;
- completionHandler([CHIPError errorForCHIPErrorCode:err], nil);
- }
-}
-- (void)playRequest:(ResponseHandler)completionHandler
-{
- CHIPDefaultSuccessCallbackBridge * onSuccess = new CHIPDefaultSuccessCallbackBridge(completionHandler, [self callbackQueue]);
- if (!onSuccess) {
- completionHandler([CHIPError errorForCHIPErrorCode:CHIP_ERROR_INCORRECT_STATE], nil);
- return;
- }
-
- CHIPDefaultFailureCallbackBridge * onFailure = new CHIPDefaultFailureCallbackBridge(completionHandler, [self callbackQueue]);
- if (!onFailure) {
- delete onSuccess;
- completionHandler([CHIPError errorForCHIPErrorCode:CHIP_ERROR_INCORRECT_STATE], nil);
- return;
- }
-
- CHIP_ERROR err = self.cppCluster.PlayRequest(onSuccess->Cancel(), onFailure->Cancel());
- if (err != CHIP_NO_ERROR) {
- delete onSuccess;
- delete onFailure;
- completionHandler([CHIPError errorForCHIPErrorCode:err], nil);
- }
-}
-- (void)previousRequest:(ResponseHandler)completionHandler
-{
- CHIPDefaultSuccessCallbackBridge * onSuccess = new CHIPDefaultSuccessCallbackBridge(completionHandler, [self callbackQueue]);
- if (!onSuccess) {
- completionHandler([CHIPError errorForCHIPErrorCode:CHIP_ERROR_INCORRECT_STATE], nil);
- return;
- }
-
- CHIPDefaultFailureCallbackBridge * onFailure = new CHIPDefaultFailureCallbackBridge(completionHandler, [self callbackQueue]);
- if (!onFailure) {
- delete onSuccess;
- completionHandler([CHIPError errorForCHIPErrorCode:CHIP_ERROR_INCORRECT_STATE], nil);
- return;
- }
-
- CHIP_ERROR err = self.cppCluster.PreviousRequest(onSuccess->Cancel(), onFailure->Cancel());
- if (err != CHIP_NO_ERROR) {
- delete onSuccess;
- delete onFailure;
- completionHandler([CHIPError errorForCHIPErrorCode:err], nil);
- }
-}
-- (void)rewindRequest:(ResponseHandler)completionHandler
-{
- CHIPDefaultSuccessCallbackBridge * onSuccess = new CHIPDefaultSuccessCallbackBridge(completionHandler, [self callbackQueue]);
- if (!onSuccess) {
- completionHandler([CHIPError errorForCHIPErrorCode:CHIP_ERROR_INCORRECT_STATE], nil);
- return;
- }
-
- CHIPDefaultFailureCallbackBridge * onFailure = new CHIPDefaultFailureCallbackBridge(completionHandler, [self callbackQueue]);
- if (!onFailure) {
- delete onSuccess;
- completionHandler([CHIPError errorForCHIPErrorCode:CHIP_ERROR_INCORRECT_STATE], nil);
- return;
- }
-
- CHIP_ERROR err = self.cppCluster.RewindRequest(onSuccess->Cancel(), onFailure->Cancel());
- if (err != CHIP_NO_ERROR) {
- delete onSuccess;
- delete onFailure;
- completionHandler([CHIPError errorForCHIPErrorCode:err], nil);
- }
-}
-- (void)skipBackwardRequest:(ResponseHandler)completionHandler
-{
- CHIPDefaultSuccessCallbackBridge * onSuccess = new CHIPDefaultSuccessCallbackBridge(completionHandler, [self callbackQueue]);
- if (!onSuccess) {
- completionHandler([CHIPError errorForCHIPErrorCode:CHIP_ERROR_INCORRECT_STATE], nil);
- return;
- }
-
- CHIPDefaultFailureCallbackBridge * onFailure = new CHIPDefaultFailureCallbackBridge(completionHandler, [self callbackQueue]);
- if (!onFailure) {
- delete onSuccess;
- completionHandler([CHIPError errorForCHIPErrorCode:CHIP_ERROR_INCORRECT_STATE], nil);
- return;
- }
-
- CHIP_ERROR err = self.cppCluster.SkipBackwardRequest(onSuccess->Cancel(), onFailure->Cancel());
- if (err != CHIP_NO_ERROR) {
- delete onSuccess;
- delete onFailure;
- completionHandler([CHIPError errorForCHIPErrorCode:err], nil);
- }
-}
-- (void)skipForwardRequest:(ResponseHandler)completionHandler
-{
- CHIPDefaultSuccessCallbackBridge * onSuccess = new CHIPDefaultSuccessCallbackBridge(completionHandler, [self callbackQueue]);
- if (!onSuccess) {
- completionHandler([CHIPError errorForCHIPErrorCode:CHIP_ERROR_INCORRECT_STATE], nil);
- return;
- }
-
- CHIPDefaultFailureCallbackBridge * onFailure = new CHIPDefaultFailureCallbackBridge(completionHandler, [self callbackQueue]);
- if (!onFailure) {
- delete onSuccess;
- completionHandler([CHIPError errorForCHIPErrorCode:CHIP_ERROR_INCORRECT_STATE], nil);
- return;
- }
-
- CHIP_ERROR err = self.cppCluster.SkipForwardRequest(onSuccess->Cancel(), onFailure->Cancel());
- if (err != CHIP_NO_ERROR) {
- delete onSuccess;
- delete onFailure;
- completionHandler([CHIPError errorForCHIPErrorCode:err], nil);
- }
-}
-- (void)startOverRequest:(ResponseHandler)completionHandler
-{
- CHIPDefaultSuccessCallbackBridge * onSuccess = new CHIPDefaultSuccessCallbackBridge(completionHandler, [self callbackQueue]);
- if (!onSuccess) {
- completionHandler([CHIPError errorForCHIPErrorCode:CHIP_ERROR_INCORRECT_STATE], nil);
- return;
- }
-
- CHIPDefaultFailureCallbackBridge * onFailure = new CHIPDefaultFailureCallbackBridge(completionHandler, [self callbackQueue]);
- if (!onFailure) {
- delete onSuccess;
- completionHandler([CHIPError errorForCHIPErrorCode:CHIP_ERROR_INCORRECT_STATE], nil);
- return;
- }
-
- CHIP_ERROR err = self.cppCluster.StartOverRequest(onSuccess->Cancel(), onFailure->Cancel());
- if (err != CHIP_NO_ERROR) {
- delete onSuccess;
- delete onFailure;
- completionHandler([CHIPError errorForCHIPErrorCode:err], nil);
- }
-}
-- (void)stopRequest:(ResponseHandler)completionHandler
-{
- CHIPDefaultSuccessCallbackBridge * onSuccess = new CHIPDefaultSuccessCallbackBridge(completionHandler, [self callbackQueue]);
- if (!onSuccess) {
- completionHandler([CHIPError errorForCHIPErrorCode:CHIP_ERROR_INCORRECT_STATE], nil);
- return;
- }
-
- CHIPDefaultFailureCallbackBridge * onFailure = new CHIPDefaultFailureCallbackBridge(completionHandler, [self callbackQueue]);
- if (!onFailure) {
- delete onSuccess;
- completionHandler([CHIPError errorForCHIPErrorCode:CHIP_ERROR_INCORRECT_STATE], nil);
- return;
- }
-
- CHIP_ERROR err = self.cppCluster.StopRequest(onSuccess->Cancel(), onFailure->Cancel());
- if (err != CHIP_NO_ERROR) {
- delete onSuccess;
- delete onFailure;
- completionHandler([CHIPError errorForCHIPErrorCode:err], nil);
- }
-}
-
-- (void)readAttributeCurrentState:(ResponseHandler)completionHandler
-{
- CHIPInt16uAttributeCallbackBridge * onSuccess = new CHIPInt16uAttributeCallbackBridge(completionHandler, [self callbackQueue]);
- if (!onSuccess) {
- completionHandler([CHIPError errorForCHIPErrorCode:CHIP_ERROR_INCORRECT_STATE], nil);
- return;
- }
-
- CHIPDefaultFailureCallbackBridge * onFailure = new CHIPDefaultFailureCallbackBridge(completionHandler, [self callbackQueue]);
- if (!onFailure) {
- delete onSuccess;
- completionHandler([CHIPError errorForCHIPErrorCode:CHIP_ERROR_INCORRECT_STATE], nil);
- return;
- }
-
- CHIP_ERROR err = self.cppCluster.ReadAttributeCurrentState(onSuccess->Cancel(), onFailure->Cancel());
- if (err != CHIP_NO_ERROR) {
- delete onSuccess;
- delete onFailure;
- completionHandler([CHIPError errorForCHIPErrorCode:err], nil);
- }
-}
-
-- (void)readAttributeClusterRevision:(ResponseHandler)completionHandler
-{
- CHIPInt16uAttributeCallbackBridge * onSuccess = new CHIPInt16uAttributeCallbackBridge(completionHandler, [self callbackQueue]);
- if (!onSuccess) {
- completionHandler([CHIPError errorForCHIPErrorCode:CHIP_ERROR_INCORRECT_STATE], nil);
- return;
- }
-
- CHIPDefaultFailureCallbackBridge * onFailure = new CHIPDefaultFailureCallbackBridge(completionHandler, [self callbackQueue]);
- if (!onFailure) {
- delete onSuccess;
- completionHandler([CHIPError errorForCHIPErrorCode:CHIP_ERROR_INCORRECT_STATE], nil);
- return;
- }
-
- CHIP_ERROR err = self.cppCluster.ReadAttributeClusterRevision(onSuccess->Cancel(), onFailure->Cancel());
- if (err != CHIP_NO_ERROR) {
- delete onSuccess;
- delete onFailure;
- completionHandler([CHIPError errorForCHIPErrorCode:err], nil);
- }
-}
-
-@end
-
@interface CHIPOnOff ()
@property (readonly) Controller::OnOffCluster cppCluster;
@end
namespace clusters {
-namespace ContentLaunch {
-
-void DispatchClientCommand(app::Command * command, CommandId commandId, EndpointId endpointId, TLV::TLVReader & dataTlv)
-{
- {
- switch (commandId)
- {
- case ZCL_LAUNCH_CONTENT_RESPONSE_COMMAND_ID: {
- CHIP_ERROR TLVError = CHIP_NO_ERROR;
- uint8_t contentLaunchStatus;
-
- while ((TLVError = dataTlv.Next()) == CHIP_NO_ERROR)
- {
- switch (TLV::TagNumFromTag(dataTlv.GetTag()))
- {
- case 0:
- TLVError = dataTlv.Get(contentLaunchStatus);
- break;
- default:
- // Unsupported tag, ignore it.
- ChipLogProgress(Zcl, "Unknown TLV tag during processing.");
- break;
- }
- if (TLVError != CHIP_NO_ERROR)
- {
- ChipLogProgress(Zcl, "Failed to decode TLV data with tag %" PRIx32 ": %" PRId32,
- TLV::TagNumFromTag(dataTlv.GetTag()), TLVError);
- }
- }
- // TODO(#5098) We should pass the Command Object and EndpointId to the cluster callbacks.
- emberAfContentLaunchClusterLaunchContentResponseCallback(contentLaunchStatus);
- break;
- }
- case ZCL_LAUNCH_URL_RESPONSE_COMMAND_ID: {
- CHIP_ERROR TLVError = CHIP_NO_ERROR;
- uint8_t contentLaunchStatus;
-
- while ((TLVError = dataTlv.Next()) == CHIP_NO_ERROR)
- {
- switch (TLV::TagNumFromTag(dataTlv.GetTag()))
- {
- case 0:
- TLVError = dataTlv.Get(contentLaunchStatus);
- break;
- default:
- // Unsupported tag, ignore it.
- ChipLogProgress(Zcl, "Unknown TLV tag during processing.");
- break;
- }
- if (TLVError != CHIP_NO_ERROR)
- {
- ChipLogProgress(Zcl, "Failed to decode TLV data with tag %" PRIx32 ": %" PRId32,
- TLV::TagNumFromTag(dataTlv.GetTag()), TLVError);
- }
- }
- // TODO(#5098) We should pass the Command Object and EndpointId to the cluster callbacks.
- emberAfContentLaunchClusterLaunchURLResponseCallback(contentLaunchStatus);
- break;
- }
- default: {
- // Unrecognized command ID, error status will apply.
- // TODO: Encode response for command not found
- ChipLogError(Zcl, "Unknown command %" PRIx16 " for cluster %" PRIx16, commandId, ZCL_CONTENT_LAUNCH_CLUSTER_ID);
- break;
- }
- }
- }
-}
-
-} // namespace ContentLaunch
-
namespace DoorLock {
void DispatchClientCommand(app::Command * command, CommandId commandId, EndpointId endpointId, TLV::TLVReader & dataTlv)
} // namespace Identify
-namespace MediaPlayback {
-
-void DispatchClientCommand(app::Command * command, CommandId commandId, EndpointId endpointId, TLV::TLVReader & dataTlv)
-{
- {
- switch (commandId)
- {
- case ZCL_PLAYBACK_COMMAND_ID: {
- // TODO(#5098) We should pass the Command Object and EndpointId to the cluster callbacks.
- emberAfMediaPlaybackClusterPlaybackCallback();
- break;
- }
- default: {
- // Unrecognized command ID, error status will apply.
- // TODO: Encode response for command not found
- ChipLogError(Zcl, "Unknown command %" PRIx16 " for cluster %" PRIx16, commandId, ZCL_MEDIA_PLAYBACK_CLUSTER_ID);
- break;
- }
- }
- }
-}
-
-} // namespace MediaPlayback
-
namespace Scenes {
void DispatchClientCommand(app::Command * command, CommandId commandId, EndpointId endpointId, TLV::TLVReader & dataTlv)
// Server attributes
#define ZCL_MAX_DURATION_ATTRIBUTE_ID (0x0000)
+// Attribute ids for cluster: Media Playback
+
+// Client attributes
+
+// Server attributes
+#define ZCL_CURRENT_STATE_ATTRIBUTE_ID (0x0000)
+
// Attribute ids for cluster: Low Power
// Client attributes
// Server attributes
+// Attribute ids for cluster: Content Launch
+
+// Client attributes
+
+// Server attributes
+
// Attribute ids for cluster: Application Basic
// Client attributes
// Server attributes
-// Attribute ids for cluster: Media Playback
-
-// Client attributes
-
-// Server attributes
-#define ZCL_CURRENT_STATE_ATTRIBUTE_ID (0x0000)
-
-// Attribute ids for cluster: Content Launch
-
-// Client attributes
-
-// Server attributes
-
// Attribute ids for cluster: Group Key Management
// Client attributes
EmberAfStatus emberAfBasicClusterClientCommandParse(EmberAfClusterCommand * cmd);
EmberAfStatus emberAfBindingClusterClientCommandParse(EmberAfClusterCommand * cmd);
EmberAfStatus emberAfColorControlClusterClientCommandParse(EmberAfClusterCommand * cmd);
-EmberAfStatus emberAfContentLaunchClusterClientCommandParse(EmberAfClusterCommand * cmd);
EmberAfStatus emberAfDoorLockClusterClientCommandParse(EmberAfClusterCommand * cmd);
EmberAfStatus emberAfGeneralCommissioningClusterClientCommandParse(EmberAfClusterCommand * cmd);
EmberAfStatus emberAfGroupsClusterClientCommandParse(EmberAfClusterCommand * cmd);
EmberAfStatus emberAfIdentifyClusterClientCommandParse(EmberAfClusterCommand * cmd);
EmberAfStatus emberAfLevelControlClusterClientCommandParse(EmberAfClusterCommand * cmd);
EmberAfStatus emberAfLowPowerClusterClientCommandParse(EmberAfClusterCommand * cmd);
-EmberAfStatus emberAfMediaPlaybackClusterClientCommandParse(EmberAfClusterCommand * cmd);
EmberAfStatus emberAfOnOffClusterClientCommandParse(EmberAfClusterCommand * cmd);
EmberAfStatus emberAfScenesClusterClientCommandParse(EmberAfClusterCommand * cmd);
EmberAfStatus emberAfTemperatureMeasurementClusterClientCommandParse(EmberAfClusterCommand * cmd);
// No commands are enabled for cluster Color Control
result = status(false, true, cmd->mfgSpecific);
break;
- case ZCL_CONTENT_LAUNCH_CLUSTER_ID:
- result = emberAfContentLaunchClusterClientCommandParse(cmd);
- break;
case ZCL_DOOR_LOCK_CLUSTER_ID:
result = emberAfDoorLockClusterClientCommandParse(cmd);
break;
// No commands are enabled for cluster Low Power
result = status(false, true, cmd->mfgSpecific);
break;
- case ZCL_MEDIA_PLAYBACK_CLUSTER_ID:
- result = emberAfMediaPlaybackClusterClientCommandParse(cmd);
- break;
case ZCL_ON_OFF_CLUSTER_ID:
// No commands are enabled for cluster On/off
result = status(false, true, cmd->mfgSpecific);
// Cluster specific command parsing
-EmberAfStatus emberAfContentLaunchClusterClientCommandParse(EmberAfClusterCommand * cmd)
-{
- bool wasHandled = false;
-
- if (!cmd->mfgSpecific)
- {
- switch (cmd->commandId)
- {
- case ZCL_LAUNCH_CONTENT_RESPONSE_COMMAND_ID: {
- uint16_t payloadOffset = cmd->payloadStartIndex;
- uint8_t contentLaunchStatus;
-
- if (cmd->bufLen < payloadOffset + 1)
- {
- return EMBER_ZCL_STATUS_MALFORMED_COMMAND;
- }
- contentLaunchStatus = emberAfGetInt8u(cmd->buffer, payloadOffset, cmd->bufLen);
-
- wasHandled = emberAfContentLaunchClusterLaunchContentResponseCallback(contentLaunchStatus);
- break;
- }
- case ZCL_LAUNCH_URL_RESPONSE_COMMAND_ID: {
- uint16_t payloadOffset = cmd->payloadStartIndex;
- uint8_t contentLaunchStatus;
-
- if (cmd->bufLen < payloadOffset + 1)
- {
- return EMBER_ZCL_STATUS_MALFORMED_COMMAND;
- }
- contentLaunchStatus = emberAfGetInt8u(cmd->buffer, payloadOffset, cmd->bufLen);
-
- wasHandled = emberAfContentLaunchClusterLaunchURLResponseCallback(contentLaunchStatus);
- break;
- }
- default: {
- // Unrecognized command ID, error status will apply.
- break;
- }
- }
- }
- return status(wasHandled, true, cmd->mfgSpecific);
-}
EmberAfStatus emberAfDoorLockClusterClientCommandParse(EmberAfClusterCommand * cmd)
{
bool wasHandled = false;
}
return status(wasHandled, true, cmd->mfgSpecific);
}
-EmberAfStatus emberAfMediaPlaybackClusterClientCommandParse(EmberAfClusterCommand * cmd)
-{
- bool wasHandled = false;
-
- if (!cmd->mfgSpecific)
- {
- switch (cmd->commandId)
- {
- case ZCL_PLAYBACK_COMMAND_ID: {
- wasHandled = emberAfMediaPlaybackClusterPlaybackCallback();
- break;
- }
- default: {
- // Unrecognized command ID, error status will apply.
- break;
- }
- }
- }
- return status(wasHandled, true, cmd->mfgSpecific);
-}
EmberAfStatus emberAfScenesClusterClientCommandParse(EmberAfClusterCommand * cmd)
{
bool wasHandled = false;
case ZCL_COLOR_CONTROL_CLUSTER_ID:
emberAfColorControlClusterInitCallback(endpoint);
break;
- case ZCL_CONTENT_LAUNCH_CLUSTER_ID:
- emberAfContentLaunchClusterInitCallback(endpoint);
- break;
case ZCL_DOOR_LOCK_CLUSTER_ID:
emberAfDoorLockClusterInitCallback(endpoint);
break;
case ZCL_LOW_POWER_CLUSTER_ID:
emberAfLowPowerClusterInitCallback(endpoint);
break;
- case ZCL_MEDIA_PLAYBACK_CLUSTER_ID:
- emberAfMediaPlaybackClusterInitCallback(endpoint);
- break;
case ZCL_ON_OFF_CLUSTER_ID:
emberAfOnOffClusterInitCallback(endpoint);
break;
// To prevent warning
(void) endpoint;
}
-void __attribute__((weak)) emberAfContentLaunchClusterInitCallback(EndpointId endpoint)
-{
- // To prevent warning
- (void) endpoint;
-}
void __attribute__((weak)) emberAfDoorLockClusterInitCallback(EndpointId endpoint)
{
// To prevent warning
// To prevent warning
(void) endpoint;
}
-void __attribute__((weak)) emberAfMediaPlaybackClusterInitCallback(EndpointId endpoint)
-{
- // To prevent warning
- (void) endpoint;
-}
void __attribute__((weak)) emberAfOnOffClusterInitCallback(EndpointId endpoint)
{
// To prevent warning
*/
void emberAfColorControlClusterInitCallback(chip::EndpointId endpoint);
-/** @brief Content Launch Cluster Init
- *
- * Cluster Init
- *
- * @param endpoint Endpoint that is being initialized
- */
-void emberAfContentLaunchClusterInitCallback(chip::EndpointId endpoint);
-
/** @brief Door Lock Cluster Init
*
* Cluster Init
*/
void emberAfLowPowerClusterInitCallback(chip::EndpointId endpoint);
-/** @brief Media Playback Cluster Init
- *
- * Cluster Init
- *
- * @param endpoint Endpoint that is being initialized
- */
-void emberAfMediaPlaybackClusterInitCallback(chip::EndpointId endpoint);
-
/** @brief On/off Cluster Init
*
* Cluster Init
void emberAfColorControlClusterClientTickCallback(chip::EndpointId endpoint);
//
-// Content Launch Cluster client
-//
-
-/** @brief Content Launch Cluster Client Init
- *
- * Client Init
- *
- * @param endpoint Endpoint that is being initialized
- */
-void emberAfContentLaunchClusterClientInitCallback(chip::EndpointId endpoint);
-
-/** @brief Content Launch Cluster Client Attribute Changed
- *
- * Client Attribute Changed
- *
- * @param endpoint Endpoint that is being initialized
- * @param attributeId Attribute that changed
- */
-void emberAfContentLaunchClusterClientAttributeChangedCallback(chip::EndpointId endpoint, chip::AttributeId attributeId);
-
-/** @brief Content Launch Cluster Client Manufacturer Specific Attribute Changed
- *
- * Client Manufacturer Specific Attribute Changed
- *
- * @param endpoint Endpoint that is being initialized
- * @param attributeId Attribute that changed
- * @param manufacturerCode Manufacturer Code of the attribute that changed
- */
-void emberAfContentLaunchClusterClientManufacturerSpecificAttributeChangedCallback(chip::EndpointId endpoint,
- chip::AttributeId attributeId,
- uint16_t manufacturerCode);
-
-/** @brief Content Launch Cluster Client Message Sent
- *
- * Client Message Sent
- *
- * @param type The type of message sent
- * @param indexOrDestination The destination or address to which the message was sent
- * @param apsFrame The APS frame for the message
- * @param msgLen The length of the message
- * @param message The message that was sent
- * @param status The status of the sent message
- */
-void emberAfContentLaunchClusterClientMessageSentCallback(EmberOutgoingMessageType type, uint64_t indexOrDestination,
- EmberApsFrame * apsFrame, uint16_t msgLen, uint8_t * message,
- EmberStatus status);
-
-/** @brief Content Launch Cluster Client Pre Attribute Changed
- *
- * client Pre Attribute Changed
- *
- * @param endpoint Endpoint that is being initialized
- * @param attributeId Attribute to be changed
- * @param attributeType Attribute type
- * @param size Attribute size
- * @param value Attribute value
- */
-EmberAfStatus emberAfContentLaunchClusterClientPreAttributeChangedCallback(chip::EndpointId endpoint, chip::AttributeId attributeId,
- EmberAfAttributeType attributeType, uint8_t size,
- uint8_t * value);
-
-/** @brief Content Launch Cluster Client Tick
- *
- * client Tick
- *
- * @param endpoint Endpoint that is being served
- */
-void emberAfContentLaunchClusterClientTickCallback(chip::EndpointId endpoint);
-
-//
// Door Lock Cluster client
//
void emberAfLowPowerClusterClientTickCallback(chip::EndpointId endpoint);
//
-// Media Playback Cluster client
-//
-
-/** @brief Media Playback Cluster Client Init
- *
- * Client Init
- *
- * @param endpoint Endpoint that is being initialized
- */
-void emberAfMediaPlaybackClusterClientInitCallback(chip::EndpointId endpoint);
-
-/** @brief Media Playback Cluster Client Attribute Changed
- *
- * Client Attribute Changed
- *
- * @param endpoint Endpoint that is being initialized
- * @param attributeId Attribute that changed
- */
-void emberAfMediaPlaybackClusterClientAttributeChangedCallback(chip::EndpointId endpoint, chip::AttributeId attributeId);
-
-/** @brief Media Playback Cluster Client Manufacturer Specific Attribute Changed
- *
- * Client Manufacturer Specific Attribute Changed
- *
- * @param endpoint Endpoint that is being initialized
- * @param attributeId Attribute that changed
- * @param manufacturerCode Manufacturer Code of the attribute that changed
- */
-void emberAfMediaPlaybackClusterClientManufacturerSpecificAttributeChangedCallback(chip::EndpointId endpoint,
- chip::AttributeId attributeId,
- uint16_t manufacturerCode);
-
-/** @brief Media Playback Cluster Client Message Sent
- *
- * Client Message Sent
- *
- * @param type The type of message sent
- * @param indexOrDestination The destination or address to which the message was sent
- * @param apsFrame The APS frame for the message
- * @param msgLen The length of the message
- * @param message The message that was sent
- * @param status The status of the sent message
- */
-void emberAfMediaPlaybackClusterClientMessageSentCallback(EmberOutgoingMessageType type, uint64_t indexOrDestination,
- EmberApsFrame * apsFrame, uint16_t msgLen, uint8_t * message,
- EmberStatus status);
-
-/** @brief Media Playback Cluster Client Pre Attribute Changed
- *
- * client Pre Attribute Changed
- *
- * @param endpoint Endpoint that is being initialized
- * @param attributeId Attribute to be changed
- * @param attributeType Attribute type
- * @param size Attribute size
- * @param value Attribute value
- */
-EmberAfStatus emberAfMediaPlaybackClusterClientPreAttributeChangedCallback(chip::EndpointId endpoint, chip::AttributeId attributeId,
- EmberAfAttributeType attributeType, uint8_t size,
- uint8_t * value);
-
-/** @brief Media Playback Cluster Client Tick
- *
- * client Tick
- *
- * @param endpoint Endpoint that is being served
- */
-void emberAfMediaPlaybackClusterClientTickCallback(chip::EndpointId endpoint);
-
-//
// On/off Cluster client
//
// Cluster Commands Callback
/**
- * @brief Content Launch Cluster LaunchContentResponse Command callback
- * @param contentLaunchStatus
- */
-
-bool emberAfContentLaunchClusterLaunchContentResponseCallback(uint8_t contentLaunchStatus);
-
-/**
- * @brief Content Launch Cluster LaunchURLResponse Command callback
- * @param contentLaunchStatus
- */
-
-bool emberAfContentLaunchClusterLaunchURLResponseCallback(uint8_t contentLaunchStatus);
-
-/**
* @brief Door Lock Cluster ClearAllPinsResponse Command callback
* @param status
*/
bool emberAfIdentifyClusterIdentifyQueryResponseCallback(uint16_t timeout);
/**
- * @brief Media Playback Cluster Playback Command callback
- */
-
-bool emberAfMediaPlaybackClusterPlaybackCallback();
-
-/**
* @brief Scenes Cluster AddSceneResponse Command callback
* @param status
* @param groupId
\
ZCL_SQUAWK_COMMAND_ID, "u", squawkInfo);
+/** @brief Command description for PlayRequest
+ *
+ * Command: PlayRequest
+ */
+#define emberAfFillCommandMedia \
+ PlaybackClusterPlayRequest() emberAfFillExternalBuffer(mask, \
+ \
+ ZCL_PLAY_REQUEST_COMMAND_ID, "", );
+
+/** @brief Command description for PauseRequest
+ *
+ * Command: PauseRequest
+ */
+#define emberAfFillCommandMedia \
+ PlaybackClusterPauseRequest() emberAfFillExternalBuffer(mask, \
+ \
+ ZCL_PAUSE_REQUEST_COMMAND_ID, "", );
+
+/** @brief Command description for StopRequest
+ *
+ * Command: StopRequest
+ */
+#define emberAfFillCommandMedia \
+ PlaybackClusterStopRequest() emberAfFillExternalBuffer(mask, \
+ \
+ ZCL_STOP_REQUEST_COMMAND_ID, "", );
+
+/** @brief Command description for StartOverRequest
+ *
+ * Command: StartOverRequest
+ */
+#define emberAfFillCommandMedia \
+ PlaybackClusterStartOverRequest() emberAfFillExternalBuffer(mask, \
+ \
+ ZCL_START_OVER_REQUEST_COMMAND_ID, "", );
+
+/** @brief Command description for PreviousRequest
+ *
+ * Command: PreviousRequest
+ */
+#define emberAfFillCommandMedia \
+ PlaybackClusterPreviousRequest() emberAfFillExternalBuffer(mask, \
+ \
+ ZCL_PREVIOUS_REQUEST_COMMAND_ID, "", );
+
+/** @brief Command description for NextRequest
+ *
+ * Command: NextRequest
+ */
+#define emberAfFillCommandMedia \
+ PlaybackClusterNextRequest() emberAfFillExternalBuffer(mask, \
+ \
+ ZCL_NEXT_REQUEST_COMMAND_ID, "", );
+
+/** @brief Command description for RewindRequest
+ *
+ * Command: RewindRequest
+ */
+#define emberAfFillCommandMedia \
+ PlaybackClusterRewindRequest() emberAfFillExternalBuffer(mask, \
+ \
+ ZCL_REWIND_REQUEST_COMMAND_ID, "", );
+
+/** @brief Command description for FastForwardRequest
+ *
+ * Command: FastForwardRequest
+ */
+#define emberAfFillCommandMedia \
+ PlaybackClusterFastForwardRequest() emberAfFillExternalBuffer(mask, \
+ \
+ ZCL_FAST_FORWARD_REQUEST_COMMAND_ID, "", );
+
+/** @brief Command description for SkipForwardRequest
+ *
+ * Command: SkipForwardRequest
+ */
+#define emberAfFillCommandMedia \
+ PlaybackClusterSkipForwardRequest() emberAfFillExternalBuffer(mask, \
+ \
+ ZCL_SKIP_FORWARD_REQUEST_COMMAND_ID, "", );
+
+/** @brief Command description for SkipBackwardRequest
+ *
+ * Command: SkipBackwardRequest
+ */
+#define emberAfFillCommandMedia \
+ PlaybackClusterSkipBackwardRequest() emberAfFillExternalBuffer(mask, \
+ \
+ ZCL_SKIP_BACKWARD_REQUEST_COMMAND_ID, "", );
+
/** @brief Command description for Sleep
*
* Command: Sleep
\
ZCL_SLEEP_COMMAND_ID, "", );
+/** @brief Command description for LaunchContent
+ *
+ * Command: LaunchContent
+ * @param contentLaunchStatus ContentLaunchStatus
+ */
+#define emberAfFillCommandContent \
+ LaunchClusterLaunchContent(contentLaunchStatus) \
+ emberAfFillExternalBuffer(mask, \
+ \
+ ZCL_LAUNCH_CONTENT_COMMAND_ID, "u", contentLaunchStatus);
+
+/** @brief Command description for LaunchURL
+ *
+ * Command: LaunchURL
+ * @param contentLaunchStatus ContentLaunchStatus
+ */
+#define emberAfFillCommandContent \
+ LaunchClusterLaunchURL(contentLaunchStatus) emberAfFillExternalBuffer(mask, \
+ \
+ ZCL_LAUNCH_URL_COMMAND_ID, "u", contentLaunchStatus);
+
/** @brief Command description for MatchProtocolAddress
*
* Command: MatchProtocolAddress
\
ZCL_UNBIND_COMMAND_ID, "uuuu", nodeId, groupId, endpointId, clusterId);
-/** @brief Command description for PlayRequest
- *
- * Command: PlayRequest
- */
-#define emberAfFillCommandMedia \
- PlaybackClusterPlayRequest() emberAfFillExternalBuffer(mask, \
- \
- ZCL_PLAY_REQUEST_COMMAND_ID, "", );
-
-/** @brief Command description for PauseRequest
- *
- * Command: PauseRequest
- */
-#define emberAfFillCommandMedia \
- PlaybackClusterPauseRequest() emberAfFillExternalBuffer(mask, \
- \
- ZCL_PAUSE_REQUEST_COMMAND_ID, "", );
-
-/** @brief Command description for StopRequest
- *
- * Command: StopRequest
- */
-#define emberAfFillCommandMedia \
- PlaybackClusterStopRequest() emberAfFillExternalBuffer(mask, \
- \
- ZCL_STOP_REQUEST_COMMAND_ID, "", );
-
-/** @brief Command description for StartOverRequest
- *
- * Command: StartOverRequest
- */
-#define emberAfFillCommandMedia \
- PlaybackClusterStartOverRequest() emberAfFillExternalBuffer(mask, \
- \
- ZCL_START_OVER_REQUEST_COMMAND_ID, "", );
-
-/** @brief Command description for PreviousRequest
- *
- * Command: PreviousRequest
- */
-#define emberAfFillCommandMedia \
- PlaybackClusterPreviousRequest() emberAfFillExternalBuffer(mask, \
- \
- ZCL_PREVIOUS_REQUEST_COMMAND_ID, "", );
-
-/** @brief Command description for NextRequest
- *
- * Command: NextRequest
- */
-#define emberAfFillCommandMedia \
- PlaybackClusterNextRequest() emberAfFillExternalBuffer(mask, \
- \
- ZCL_NEXT_REQUEST_COMMAND_ID, "", );
-
-/** @brief Command description for RewindRequest
- *
- * Command: RewindRequest
- */
-#define emberAfFillCommandMedia \
- PlaybackClusterRewindRequest() emberAfFillExternalBuffer(mask, \
- \
- ZCL_REWIND_REQUEST_COMMAND_ID, "", );
-
-/** @brief Command description for FastForwardRequest
- *
- * Command: FastForwardRequest
- */
-#define emberAfFillCommandMedia \
- PlaybackClusterFastForwardRequest() emberAfFillExternalBuffer(mask, \
- \
- ZCL_FAST_FORWARD_REQUEST_COMMAND_ID, "", );
-
-/** @brief Command description for SkipForwardRequest
- *
- * Command: SkipForwardRequest
- */
-#define emberAfFillCommandMedia \
- PlaybackClusterSkipForwardRequest() emberAfFillExternalBuffer(mask, \
- \
- ZCL_SKIP_FORWARD_REQUEST_COMMAND_ID, "", );
-
-/** @brief Command description for SkipBackwardRequest
- *
- * Command: SkipBackwardRequest
- */
-#define emberAfFillCommandMedia \
- PlaybackClusterSkipBackwardRequest() emberAfFillExternalBuffer(mask, \
- \
- ZCL_SKIP_BACKWARD_REQUEST_COMMAND_ID, "", );
-
-/** @brief Command description for LaunchContent
- *
- * Command: LaunchContent
- * @param contentLaunchStatus ContentLaunchStatus
- */
-#define emberAfFillCommandContent \
- LaunchClusterLaunchContent(contentLaunchStatus) \
- emberAfFillExternalBuffer(mask, \
- \
- ZCL_LAUNCH_CONTENT_COMMAND_ID, "u", contentLaunchStatus);
-
-/** @brief Command description for LaunchURL
- *
- * Command: LaunchURL
- * @param contentLaunchStatus ContentLaunchStatus
- */
-#define emberAfFillCommandContent \
- LaunchClusterLaunchURL(contentLaunchStatus) emberAfFillExternalBuffer(mask, \
- \
- ZCL_LAUNCH_URL_COMMAND_ID, "u", contentLaunchStatus);
-
/** @brief Command description for CommandOne
*
* Command: CommandOne
// Definitions for cluster: IAS WD
#define ZCL_IAS_WD_CLUSTER_ID (0x0502)
+// Definitions for cluster: Media Playback
+#define ZCL_MEDIA_PLAYBACK_CLUSTER_ID (0x0506)
+
// Definitions for cluster: Low Power
#define ZCL_LOW_POWER_CLUSTER_ID (0x0508)
+// Definitions for cluster: Content Launch
+#define ZCL_CONTENT_LAUNCH_CLUSTER_ID (0x050A)
+
// Definitions for cluster: Application Basic
#define ZCL_APPLICATION_BASIC_CLUSTER_ID (0x050D)
// Definitions for cluster: Binding
#define ZCL_BINDING_CLUSTER_ID (0xF000)
-// Definitions for cluster: Media Playback
-#define ZCL_MEDIA_PLAYBACK_CLUSTER_ID (0xF001)
-
-// Definitions for cluster: Content Launch
-#define ZCL_CONTENT_LAUNCH_CLUSTER_ID (0xF002)
-
// Definitions for cluster: Group Key Management
#define ZCL_GROUP_KEY_MANAGEMENT_CLUSTER_ID (0xF004)
#define ZCL_START_WARNING_COMMAND_ID (0x00)
#define ZCL_SQUAWK_COMMAND_ID (0x01)
+// Commands for cluster: Media Playback
+#define ZCL_PLAY_REQUEST_COMMAND_ID (0x00)
+#define ZCL_PLAYBACK_COMMAND_ID (0x00)
+#define ZCL_PAUSE_REQUEST_COMMAND_ID (0x01)
+#define ZCL_STOP_REQUEST_COMMAND_ID (0x02)
+#define ZCL_START_OVER_REQUEST_COMMAND_ID (0x03)
+#define ZCL_PREVIOUS_REQUEST_COMMAND_ID (0x04)
+#define ZCL_NEXT_REQUEST_COMMAND_ID (0x05)
+#define ZCL_REWIND_REQUEST_COMMAND_ID (0x06)
+#define ZCL_FAST_FORWARD_REQUEST_COMMAND_ID (0x07)
+#define ZCL_SKIP_FORWARD_REQUEST_COMMAND_ID (0x08)
+#define ZCL_SKIP_BACKWARD_REQUEST_COMMAND_ID (0x09)
+
// Commands for cluster: Low Power
#define ZCL_SLEEP_COMMAND_ID (0x00)
+// Commands for cluster: Content Launch
+#define ZCL_LAUNCH_CONTENT_COMMAND_ID (0x00)
+#define ZCL_LAUNCH_CONTENT_RESPONSE_COMMAND_ID (0x00)
+#define ZCL_LAUNCH_URL_COMMAND_ID (0x01)
+#define ZCL_LAUNCH_URL_RESPONSE_COMMAND_ID (0x01)
+
// Commands for cluster: Generic Tunnel
#define ZCL_MATCH_PROTOCOL_ADDRESS_COMMAND_ID (0x00)
#define ZCL_MATCH_PROTOCOL_ADDRESS_RESPONSE_COMMAND_ID (0x00)
#define ZCL_BIND_COMMAND_ID (0x00)
#define ZCL_UNBIND_COMMAND_ID (0x01)
-// Commands for cluster: Media Playback
-#define ZCL_PLAY_REQUEST_COMMAND_ID (0x00)
-#define ZCL_PLAYBACK_COMMAND_ID (0x00)
-#define ZCL_PAUSE_REQUEST_COMMAND_ID (0x01)
-#define ZCL_STOP_REQUEST_COMMAND_ID (0x02)
-#define ZCL_START_OVER_REQUEST_COMMAND_ID (0x03)
-#define ZCL_PREVIOUS_REQUEST_COMMAND_ID (0x04)
-#define ZCL_NEXT_REQUEST_COMMAND_ID (0x05)
-#define ZCL_REWIND_REQUEST_COMMAND_ID (0x06)
-#define ZCL_FAST_FORWARD_REQUEST_COMMAND_ID (0x07)
-#define ZCL_SKIP_FORWARD_REQUEST_COMMAND_ID (0x08)
-#define ZCL_SKIP_BACKWARD_REQUEST_COMMAND_ID (0x09)
-
-// Commands for cluster: Content Launch
-#define ZCL_LAUNCH_CONTENT_COMMAND_ID (0x00)
-#define ZCL_LAUNCH_CONTENT_RESPONSE_COMMAND_ID (0x00)
-#define ZCL_LAUNCH_URL_COMMAND_ID (0x01)
-#define ZCL_LAUNCH_URL_RESPONSE_COMMAND_ID (0x01)
-
// Commands for cluster: Sample Mfg Specific Cluster
#define ZCL_COMMAND_ONE_COMMAND_ID (0x00)
#define ZAP_ATTRIBUTE_MASK(mask) ATTRIBUTE_MASK_##mask
// This is an array of EmberAfAttributeMetadata structures.
-#define GENERATED_ATTRIBUTE_COUNT 16
+#define GENERATED_ATTRIBUTE_COUNT 14
#define GENERATED_ATTRIBUTES \
{ \
{ 0xFFFD, ZAP_TYPE(INT16U), 2, ZAP_ATTRIBUTE_MASK(CLIENT), \
ZAP_SIMPLE_DEFAULT(0x0001) }, /* Application Basic (client): cluster revision */ \
{ 0xFFFD, ZAP_TYPE(INT16U), 2, ZAP_ATTRIBUTE_MASK(CLIENT), \
ZAP_SIMPLE_DEFAULT(0x0001) }, /* Binding (client): cluster revision */ \
- { 0xFFFD, ZAP_TYPE(INT16U), 2, ZAP_ATTRIBUTE_MASK(CLIENT), \
- ZAP_SIMPLE_DEFAULT(0x0001) }, /* Media Playback (client): cluster revision */ \
- { 0xFFFD, ZAP_TYPE(INT16U), 2, ZAP_ATTRIBUTE_MASK(CLIENT), \
- ZAP_SIMPLE_DEFAULT(0x0001) }, /* Content Launch (client): cluster revision */ \
}
// This is an array of EmberAfCluster structures.
#define GENERATED_FUNCTION_ARRAYS
#define ZAP_CLUSTER_MASK(mask) CLUSTER_MASK_##mask
-#define GENERATED_CLUSTER_COUNT 16
+#define GENERATED_CLUSTER_COUNT 14
#define GENERATED_CLUSTERS \
{ \
{ 0x0003, ZAP_ATTRIBUTE_INDEX(0), 1, 2, ZAP_CLUSTER_MASK(CLIENT), NULL }, /* Endpoint: 1, Cluster: Identify (client) */ \
{ \
0xF000, ZAP_ATTRIBUTE_INDEX(13), 1, 2, ZAP_CLUSTER_MASK(CLIENT), NULL \
}, /* Endpoint: 1, Cluster: Binding (client) */ \
- { \
- 0xF001, ZAP_ATTRIBUTE_INDEX(14), 1, 2, ZAP_CLUSTER_MASK(CLIENT), NULL \
- }, /* Endpoint: 1, Cluster: Media Playback (client) */ \
- { \
- 0xF002, ZAP_ATTRIBUTE_INDEX(15), 1, 2, ZAP_CLUSTER_MASK(CLIENT), NULL \
- }, /* Endpoint: 1, Cluster: Content Launch (client) */ \
}
#define ZAP_CLUSTER_INDEX(index) ((EmberAfCluster *) (&generatedClusters[index]))
// This is an array of EmberAfEndpointType structures.
#define GENERATED_ENDPOINT_TYPES \
{ \
- { ZAP_CLUSTER_INDEX(0), 16, 32 }, \
+ { ZAP_CLUSTER_INDEX(0), 14, 28 }, \
}
// Largest attribute size is needed for various buffers
#define ATTRIBUTE_SINGLETONS_SIZE (2)
// Total size of attribute storage
-#define ATTRIBUTE_MAX_SIZE (32)
+#define ATTRIBUTE_MAX_SIZE (28)
// Number of fixed endpoints
#define FIXED_ENDPOINT_COUNT (1)
// Array of EmberAfCommandMetadata structs.
#define ZAP_COMMAND_MASK(mask) COMMAND_MASK_##mask
-#define EMBER_AF_GENERATED_COMMAND_COUNT (129)
+#define EMBER_AF_GENERATED_COMMAND_COUNT (114)
#define GENERATED_COMMANDS \
{ \
{ 0x0003, 0x00, ZAP_COMMAND_MASK(INCOMING_SERVER) }, /* Identify (client): Identify */ \
{ 0x0508, 0x00, ZAP_COMMAND_MASK(INCOMING_SERVER) }, /* Low Power (client): Sleep */ \
{ 0xF000, 0x00, ZAP_COMMAND_MASK(INCOMING_SERVER) }, /* Binding (client): Bind */ \
{ 0xF000, 0x01, ZAP_COMMAND_MASK(INCOMING_SERVER) }, /* Binding (client): Unbind */ \
- { 0xF001, 0x00, ZAP_COMMAND_MASK(INCOMING_SERVER) }, /* Media Playback (client): PlayRequest */ \
- { 0xF001, 0x00, ZAP_COMMAND_MASK(INCOMING_CLIENT) }, /* Media Playback (client): Playback */ \
- { 0xF001, 0x01, ZAP_COMMAND_MASK(INCOMING_SERVER) }, /* Media Playback (client): PauseRequest */ \
- { 0xF001, 0x02, ZAP_COMMAND_MASK(INCOMING_SERVER) }, /* Media Playback (client): StopRequest */ \
- { 0xF001, 0x03, ZAP_COMMAND_MASK(INCOMING_SERVER) }, /* Media Playback (client): StartOverRequest */ \
- { 0xF001, 0x04, ZAP_COMMAND_MASK(INCOMING_SERVER) }, /* Media Playback (client): PreviousRequest */ \
- { 0xF001, 0x05, ZAP_COMMAND_MASK(INCOMING_SERVER) }, /* Media Playback (client): NextRequest */ \
- { 0xF001, 0x06, ZAP_COMMAND_MASK(INCOMING_SERVER) }, /* Media Playback (client): RewindRequest */ \
- { 0xF001, 0x07, ZAP_COMMAND_MASK(INCOMING_SERVER) }, /* Media Playback (client): FastForwardRequest */ \
- { 0xF001, 0x08, ZAP_COMMAND_MASK(INCOMING_SERVER) }, /* Media Playback (client): SkipForwardRequest */ \
- { 0xF001, 0x09, ZAP_COMMAND_MASK(INCOMING_SERVER) }, /* Media Playback (client): SkipBackwardRequest */ \
- { 0xF002, 0x00, ZAP_COMMAND_MASK(INCOMING_SERVER) }, /* Content Launch (client): LaunchContent */ \
- { 0xF002, 0x00, ZAP_COMMAND_MASK(INCOMING_CLIENT) }, /* Content Launch (client): LaunchContentResponse */ \
- { 0xF002, 0x01, ZAP_COMMAND_MASK(INCOMING_SERVER) }, /* Content Launch (client): LaunchURL */ \
- { 0xF002, 0x01, ZAP_COMMAND_MASK(INCOMING_CLIENT) }, /* Content Launch (client): LaunchURLResponse */ \
}
// Array of EmberAfManufacturerCodeEntry structures for commands.
#define EMBER_AF_BASIC_CLUSTER_CLIENT_ENDPOINT_COUNT (1)
#define EMBER_AF_BINDING_CLUSTER_CLIENT_ENDPOINT_COUNT (1)
#define EMBER_AF_COLOR_CONTROL_CLUSTER_CLIENT_ENDPOINT_COUNT (1)
-#define EMBER_AF_CONTENT_LAUNCH_CLUSTER_CLIENT_ENDPOINT_COUNT (1)
#define EMBER_AF_DOOR_LOCK_CLUSTER_CLIENT_ENDPOINT_COUNT (1)
#define EMBER_AF_GENERAL_COMMISSIONING_CLUSTER_CLIENT_ENDPOINT_COUNT (1)
#define EMBER_AF_GROUPS_CLUSTER_CLIENT_ENDPOINT_COUNT (1)
#define EMBER_AF_IDENTIFY_CLUSTER_CLIENT_ENDPOINT_COUNT (1)
#define EMBER_AF_LEVEL_CONTROL_CLUSTER_CLIENT_ENDPOINT_COUNT (1)
#define EMBER_AF_LOW_POWER_CLUSTER_CLIENT_ENDPOINT_COUNT (1)
-#define EMBER_AF_MEDIA_PLAYBACK_CLUSTER_CLIENT_ENDPOINT_COUNT (1)
#define EMBER_AF_ON_OFF_CLUSTER_CLIENT_ENDPOINT_COUNT (1)
#define EMBER_AF_SCENES_CLUSTER_CLIENT_ENDPOINT_COUNT (1)
#define EMBER_AF_TEMP_MEASUREMENT_CLUSTER_CLIENT_ENDPOINT_COUNT (1)
#define ZCL_USING_COLOR_CONTROL_CLUSTER_CLIENT
#define EMBER_AF_PLUGIN_COLOR_CONTROL_CLIENT
-// Use this macro to check if the client side of the Content Launch cluster is included
-#define ZCL_USING_CONTENT_LAUNCH_CLUSTER_CLIENT
-#define EMBER_AF_PLUGIN_CONTENT_LAUNCH_CLIENT
-
// Use this macro to check if the client side of the Door Lock cluster is included
#define ZCL_USING_DOOR_LOCK_CLUSTER_CLIENT
#define EMBER_AF_PLUGIN_DOOR_LOCK_CLIENT
#define ZCL_USING_LOW_POWER_CLUSTER_CLIENT
#define EMBER_AF_PLUGIN_LOW_POWER_CLIENT
-// Use this macro to check if the client side of the Media Playback cluster is included
-#define ZCL_USING_MEDIA_PLAYBACK_CLUSTER_CLIENT
-#define EMBER_AF_PLUGIN_MEDIA_PLAYBACK_CLIENT
-
// Use this macro to check if the client side of the On/off cluster is included
#define ZCL_USING_ON_OFF_CLUSTER_CLIENT
#define EMBER_AF_PLUGIN_ON_OFF_CLIENT
#define CHIP_PRINTCLUSTER_IAS_WD_CLUSTER
#endif
+#if defined(ZCL_USING_MEDIA_PLAYBACK_CLUSTER_SERVER) || defined(ZCL_USING_MEDIA_PLAYBACK_CLUSTER_CLIENT)
+#define CHIP_PRINTCLUSTER_MEDIA_PLAYBACK_CLUSTER { ZCL_MEDIA_PLAYBACK_CLUSTER_ID, 1286, "Media Playback" },
+#else
+#define CHIP_PRINTCLUSTER_MEDIA_PLAYBACK_CLUSTER
+#endif
+
#if defined(ZCL_USING_LOW_POWER_CLUSTER_SERVER) || defined(ZCL_USING_LOW_POWER_CLUSTER_CLIENT)
#define CHIP_PRINTCLUSTER_LOW_POWER_CLUSTER { ZCL_LOW_POWER_CLUSTER_ID, 1288, "Low Power" },
#else
#define CHIP_PRINTCLUSTER_LOW_POWER_CLUSTER
#endif
+#if defined(ZCL_USING_CONTENT_LAUNCH_CLUSTER_SERVER) || defined(ZCL_USING_CONTENT_LAUNCH_CLUSTER_CLIENT)
+#define CHIP_PRINTCLUSTER_CONTENT_LAUNCH_CLUSTER { ZCL_CONTENT_LAUNCH_CLUSTER_ID, 1290, "Content Launch" },
+#else
+#define CHIP_PRINTCLUSTER_CONTENT_LAUNCH_CLUSTER
+#endif
+
#if defined(ZCL_USING_APPLICATION_BASIC_CLUSTER_SERVER) || defined(ZCL_USING_APPLICATION_BASIC_CLUSTER_CLIENT)
#define CHIP_PRINTCLUSTER_APPLICATION_BASIC_CLUSTER { ZCL_APPLICATION_BASIC_CLUSTER_ID, 1293, "Application Basic" },
#else
#define CHIP_PRINTCLUSTER_BINDING_CLUSTER
#endif
-#if defined(ZCL_USING_MEDIA_PLAYBACK_CLUSTER_SERVER) || defined(ZCL_USING_MEDIA_PLAYBACK_CLUSTER_CLIENT)
-#define CHIP_PRINTCLUSTER_MEDIA_PLAYBACK_CLUSTER { ZCL_MEDIA_PLAYBACK_CLUSTER_ID, 61441, "Media Playback" },
-#else
-#define CHIP_PRINTCLUSTER_MEDIA_PLAYBACK_CLUSTER
-#endif
-
-#if defined(ZCL_USING_CONTENT_LAUNCH_CLUSTER_SERVER) || defined(ZCL_USING_CONTENT_LAUNCH_CLUSTER_CLIENT)
-#define CHIP_PRINTCLUSTER_CONTENT_LAUNCH_CLUSTER { ZCL_CONTENT_LAUNCH_CLUSTER_ID, 61442, "Content Launch" },
-#else
-#define CHIP_PRINTCLUSTER_CONTENT_LAUNCH_CLUSTER
-#endif
-
#if defined(ZCL_USING_GROUP_KEY_MANAGEMENT_CLUSTER_SERVER) || defined(ZCL_USING_GROUP_KEY_MANAGEMENT_CLUSTER_CLIENT)
#define CHIP_PRINTCLUSTER_GROUP_KEY_MANAGEMENT_CLUSTER { ZCL_GROUP_KEY_MANAGEMENT_CLUSTER_ID, 61444, "Group Key Management" },
#else
CHIP_PRINTCLUSTER_IAS_ZONE_CLUSTER \
CHIP_PRINTCLUSTER_IAS_ACE_CLUSTER \
CHIP_PRINTCLUSTER_IAS_WD_CLUSTER \
+ CHIP_PRINTCLUSTER_MEDIA_PLAYBACK_CLUSTER \
CHIP_PRINTCLUSTER_LOW_POWER_CLUSTER \
+ CHIP_PRINTCLUSTER_CONTENT_LAUNCH_CLUSTER \
CHIP_PRINTCLUSTER_APPLICATION_BASIC_CLUSTER \
CHIP_PRINTCLUSTER_GENERIC_TUNNEL_CLUSTER \
CHIP_PRINTCLUSTER_BACNET_PROTOCOL_TUNNEL_CLUSTER \
CHIP_PRINTCLUSTER_DIAGNOSTICS_CLUSTER \
CHIP_PRINTCLUSTER_ZLL_COMMISSIONING_CLUSTER \
CHIP_PRINTCLUSTER_BINDING_CLUSTER \
- CHIP_PRINTCLUSTER_MEDIA_PLAYBACK_CLUSTER \
- CHIP_PRINTCLUSTER_CONTENT_LAUNCH_CLUSTER \
CHIP_PRINTCLUSTER_GROUP_KEY_MANAGEMENT_CLUSTER \
CHIP_PRINTCLUSTER_SAMPLE_MFG_SPECIFIC_CLUSTER \
CHIP_PRINTCLUSTER_SAMPLE_MFG_SPECIFIC_CLUSTER_2 \
{{/chip_server_cluster_command_arguments}}
ModelCommand::AddArguments();
}
+ ~{{asCamelCased clusterName false}}{{asCamelCased name false}}()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
ModelCommand::AddArguments();
}
+ ~Discover{{asCamelCased name false}}Attributes()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
+
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
ChipLogProgress(chipTool, "Sending cluster ({{asHex parent.code 4}}) command (0x0C) on endpoint %" PRIu16, endpointId);
ModelCommand::AddArguments();
}
+ ~Read{{asCamelCased parent.name false}}{{asCamelCased name false}}()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
+
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
ChipLogProgress(chipTool, "Sending cluster ({{asHex parent.code 4}}) command (0x00) on endpoint %" PRIu16, endpointId);
ModelCommand::AddArguments();
}
+ ~Write{{asCamelCased parent.name false}}{{asCamelCased name false}}()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ }
+
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
ChipLogProgress(chipTool, "Sending cluster ({{asHex parent.code 4}}) command (0x01) on endpoint %" PRIu16, endpointId);
ModelCommand::AddArguments();
}
+ ~Report{{asCamelCased parent.name false}}{{asCamelCased name false}}()
+ {
+ delete onSuccessCallback;
+ delete onFailureCallback;
+ delete onReportCallback;
+ }
+
CHIP_ERROR SendCommand(ChipDevice * device, uint8_t endpointId) override
{
ChipLogProgress(chipTool, "Sending cluster ({{asHex parent.code 4}}) command (0x06) on endpoint %" PRIu16, endpointId);
Listen() : ReportingCommand("listen")
{
}
+
+ ~Listen()
+ {
+{{#chip_clusters}}
+{{#chip_server_cluster_attributes}}
+{{#if (isReportableAttribute)}}
+ delete onReport{{asCamelCased parent.name false}}{{asCamelCased name false}}Callback;
+{{/if}}
+{{/chip_server_cluster_attributes}}
+{{/chip_clusters}}
+ }
void AddReportCallbacks(uint8_t endpointId) override
{
import("//build_overrides/pigweed.gni")
import("$dir_pw_build/target_types.gni")
+config("default_config") {
+ include_dirs = [ ".." ]
+}
+
pw_source_set("system_rpc_server") {
deps = [
"$dir_pw_hdlc:pw_rpc",
dir_pw_log,
]
sources = [ "system_rpc_server.cc" ]
+ public_configs = [ ":default_config" ]
}
#include "pw_stream/sys_io_stream.h"
#include "pw_sys_io/sys_io.h"
-#include "logging/CHIPLogging.h"
+#include "support/logging/CHIPLogging.h"
#include <array>
# Dump memory usage at link time.
chip_print_memory_usage = false
enable_pw_rpc = false
+ setupPinCode = 73141520
}
show_qr_code = true
"${efr32_project_dir}/include/FreeRTOSConfig.h",
]
- defines = [ "BOARD_ID=${efr32_board}" ]
+ defines = [
+ "BOARD_ID=${efr32_board}",
+ "CHIP_DEVICE_CONFIG_USE_TEST_SETUP_PIN_CODE=${setupPinCode}",
+ ]
if (enable_pw_rpc) {
defines += [
#define CHIP_DEVICE_CONFIG_ENABLE_TEST_DEVICE_IDENTITY 34
// Use a default pairing code if one hasn't been provisioned in flash.
+#ifndef CHIP_DEVICE_CONFIG_USE_TEST_SETUP_PIN_CODE
#define CHIP_DEVICE_CONFIG_USE_TEST_SETUP_PIN_CODE 12345678
+#endif
#define CHIP_DEVICE_CONFIG_USE_TEST_SETUP_DISCRIMINATOR 0xF00
// For convenience, Chip Security Test Mode can be enabled and the
/**
* CHIP_DEVICE_CONFIG_DEVICE_VENDOR_ID
*
- * 0xE100: Google's Vendor Id.
+ * 0x235A: Chip's Vendor Id.
*/
-#define CHIP_DEVICE_CONFIG_DEVICE_VENDOR_ID 0xE100
+#define CHIP_DEVICE_CONFIG_DEVICE_VENDOR_ID 0x235A
/**
* CHIP_DEVICE_CONFIG_DEVICE_PRODUCT_ID
*
- * 0xFE00: SDK Sample Light Resource
+ * 0x534C: EFR32 lighting-app
*/
-#define CHIP_DEVICE_CONFIG_DEVICE_PRODUCT_ID 0xFD00
+#define CHIP_DEVICE_CONFIG_DEVICE_PRODUCT_ID 0x534C
/**
* CHIP_DEVICE_CONFIG_DEVICE_PRODUCT_REVISION
* A size, in bytes, of the individual debug event logging buffer.
*/
#define CHIP_DEVICE_CONFIG_EVENT_LOGGING_DEBUG_BUFFER_SIZE (512)
+
+/**
+ * CHIP_DEVICE_CONFIG_BLE_FAST_ADVERTISING_INTERVAL
+ *
+ * The interval (in units of 0.625ms) at which the device will send BLE advertisements while
+ * in fast advertising mode.
+ *
+ * 40 (25ms).
+ */
+#define CHIP_DEVICE_CONFIG_BLE_FAST_ADVERTISING_INTERVAL 40
+
+/**
+ * CHIP_DEVICE_CONFIG_BLE_SLOW_ADVERTISING_INTERVAL
+ *
+ * The interval (in units of 0.625ms) at which the device will send BLE advertisements while
+ * in slow advertisement mode.
+ *
+ * 800 (500ms).
+ */
+#define CHIP_DEVICE_CONFIG_BLE_SLOW_ADVERTISING_INTERVAL 800
+
+/**
+ * CHIP_DEVICE_CONFIG_BLE_FAST_ADVERTISING_TIMEOUT
+ *
+ * The amount of time in miliseconds after which BLE should change his advertisements
+ * from fast interval to slow interval.
+ *
+ * 30000 (30 secondes).
+ */
+#define CHIP_DEVICE_CONFIG_BLE_FAST_ADVERTISING_TIMEOUT (30 * 1000)
+
+/**
+ * CHIP_DEVICE_CONFIG_BLE_ADVERTISING_TIMEOUT
+ *
+ * The amount of time in miliseconds after which BLE advertisement should be disabled, counting
+ * from the moment of slow advertisement commencement.
+ *
+ * Defaults to 9000000 (15 minutes).
+ */
+#define CHIP_DEVICE_CONFIG_BLE_ADVERTISING_TIMEOUT (15 * 60 * 1000)
#include <mbedtls/threading.h>
#include <platform/CHIPDeviceLayer.h>
+#include <platform/KeyValueStoreManager.h>
#include <support/CHIPMem.h>
#include <support/CHIPPlatformMemory.h>
// Init Chip memory management before the stack
chip::Platform::MemoryInit();
+ chip::DeviceLayer::PersistedStorage::KeyValueStoreMgrImpl().Init();
ret = PlatformMgr().InitChipStack();
if (ret != CHIP_NO_ERROR)
#pragma once
+/**
+ * CHIP_DEVICE_CONFIG_DEVICE_PRODUCT_ID
+ *
+ * 0x4E4C: nrfconnect lighting-app
+ */
+#define CHIP_DEVICE_CONFIG_DEVICE_PRODUCT_ID 0x4E4C
+
// Use a default pairing code if one hasn't been provisioned in flash.
#define CHIP_DEVICE_CONFIG_USE_TEST_SETUP_PIN_CODE 12345678
#define CHIP_DEVICE_CONFIG_USE_TEST_SETUP_DISCRIMINATOR 0xF00
/**
* CHIP_DEVICE_CONFIG_DEVICE_VENDOR_ID
*
- * 0xE100: Google's Vendor Id.
+ * 0x235A: Chip's Vendor Id.
*/
-#define CHIP_DEVICE_CONFIG_DEVICE_VENDOR_ID 0xE100
+#define CHIP_DEVICE_CONFIG_DEVICE_VENDOR_ID 0x235A
/**
* CHIP_DEVICE_CONFIG_DEVICE_PRODUCT_ID
*
- * 0xFE00: SDK Sample Lock Resource
+ * 0x434B: cc13x2x7_26x2x7 lock-app
*/
-#define CHIP_DEVICE_CONFIG_DEVICE_PRODUCT_ID 0xFE00
+#define CHIP_DEVICE_CONFIG_DEVICE_PRODUCT_ID 0x434B
/**
* CHIP_DEVICE_CONFIG_DEVICE_PRODUCT_REVISION
declare_args() {
# Dump memory usage at link time.
chip_print_memory_usage = false
+ setupPinCode = 73141520
}
show_qr_code = true
"${efr32_project_dir}/include/FreeRTOSConfig.h",
]
- defines = [ "BOARD_ID=${efr32_board}" ]
+ defines = [
+ "BOARD_ID=${efr32_board}",
+ "CHIP_DEVICE_CONFIG_USE_TEST_SETUP_PIN_CODE=${setupPinCode}",
+ ]
}
efr32_executable("lock_app") {
#define CHIP_DEVICE_CONFIG_ENABLE_TEST_DEVICE_IDENTITY 34
// Use a default pairing code if one hasn't been provisioned in flash.
+#ifndef CHIP_DEVICE_CONFIG_USE_TEST_SETUP_PIN_CODE
#define CHIP_DEVICE_CONFIG_USE_TEST_SETUP_PIN_CODE 12345678
+#endif
#define CHIP_DEVICE_CONFIG_USE_TEST_SETUP_DISCRIMINATOR 0xF00
// For convenience, Chip Security Test Mode can be enabled and the
/**
* CHIP_DEVICE_CONFIG_DEVICE_PRODUCT_ID
*
- * 0xFE00: SDK Sample Lock Resource
+ * 0x534B: EFR32 lock-app
*/
-#define CHIP_DEVICE_CONFIG_DEVICE_PRODUCT_ID 0xFE00
+#define CHIP_DEVICE_CONFIG_DEVICE_PRODUCT_ID 0x534B
/**
* CHIP_DEVICE_CONFIG_DEVICE_PRODUCT_REVISION
* A size, in bytes, of the individual debug event logging buffer.
*/
#define CHIP_DEVICE_CONFIG_EVENT_LOGGING_DEBUG_BUFFER_SIZE (512)
+
+/**
+ * CHIP_DEVICE_CONFIG_BLE_FAST_ADVERTISING_INTERVAL
+ *
+ * The interval (in units of 0.625ms) at which the device will send BLE advertisements while
+ * in fast advertising mode.
+ *
+ * 40 (25ms).
+ */
+#define CHIP_DEVICE_CONFIG_BLE_FAST_ADVERTISING_INTERVAL 40
+
+/**
+ * CHIP_DEVICE_CONFIG_BLE_SLOW_ADVERTISING_INTERVAL
+ *
+ * The interval (in units of 0.625ms) at which the device will send BLE advertisements while
+ * in slow advertisement mode.
+ *
+ * 800 (500ms).
+ */
+#define CHIP_DEVICE_CONFIG_BLE_SLOW_ADVERTISING_INTERVAL 800
+
+/**
+ * CHIP_DEVICE_CONFIG_BLE_FAST_ADVERTISING_TIMEOUT
+ *
+ * The amount of time in miliseconds after which BLE should change his advertisements
+ * from fast interval to slow interval.
+ *
+ * 30000 (30 secondes).
+ */
+#define CHIP_DEVICE_CONFIG_BLE_FAST_ADVERTISING_TIMEOUT (30 * 1000)
+
+/**
+ * CHIP_DEVICE_CONFIG_BLE_ADVERTISING_TIMEOUT
+ *
+ * The amount of time in miliseconds after which BLE advertisement should be disabled, counting
+ * from the moment of slow advertisement commencement.
+ *
+ * Defaults to 9000000 (15 minutes).
+ */
+#define CHIP_DEVICE_CONFIG_BLE_ADVERTISING_TIMEOUT (15 * 60 * 1000)
#include <mbedtls/threading.h>
#include <platform/CHIPDeviceLayer.h>
+#include <platform/KeyValueStoreManager.h>
#include <support/CHIPMem.h>
#include <support/CHIPPlatformMemory.h>
// Init Chip memory management before the stack
chip::Platform::MemoryInit();
+ chip::DeviceLayer::PersistedStorage::KeyValueStoreMgrImpl().Init();
ret = PlatformMgr().InitChipStack();
if (ret != CHIP_NO_ERROR)
#pragma once
+/**
+ * CHIP_DEVICE_CONFIG_DEVICE_PRODUCT_ID
+ *
+ * 0x4E4B: nrfconnect lock-app
+ */
+#define CHIP_DEVICE_CONFIG_DEVICE_PRODUCT_ID 0x4E4B
+
// Use a default pairing code if one hasn't been provisioned in flash.
#define CHIP_DEVICE_CONFIG_USE_TEST_SETUP_PIN_CODE 12345678
#define CHIP_DEVICE_CONFIG_USE_TEST_SETUP_DISCRIMINATOR 0xF00
#include <platform/KeyValueStoreManager.h>
#include <support/ErrorStr.h>
-#include <support/ReturnMacros.h>
#include <support/logging/CHIPLogging.h>
using namespace chip::DeviceLayer::PersistedStorage;
/**
* CHIP_DEVICE_CONFIG_DEVICE_VENDOR_ID
*
- * 0xE100: Google's Vendor Id.
+ * 0x235A: Chip's Vendor Id.
*/
-#define CHIP_DEVICE_CONFIG_DEVICE_VENDOR_ID 0xE100
+#define CHIP_DEVICE_CONFIG_DEVICE_VENDOR_ID 0x235A
/**
* CHIP_DEVICE_CONFIG_DEVICE_PRODUCT_ID
--- /dev/null
+#
+# Copyright (c) 2021 Project CHIP Authors
+# All rights reserved.
+#
+# Licensed under the Apache License, Version 2.0 (the "License");
+# you may not use this file except in compliance with the License.
+# You may obtain a copy of the License at
+#
+# http://www.apache.org/licenses/LICENSE-2.0
+#
+# Unless required by applicable law or agreed to in writing, software
+# distributed under the License is distributed on an "AS IS" BASIS,
+# WITHOUT WARRANTIES OR CONDITIONS OF ANY KIND, either express or implied.
+# See the License for the specific language governing permissions and
+# limitations under the License.
+
+# CMakeLists in this exact order for cmake to work correctly
+cmake_minimum_required(VERSION 3.5)
+include($ENV{IDF_PATH}/tools/cmake/project.cmake)
+
+# The list of extra component dirs must be in sync with that in persistent-storage/esp32/Makefile
+set(EXTRA_COMPONENT_DIRS
+ "${CMAKE_CURRENT_LIST_DIR}/third_party/connectedhomeip/config/esp32/components"
+)
+
+project(persistent-storage)
+idf_build_set_property(CXX_COMPILE_OPTIONS "-std=c++14;-Os;-DLWIP_IPV6_SCOPES=0;-DCHIP_HAVE_CONFIG_H" APPEND)
+idf_build_set_property(C_COMPILE_OPTIONS "-Os;-DLWIP_IPV6_SCOPES=0" APPEND)
Currently building in VSCode _and_ deploying from native is not supported, so
make sure the IDF_PATH has been exported(See the manual setup steps above).
-- In the root of the example directory, sync the CHIP tree's submodules and
- source `idf.sh`. Note: This does not have to be repeated for incremental
- builds.
+- Setting up the environment
- $ source idf.sh
+To download and install packages.
+
+ $ cd ${HOME}/tools/esp-idf
+ $ ./install.sh
+ $ . ./export.sh
+ $ cd {path-to-connectedhomeip}
+ $ source ./scripts/bootstrap.sh
+ $ source ./scripts/activate.sh
+ $ cd {path-to-connectedhomeip-examples}
+
+If packages are already installed then simply activate it.
+
+ $ cd ${HOME}/tools/esp-idf
+ $ ./install.sh
+ $ . ./export.sh
+ $ cd {path-to-connectedhomeip}
+ $ source ./scripts/activate.sh
+ $ cd {path-to-connectedhomeip-examples}
- Configuration Options
- To use the default configuration options, run the default config
+ To choose from the different configuration options, run menuconfig
- $ idf make defconfig
+ $ idf.py menuconfig
-- Run make to build the demo application.
+- To build the demo application.
- $ idf make
+ $ idf.py build
<a name="flashing"></a>
before flashing. For ESP32-DevKitC devices this is labeled in the
[functional description diagram](https://docs.espressif.com/projects/esp-idf/en/latest/esp32/hw-reference/esp32/get-started-devkitc.html#functional-description).
- $ idf make flash ESPPORT=/dev/tty.SLAB_USBtoUART
+ $ idf.py flash monitor ESPPORT=/dev/tty.SLAB_USBtoUART
Note: Some users might have to install the
[VCP driver](https://www.silabs.com/products/development-tools/software/usb-to-uart-bridge-vcp-drivers)
--- /dev/null
+#
+# Copyright (c) 2021 Project CHIP Authors
+# All rights reserved.
+#
+# Licensed under the Apache License, Version 2.0 (the "License");
+# you may not use this file except in compliance with the License.
+# You may obtain a copy of the License at
+#
+# http://www.apache.org/licenses/LICENSE-2.0
+#
+# Unless required by applicable law or agreed to in writing, software
+# distributed under the License is distributed on an "AS IS" BASIS,
+# WITHOUT WARRANTIES OR CONDITIONS OF ANY KIND, either express or implied.
+# See the License for the specific language governing permissions and
+# limitations under the License.
+#
+
+# The list of src and include dirs must be in sync with that in persistent-storage/esp32/main/component.mk
+idf_component_register(PRIV_INCLUDE_DIRS
+ "${CMAKE_CURRENT_LIST_DIR}"
+ "${CMAKE_SOURCE_DIR}/.."
+ SRC_DIRS
+ "${CMAKE_CURRENT_LIST_DIR}"
+ "${CMAKE_SOURCE_DIR}/.."
+ PRIV_REQUIRES chip nvs_flash)
+
+set_property(TARGET ${COMPONENT_LIB} PROPERTY CXX_STANDARD 14)
+target_compile_options(${COMPONENT_LIB} PRIVATE "-DLWIP_IPV6_SCOPES=0" "-DCHIP_HAVE_CONFIG_H")
# Use a custom partition table
CONFIG_PARTITION_TABLE_CUSTOM=y
CONFIG_PARTITION_TABLE_FILENAME="partitions.csv"
+
+# Vendor and product id
+CONFIG_DEVICE_VENDOR_ID=0x235A
+CONFIG_DEVICE_PRODUCT_ID=0x4553
sources = [
"${efr32_project_dir}/include/CHIPProjectConfig.h",
"${efr32_project_dir}/include/FreeRTOSConfig.h",
+ "${efr32_sdk_root}/hardware/kit/common/drivers/retargetserial.c",
]
defines = [
"BOARD_ID=${efr32_board}",
- "HAL_VCOM_ENABLE = 1",
- "EFR32_LOG_ENABLED = 1",
+ "HAL_VCOM_ENABLE=1",
+ "EFR32_LOG_ENABLED=1",
"PW_RPC_ENABLED",
]
}
"$dir_pw_assert",
"$dir_pw_checksum",
"${chip_root}/config/efr32/lib/pw_rpc:pw_rpc",
+ "${chip_root}/examples/common/pigweed:system_rpc_server",
"${chip_root}/src/lib",
"${examples_plat_dir}/pw_sys_io:pw_sys_io_efr32",
]
- include_dirs += [
- "include",
- "${examples_plat_dir}",
- "${examples_plat_dir}/${efr32_family}/${efr32_board}",
- "${examples_plat_dir}/pw_sys_io/public",
- "${dir_pigweed}/pw_sys_io/public",
- "${dir_pigweed}/pw_span/public_overrides",
- "${dir_pigweed}/pw_span/public",
- "${dir_pigweed}/pw_polyfill/public",
- "${dir_pigweed}/pw_polyfill/standard_library_public",
- "${dir_pigweed}/pw_polyfill/public_overrides",
- "${dir_pigweed}/pw_status/public",
- "${dir_pigweed}/pw_stream/public",
- "${dir_pigweed}/pw_preprocessor/public",
- "${dir_pigweed}/pw_rpc/public",
- "${dir_pigweed}/pw_rpc/nanopb/public",
- "${dir_pigweed}/pw_rpc/raw/public",
- "${dir_pigweed}/pw_rpc/system_server/public",
- "${dir_pigweed}/pw_protobuf/public",
- "${dir_pigweed}/pw_result/public",
- "${dir_pigweed}/pw_varint/public",
- "${chip_root}/third_party/nanopb/repo",
- "${chip_root}/src/lib/support",
- "${chip_root}/examples/common",
- "${chip_root}/examples/common/pigweed/efr32",
- "out/debug/gen/third_party/connectedhomeip/third_party/pigweed/repo/pw_rpc/protos",
- ]
+ include_dirs += [ "${chip_root}/examples/common/pigweed/efr32" ]
sources = [
"${chip_root}/examples/common/pigweed/RpcService.cpp",
/**
* CHIP_DEVICE_CONFIG_DEVICE_PRODUCT_ID
*
- * 0xFE00: SDK Sample Lock Resource
+ * 0x5350: EFR32 pigweed-app
*/
-#define CHIP_DEVICE_CONFIG_DEVICE_PRODUCT_ID 0xFE00
+#define CHIP_DEVICE_CONFIG_DEVICE_PRODUCT_ID 0x5350
/**
* CHIP_DEVICE_CONFIG_DEVICE_PRODUCT_REVISION
# Enable Pigweed RPC Library in CHIP
CONFIG_ENABLE_PW_RPC=y
+
+# Vendor and product id
+CONFIG_DEVICE_VENDOR_ID=0x235A
+CONFIG_DEVICE_PRODUCT_ID=0x4550
/**
* CHIP_DEVICE_CONFIG_DEVICE_PRODUCT_ID
*
- * 0xFE00: SDK Sample Lock Resource
+ * 0x4B4C: K32W lighting-app
*/
-#define CHIP_DEVICE_CONFIG_DEVICE_PRODUCT_ID 0xFE00
+#define CHIP_DEVICE_CONFIG_DEVICE_PRODUCT_ID 0x4B4C
/**
* CHIP_DEVICE_CONFIG_DEVICE_PRODUCT_REVISION
/**
* CHIP_DEVICE_CONFIG_DEVICE_VENDOR_ID
*
- * 0xE100: Google's Vendor Id.
+ * 0x235A: Chip's Vendor Id.
*/
-#define CHIP_DEVICE_CONFIG_DEVICE_VENDOR_ID 0xE100
+#define CHIP_DEVICE_CONFIG_DEVICE_VENDOR_ID 0x235A
/**
* CHIP_DEVICE_CONFIG_DEVICE_PRODUCT_ID
*
- * 0xFE00: SDK Sample Lock Resource
+ * 0x514C: qpg6100 lighting-app
*/
-#define CHIP_DEVICE_CONFIG_DEVICE_PRODUCT_ID 0xFE00
+#define CHIP_DEVICE_CONFIG_DEVICE_PRODUCT_ID 0x514C
/**
* CHIP_DEVICE_CONFIG_DEVICE_PRODUCT_REVISION
#define CHIP_CONFIG_ENABLE_ARG_PARSER 1
#define CHIP_DEVICE_CONFIG_DISABLE_SHELL_PING 1
+
+/**
+ * CHIP_DEVICE_CONFIG_DEVICE_PRODUCT_ID
+ *
+ * 0x4E53: nrfconnect shell
+ */
+#define CHIP_DEVICE_CONFIG_DEVICE_PRODUCT_ID 0x4E53
${APP_ROOT}/shell_common/cmd_device.cpp
${APP_ROOT}/shell_common/cmd_misc.cpp
${APP_ROOT}/shell_common/cmd_otcli.cpp
+ ${APP_ROOT}/shell_common/cmd_ping.cpp
${APP_ROOT}/shell_common/cmd_btp.cpp
${APP_ROOT}/standalone/main.cpp
)
#if CHIP_DEVICE_CONFIG_ENABLE_THREAD
streamer_printf(sout, "Init Thread stack\r\n");
- error = ThreadStackMgr().InitThreadStack();
- VerifyOrExit(error == CHIP_NO_ERROR, streamer_printf(sout, "ThreadStackMgr().InitThreadStack() failed\r\n"));
+ if (ThreadStackMgr().InitThreadStack() != CHIP_NO_ERROR)
+ {
+ streamer_printf(sout, "ThreadStackMgr().InitThreadStack() failed\r\n");
+ }
#endif
// Starting Platform Manager Event Loop;
#include <stdio.h>
#include <stdlib.h>
-#include <core/CHIPCore.h>
+#include <lib/core/CHIPCore.h>
+#include <lib/shell/shell.h>
+#include <lib/support/CodeUtils.h>
+#include <lib/support/ErrorStr.h>
#include <messaging/ExchangeMgr.h>
#include <platform/CHIPDeviceLayer.h>
#include <protocols/echo/Echo.h>
-#include <shell/shell.h>
-#include <support/CodeUtils.h>
-#include <support/ErrorStr.h>
#include <system/SystemPacketBuffer.h>
#include <transport/PASESession.h>
#include <transport/SecureSessionMgr.h>
using namespace Shell;
using namespace Logging;
+#if INET_CONFIG_ENABLE_TCP_ENDPOINT
constexpr size_t kMaxTcpActiveConnectionCount = 4;
constexpr size_t kMaxTcpPendingPackets = 4;
-constexpr size_t kNetworkSleepTimeMsecs = (100 * 1000);
-constexpr size_t kDecimalDigitsForUint64 = 20;
+#endif
+constexpr size_t kDecimalDigitsForUint64 = 20;
namespace {
mEchoCount = 0;
mEchoRespCount = 0;
mWaitingForEchoResp = false;
- mUsingTCP = false;
- mUsingCRMP = true;
- mEchoPort = CHIP_PORT;
+#if INET_CONFIG_ENABLE_TCP_ENDPOINT
+ mUsingTCP = false;
+#endif
+ mUsingCRMP = true;
+ mEchoPort = CHIP_PORT;
}
uint64_t GetLastEchoTime() const { return mLastEchoTime; }
bool IsWaitingForEchoResp() const { return mWaitingForEchoResp; }
void SetWaitingForEchoResp(bool value) { mWaitingForEchoResp = value; }
+#if INET_CONFIG_ENABLE_TCP_ENDPOINT
bool IsUsingTCP() const { return mUsingTCP; }
void SetUsingTCP(bool value) { mUsingTCP = value; }
+#endif
bool IsUsingCRMP() const { return mUsingCRMP; }
void SetUsingCRMP(bool value) { mUsingCRMP = value; }
// after sending an echo request, false otherwise.
bool mWaitingForEchoResp;
+#if INET_CONFIG_ENABLE_TCP_ENDPOINT
bool mUsingTCP;
+#endif
+
bool mUsingCRMP;
} gPingArguments;
constexpr Transport::AdminId gAdminId = 0;
Protocols::Echo::EchoClient gEchoClient;
+
TransportMgr<Transport::UDP> gUDPManager;
+
+#if INET_CONFIG_ENABLE_TCP_ENDPOINT
TransportMgr<Transport::TCP<kMaxTcpActiveConnectionCount, kMaxTcpPendingPackets>> gTCPManager;
+#endif
+
Messaging::ExchangeManager gExchangeManager;
SecureSessionMgr gSessionManager;
Inet::IPAddress gDestAddr;
SecurePairingUsingTestSecret * testSecurePairingSecret = chip::Platform::New<SecurePairingUsingTestSecret>();
VerifyOrExit(testSecurePairingSecret != nullptr, err = CHIP_ERROR_NO_MEMORY);
+#if INET_CONFIG_ENABLE_TCP_ENDPOINT
if (gPingArguments.IsUsingTCP())
{
peerAddr = Optional<Transport::PeerAddress>::Value(Transport::PeerAddress::TCP(gDestAddr, gPingArguments.GetEchoPort()));
}
else
+#endif
{
peerAddr = Optional<Transport::PeerAddress>::Value(
Transport::PeerAddress::UDP(gDestAddr, gPingArguments.GetEchoPort(), INET_NULL_INTERFACEID));
payload->DataLength(), static_cast<double>(transitTime) / 1000);
}
-void DriveIO(streamer_t * stream)
-{
- struct timeval sleepTime;
- fd_set readFDs, writeFDs, exceptFDs;
- int numFDs = 0;
- int selectRes;
-
- sleepTime.tv_sec = 0;
- sleepTime.tv_usec = kNetworkSleepTimeMsecs;
-
- FD_ZERO(&readFDs);
- FD_ZERO(&writeFDs);
- FD_ZERO(&exceptFDs);
-
- if (chip::DeviceLayer::SystemLayer.State() == chip::System::kLayerState_Initialized)
- chip::DeviceLayer::SystemLayer.PrepareSelect(numFDs, &readFDs, &writeFDs, &exceptFDs, sleepTime);
-
- if (chip::DeviceLayer::InetLayer.State == chip::Inet::InetLayer::kState_Initialized)
- chip::DeviceLayer::InetLayer.PrepareSelect(numFDs, &readFDs, &writeFDs, &exceptFDs, sleepTime);
-
- selectRes = select(numFDs, &readFDs, &writeFDs, &exceptFDs, &sleepTime);
- if (selectRes < 0)
- {
- streamer_printf(stream, "Select failed: %s\n", chip::ErrorStr(chip::System::MapErrorPOSIX(errno)));
- return;
- }
-
- if (chip::DeviceLayer::SystemLayer.State() == chip::System::kLayerState_Initialized)
- {
- chip::DeviceLayer::SystemLayer.HandleSelectResult(selectRes, &readFDs, &writeFDs, &exceptFDs);
- }
-
- if (chip::DeviceLayer::InetLayer.State == chip::Inet::InetLayer::kState_Initialized)
- {
- chip::DeviceLayer::InetLayer.HandleSelectResult(selectRes, &readFDs, &writeFDs, &exceptFDs);
- }
-}
-
void StartPinging(streamer_t * stream, char * destination)
{
CHIP_ERROR err = CHIP_NO_ERROR;
adminInfo = admins.AssignAdminId(gAdminId, kTestControllerNodeId);
VerifyOrExit(adminInfo != nullptr, err = CHIP_ERROR_NO_MEMORY);
+#if INET_CONFIG_ENABLE_TCP_ENDPOINT
err = gTCPManager.Init(Transport::TcpListenParameters(&DeviceLayer::InetLayer)
- .SetAddressType(Inet::kIPAddressType_IPv4)
+ .SetAddressType(gDestAddr.Type())
.SetListenPort(gPingArguments.GetEchoPort() + 1));
- VerifyOrExit(err == CHIP_NO_ERROR, streamer_printf(stream, "Failed to init TCP manager error: %s\r\n", ErrorStr(err)));
+ VerifyOrExit(err == CHIP_NO_ERROR, streamer_printf(stream, "Failed to init TCP manager error: %s\n", ErrorStr(err)));
+#endif
err = gUDPManager.Init(Transport::UdpListenParameters(&DeviceLayer::InetLayer)
- .SetAddressType(Inet::kIPAddressType_IPv4)
+ .SetAddressType(gDestAddr.Type())
.SetListenPort(gPingArguments.GetEchoPort() + 1));
- VerifyOrExit(err == CHIP_NO_ERROR, streamer_printf(stream, "Failed to init UDP manager error: %s\r\n", ErrorStr(err)));
+ VerifyOrExit(err == CHIP_NO_ERROR, streamer_printf(stream, "Failed to init UDP manager error: %s\n", ErrorStr(err)));
+#if INET_CONFIG_ENABLE_TCP_ENDPOINT
if (gPingArguments.IsUsingTCP())
{
err = gSessionManager.Init(kTestControllerNodeId, &DeviceLayer::SystemLayer, &gTCPManager, &admins);
SuccessOrExit(err);
}
else
+#endif
{
err = gSessionManager.Init(kTestControllerNodeId, &DeviceLayer::SystemLayer, &gUDPManager, &admins);
SuccessOrExit(err);
for (unsigned int i = 0; i < maxEchoCount; i++)
{
err = SendEchoRequest(stream);
+
if (err != CHIP_NO_ERROR)
{
streamer_printf(stream, "Send request failed: %s\n", ErrorStr(err));
// Wait for response until the Echo interval.
while (!EchoIntervalExpired())
{
- DriveIO(stream);
+ // TODO:#5496: Use condition_varible to suspend the current thread and wake it up when response arrive.
+ sleep(1);
}
// Check if expected response was received.
// Need to split the help info to prevent overflowing the streamer_printf
// buffer (CONSOLE_DEFAULT_MAX_LINE 256)
streamer_printf(stream, " -h print help information\n");
+#if INET_CONFIG_ENABLE_TCP_ENDPOINT
streamer_printf(stream, " -u use UDP (default)\n");
streamer_printf(stream, " -t use TCP\n");
+#endif
streamer_printf(stream, " -p <port> echo server port\n");
streamer_printf(stream, " -i <interval> ping interval time in seconds\n");
streamer_printf(stream, " -c <count> stop after <count> replies\n");
case 'h':
PrintUsage(sout);
return 0;
+#if INET_CONFIG_ENABLE_TCP_ENDPOINT
case 'u':
gPingArguments.SetUsingTCP(false);
break;
case 't':
gPingArguments.SetUsingTCP(true);
break;
+#endif
case 'i':
if (++optIndex >= argc || argv[optIndex][0] == '-')
{
cmd_device_init();
cmd_btp_init();
cmd_otcli_init();
-
-#ifndef CHIP_DEVICE_CONFIG_DISABLE_SHELL_PING
cmd_ping_init();
-#endif
shell_task(nullptr);
return 0;
--- /dev/null
+#
+# Copyright (c) 2021 Project CHIP Authors
+# All rights reserved.
+#
+# Licensed under the Apache License, Version 2.0 (the "License");
+# you may not use this file except in compliance with the License.
+# You may obtain a copy of the License at
+#
+# http://www.apache.org/licenses/LICENSE-2.0
+#
+# Unless required by applicable law or agreed to in writing, software
+# distributed under the License is distributed on an "AS IS" BASIS,
+# WITHOUT WARRANTIES OR CONDITIONS OF ANY KIND, either express or implied.
+# See the License for the specific language governing permissions and
+# limitations under the License.
+
+# The following lines of boilerplate have to be in your project's
+# CMakeLists in this exact order for cmake to work correctly
+cmake_minimum_required(VERSION 3.5)
+include($ENV{IDF_PATH}/tools/cmake/project.cmake)
+
+# The list of extra component dirs must be in sync with that in temperature-measurement-app/esp32/Makefile
+set(EXTRA_COMPONENT_DIRS
+ "${CMAKE_CURRENT_LIST_DIR}/third_party/connectedhomeip/config/esp32/components"
+ "${CMAKE_CURRENT_LIST_DIR}/../../common/m5stack-tft/repo/components"
+ "${CMAKE_CURRENT_LIST_DIR}/../../common/QRCode"
+ "${CMAKE_CURRENT_LIST_DIR}/../../common/screen-framework"
+)
+
+project(chip-temperature-measurement-app)
+idf_build_set_property(CXX_COMPILE_OPTIONS "-std=c++14;-Os;-DLWIP_IPV6_SCOPES=0;-DCHIP_HAVE_CONFIG_H" APPEND)
+idf_build_set_property(C_COMPILE_OPTIONS "-Os;-DLWIP_IPV6_SCOPES=0" APPEND)
Currently building in VSCode _and_ deploying from native is not supported, so
make sure the IDF_PATH has been exported(See the manual setup steps above).
-- In the root of the example directory, sync the CHIP tree's submodules and
- source `idf.sh`. Note: This does not have to be repeated for incremental
- builds.
+- Setting up the environment
- $ source idf.sh
+To download and install packages.
+
+ $ cd ${HOME}/tools/esp-idf
+ $ ./install.sh
+ $ . ./export.sh
+ $ cd {path-to-connectedhomeip}
+ $ source ./scripts/bootstrap.sh
+ $ source ./scripts/activate.sh
+ $ cd {path-to-connectedhomeip-examples}
+
+If packages are already installed then simply activate it.
+
+ $ cd ${HOME}/tools/esp-idf
+ $ ./install.sh
+ $ . ./export.sh
+ $ cd {path-to-connectedhomeip}
+ $ source ./scripts/activate.sh
+ $ cd {path-to-connectedhomeip-examples}
- Configuration Options
To choose from the different configuration options, run menuconfig
- $ idf make menuconfig
+ $ idf.py menuconfig
Select ESP32 based `Device Type` through `Demo`->`Device Type`.
The device types that are currently supported include `ESP32-DevKitC` (default),
`Component config`->`CHIP Device Layer`->`WiFi Station Options`->`Default WiFi SSID` and
`Default WiFi Password` respectively.
- To use the default configuration options, run the default config
- $ idf make defconfig
+- To build the demo application.
-- Run make to build the demo application.
-
- $ idf make
+ $ idf.py build
- After building the application, to flash it outside of VSCode, connect your
device via USB. Then run the following command to flash the demo application
before flashing. For ESP32-DevKitC devices this is labeled in the
[functional description diagram](https://docs.espressif.com/projects/esp-idf/en/latest/esp32/hw-reference/esp32/get-started-devkitc.html#functional-description).
- $ idf make flash monitor ESPPORT=/dev/ttyUSB0
+ $ idf.py flash monitor ESPPORT=/dev/ttyUSB0
Note: Some users might have to install the
[VCP driver](https://www.silabs.com/products/development-tools/software/usb-to-uart-bridge-vcp-drivers)
- If desired, the monitor can be run again like so:
- $ idf make monitor ESPPORT=/dev/ttyUSB0
+ $ idf.py monitor ESPPORT=/dev/ttyUSB0
## Using the Echo Server
--- /dev/null
+#
+# Copyright (c) 2021 Project CHIP Authors
+# All rights reserved.
+#
+# Licensed under the Apache License, Version 2.0 (the "License");
+# you may not use this file except in compliance with the License.
+# You may obtain a copy of the License at
+#
+# http://www.apache.org/licenses/LICENSE-2.0
+#
+# Unless required by applicable law or agreed to in writing, software
+# distributed under the License is distributed on an "AS IS" BASIS,
+# WITHOUT WARRANTIES OR CONDITIONS OF ANY KIND, either express or implied.
+# See the License for the specific language governing permissions and
+# limitations under the License.
+#
+#
+# (Uses default behaviour of compiling all source files in directory, adding 'include' to include path.)
+# The list of src and include dirs must be in sync with that in temperature-measurement-app/esp32/main/component.mk
+idf_component_register(PRIV_INCLUDE_DIRS
+ "${CMAKE_CURRENT_LIST_DIR}"
+ "${CMAKE_SOURCE_DIR}/third_party/connectedhomeip/src/app"
+ "${CMAKE_SOURCE_DIR}/third_party/connectedhomeip/src/app/util"
+ "${CMAKE_SOURCE_DIR}/third_party/connectedhomeip/src/app/reporting"
+ "${CMAKE_SOURCE_DIR}/third_party/connectedhomeip/src/app/server"
+ "${CMAKE_SOURCE_DIR}/third_party/connectedhomeip/third_party/nlio/repo/include"
+ "${CMAKE_SOURCE_DIR}/third_party/connectedhomeip/src"
+ "${CMAKE_CURRENT_LIST_DIR}/include"
+ SRC_DIRS
+ "${CMAKE_CURRENT_LIST_DIR}"
+ "${CMAKE_CURRENT_LIST_DIR}/gen"
+ "${CMAKE_SOURCE_DIR}/third_party/connectedhomeip/src/app/server"
+ "${CMAKE_SOURCE_DIR}/third_party/connectedhomeip/src/app/util"
+ "${CMAKE_SOURCE_DIR}/third_party/connectedhomeip/src/app/reporting"
+ "${CMAKE_SOURCE_DIR}/third_party/connectedhomeip/src/app/clusters/basic"
+ "${CMAKE_SOURCE_DIR}/third_party/connectedhomeip/src/app/clusters/bindings"
+ "${CMAKE_SOURCE_DIR}/third_party/connectedhomeip/src/app/clusters/network-commissioning"
+ "${CMAKE_SOURCE_DIR}/third_party/connectedhomeip/src/app/clusters/temperature-measurement-server"
+ PRIV_REQUIRES chip QRCode tft spidriver bt screen-framework)
+
+set_property(TARGET ${COMPONENT_LIB} PROPERTY CXX_STANDARD 14)
+target_compile_options(${COMPONENT_LIB} PRIVATE "-DLWIP_IPV6_SCOPES=0" "-DCHIP_HAVE_CONFIG_H")
CONFIG_NIMBLE_MAX_CONNECTIONS=1
CONFIG_TCPIP_RECVMBOX_SIZE=16
CONFIG_TCP_SYNMAXRTX=6
+
+# Product id
+CONFIG_DEVICE_VENDOR_ID=0x235A
+CONFIG_DEVICE_PRODUCT_ID=0x4554
CHIPDefaultFailureCallbackBridge * callback = reinterpret_cast<CHIPDefaultFailureCallbackBridge *>(context);
if (callback && callback->mQueue) {
dispatch_async(callback->mQueue, ^{
- NSError * error = [NSError errorWithDomain:CHIPErrorDomain
- code:status
- userInfo:@ { NSLocalizedDescriptionKey : @"" }];
+ NSError * error = [CHIPError errorForCHIPErrorCode:status];
callback->mHandler(error, nil);
callback->Cancel();
delete callback;
} // namespace ColorControl
-namespace ContentLaunch {
-
-void DispatchServerCommand(app::Command * command, CommandId commandId, EndpointId endpointId, TLV::TLVReader & dataTlv)
-{
- {
- switch (commandId)
- {
- case ZCL_LAUNCH_CONTENT_COMMAND_ID: {
- // TODO(#5098) We should pass the Command Object and EndpointId to the cluster callbacks.
- emberAfContentLaunchClusterLaunchContentCallback();
- break;
- }
- case ZCL_LAUNCH_URL_COMMAND_ID: {
- // TODO(#5098) We should pass the Command Object and EndpointId to the cluster callbacks.
- emberAfContentLaunchClusterLaunchURLCallback();
- break;
- }
- default: {
- // Unrecognized command ID, error status will apply.
- // TODO: Encode response for command not found
- ChipLogError(Zcl, "Unknown command %" PRIx16 " for cluster %" PRIx16, commandId, ZCL_CONTENT_LAUNCH_CLUSTER_ID);
- break;
- }
- }
- }
-}
-
-} // namespace ContentLaunch
-
namespace DoorLock {
void DispatchClientCommand(app::Command * command, CommandId commandId, EndpointId endpointId, TLV::TLVReader & dataTlv)
} // namespace LowPower
-namespace MediaPlayback {
-
-void DispatchServerCommand(app::Command * command, CommandId commandId, EndpointId endpointId, TLV::TLVReader & dataTlv)
-{
- {
- switch (commandId)
- {
- case ZCL_FAST_FORWARD_REQUEST_COMMAND_ID: {
- // TODO(#5098) We should pass the Command Object and EndpointId to the cluster callbacks.
- emberAfMediaPlaybackClusterFastForwardRequestCallback();
- break;
- }
- case ZCL_NEXT_REQUEST_COMMAND_ID: {
- // TODO(#5098) We should pass the Command Object and EndpointId to the cluster callbacks.
- emberAfMediaPlaybackClusterNextRequestCallback();
- break;
- }
- case ZCL_PAUSE_REQUEST_COMMAND_ID: {
- // TODO(#5098) We should pass the Command Object and EndpointId to the cluster callbacks.
- emberAfMediaPlaybackClusterPauseRequestCallback();
- break;
- }
- case ZCL_PLAY_REQUEST_COMMAND_ID: {
- // TODO(#5098) We should pass the Command Object and EndpointId to the cluster callbacks.
- emberAfMediaPlaybackClusterPlayRequestCallback();
- break;
- }
- case ZCL_PREVIOUS_REQUEST_COMMAND_ID: {
- // TODO(#5098) We should pass the Command Object and EndpointId to the cluster callbacks.
- emberAfMediaPlaybackClusterPreviousRequestCallback();
- break;
- }
- case ZCL_REWIND_REQUEST_COMMAND_ID: {
- // TODO(#5098) We should pass the Command Object and EndpointId to the cluster callbacks.
- emberAfMediaPlaybackClusterRewindRequestCallback();
- break;
- }
- case ZCL_SKIP_BACKWARD_REQUEST_COMMAND_ID: {
- // TODO(#5098) We should pass the Command Object and EndpointId to the cluster callbacks.
- emberAfMediaPlaybackClusterSkipBackwardRequestCallback();
- break;
- }
- case ZCL_SKIP_FORWARD_REQUEST_COMMAND_ID: {
- // TODO(#5098) We should pass the Command Object and EndpointId to the cluster callbacks.
- emberAfMediaPlaybackClusterSkipForwardRequestCallback();
- break;
- }
- case ZCL_START_OVER_REQUEST_COMMAND_ID: {
- // TODO(#5098) We should pass the Command Object and EndpointId to the cluster callbacks.
- emberAfMediaPlaybackClusterStartOverRequestCallback();
- break;
- }
- case ZCL_STOP_REQUEST_COMMAND_ID: {
- // TODO(#5098) We should pass the Command Object and EndpointId to the cluster callbacks.
- emberAfMediaPlaybackClusterStopRequestCallback();
- break;
- }
- default: {
- // Unrecognized command ID, error status will apply.
- // TODO: Encode response for command not found
- ChipLogError(Zcl, "Unknown command %" PRIx16 " for cluster %" PRIx16, commandId, ZCL_MEDIA_PLAYBACK_CLUSTER_ID);
- break;
- }
- }
- }
-}
-
-} // namespace MediaPlayback
-
namespace NetworkCommissioning {
void DispatchServerCommand(app::Command * command, CommandId commandId, EndpointId endpointId, TLV::TLVReader & dataTlv)
case ZCL_COLOR_CONTROL_CLUSTER_ID:
clusters::ColorControl::DispatchServerCommand(apCommandObj, aCommandId, aEndPointId, aReader);
break;
- case ZCL_CONTENT_LAUNCH_CLUSTER_ID:
- clusters::ContentLaunch::DispatchServerCommand(apCommandObj, aCommandId, aEndPointId, aReader);
- break;
case ZCL_DOOR_LOCK_CLUSTER_ID:
clusters::DoorLock::DispatchServerCommand(apCommandObj, aCommandId, aEndPointId, aReader);
break;
case ZCL_LOW_POWER_CLUSTER_ID:
clusters::LowPower::DispatchServerCommand(apCommandObj, aCommandId, aEndPointId, aReader);
break;
- case ZCL_MEDIA_PLAYBACK_CLUSTER_ID:
- clusters::MediaPlayback::DispatchServerCommand(apCommandObj, aCommandId, aEndPointId, aReader);
- break;
case ZCL_NETWORK_COMMISSIONING_CLUSTER_ID:
clusters::NetworkCommissioning::DispatchServerCommand(apCommandObj, aCommandId, aEndPointId, aReader);
break;
// Server attributes
#define ZCL_MAX_DURATION_ATTRIBUTE_ID (0x0000)
+// Attribute ids for cluster: Media Playback
+
+// Client attributes
+
+// Server attributes
+#define ZCL_CURRENT_STATE_ATTRIBUTE_ID (0x0000)
+
// Attribute ids for cluster: Low Power
// Client attributes
// Server attributes
+// Attribute ids for cluster: Content Launch
+
+// Client attributes
+
+// Server attributes
+
// Attribute ids for cluster: Application Basic
// Client attributes
// Server attributes
-// Attribute ids for cluster: Media Playback
-
-// Client attributes
-
-// Server attributes
-#define ZCL_CURRENT_STATE_ATTRIBUTE_ID (0x0000)
-
-// Attribute ids for cluster: Content Launch
-
-// Client attributes
-
-// Server attributes
-
// Attribute ids for cluster: Group Key Management
// Client attributes
EmberAfStatus emberAfBasicClusterServerCommandParse(EmberAfClusterCommand * cmd);
EmberAfStatus emberAfColorControlClusterClientCommandParse(EmberAfClusterCommand * cmd);
EmberAfStatus emberAfColorControlClusterServerCommandParse(EmberAfClusterCommand * cmd);
-EmberAfStatus emberAfContentLaunchClusterServerCommandParse(EmberAfClusterCommand * cmd);
EmberAfStatus emberAfDoorLockClusterClientCommandParse(EmberAfClusterCommand * cmd);
EmberAfStatus emberAfDoorLockClusterServerCommandParse(EmberAfClusterCommand * cmd);
EmberAfStatus emberAfGroupsClusterServerCommandParse(EmberAfClusterCommand * cmd);
EmberAfStatus emberAfIdentifyClusterServerCommandParse(EmberAfClusterCommand * cmd);
EmberAfStatus emberAfLevelControlClusterServerCommandParse(EmberAfClusterCommand * cmd);
EmberAfStatus emberAfLowPowerClusterServerCommandParse(EmberAfClusterCommand * cmd);
-EmberAfStatus emberAfMediaPlaybackClusterServerCommandParse(EmberAfClusterCommand * cmd);
EmberAfStatus emberAfNetworkCommissioningClusterServerCommandParse(EmberAfClusterCommand * cmd);
EmberAfStatus emberAfOnOffClusterServerCommandParse(EmberAfClusterCommand * cmd);
EmberAfStatus emberAfScenesClusterServerCommandParse(EmberAfClusterCommand * cmd);
case ZCL_COLOR_CONTROL_CLUSTER_ID:
result = emberAfColorControlClusterServerCommandParse(cmd);
break;
- case ZCL_CONTENT_LAUNCH_CLUSTER_ID:
- result = emberAfContentLaunchClusterServerCommandParse(cmd);
- break;
case ZCL_DOOR_LOCK_CLUSTER_ID:
result = emberAfDoorLockClusterServerCommandParse(cmd);
break;
case ZCL_LOW_POWER_CLUSTER_ID:
result = emberAfLowPowerClusterServerCommandParse(cmd);
break;
- case ZCL_MEDIA_PLAYBACK_CLUSTER_ID:
- result = emberAfMediaPlaybackClusterServerCommandParse(cmd);
- break;
case ZCL_NETWORK_COMMISSIONING_CLUSTER_ID:
result = emberAfNetworkCommissioningClusterServerCommandParse(cmd);
break;
}
return status(wasHandled, true, cmd->mfgSpecific);
}
-EmberAfStatus emberAfContentLaunchClusterServerCommandParse(EmberAfClusterCommand * cmd)
-{
- bool wasHandled = false;
-
- if (!cmd->mfgSpecific)
- {
- switch (cmd->commandId)
- {
- case ZCL_LAUNCH_CONTENT_COMMAND_ID: {
- wasHandled = emberAfContentLaunchClusterLaunchContentCallback();
- break;
- }
- case ZCL_LAUNCH_URL_COMMAND_ID: {
- wasHandled = emberAfContentLaunchClusterLaunchURLCallback();
- break;
- }
- default: {
- // Unrecognized command ID, error status will apply.
- break;
- }
- }
- }
- return status(wasHandled, true, cmd->mfgSpecific);
-}
EmberAfStatus emberAfDoorLockClusterClientCommandParse(EmberAfClusterCommand * cmd)
{
bool wasHandled = false;
}
return status(wasHandled, true, cmd->mfgSpecific);
}
-EmberAfStatus emberAfMediaPlaybackClusterServerCommandParse(EmberAfClusterCommand * cmd)
-{
- bool wasHandled = false;
-
- if (!cmd->mfgSpecific)
- {
- switch (cmd->commandId)
- {
- case ZCL_FAST_FORWARD_REQUEST_COMMAND_ID: {
- wasHandled = emberAfMediaPlaybackClusterFastForwardRequestCallback();
- break;
- }
- case ZCL_NEXT_REQUEST_COMMAND_ID: {
- wasHandled = emberAfMediaPlaybackClusterNextRequestCallback();
- break;
- }
- case ZCL_PAUSE_REQUEST_COMMAND_ID: {
- wasHandled = emberAfMediaPlaybackClusterPauseRequestCallback();
- break;
- }
- case ZCL_PLAY_REQUEST_COMMAND_ID: {
- wasHandled = emberAfMediaPlaybackClusterPlayRequestCallback();
- break;
- }
- case ZCL_PREVIOUS_REQUEST_COMMAND_ID: {
- wasHandled = emberAfMediaPlaybackClusterPreviousRequestCallback();
- break;
- }
- case ZCL_REWIND_REQUEST_COMMAND_ID: {
- wasHandled = emberAfMediaPlaybackClusterRewindRequestCallback();
- break;
- }
- case ZCL_SKIP_BACKWARD_REQUEST_COMMAND_ID: {
- wasHandled = emberAfMediaPlaybackClusterSkipBackwardRequestCallback();
- break;
- }
- case ZCL_SKIP_FORWARD_REQUEST_COMMAND_ID: {
- wasHandled = emberAfMediaPlaybackClusterSkipForwardRequestCallback();
- break;
- }
- case ZCL_START_OVER_REQUEST_COMMAND_ID: {
- wasHandled = emberAfMediaPlaybackClusterStartOverRequestCallback();
- break;
- }
- case ZCL_STOP_REQUEST_COMMAND_ID: {
- wasHandled = emberAfMediaPlaybackClusterStopRequestCallback();
- break;
- }
- default: {
- // Unrecognized command ID, error status will apply.
- break;
- }
- }
- }
- return status(wasHandled, true, cmd->mfgSpecific);
-}
EmberAfStatus emberAfNetworkCommissioningClusterServerCommandParse(EmberAfClusterCommand * cmd)
{
bool wasHandled = false;
case ZCL_COLOR_CONTROL_CLUSTER_ID:
emberAfColorControlClusterInitCallback(endpoint);
break;
- case ZCL_CONTENT_LAUNCH_CLUSTER_ID:
- emberAfContentLaunchClusterInitCallback(endpoint);
- break;
case ZCL_DOOR_LOCK_CLUSTER_ID:
emberAfDoorLockClusterInitCallback(endpoint);
break;
case ZCL_LOW_POWER_CLUSTER_ID:
emberAfLowPowerClusterInitCallback(endpoint);
break;
- case ZCL_MEDIA_PLAYBACK_CLUSTER_ID:
- emberAfMediaPlaybackClusterInitCallback(endpoint);
- break;
case ZCL_NETWORK_COMMISSIONING_CLUSTER_ID:
emberAfNetworkCommissioningClusterInitCallback(endpoint);
break;
// To prevent warning
(void) endpoint;
}
-void __attribute__((weak)) emberAfContentLaunchClusterInitCallback(EndpointId endpoint)
-{
- // To prevent warning
- (void) endpoint;
-}
void __attribute__((weak)) emberAfDoorLockClusterInitCallback(EndpointId endpoint)
{
// To prevent warning
// To prevent warning
(void) endpoint;
}
-void __attribute__((weak)) emberAfMediaPlaybackClusterInitCallback(EndpointId endpoint)
-{
- // To prevent warning
- (void) endpoint;
-}
void __attribute__((weak)) emberAfNetworkCommissioningClusterInitCallback(EndpointId endpoint)
{
// To prevent warning
*/
void emberAfColorControlClusterInitCallback(chip::EndpointId endpoint);
-/** @brief Content Launch Cluster Init
- *
- * Cluster Init
- *
- * @param endpoint Endpoint that is being initialized
- */
-void emberAfContentLaunchClusterInitCallback(chip::EndpointId endpoint);
-
/** @brief Door Lock Cluster Init
*
* Cluster Init
*/
void emberAfLowPowerClusterInitCallback(chip::EndpointId endpoint);
-/** @brief Media Playback Cluster Init
- *
- * Cluster Init
- *
- * @param endpoint Endpoint that is being initialized
- */
-void emberAfMediaPlaybackClusterInitCallback(chip::EndpointId endpoint);
-
/** @brief Network Commissioning Cluster Init
*
* Cluster Init
void emberAfColorControlClusterServerTickCallback(chip::EndpointId endpoint);
//
-// Content Launch Cluster server
-//
-
-/** @brief Content Launch Cluster Server Init
- *
- * Server Init
- *
- * @param endpoint Endpoint that is being initialized
- */
-void emberAfContentLaunchClusterServerInitCallback(chip::EndpointId endpoint);
-
-/** @brief Content Launch Cluster Server Attribute Changed
- *
- * Server Attribute Changed
- *
- * @param endpoint Endpoint that is being initialized
- * @param attributeId Attribute that changed
- */
-void emberAfContentLaunchClusterServerAttributeChangedCallback(chip::EndpointId endpoint, chip::AttributeId attributeId);
-
-/** @brief Content Launch Cluster Server Manufacturer Specific Attribute Changed
- *
- * Server Manufacturer Specific Attribute Changed
- *
- * @param endpoint Endpoint that is being initialized
- * @param attributeId Attribute that changed
- * @param manufacturerCode Manufacturer Code of the attribute that changed
- */
-void emberAfContentLaunchClusterServerManufacturerSpecificAttributeChangedCallback(chip::EndpointId endpoint,
- chip::AttributeId attributeId,
- uint16_t manufacturerCode);
-
-/** @brief Content Launch Cluster Server Message Sent
- *
- * Server Message Sent
- *
- * @param type The type of message sent
- * @param indexOrDestination The destination or address to which the message was sent
- * @param apsFrame The APS frame for the message
- * @param msgLen The length of the message
- * @param message The message that was sent
- * @param status The status of the sent message
- */
-void emberAfContentLaunchClusterServerMessageSentCallback(EmberOutgoingMessageType type, uint64_t indexOrDestination,
- EmberApsFrame * apsFrame, uint16_t msgLen, uint8_t * message,
- EmberStatus status);
-
-/** @brief Content Launch Cluster Server Pre Attribute Changed
- *
- * server Pre Attribute Changed
- *
- * @param endpoint Endpoint that is being initialized
- * @param attributeId Attribute to be changed
- * @param attributeType Attribute type
- * @param size Attribute size
- * @param value Attribute value
- */
-EmberAfStatus emberAfContentLaunchClusterServerPreAttributeChangedCallback(chip::EndpointId endpoint, chip::AttributeId attributeId,
- EmberAfAttributeType attributeType, uint8_t size,
- uint8_t * value);
-
-/** @brief Content Launch Cluster Server Tick
- *
- * server Tick
- *
- * @param endpoint Endpoint that is being served
- */
-void emberAfContentLaunchClusterServerTickCallback(chip::EndpointId endpoint);
-
-//
// Door Lock Cluster client
//
void emberAfLowPowerClusterServerTickCallback(chip::EndpointId endpoint);
//
-// Media Playback Cluster server
-//
-
-/** @brief Media Playback Cluster Server Init
- *
- * Server Init
- *
- * @param endpoint Endpoint that is being initialized
- */
-void emberAfMediaPlaybackClusterServerInitCallback(chip::EndpointId endpoint);
-
-/** @brief Media Playback Cluster Server Attribute Changed
- *
- * Server Attribute Changed
- *
- * @param endpoint Endpoint that is being initialized
- * @param attributeId Attribute that changed
- */
-void emberAfMediaPlaybackClusterServerAttributeChangedCallback(chip::EndpointId endpoint, chip::AttributeId attributeId);
-
-/** @brief Media Playback Cluster Server Manufacturer Specific Attribute Changed
- *
- * Server Manufacturer Specific Attribute Changed
- *
- * @param endpoint Endpoint that is being initialized
- * @param attributeId Attribute that changed
- * @param manufacturerCode Manufacturer Code of the attribute that changed
- */
-void emberAfMediaPlaybackClusterServerManufacturerSpecificAttributeChangedCallback(chip::EndpointId endpoint,
- chip::AttributeId attributeId,
- uint16_t manufacturerCode);
-
-/** @brief Media Playback Cluster Server Message Sent
- *
- * Server Message Sent
- *
- * @param type The type of message sent
- * @param indexOrDestination The destination or address to which the message was sent
- * @param apsFrame The APS frame for the message
- * @param msgLen The length of the message
- * @param message The message that was sent
- * @param status The status of the sent message
- */
-void emberAfMediaPlaybackClusterServerMessageSentCallback(EmberOutgoingMessageType type, uint64_t indexOrDestination,
- EmberApsFrame * apsFrame, uint16_t msgLen, uint8_t * message,
- EmberStatus status);
-
-/** @brief Media Playback Cluster Server Pre Attribute Changed
- *
- * server Pre Attribute Changed
- *
- * @param endpoint Endpoint that is being initialized
- * @param attributeId Attribute to be changed
- * @param attributeType Attribute type
- * @param size Attribute size
- * @param value Attribute value
- */
-EmberAfStatus emberAfMediaPlaybackClusterServerPreAttributeChangedCallback(chip::EndpointId endpoint, chip::AttributeId attributeId,
- EmberAfAttributeType attributeType, uint8_t size,
- uint8_t * value);
-
-/** @brief Media Playback Cluster Server Tick
- *
- * server Tick
- *
- * @param endpoint Endpoint that is being served
- */
-void emberAfMediaPlaybackClusterServerTickCallback(chip::EndpointId endpoint);
-
-//
// Network Commissioning Cluster server
//
bool emberAfColorControlClusterStopMoveStepCallback(uint8_t optionsMask, uint8_t optionsOverride);
/**
- * @brief Content Launch Cluster LaunchContent Command callback
- */
-
-bool emberAfContentLaunchClusterLaunchContentCallback();
-
-/**
- * @brief Content Launch Cluster LaunchURL Command callback
- */
-
-bool emberAfContentLaunchClusterLaunchURLCallback();
-
-/**
* @brief Door Lock Cluster LockDoorResponse Command callback
* @param status
*/
bool emberAfLowPowerClusterSleepCallback();
/**
- * @brief Media Playback Cluster FastForwardRequest Command callback
- */
-
-bool emberAfMediaPlaybackClusterFastForwardRequestCallback();
-
-/**
- * @brief Media Playback Cluster NextRequest Command callback
- */
-
-bool emberAfMediaPlaybackClusterNextRequestCallback();
-
-/**
- * @brief Media Playback Cluster PauseRequest Command callback
- */
-
-bool emberAfMediaPlaybackClusterPauseRequestCallback();
-
-/**
- * @brief Media Playback Cluster PlayRequest Command callback
- */
-
-bool emberAfMediaPlaybackClusterPlayRequestCallback();
-
-/**
- * @brief Media Playback Cluster PreviousRequest Command callback
- */
-
-bool emberAfMediaPlaybackClusterPreviousRequestCallback();
-
-/**
- * @brief Media Playback Cluster RewindRequest Command callback
- */
-
-bool emberAfMediaPlaybackClusterRewindRequestCallback();
-
-/**
- * @brief Media Playback Cluster SkipBackwardRequest Command callback
- */
-
-bool emberAfMediaPlaybackClusterSkipBackwardRequestCallback();
-
-/**
- * @brief Media Playback Cluster SkipForwardRequest Command callback
- */
-
-bool emberAfMediaPlaybackClusterSkipForwardRequestCallback();
-
-/**
- * @brief Media Playback Cluster StartOverRequest Command callback
- */
-
-bool emberAfMediaPlaybackClusterStartOverRequestCallback();
-
-/**
- * @brief Media Playback Cluster StopRequest Command callback
- */
-
-bool emberAfMediaPlaybackClusterStopRequestCallback();
-
-/**
* @brief Network Commissioning Cluster AddThreadNetwork Command callback
* @param operationalDataset
* @param breadcrumb
\
ZCL_SQUAWK_COMMAND_ID, "u", squawkInfo);
+/** @brief Command description for PlayRequest
+ *
+ * Command: PlayRequest
+ */
+#define emberAfFillCommandMedia \
+ PlaybackClusterPlayRequest() emberAfFillExternalBuffer(mask, \
+ \
+ ZCL_PLAY_REQUEST_COMMAND_ID, "", );
+
+/** @brief Command description for PauseRequest
+ *
+ * Command: PauseRequest
+ */
+#define emberAfFillCommandMedia \
+ PlaybackClusterPauseRequest() emberAfFillExternalBuffer(mask, \
+ \
+ ZCL_PAUSE_REQUEST_COMMAND_ID, "", );
+
+/** @brief Command description for StopRequest
+ *
+ * Command: StopRequest
+ */
+#define emberAfFillCommandMedia \
+ PlaybackClusterStopRequest() emberAfFillExternalBuffer(mask, \
+ \
+ ZCL_STOP_REQUEST_COMMAND_ID, "", );
+
+/** @brief Command description for StartOverRequest
+ *
+ * Command: StartOverRequest
+ */
+#define emberAfFillCommandMedia \
+ PlaybackClusterStartOverRequest() emberAfFillExternalBuffer(mask, \
+ \
+ ZCL_START_OVER_REQUEST_COMMAND_ID, "", );
+
+/** @brief Command description for PreviousRequest
+ *
+ * Command: PreviousRequest
+ */
+#define emberAfFillCommandMedia \
+ PlaybackClusterPreviousRequest() emberAfFillExternalBuffer(mask, \
+ \
+ ZCL_PREVIOUS_REQUEST_COMMAND_ID, "", );
+
+/** @brief Command description for NextRequest
+ *
+ * Command: NextRequest
+ */
+#define emberAfFillCommandMedia \
+ PlaybackClusterNextRequest() emberAfFillExternalBuffer(mask, \
+ \
+ ZCL_NEXT_REQUEST_COMMAND_ID, "", );
+
+/** @brief Command description for RewindRequest
+ *
+ * Command: RewindRequest
+ */
+#define emberAfFillCommandMedia \
+ PlaybackClusterRewindRequest() emberAfFillExternalBuffer(mask, \
+ \
+ ZCL_REWIND_REQUEST_COMMAND_ID, "", );
+
+/** @brief Command description for FastForwardRequest
+ *
+ * Command: FastForwardRequest
+ */
+#define emberAfFillCommandMedia \
+ PlaybackClusterFastForwardRequest() emberAfFillExternalBuffer(mask, \
+ \
+ ZCL_FAST_FORWARD_REQUEST_COMMAND_ID, "", );
+
+/** @brief Command description for SkipForwardRequest
+ *
+ * Command: SkipForwardRequest
+ */
+#define emberAfFillCommandMedia \
+ PlaybackClusterSkipForwardRequest() emberAfFillExternalBuffer(mask, \
+ \
+ ZCL_SKIP_FORWARD_REQUEST_COMMAND_ID, "", );
+
+/** @brief Command description for SkipBackwardRequest
+ *
+ * Command: SkipBackwardRequest
+ */
+#define emberAfFillCommandMedia \
+ PlaybackClusterSkipBackwardRequest() emberAfFillExternalBuffer(mask, \
+ \
+ ZCL_SKIP_BACKWARD_REQUEST_COMMAND_ID, "", );
+
/** @brief Command description for Sleep
*
* Command: Sleep
\
ZCL_SLEEP_COMMAND_ID, "", );
+/** @brief Command description for LaunchContent
+ *
+ * Command: LaunchContent
+ * @param contentLaunchStatus ContentLaunchStatus
+ */
+#define emberAfFillCommandContent \
+ LaunchClusterLaunchContent(contentLaunchStatus) \
+ emberAfFillExternalBuffer(mask, \
+ \
+ ZCL_LAUNCH_CONTENT_COMMAND_ID, "u", contentLaunchStatus);
+
+/** @brief Command description for LaunchURL
+ *
+ * Command: LaunchURL
+ * @param contentLaunchStatus ContentLaunchStatus
+ */
+#define emberAfFillCommandContent \
+ LaunchClusterLaunchURL(contentLaunchStatus) emberAfFillExternalBuffer(mask, \
+ \
+ ZCL_LAUNCH_URL_COMMAND_ID, "u", contentLaunchStatus);
+
/** @brief Command description for MatchProtocolAddress
*
* Command: MatchProtocolAddress
\
ZCL_UNBIND_COMMAND_ID, "uuuu", nodeId, groupId, endpointId, clusterId);
-/** @brief Command description for PlayRequest
- *
- * Command: PlayRequest
- */
-#define emberAfFillCommandMedia \
- PlaybackClusterPlayRequest() emberAfFillExternalBuffer(mask, \
- \
- ZCL_PLAY_REQUEST_COMMAND_ID, "", );
-
-/** @brief Command description for PauseRequest
- *
- * Command: PauseRequest
- */
-#define emberAfFillCommandMedia \
- PlaybackClusterPauseRequest() emberAfFillExternalBuffer(mask, \
- \
- ZCL_PAUSE_REQUEST_COMMAND_ID, "", );
-
-/** @brief Command description for StopRequest
- *
- * Command: StopRequest
- */
-#define emberAfFillCommandMedia \
- PlaybackClusterStopRequest() emberAfFillExternalBuffer(mask, \
- \
- ZCL_STOP_REQUEST_COMMAND_ID, "", );
-
-/** @brief Command description for StartOverRequest
- *
- * Command: StartOverRequest
- */
-#define emberAfFillCommandMedia \
- PlaybackClusterStartOverRequest() emberAfFillExternalBuffer(mask, \
- \
- ZCL_START_OVER_REQUEST_COMMAND_ID, "", );
-
-/** @brief Command description for PreviousRequest
- *
- * Command: PreviousRequest
- */
-#define emberAfFillCommandMedia \
- PlaybackClusterPreviousRequest() emberAfFillExternalBuffer(mask, \
- \
- ZCL_PREVIOUS_REQUEST_COMMAND_ID, "", );
-
-/** @brief Command description for NextRequest
- *
- * Command: NextRequest
- */
-#define emberAfFillCommandMedia \
- PlaybackClusterNextRequest() emberAfFillExternalBuffer(mask, \
- \
- ZCL_NEXT_REQUEST_COMMAND_ID, "", );
-
-/** @brief Command description for RewindRequest
- *
- * Command: RewindRequest
- */
-#define emberAfFillCommandMedia \
- PlaybackClusterRewindRequest() emberAfFillExternalBuffer(mask, \
- \
- ZCL_REWIND_REQUEST_COMMAND_ID, "", );
-
-/** @brief Command description for FastForwardRequest
- *
- * Command: FastForwardRequest
- */
-#define emberAfFillCommandMedia \
- PlaybackClusterFastForwardRequest() emberAfFillExternalBuffer(mask, \
- \
- ZCL_FAST_FORWARD_REQUEST_COMMAND_ID, "", );
-
-/** @brief Command description for SkipForwardRequest
- *
- * Command: SkipForwardRequest
- */
-#define emberAfFillCommandMedia \
- PlaybackClusterSkipForwardRequest() emberAfFillExternalBuffer(mask, \
- \
- ZCL_SKIP_FORWARD_REQUEST_COMMAND_ID, "", );
-
-/** @brief Command description for SkipBackwardRequest
- *
- * Command: SkipBackwardRequest
- */
-#define emberAfFillCommandMedia \
- PlaybackClusterSkipBackwardRequest() emberAfFillExternalBuffer(mask, \
- \
- ZCL_SKIP_BACKWARD_REQUEST_COMMAND_ID, "", );
-
-/** @brief Command description for LaunchContent
- *
- * Command: LaunchContent
- * @param contentLaunchStatus ContentLaunchStatus
- */
-#define emberAfFillCommandContent \
- LaunchClusterLaunchContent(contentLaunchStatus) \
- emberAfFillExternalBuffer(mask, \
- \
- ZCL_LAUNCH_CONTENT_COMMAND_ID, "u", contentLaunchStatus);
-
-/** @brief Command description for LaunchURL
- *
- * Command: LaunchURL
- * @param contentLaunchStatus ContentLaunchStatus
- */
-#define emberAfFillCommandContent \
- LaunchClusterLaunchURL(contentLaunchStatus) emberAfFillExternalBuffer(mask, \
- \
- ZCL_LAUNCH_URL_COMMAND_ID, "u", contentLaunchStatus);
-
/** @brief Command description for CommandOne
*
* Command: CommandOne
// Definitions for cluster: IAS WD
#define ZCL_IAS_WD_CLUSTER_ID (0x0502)
+// Definitions for cluster: Media Playback
+#define ZCL_MEDIA_PLAYBACK_CLUSTER_ID (0x0506)
+
// Definitions for cluster: Low Power
#define ZCL_LOW_POWER_CLUSTER_ID (0x0508)
+// Definitions for cluster: Content Launch
+#define ZCL_CONTENT_LAUNCH_CLUSTER_ID (0x050A)
+
// Definitions for cluster: Application Basic
#define ZCL_APPLICATION_BASIC_CLUSTER_ID (0x050D)
// Definitions for cluster: Binding
#define ZCL_BINDING_CLUSTER_ID (0xF000)
-// Definitions for cluster: Media Playback
-#define ZCL_MEDIA_PLAYBACK_CLUSTER_ID (0xF001)
-
-// Definitions for cluster: Content Launch
-#define ZCL_CONTENT_LAUNCH_CLUSTER_ID (0xF002)
-
// Definitions for cluster: Group Key Management
#define ZCL_GROUP_KEY_MANAGEMENT_CLUSTER_ID (0xF004)
#define ZCL_START_WARNING_COMMAND_ID (0x00)
#define ZCL_SQUAWK_COMMAND_ID (0x01)
+// Commands for cluster: Media Playback
+#define ZCL_PLAY_REQUEST_COMMAND_ID (0x00)
+#define ZCL_PLAYBACK_COMMAND_ID (0x00)
+#define ZCL_PAUSE_REQUEST_COMMAND_ID (0x01)
+#define ZCL_STOP_REQUEST_COMMAND_ID (0x02)
+#define ZCL_START_OVER_REQUEST_COMMAND_ID (0x03)
+#define ZCL_PREVIOUS_REQUEST_COMMAND_ID (0x04)
+#define ZCL_NEXT_REQUEST_COMMAND_ID (0x05)
+#define ZCL_REWIND_REQUEST_COMMAND_ID (0x06)
+#define ZCL_FAST_FORWARD_REQUEST_COMMAND_ID (0x07)
+#define ZCL_SKIP_FORWARD_REQUEST_COMMAND_ID (0x08)
+#define ZCL_SKIP_BACKWARD_REQUEST_COMMAND_ID (0x09)
+
// Commands for cluster: Low Power
#define ZCL_SLEEP_COMMAND_ID (0x00)
+// Commands for cluster: Content Launch
+#define ZCL_LAUNCH_CONTENT_COMMAND_ID (0x00)
+#define ZCL_LAUNCH_CONTENT_RESPONSE_COMMAND_ID (0x00)
+#define ZCL_LAUNCH_URL_COMMAND_ID (0x01)
+#define ZCL_LAUNCH_URL_RESPONSE_COMMAND_ID (0x01)
+
// Commands for cluster: Generic Tunnel
#define ZCL_MATCH_PROTOCOL_ADDRESS_COMMAND_ID (0x00)
#define ZCL_MATCH_PROTOCOL_ADDRESS_RESPONSE_COMMAND_ID (0x00)
#define ZCL_BIND_COMMAND_ID (0x00)
#define ZCL_UNBIND_COMMAND_ID (0x01)
-// Commands for cluster: Media Playback
-#define ZCL_PLAY_REQUEST_COMMAND_ID (0x00)
-#define ZCL_PLAYBACK_COMMAND_ID (0x00)
-#define ZCL_PAUSE_REQUEST_COMMAND_ID (0x01)
-#define ZCL_STOP_REQUEST_COMMAND_ID (0x02)
-#define ZCL_START_OVER_REQUEST_COMMAND_ID (0x03)
-#define ZCL_PREVIOUS_REQUEST_COMMAND_ID (0x04)
-#define ZCL_NEXT_REQUEST_COMMAND_ID (0x05)
-#define ZCL_REWIND_REQUEST_COMMAND_ID (0x06)
-#define ZCL_FAST_FORWARD_REQUEST_COMMAND_ID (0x07)
-#define ZCL_SKIP_FORWARD_REQUEST_COMMAND_ID (0x08)
-#define ZCL_SKIP_BACKWARD_REQUEST_COMMAND_ID (0x09)
-
-// Commands for cluster: Content Launch
-#define ZCL_LAUNCH_CONTENT_COMMAND_ID (0x00)
-#define ZCL_LAUNCH_CONTENT_RESPONSE_COMMAND_ID (0x00)
-#define ZCL_LAUNCH_URL_COMMAND_ID (0x01)
-#define ZCL_LAUNCH_URL_RESPONSE_COMMAND_ID (0x01)
-
// Commands for cluster: Sample Mfg Specific Cluster
#define ZCL_COMMAND_ONE_COMMAND_ID (0x00)
#define ZAP_ATTRIBUTE_MASK(mask) ATTRIBUTE_MASK_##mask
// This is an array of EmberAfAttributeMetadata structures.
-#define GENERATED_ATTRIBUTE_COUNT 112
+#define GENERATED_ATTRIBUTE_COUNT 109
#define GENERATED_ATTRIBUTES \
{ \
{ 0xFFFD, ZAP_TYPE(INT16U), 2, 0, ZAP_SIMPLE_DEFAULT(2) }, /* Identify (server): cluster revision */ \
{ 0x0003, ZAP_TYPE(INT16U), 2, 0, ZAP_EMPTY_DEFAULT() }, /* Application Basic (server): product id */ \
{ 0xFFFD, ZAP_TYPE(INT16U), 2, 0, ZAP_SIMPLE_DEFAULT(0x0001) }, /* Application Basic (server): cluster revision */ \
{ 0x0005, ZAP_TYPE(OCTET_STRING), 32, 0, \
- ZAP_LONG_DEFAULTS_INDEX(570) }, /* Application Basic (server): application id */ \
- { 0x0006, ZAP_TYPE(INT16U), 2, 0, ZAP_EMPTY_DEFAULT() }, /* Application Basic (server): catalog vendor id */ \
- { 0x0007, ZAP_TYPE(ENUM8), 1, 0, ZAP_SIMPLE_DEFAULT(0x01) }, /* Application Basic (server): application satus */ \
- { 0x0000, ZAP_TYPE(INT16U), 2, 0, ZAP_EMPTY_DEFAULT() }, /* Media Playback (server): current state */ \
- { 0xFFFD, ZAP_TYPE(INT16U), 2, 0, ZAP_SIMPLE_DEFAULT(0x0001) }, /* Media Playback (server): cluster revision */ \
- { 0xFFFD, ZAP_TYPE(INT16U), 2, 0, ZAP_SIMPLE_DEFAULT(0x0001) }, /* Content Launch (server): cluster revision */ \
+ ZAP_LONG_DEFAULTS_INDEX(570) }, /* Application Basic (server): application id */ \
+ { 0x0006, ZAP_TYPE(INT16U), 2, 0, ZAP_EMPTY_DEFAULT() }, /* Application Basic (server): catalog vendor id */ \
+ { 0x0007, ZAP_TYPE(ENUM8), 1, 0, ZAP_SIMPLE_DEFAULT(0x01) }, /* Application Basic (server): application satus */ \
}
// This is an array of EmberAfCluster structures.
};
#define ZAP_CLUSTER_MASK(mask) CLUSTER_MASK_##mask
-#define GENERATED_CLUSTER_COUNT 19
+#define GENERATED_CLUSTER_COUNT 17
#define GENERATED_CLUSTERS \
{ \
{ 0x0003, \
{ \
0x050D, ZAP_ATTRIBUTE_INDEX(101), 8, 105, ZAP_CLUSTER_MASK(SERVER), NULL \
}, /* Endpoint: 1, Cluster: Application Basic (server) */ \
- { \
- 0xF001, ZAP_ATTRIBUTE_INDEX(109), 2, 4, ZAP_CLUSTER_MASK(SERVER), NULL \
- }, /* Endpoint: 1, Cluster: Media Playback (server) */ \
- { \
- 0xF002, ZAP_ATTRIBUTE_INDEX(111), 1, 2, ZAP_CLUSTER_MASK(SERVER), NULL \
- }, /* Endpoint: 1, Cluster: Content Launch (server) */ \
}
#define ZAP_CLUSTER_INDEX(index) ((EmberAfCluster *) (&generatedClusters[index]))
// This is an array of EmberAfEndpointType structures.
#define GENERATED_ENDPOINT_TYPES \
{ \
- { ZAP_CLUSTER_INDEX(0), 19, 768 }, \
+ { ZAP_CLUSTER_INDEX(0), 17, 762 }, \
}
// Largest attribute size is needed for various buffers
#define ATTRIBUTE_SINGLETONS_SIZE (254)
// Total size of attribute storage
-#define ATTRIBUTE_MAX_SIZE (768)
+#define ATTRIBUTE_MAX_SIZE (762)
// Number of fixed endpoints
#define FIXED_ENDPOINT_COUNT (1)
// Array of EmberAfCommandMetadata structs.
#define ZAP_COMMAND_MASK(mask) COMMAND_MASK_##mask
-#define EMBER_AF_GENERATED_COMMAND_COUNT (158)
+#define EMBER_AF_GENERATED_COMMAND_COUNT (143)
#define GENERATED_COMMANDS \
{ \
{ 0x0003, 0x00, ZAP_COMMAND_MASK(INCOMING_SERVER) }, /* Identify (server): Identify */ \
{ 0x0500, 0x00, ZAP_COMMAND_MASK(INCOMING_CLIENT) }, /* IAS Zone (server): ZoneStatusChangeNotification */ \
{ 0x0500, 0x01, ZAP_COMMAND_MASK(INCOMING_CLIENT) }, /* IAS Zone (server): ZoneEnrollRequest */ \
{ 0x0508, 0x00, ZAP_COMMAND_MASK(INCOMING_SERVER) }, /* Low Power (server): Sleep */ \
- { 0xF001, 0x00, ZAP_COMMAND_MASK(INCOMING_SERVER) }, /* Media Playback (server): PlayRequest */ \
- { 0xF001, 0x00, ZAP_COMMAND_MASK(INCOMING_CLIENT) }, /* Media Playback (server): Playback */ \
- { 0xF001, 0x01, ZAP_COMMAND_MASK(INCOMING_SERVER) }, /* Media Playback (server): PauseRequest */ \
- { 0xF001, 0x02, ZAP_COMMAND_MASK(INCOMING_SERVER) }, /* Media Playback (server): StopRequest */ \
- { 0xF001, 0x03, ZAP_COMMAND_MASK(INCOMING_SERVER) }, /* Media Playback (server): StartOverRequest */ \
- { 0xF001, 0x04, ZAP_COMMAND_MASK(INCOMING_SERVER) }, /* Media Playback (server): PreviousRequest */ \
- { 0xF001, 0x05, ZAP_COMMAND_MASK(INCOMING_SERVER) }, /* Media Playback (server): NextRequest */ \
- { 0xF001, 0x06, ZAP_COMMAND_MASK(INCOMING_SERVER) }, /* Media Playback (server): RewindRequest */ \
- { 0xF001, 0x07, ZAP_COMMAND_MASK(INCOMING_SERVER) }, /* Media Playback (server): FastForwardRequest */ \
- { 0xF001, 0x08, ZAP_COMMAND_MASK(INCOMING_SERVER) }, /* Media Playback (server): SkipForwardRequest */ \
- { 0xF001, 0x09, ZAP_COMMAND_MASK(INCOMING_SERVER) }, /* Media Playback (server): SkipBackwardRequest */ \
- { 0xF002, 0x00, ZAP_COMMAND_MASK(INCOMING_SERVER) }, /* Content Launch (server): LaunchContent */ \
- { 0xF002, 0x00, ZAP_COMMAND_MASK(INCOMING_CLIENT) }, /* Content Launch (server): LaunchContentResponse */ \
- { 0xF002, 0x01, ZAP_COMMAND_MASK(INCOMING_SERVER) }, /* Content Launch (server): LaunchURL */ \
- { 0xF002, 0x01, ZAP_COMMAND_MASK(INCOMING_CLIENT) }, /* Content Launch (server): LaunchURLResponse */ \
}
// Array of EmberAfManufacturerCodeEntry structures for commands.
#define EMBER_AF_BASIC_CLUSTER_SERVER_ENDPOINT_COUNT (1)
#define EMBER_AF_COLOR_CONTROL_CLUSTER_CLIENT_ENDPOINT_COUNT (1)
#define EMBER_AF_COLOR_CONTROL_CLUSTER_SERVER_ENDPOINT_COUNT (1)
-#define EMBER_AF_CONTENT_LAUNCH_CLUSTER_SERVER_ENDPOINT_COUNT (1)
#define EMBER_AF_DOOR_LOCK_CLUSTER_CLIENT_ENDPOINT_COUNT (1)
#define EMBER_AF_DOOR_LOCK_CLUSTER_SERVER_ENDPOINT_COUNT (1)
#define EMBER_AF_GROUPS_CLUSTER_SERVER_ENDPOINT_COUNT (1)
#define EMBER_AF_IDENTIFY_CLUSTER_SERVER_ENDPOINT_COUNT (1)
#define EMBER_AF_LEVEL_CONTROL_CLUSTER_SERVER_ENDPOINT_COUNT (1)
#define EMBER_AF_LOW_POWER_CLUSTER_SERVER_ENDPOINT_COUNT (1)
-#define EMBER_AF_MEDIA_PLAYBACK_CLUSTER_SERVER_ENDPOINT_COUNT (1)
#define EMBER_AF_NETWORK_COMMISSIONING_CLUSTER_SERVER_ENDPOINT_COUNT (1)
#define EMBER_AF_ON_OFF_CLUSTER_SERVER_ENDPOINT_COUNT (1)
#define EMBER_AF_SCENES_CLUSTER_SERVER_ENDPOINT_COUNT (1)
#define EMBER_AF_PLUGIN_COLOR_CONTROL_SERVER_TEMP
#define EMBER_AF_PLUGIN_COLOR_CONTROL_SERVER_HSV
-// Use this macro to check if the server side of the Content Launch cluster is included
-#define ZCL_USING_CONTENT_LAUNCH_CLUSTER_SERVER
-#define EMBER_AF_PLUGIN_CONTENT_LAUNCH_SERVER
-#define EMBER_AF_PLUGIN_CONTENT_LAUNCH
-
// Use this macro to check if the client side of the Door Lock cluster is included
#define ZCL_USING_DOOR_LOCK_CLUSTER_CLIENT
#define EMBER_AF_PLUGIN_DOOR_LOCK_CLIENT
#define EMBER_AF_PLUGIN_LOW_POWER_SERVER
#define EMBER_AF_PLUGIN_LOW_POWER
-// Use this macro to check if the server side of the Media Playback cluster is included
-#define ZCL_USING_MEDIA_PLAYBACK_CLUSTER_SERVER
-#define EMBER_AF_PLUGIN_MEDIA_PLAYBACK_SERVER
-#define EMBER_AF_PLUGIN_MEDIA_PLAYBACK
-
// Use this macro to check if the server side of the Network Commissioning cluster is included
#define ZCL_USING_NETWORK_COMMISSIONING_CLUSTER_SERVER
#define EMBER_AF_PLUGIN_NETWORK_COMMISSIONING_SERVER
#define CHIP_PRINTCLUSTER_IAS_WD_CLUSTER
#endif
+#if defined(ZCL_USING_MEDIA_PLAYBACK_CLUSTER_SERVER) || defined(ZCL_USING_MEDIA_PLAYBACK_CLUSTER_CLIENT)
+#define CHIP_PRINTCLUSTER_MEDIA_PLAYBACK_CLUSTER { ZCL_MEDIA_PLAYBACK_CLUSTER_ID, 1286, "Media Playback" },
+#else
+#define CHIP_PRINTCLUSTER_MEDIA_PLAYBACK_CLUSTER
+#endif
+
#if defined(ZCL_USING_LOW_POWER_CLUSTER_SERVER) || defined(ZCL_USING_LOW_POWER_CLUSTER_CLIENT)
#define CHIP_PRINTCLUSTER_LOW_POWER_CLUSTER { ZCL_LOW_POWER_CLUSTER_ID, 1288, "Low Power" },
#else
#define CHIP_PRINTCLUSTER_LOW_POWER_CLUSTER
#endif
+#if defined(ZCL_USING_CONTENT_LAUNCH_CLUSTER_SERVER) || defined(ZCL_USING_CONTENT_LAUNCH_CLUSTER_CLIENT)
+#define CHIP_PRINTCLUSTER_CONTENT_LAUNCH_CLUSTER { ZCL_CONTENT_LAUNCH_CLUSTER_ID, 1290, "Content Launch" },
+#else
+#define CHIP_PRINTCLUSTER_CONTENT_LAUNCH_CLUSTER
+#endif
+
#if defined(ZCL_USING_APPLICATION_BASIC_CLUSTER_SERVER) || defined(ZCL_USING_APPLICATION_BASIC_CLUSTER_CLIENT)
#define CHIP_PRINTCLUSTER_APPLICATION_BASIC_CLUSTER { ZCL_APPLICATION_BASIC_CLUSTER_ID, 1293, "Application Basic" },
#else
#define CHIP_PRINTCLUSTER_BINDING_CLUSTER
#endif
-#if defined(ZCL_USING_MEDIA_PLAYBACK_CLUSTER_SERVER) || defined(ZCL_USING_MEDIA_PLAYBACK_CLUSTER_CLIENT)
-#define CHIP_PRINTCLUSTER_MEDIA_PLAYBACK_CLUSTER { ZCL_MEDIA_PLAYBACK_CLUSTER_ID, 61441, "Media Playback" },
-#else
-#define CHIP_PRINTCLUSTER_MEDIA_PLAYBACK_CLUSTER
-#endif
-
-#if defined(ZCL_USING_CONTENT_LAUNCH_CLUSTER_SERVER) || defined(ZCL_USING_CONTENT_LAUNCH_CLUSTER_CLIENT)
-#define CHIP_PRINTCLUSTER_CONTENT_LAUNCH_CLUSTER { ZCL_CONTENT_LAUNCH_CLUSTER_ID, 61442, "Content Launch" },
-#else
-#define CHIP_PRINTCLUSTER_CONTENT_LAUNCH_CLUSTER
-#endif
-
#if defined(ZCL_USING_GROUP_KEY_MANAGEMENT_CLUSTER_SERVER) || defined(ZCL_USING_GROUP_KEY_MANAGEMENT_CLUSTER_CLIENT)
#define CHIP_PRINTCLUSTER_GROUP_KEY_MANAGEMENT_CLUSTER { ZCL_GROUP_KEY_MANAGEMENT_CLUSTER_ID, 61444, "Group Key Management" },
#else
CHIP_PRINTCLUSTER_IAS_ZONE_CLUSTER \
CHIP_PRINTCLUSTER_IAS_ACE_CLUSTER \
CHIP_PRINTCLUSTER_IAS_WD_CLUSTER \
+ CHIP_PRINTCLUSTER_MEDIA_PLAYBACK_CLUSTER \
CHIP_PRINTCLUSTER_LOW_POWER_CLUSTER \
+ CHIP_PRINTCLUSTER_CONTENT_LAUNCH_CLUSTER \
CHIP_PRINTCLUSTER_APPLICATION_BASIC_CLUSTER \
CHIP_PRINTCLUSTER_GENERIC_TUNNEL_CLUSTER \
CHIP_PRINTCLUSTER_BACNET_PROTOCOL_TUNNEL_CLUSTER \
CHIP_PRINTCLUSTER_DIAGNOSTICS_CLUSTER \
CHIP_PRINTCLUSTER_ZLL_COMMISSIONING_CLUSTER \
CHIP_PRINTCLUSTER_BINDING_CLUSTER \
- CHIP_PRINTCLUSTER_MEDIA_PLAYBACK_CLUSTER \
- CHIP_PRINTCLUSTER_CONTENT_LAUNCH_CLUSTER \
CHIP_PRINTCLUSTER_GROUP_KEY_MANAGEMENT_CLUSTER \
CHIP_PRINTCLUSTER_SAMPLE_MFG_SPECIFIC_CLUSTER \
CHIP_PRINTCLUSTER_SAMPLE_MFG_SPECIFIC_CLUSTER_2 \
virtualenv
# esp-idf
-pyelftools>=0.22
+setuptools>=21
click>=5.0
pyserial>=3.0
future>=0.15.2
-cryptography>=3.2
+cryptography>=2.1.4
pyparsing>=2.0.3,<2.4.0
pyelftools>=0.22
+gdbgui==0.13.2.0
+pygdbmi<=0.9.0.2
+reedsolo>=1.5.3,<=1.5.4
+bitstring>=3.1.6
+ecdsa>=0.16.0
# cirque tests
requests>=2.24.0
# pigweed
ipython
-appnope; sys_platform == 'darwin'
-appdirs; sys_platform == 'darwin'
+appnope
+appdirs
coloredlogs
watchdog
protobuf
#
# pip-compile requirements.in
#
-appdirs==1.4.4 ; sys_platform == "darwin"
+appdirs==1.4.4
# via
# -r requirements.in
# virtualenv
-appnope==0.1.2 ; sys_platform == "darwin"
- # via
- # -r requirements.in
- # ipython
+appnope==0.1.2
+ # via -r requirements.in
backcall==0.2.0
# via ipython
+bidict==0.21.2
+ # via python-socketio
+bitstring==3.1.7
+ # via -r requirements.in
+brotli==1.0.9
+ # via flask-compress
certifi==2020.12.5
# via requests
cffi==1.14.5
click==7.1.2
# via
# -r requirements.in
+ # flask
# pip-tools
colorama==0.4.4
# via west
# via virtualenv
docopt==0.6.2
# via pykwalify
+ecdsa==0.16.1
+ # via -r requirements.in
filelock==3.0.12
# via virtualenv
+flask-compress==1.9.0
+ # via gdbgui
+flask-socketio==2.9.6
+ # via gdbgui
+flask==0.12.5
+ # via
+ # flask-compress
+ # flask-socketio
+ # gdbgui
future==0.18.2
# via
# -r requirements.in
# mobly
+gdbgui==0.13.2.0
+ # via -r requirements.in
+gevent==1.5.0
+ # via gdbgui
+greenlet==1.0.0
+ # via gevent
humanfriendly==9.1
# via coloredlogs
idna==2.10
# via traitlets
ipython==7.21.0
# via -r requirements.in
+itsdangerous==1.1.0
+ # via flask
jedi==0.18.0
# via ipython
+jinja2==2.11.3
+ # via flask
lockfile==0.12.2
# via -r requirements.in
+markupsafe==1.1.1
+ # via jinja2
mobly==1.10.1
# via -r requirements.in
packaging==20.9
# via west
parso==0.8.1
# via jedi
+pep517==0.10.0
+ # via pip-tools
pexpect==4.8.0
# via ipython
pgi==0.0.11.2 ; sys_platform == "linux"
# via -r requirements.in
pickleshare==0.7.5
# via ipython
-pip-tools==5.5.0
+pip-tools==6.0.1
# via -r requirements.in
portpicker==1.3.1
# via
# -r requirements.in
# mobly
-prompt-toolkit==3.0.16
+prompt-toolkit==3.0.17
# via ipython
-protobuf==3.15.5
+protobuf==3.15.6
# via -r requirements.in
psutil==5.8.0
# via
# via cffi
pyelftools==0.27
# via -r requirements.in
-pygments==2.8.0
- # via ipython
+pygdbmi==0.9.0.2
+ # via
+ # -r requirements.in
+ # gdbgui
+pygments==2.8.1
+ # via
+ # gdbgui
+ # ipython
pykwalify==1.8.0
# via west
pyobjc-core==7.1 ; sys_platform == "darwin"
# mobly
python-dateutil==2.8.1
# via pykwalify
+python-engineio==4.0.1
+ # via python-socketio
+python-socketio==5.1.0
+ # via flask-socketio
pyyaml==5.4.1
# via
# mobly
# west
+reedsolo==1.5.4
+ # via -r requirements.in
requests==2.25.1
# via -r requirements.in
ruamel.yaml.clib==0.2.2
# via pykwalify
six==1.15.0
# via
+ # ecdsa
# protobuf
# python-dateutil
# virtualenv
timeout-decorator==0.5.0
# via mobly
+toml==0.10.2
+ # via pep517
traitlets==5.0.5
# via ipython
-urllib3==1.26.3
+urllib3==1.26.4
# via requests
-virtualenv==20.4.2
+virtualenv==20.4.3
# via -r requirements.in
watchdog==2.0.2
# via -r requirements.in
wcwidth==0.2.5
# via prompt-toolkit
-west==0.9.0
+werkzeug==0.16.1
+ # via flask
+west==0.10.1
# via -r requirements.in
wheel==0.36.2
# via -r requirements.in
"${chip_root}/src/lib/support/tests",
"${chip_root}/src/messaging/tests",
"${chip_root}/src/protocols/bdx/tests",
+ "${chip_root}/src/protocols/secure_channel/tests",
"${chip_root}/src/setup_payload/tests",
"${chip_root}/src/system/tests",
"${chip_root}/src/transport/raw/tests",
return err;
}
-CHIP_ERROR Command::AddStatusCode(const uint16_t aGeneralCode, const uint32_t aProtocolId, const uint16_t aProtocolCode,
+CHIP_ERROR Command::AddStatusCode(const uint16_t aGeneralCode, Protocols::Id aProtocolId, const uint16_t aProtocolCode,
const chip::ClusterId aClusterId)
{
CHIP_ERROR err = CHIP_NO_ERROR;
err = statusElementBuilder.Init(mInvokeCommandBuilder.GetWriter());
SuccessOrExit(err);
- statusElementBuilder.EncodeStatusElement(aGeneralCode, aProtocolId, aProtocolCode, aProtocolCode).EndOfStatusElement();
+ statusElementBuilder.EncodeStatusElement(aGeneralCode, aProtocolId.ToFullyQualifiedSpecForm(), aProtocolCode, aProtocolCode)
+ .EndOfStatusElement();
err = statusElementBuilder.GetError();
MoveToState(CommandState::AddCommand);
CHIP_ERROR AddCommand(chip::EndpointId aEndpintId, chip::GroupId aGroupId, chip::ClusterId aClusterId,
chip::CommandId aCommandId, BitFlags<CommandPathFlags> Flags);
CHIP_ERROR AddCommand(CommandParams & aCommandParams);
- CHIP_ERROR AddStatusCode(const uint16_t aGeneralCode, const uint32_t aProtocolId, const uint16_t aProtocolCode,
+ CHIP_ERROR AddStatusCode(const uint16_t aGeneralCode, Protocols::Id aProtocolId, const uint16_t aProtocolCode,
const chip::ClusterId aClusterId);
/**
#include "InteractionModelEngine.h"
#include <protocols/secure_channel/Constants.h>
-#include <support/ReturnMacros.h>
using GeneralStatusCode = chip::Protocols::SecureChannel::GeneralStatusCode;
// Empty Command, Add status code in invoke command response, notify cluster handler to hand it further.
err = CHIP_NO_ERROR;
ChipLogDetail(DataManagement, "Add Status code for empty command, cluster Id is %d", clusterId);
- AddStatusCode(static_cast<uint16_t>(GeneralStatusCode::kSuccess), Protocols::kProtocol_SecureChannel,
+ AddStatusCode(static_cast<uint16_t>(GeneralStatusCode::kSuccess), Protocols::SecureChannel::Id,
Protocols::SecureChannel::kProtocolCodeSuccess, clusterId);
}
else if (CHIP_NO_ERROR == err)
{
err = CHIP_NO_ERROR;
ChipLogDetail(DataManagement, "Add Status code for empty command, cluster Id is %d", clusterId);
- AddStatusCode(static_cast<uint16_t>(GeneralStatusCode::kSuccess), Protocols::kProtocol_SecureChannel,
+ AddStatusCode(static_cast<uint16_t>(GeneralStatusCode::kSuccess), Protocols::SecureChannel::Id,
Protocols::SecureChannel::kProtocolCodeSuccess, clusterId);
}
// TODO(#4503): Should call callbacks of cluster that sends the command.
mpExchangeMgr = apExchangeMgr;
mpDelegate = apDelegate;
- err = mpExchangeMgr->RegisterUnsolicitedMessageHandlerForProtocol(Protocols::kProtocol_InteractionModel, this);
+ err = mpExchangeMgr->RegisterUnsolicitedMessageHandlerForProtocol(Protocols::InteractionModel::Id, this);
SuccessOrExit(err);
exit:
| Basic | 0x0028 |
| Binding | 0xF000 |
| ColorControl | 0x0300 |
-| ContentLaunch | 0xF002 |
| DoorLock | 0x0101 |
| GeneralCommissioning | 0x0030 |
| GroupKeyManagement | 0xF004 |
| Identify | 0x0003 |
| LevelControl | 0x0008 |
| LowPower | 0x0508 |
-| MediaPlayback | 0xF001 |
| NetworkCommissioning | 0x0031 |
| OnOff | 0x0006 |
| Scenes | 0x0005 |
chip::EndpointId destinationEndpoint);
/*----------------------------------------------------------------------------*\
-| Cluster ContentLaunch | 0xF002 |
-|------------------------------------------------------------------------------|
-| Commands: | |
-| * LaunchContent | 0x00 |
-| * LaunchURL | 0x01 |
-|------------------------------------------------------------------------------|
-| Attributes: | |
-| * ClusterRevision | 0xFFFD |
-\*----------------------------------------------------------------------------*/
-
-/**
- * @brief
- * Encode an LaunchContent command for Content Launch server into buffer including the APS frame
- */
-chip::System::PacketBufferHandle encodeContentLaunchClusterLaunchContentCommand(uint8_t seqNum,
- chip::EndpointId destinationEndpoint);
-
-/**
- * @brief
- * Encode an LaunchURL command for Content Launch server into buffer including the APS frame
- */
-chip::System::PacketBufferHandle encodeContentLaunchClusterLaunchURLCommand(uint8_t seqNum, chip::EndpointId destinationEndpoint);
-
-/**
- * @brief
- * Encode a Content Launch server discover command into buffer including the APS frame
- */
-chip::System::PacketBufferHandle encodeContentLaunchClusterDiscoverAttributes(uint8_t seqNum, chip::EndpointId destinationEndpoint);
-
-/**
- * @brief
- * Encode a Content Launch server read command for the cluster revision attribute into buffer including the APS frame
- */
-chip::System::PacketBufferHandle encodeContentLaunchClusterReadClusterRevisionAttribute(uint8_t seqNum,
- chip::EndpointId destinationEndpoint);
-
-/*----------------------------------------------------------------------------*\
| Cluster DoorLock | 0x0101 |
|------------------------------------------------------------------------------|
| Commands: | |
chip::EndpointId destinationEndpoint);
/*----------------------------------------------------------------------------*\
-| Cluster MediaPlayback | 0xF001 |
-|------------------------------------------------------------------------------|
-| Commands: | |
-| * FastForwardRequest | 0x07 |
-| * NextRequest | 0x05 |
-| * PauseRequest | 0x01 |
-| * PlayRequest | 0x00 |
-| * PreviousRequest | 0x04 |
-| * RewindRequest | 0x06 |
-| * SkipBackwardRequest | 0x09 |
-| * SkipForwardRequest | 0x08 |
-| * StartOverRequest | 0x03 |
-| * StopRequest | 0x02 |
-|------------------------------------------------------------------------------|
-| Attributes: | |
-| * CurrentState | 0x0000 |
-| * ClusterRevision | 0xFFFD |
-\*----------------------------------------------------------------------------*/
-
-/**
- * @brief
- * Encode an FastForwardRequest command for Media Playback server into buffer including the APS frame
- */
-chip::System::PacketBufferHandle encodeMediaPlaybackClusterFastForwardRequestCommand(uint8_t seqNum,
- chip::EndpointId destinationEndpoint);
-
-/**
- * @brief
- * Encode an NextRequest command for Media Playback server into buffer including the APS frame
- */
-chip::System::PacketBufferHandle encodeMediaPlaybackClusterNextRequestCommand(uint8_t seqNum, chip::EndpointId destinationEndpoint);
-
-/**
- * @brief
- * Encode an PauseRequest command for Media Playback server into buffer including the APS frame
- */
-chip::System::PacketBufferHandle encodeMediaPlaybackClusterPauseRequestCommand(uint8_t seqNum,
- chip::EndpointId destinationEndpoint);
-
-/**
- * @brief
- * Encode an PlayRequest command for Media Playback server into buffer including the APS frame
- */
-chip::System::PacketBufferHandle encodeMediaPlaybackClusterPlayRequestCommand(uint8_t seqNum, chip::EndpointId destinationEndpoint);
-
-/**
- * @brief
- * Encode an PreviousRequest command for Media Playback server into buffer including the APS frame
- */
-chip::System::PacketBufferHandle encodeMediaPlaybackClusterPreviousRequestCommand(uint8_t seqNum,
- chip::EndpointId destinationEndpoint);
-
-/**
- * @brief
- * Encode an RewindRequest command for Media Playback server into buffer including the APS frame
- */
-chip::System::PacketBufferHandle encodeMediaPlaybackClusterRewindRequestCommand(uint8_t seqNum,
- chip::EndpointId destinationEndpoint);
-
-/**
- * @brief
- * Encode an SkipBackwardRequest command for Media Playback server into buffer including the APS frame
- */
-chip::System::PacketBufferHandle encodeMediaPlaybackClusterSkipBackwardRequestCommand(uint8_t seqNum,
- chip::EndpointId destinationEndpoint);
-
-/**
- * @brief
- * Encode an SkipForwardRequest command for Media Playback server into buffer including the APS frame
- */
-chip::System::PacketBufferHandle encodeMediaPlaybackClusterSkipForwardRequestCommand(uint8_t seqNum,
- chip::EndpointId destinationEndpoint);
-
-/**
- * @brief
- * Encode an StartOverRequest command for Media Playback server into buffer including the APS frame
- */
-chip::System::PacketBufferHandle encodeMediaPlaybackClusterStartOverRequestCommand(uint8_t seqNum,
- chip::EndpointId destinationEndpoint);
-
-/**
- * @brief
- * Encode an StopRequest command for Media Playback server into buffer including the APS frame
- */
-chip::System::PacketBufferHandle encodeMediaPlaybackClusterStopRequestCommand(uint8_t seqNum, chip::EndpointId destinationEndpoint);
-
-/**
- * @brief
- * Encode a Media Playback server discover command into buffer including the APS frame
- */
-chip::System::PacketBufferHandle encodeMediaPlaybackClusterDiscoverAttributes(uint8_t seqNum, chip::EndpointId destinationEndpoint);
-
-/**
- * @brief
- * Encode a Media Playback server read command for the current state attribute into buffer including the APS frame
- */
-chip::System::PacketBufferHandle encodeMediaPlaybackClusterReadCurrentStateAttribute(uint8_t seqNum,
- chip::EndpointId destinationEndpoint);
-
-/**
- * @brief
- * Encode a Media Playback server read command for the cluster revision attribute into buffer including the APS frame
- */
-chip::System::PacketBufferHandle encodeMediaPlaybackClusterReadClusterRevisionAttribute(uint8_t seqNum,
- chip::EndpointId destinationEndpoint);
-
-/*----------------------------------------------------------------------------*\
| Cluster NetworkCommissioning | 0x0031 |
|------------------------------------------------------------------------------|
| Commands: | |
#include <app/util/af.h>
+#include <app/reporting/reporting.h>
#include <app/util/af-event.h>
#include <app/util/attribute-storage.h>
#include <assert.h>
#include "gen/attribute-type.h"
#include "gen/cluster-id.h"
-#ifdef EMBER_AF_PLUGIN_REPORTING
-#include <app/reporting/reporting.h>
-#endif
-
using namespace chip;
#define COLOR_TEMP_CONTROL emberAfPluginColorControlServerTempTransitionEventControl
#include "gen/cluster-id.h"
#include "gen/command-id.h"
-#ifdef EMBER_AF_PLUGIN_REPORTING
#include <app/reporting/reporting.h>
-#endif
#ifdef EMBER_AF_PLUGIN_SCENES
#include <app/clusters/scenes/scenes.h>
#include <util/af.h>
#include <lib/support/CodeUtils.h>
-#include <lib/support/ReturnMacros.h>
#include <lib/support/SafeInt.h>
#include <lib/support/Span.h>
#include <lib/support/logging/CHIPLogging.h>
#include "gen/cluster-id.h"
#include "gen/command-id.h"
-#ifdef EMBER_AF_PLUGIN_REPORTING
#include <app/reporting/reporting.h>
-#endif
#ifdef EMBER_AF_PLUGIN_SCENES
#include <app/clusters/scenes/scenes.h>
| Basic | 0x0028 |
| Binding | 0xF000 |
| ColorControl | 0x0300 |
-| ContentLaunch | 0xF002 |
| DoorLock | 0x0101 |
| GeneralCommissioning | 0x0030 |
| GroupKeyManagement | 0xF004 |
| Identify | 0x0003 |
| LevelControl | 0x0008 |
| LowPower | 0x0508 |
-| MediaPlayback | 0xF001 |
| NetworkCommissioning | 0x0031 |
| OnOff | 0x0006 |
| Scenes | 0x0005 |
#define ZCL_STEP_SATURATION_COMMAND_ID (0x05)
#define ZCL_STOP_MOVE_STEP_COMMAND_ID (0x47)
-#define CONTENT_LAUNCH_CLUSTER_ID 0xF002
-#define ZCL_LAUNCH_CONTENT_COMMAND_ID (0x00)
-#define ZCL_LAUNCH_URL_COMMAND_ID (0x01)
-
#define DOOR_LOCK_CLUSTER_ID 0x0101
#define ZCL_CLEAR_ALL_PINS_COMMAND_ID (0x08)
#define ZCL_CLEAR_ALL_RFIDS_COMMAND_ID (0x19)
#define LOW_POWER_CLUSTER_ID 0x0508
#define ZCL_SLEEP_COMMAND_ID (0x00)
-#define MEDIA_PLAYBACK_CLUSTER_ID 0xF001
-#define ZCL_FAST_FORWARD_REQUEST_COMMAND_ID (0x07)
-#define ZCL_NEXT_REQUEST_COMMAND_ID (0x05)
-#define ZCL_PAUSE_REQUEST_COMMAND_ID (0x01)
-#define ZCL_PLAY_REQUEST_COMMAND_ID (0x00)
-#define ZCL_PREVIOUS_REQUEST_COMMAND_ID (0x04)
-#define ZCL_REWIND_REQUEST_COMMAND_ID (0x06)
-#define ZCL_SKIP_BACKWARD_REQUEST_COMMAND_ID (0x09)
-#define ZCL_SKIP_FORWARD_REQUEST_COMMAND_ID (0x08)
-#define ZCL_START_OVER_REQUEST_COMMAND_ID (0x03)
-#define ZCL_STOP_REQUEST_COMMAND_ID (0x02)
-
#define NETWORK_COMMISSIONING_CLUSTER_ID 0x0031
#define ZCL_ADD_THREAD_NETWORK_COMMAND_ID (0x06)
#define ZCL_ADD_WI_FI_NETWORK_COMMAND_ID (0x02)
}
/*----------------------------------------------------------------------------*\
-| Cluster ContentLaunch | 0xF002 |
-|------------------------------------------------------------------------------|
-| Commands: | |
-| * LaunchContent | 0x00 |
-| * LaunchURL | 0x01 |
-|------------------------------------------------------------------------------|
-| Attributes: | |
-| * ClusterRevision | 0xFFFD |
-\*----------------------------------------------------------------------------*/
-
-/*
- * Command LaunchContent
- */
-PacketBufferHandle encodeContentLaunchClusterLaunchContentCommand(uint8_t seqNum, EndpointId destinationEndpoint)
-{
- COMMAND_HEADER("LaunchContent", CONTENT_LAUNCH_CLUSTER_ID);
- buf.Put8(kFrameControlClusterSpecificCommand).Put8(seqNum).Put8(ZCL_LAUNCH_CONTENT_COMMAND_ID);
- COMMAND_FOOTER();
-}
-
-/*
- * Command LaunchURL
- */
-PacketBufferHandle encodeContentLaunchClusterLaunchURLCommand(uint8_t seqNum, EndpointId destinationEndpoint)
-{
- COMMAND_HEADER("LaunchURL", CONTENT_LAUNCH_CLUSTER_ID);
- buf.Put8(kFrameControlClusterSpecificCommand).Put8(seqNum).Put8(ZCL_LAUNCH_URL_COMMAND_ID);
- COMMAND_FOOTER();
-}
-
-PacketBufferHandle encodeContentLaunchClusterDiscoverAttributes(uint8_t seqNum, EndpointId destinationEndpoint)
-{
- COMMAND_HEADER("DiscoverContentLaunchAttributes", CONTENT_LAUNCH_CLUSTER_ID);
- buf.Put8(kFrameControlGlobalCommand).Put8(seqNum).Put8(ZCL_DISCOVER_ATTRIBUTES_COMMAND_ID).Put16(0x0000).Put8(0xFF);
- COMMAND_FOOTER();
-}
-
-/*
- * Attribute ClusterRevision
- */
-PacketBufferHandle encodeContentLaunchClusterReadClusterRevisionAttribute(uint8_t seqNum, EndpointId destinationEndpoint)
-{
- COMMAND_HEADER("ReadContentLaunchClusterRevision", CONTENT_LAUNCH_CLUSTER_ID);
- buf.Put8(kFrameControlGlobalCommand).Put8(seqNum).Put8(ZCL_READ_ATTRIBUTES_COMMAND_ID).Put16(0xFFFD);
- COMMAND_FOOTER();
-}
-
-/*----------------------------------------------------------------------------*\
| Cluster DoorLock | 0x0101 |
|------------------------------------------------------------------------------|
| Commands: | |
}
/*----------------------------------------------------------------------------*\
-| Cluster MediaPlayback | 0xF001 |
-|------------------------------------------------------------------------------|
-| Commands: | |
-| * FastForwardRequest | 0x07 |
-| * NextRequest | 0x05 |
-| * PauseRequest | 0x01 |
-| * PlayRequest | 0x00 |
-| * PreviousRequest | 0x04 |
-| * RewindRequest | 0x06 |
-| * SkipBackwardRequest | 0x09 |
-| * SkipForwardRequest | 0x08 |
-| * StartOverRequest | 0x03 |
-| * StopRequest | 0x02 |
-|------------------------------------------------------------------------------|
-| Attributes: | |
-| * CurrentState | 0x0000 |
-| * ClusterRevision | 0xFFFD |
-\*----------------------------------------------------------------------------*/
-
-/*
- * Command FastForwardRequest
- */
-PacketBufferHandle encodeMediaPlaybackClusterFastForwardRequestCommand(uint8_t seqNum, EndpointId destinationEndpoint)
-{
- COMMAND_HEADER("FastForwardRequest", MEDIA_PLAYBACK_CLUSTER_ID);
- buf.Put8(kFrameControlClusterSpecificCommand).Put8(seqNum).Put8(ZCL_FAST_FORWARD_REQUEST_COMMAND_ID);
- COMMAND_FOOTER();
-}
-
-/*
- * Command NextRequest
- */
-PacketBufferHandle encodeMediaPlaybackClusterNextRequestCommand(uint8_t seqNum, EndpointId destinationEndpoint)
-{
- COMMAND_HEADER("NextRequest", MEDIA_PLAYBACK_CLUSTER_ID);
- buf.Put8(kFrameControlClusterSpecificCommand).Put8(seqNum).Put8(ZCL_NEXT_REQUEST_COMMAND_ID);
- COMMAND_FOOTER();
-}
-
-/*
- * Command PauseRequest
- */
-PacketBufferHandle encodeMediaPlaybackClusterPauseRequestCommand(uint8_t seqNum, EndpointId destinationEndpoint)
-{
- COMMAND_HEADER("PauseRequest", MEDIA_PLAYBACK_CLUSTER_ID);
- buf.Put8(kFrameControlClusterSpecificCommand).Put8(seqNum).Put8(ZCL_PAUSE_REQUEST_COMMAND_ID);
- COMMAND_FOOTER();
-}
-
-/*
- * Command PlayRequest
- */
-PacketBufferHandle encodeMediaPlaybackClusterPlayRequestCommand(uint8_t seqNum, EndpointId destinationEndpoint)
-{
- COMMAND_HEADER("PlayRequest", MEDIA_PLAYBACK_CLUSTER_ID);
- buf.Put8(kFrameControlClusterSpecificCommand).Put8(seqNum).Put8(ZCL_PLAY_REQUEST_COMMAND_ID);
- COMMAND_FOOTER();
-}
-
-/*
- * Command PreviousRequest
- */
-PacketBufferHandle encodeMediaPlaybackClusterPreviousRequestCommand(uint8_t seqNum, EndpointId destinationEndpoint)
-{
- COMMAND_HEADER("PreviousRequest", MEDIA_PLAYBACK_CLUSTER_ID);
- buf.Put8(kFrameControlClusterSpecificCommand).Put8(seqNum).Put8(ZCL_PREVIOUS_REQUEST_COMMAND_ID);
- COMMAND_FOOTER();
-}
-
-/*
- * Command RewindRequest
- */
-PacketBufferHandle encodeMediaPlaybackClusterRewindRequestCommand(uint8_t seqNum, EndpointId destinationEndpoint)
-{
- COMMAND_HEADER("RewindRequest", MEDIA_PLAYBACK_CLUSTER_ID);
- buf.Put8(kFrameControlClusterSpecificCommand).Put8(seqNum).Put8(ZCL_REWIND_REQUEST_COMMAND_ID);
- COMMAND_FOOTER();
-}
-
-/*
- * Command SkipBackwardRequest
- */
-PacketBufferHandle encodeMediaPlaybackClusterSkipBackwardRequestCommand(uint8_t seqNum, EndpointId destinationEndpoint)
-{
- COMMAND_HEADER("SkipBackwardRequest", MEDIA_PLAYBACK_CLUSTER_ID);
- buf.Put8(kFrameControlClusterSpecificCommand).Put8(seqNum).Put8(ZCL_SKIP_BACKWARD_REQUEST_COMMAND_ID);
- COMMAND_FOOTER();
-}
-
-/*
- * Command SkipForwardRequest
- */
-PacketBufferHandle encodeMediaPlaybackClusterSkipForwardRequestCommand(uint8_t seqNum, EndpointId destinationEndpoint)
-{
- COMMAND_HEADER("SkipForwardRequest", MEDIA_PLAYBACK_CLUSTER_ID);
- buf.Put8(kFrameControlClusterSpecificCommand).Put8(seqNum).Put8(ZCL_SKIP_FORWARD_REQUEST_COMMAND_ID);
- COMMAND_FOOTER();
-}
-
-/*
- * Command StartOverRequest
- */
-PacketBufferHandle encodeMediaPlaybackClusterStartOverRequestCommand(uint8_t seqNum, EndpointId destinationEndpoint)
-{
- COMMAND_HEADER("StartOverRequest", MEDIA_PLAYBACK_CLUSTER_ID);
- buf.Put8(kFrameControlClusterSpecificCommand).Put8(seqNum).Put8(ZCL_START_OVER_REQUEST_COMMAND_ID);
- COMMAND_FOOTER();
-}
-
-/*
- * Command StopRequest
- */
-PacketBufferHandle encodeMediaPlaybackClusterStopRequestCommand(uint8_t seqNum, EndpointId destinationEndpoint)
-{
- COMMAND_HEADER("StopRequest", MEDIA_PLAYBACK_CLUSTER_ID);
- buf.Put8(kFrameControlClusterSpecificCommand).Put8(seqNum).Put8(ZCL_STOP_REQUEST_COMMAND_ID);
- COMMAND_FOOTER();
-}
-
-PacketBufferHandle encodeMediaPlaybackClusterDiscoverAttributes(uint8_t seqNum, EndpointId destinationEndpoint)
-{
- COMMAND_HEADER("DiscoverMediaPlaybackAttributes", MEDIA_PLAYBACK_CLUSTER_ID);
- buf.Put8(kFrameControlGlobalCommand).Put8(seqNum).Put8(ZCL_DISCOVER_ATTRIBUTES_COMMAND_ID).Put16(0x0000).Put8(0xFF);
- COMMAND_FOOTER();
-}
-
-/*
- * Attribute CurrentState
- */
-PacketBufferHandle encodeMediaPlaybackClusterReadCurrentStateAttribute(uint8_t seqNum, EndpointId destinationEndpoint)
-{
- COMMAND_HEADER("ReadMediaPlaybackCurrentState", MEDIA_PLAYBACK_CLUSTER_ID);
- buf.Put8(kFrameControlGlobalCommand).Put8(seqNum).Put8(ZCL_READ_ATTRIBUTES_COMMAND_ID).Put16(0x0000);
- COMMAND_FOOTER();
-}
-
-/*
- * Attribute ClusterRevision
- */
-PacketBufferHandle encodeMediaPlaybackClusterReadClusterRevisionAttribute(uint8_t seqNum, EndpointId destinationEndpoint)
-{
- COMMAND_HEADER("ReadMediaPlaybackClusterRevision", MEDIA_PLAYBACK_CLUSTER_ID);
- buf.Put8(kFrameControlGlobalCommand).Put8(seqNum).Put8(ZCL_READ_ATTRIBUTES_COMMAND_ID).Put16(0xFFFD);
- COMMAND_FOOTER();
-}
-
-/*----------------------------------------------------------------------------*\
| Cluster NetworkCommissioning | 0x0031 |
|------------------------------------------------------------------------------|
| Commands: | |
}
#ifdef EZSP_HOST
+#if REPORT_TABLE_SIZE != 0
static EmberAfPluginReportingEntry table[REPORT_TABLE_SIZE];
+#endif
void emAfPluginReportingGetEntry(uint8_t index, EmberAfPluginReportingEntry * result)
{
+#if REPORT_TABLE_SIZE != 0
memmove(result, &table[index], sizeof(EmberAfPluginReportingEntry));
+#endif
}
void emAfPluginReportingSetEntry(uint8_t index, EmberAfPluginReportingEntry * value)
{
+#if REPORT_TABLE_SIZE != 0
memmove(&table[index], value, sizeof(EmberAfPluginReportingEntry));
+#endif
}
#else
void emAfPluginReportingGetEntry(uint8_t index, EmberAfPluginReportingEntry * result)
#include <mdns/Advertiser.h>
#include <platform/CHIPDeviceLayer.h>
#include <platform/ConfigurationManager.h>
-#include <support/ReturnMacros.h>
#include <support/logging/CHIPLogging.h>
#include <transport/AdminPairingTable.h>
#include <transport/PASESession.h>
#include <app/server/SessionManager.h>
#include <core/CHIPError.h>
#include <support/CodeUtils.h>
-#include <support/ReturnMacros.h>
#include <support/SafeInt.h>
#include <transport/SecureSessionMgr.h>
#include <transport/StorablePeerConnection.h>
#include <app/server/AppDelegate.h>
#include <core/CHIPPersistentStorageDelegate.h>
#include <platform/CHIPDeviceLayer.h>
-#include <support/ReturnMacros.h>
#include <transport/RendezvousSession.h>
namespace chip {
#include <setup_payload/SetupPayload.h>
#include <support/CodeUtils.h>
#include <support/ErrorStr.h>
-#include <support/ReturnMacros.h>
#include <support/logging/CHIPLogging.h>
#include <sys/param.h>
#include <system/SystemPacketBuffer.h>
chipDie();
}
- void AsyncGetKeyValue(const char * key) override
- {
- ChipLogError(AppServer, "ServerStorageDelegate does not support async operations");
- chipDie();
- }
-
void AsyncSetKeyValue(const char * key, const char * value) override
{
ChipLogError(AppServer, "ServerStorageDelegate does not support async operations");
// TODO: This code is temporary, and must be updated to use the Cluster API.
// Issue: https://github.com/project-chip/connectedhomeip/issues/4725
- if (payloadHeader.GetProtocolID() == chip::Protocols::kProtocol_ServiceProvisioning)
+ if (payloadHeader.HasProtocol(chip::Protocols::ServiceProvisioning::Id))
{
CHIP_ERROR err = CHIP_NO_ERROR;
uint32_t timeout;
ChipLogProgress(AppServer, "Received service provisioning message. Treating it as OpenPairingWindow request");
chip::System::PacketBufferTLVReader reader;
reader.Init(std::move(buffer));
- reader.ImplicitProfileId = chip::Protocols::kProtocol_ServiceProvisioning;
+ reader.ImplicitProfileId = chip::Protocols::ServiceProvisioning::Id.ToTLVProfileId();
SuccessOrExit(reader.Next(kTLVType_UnsignedInteger, TLV::ProfileTag(reader.ImplicitProfileId, 1)));
SuccessOrExit(reader.Get(timeout));
#include <core/CHIPCore.h>
#include <inttypes.h>
-#include <support/ReturnMacros.h>
namespace {
struct ResponseCallbackInfo
#include "app/util/common.h"
#include "gen/callback.h"
-#ifdef EMBER_AF_PLUGIN_REPORTING
#include <app/reporting/reporting.h>
-#endif // EMBER_AF_PLUGIN_REPORTING
using namespace chip;
// Function itself will weed out tokens that are not tokenized.
emAfSaveAttributeToToken(data, endpoint, cluster, metadata);
-#ifdef EMBER_AF_PLUGIN_REPORTING
emberAfReportingAttributeChangeCallback(endpoint, cluster, attributeID, mask, manufacturerCode, dataType, data);
-#endif // EMBER_AF_PLUGIN_REPORTING
// Post write attribute callback for all attributes changes, regardless
// of cluster.
#include "af.h"
#include <app/clusters/ias-zone-client/ias-zone-client.h>
-#include <app/util/common.h>
-
-#ifdef EMBER_AF_PLUGIN_REPORTING
#include <app/reporting/reporting.h>
-#endif // EMBER_AF_PLUGIN_REPORTING
+#include <app/util/common.h>
#include "gen/attribute-id.h"
#include "gen/attribute-type.h"
return true;
}
-#ifdef EMBER_AF_PLUGIN_REPORTING
case ZCL_CONFIGURE_REPORTING_COMMAND_ID:
if (emberAfConfigureReportingCommandCallback(cmd))
{
return true;
}
break;
-#endif // EMBER_AF_PLUGIN_REPORTING
// ([attribute id:2] [status:1] [type:0/1] [value:0/V])+
case ZCL_READ_ATTRIBUTES_RESPONSE_COMMAND_ID:
}
return true;
-#ifdef EMBER_AF_PLUGIN_REPORTING
// ([status:1] [direction:1] [attribute id:2])+
case ZCL_CONFIGURE_REPORTING_RESPONSE_COMMAND_ID:
if (!emberAfConfigureReportingResponseCallback(clusterId, message + msgIndex, static_cast<uint16_t>(msgLen - msgIndex)))
emberAfSendDefaultResponse(cmd, EMBER_ZCL_STATUS_SUCCESS);
}
return true;
-#endif // EMBER_AF_PLUGIN_REPORTING
// ([attribute id:2] [type:1] [data:V])+
case ZCL_REPORT_ATTRIBUTES_COMMAND_ID:
#include "af-main.h"
#include "af.h"
#include "app/util/common.h"
+#include <app/reporting/reporting.h>
#include "gen/attribute-id.h"
#include "gen/attribute-type.h"
#include <app/clusters/groups-server/groups-server.h>
#endif // EMBER_AF_PLUGIN_GROUPS_SERVER
-#ifdef EMBER_AF_PLUGIN_REPORTING
-#include <app/reporting/reporting.h>
-#endif // EMBER_AF_PLUGIN_REPORTING
-
using namespace chip;
// Function for Compatibility
// initialize event management system
emAfInitEvents();
-#ifdef EMBER_AF_PLUGIN_REPORTING
+ // Initialize the reporting plugin
emberAfPluginReportingInitCallback();
-#endif
+
#ifdef EMBER_AF_PLUGIN_TEMPERATURE_MEASUREMENT_SERVER
emberAfPluginTemperatureMeasurementServerInitCallback();
#endif
// && emberNetworkState() == EMBER_NO_NETWORK
)
{
-#ifdef EMBER_AF_PLUGIN_REPORTING
// the report table should be cleared when the stack comes down.
// going to a new network means new report devices should be discovered.
// if the table isnt cleared the device keeps trying to send messages.
emberAfClearReportTableCallback();
-#endif // EMBER_AF_PLUGIN_REPORTING
}
emberAfRegistrationAbortCallback();
CHIPDefaultFailureCallbackBridge * callback = reinterpret_cast<CHIPDefaultFailureCallbackBridge *>(context);
if (callback && callback->mQueue) {
dispatch_async(callback->mQueue, ^{
- NSError* error = [NSError errorWithDomain:CHIPErrorDomain code:status userInfo:@{NSLocalizedDescriptionKey:@""}];
+ NSError * error = [CHIPError errorForCHIPErrorCode:status];
callback->mHandler(error, nil);
callback->Cancel();
delete callback;
{
return nil;
}
-
+
CHIP_ERROR err = cppCluster->Associate([device internalDevice], endpoint);
if (err != CHIP_NO_ERROR) {
return nil;
#define ZRD(x) EMBER_ZCL_REPORTING_DIRECTION_ ## x
#define ZAP_REPORT_DIRECTION(x) ZRD(x)
-{{#if (endpoint_reporting_config_default_count)}}
-// Use this macro to check if Reporting plugin is included
-#define EMBER_AF_PLUGIN_REPORTING
// User options for plugin Reporting
#define EMBER_AF_PLUGIN_REPORTING_TABLE_SIZE ({{endpoint_reporting_config_default_count}})
#define EMBER_AF_PLUGIN_REPORTING_ENABLE_GROUP_BOUND_REPORTS
-{{/if}}
#define EMBER_AF_GENERATED_REPORTING_CONFIG_DEFAULTS_TABLE_SIZE ({{endpoint_reporting_config_default_count}})
#define EMBER_AF_GENERATED_REPORTING_CONFIG_DEFAULTS {{endpoint_reporting_config_defaults}}
#include <app/chip-zcl-zpro-codec-api.h>
#include <lib/support/Span.h>
-#include <support/ReturnMacros.h>
namespace chip {
namespace Controller {
#include <app/CommandSender.h>
#include <app/InteractionModelEngine.h>
#include <lib/support/Span.h>
-#include <support/ReturnMacros.h>
#include <controller/CHIPClusters.h>
#include <controller/CHIPDevice.h>
<cluster>
<domain>General</domain>
<name>Content Launch</name>
- <code>0xF002</code>
+ <code>0x050a</code>
<define>CONTENT_LAUNCH_CLUSTER</define>
<client init="false" tick="false">true</client>
<server init="false" tick="false">true</server>
<cluster>
<domain>General</domain>
<name>Media Playback</name>
- <code>0xF001</code>
+ <code>0x0506</code>
<define>MEDIA_PLAYBACK_CLUSTER</define>
<client init="false" tick="false">true</client>
<server init="false" tick="false">true</server>
if (mSendQueue.IsNull())
{
mSendQueue = std::move(data);
- ChipLogDebugBleEndPoint(Ble, "%s: Set data as new mSendQueue %p, type %d", __FUNCTION__, mSendQueue, type);
+ ChipLogDebugBleEndPoint(Ble, "%s: Set data as new mSendQueue %p, type %d", __FUNCTION__, mSendQueue->Start(), type);
}
else
{
mSendQueue->AddToEnd(std::move(data));
- ChipLogDebugBleEndPoint(Ble, "%s: Append data to mSendQueue %p, type %d", __FUNCTION__, mSendQueue, type);
+ ChipLogDebugBleEndPoint(Ble, "%s: Append data to mSendQueue %p, type %d", __FUNCTION__, mSendQueue->Start(), type);
}
QueueTxUnlock();
{
#ifdef CHIP_BLE_END_POINT_DEBUG_LOGGING_ENABLED
if (mRemoteReceiveWindowSize <= BTP_WINDOW_NO_ACK_SEND_THRESHOLD &&
- !mTimerStateFlags.Has(TimerStateFlag::kSendAckTimerRunning) && mAckToSend == NULL)
+ !mTimerStateFlags.Has(TimerStateFlag::kSendAckTimerRunning) && mAckToSend.IsNull())
{
ChipLogDebugBleEndPoint(Ble, "NO SEND: receive window almost closed, and no ack to send");
}
#include <app/chip-zcl-zpro-codec-api.h>
#include <lib/support/Span.h>
-#include <support/ReturnMacros.h>
namespace chip {
namespace Controller {
return SendCommand(seqNum, std::move(encodedCommand), onSuccessCallback, onFailureCallback);
}
-// ContentLaunch Cluster Commands
-CHIP_ERROR ContentLaunchCluster::LaunchContent(Callback::Cancelable * onSuccessCallback, Callback::Cancelable * onFailureCallback)
-{
-#ifdef CHIP_APP_USE_INTERACTION_MODEL
- VerifyOrReturnError(mDevice != nullptr, CHIP_ERROR_INCORRECT_STATE);
- (void) onSuccessCallback;
- (void) onFailureCallback;
-
- app::Command::CommandParams cmdParams = { mEndpoint, /* group id */ 0, mClusterId, kLaunchContentCommandId,
- (chip::app::Command::CommandPathFlags::kEndpointIdValid) };
- app::Command * ZCLcommand = mDevice->GetCommandSender();
-
- TLV::TLVWriter writer = ZCLcommand->CreateCommandDataElementTLVWriter();
-
- TLV::TLVType dummyType = TLV::kTLVType_NotSpecified;
- ReturnErrorOnFailure(writer.StartContainer(TLV::AnonymousTag, TLV::kTLVType_Structure, dummyType));
-
- // Command takes no arguments.
-
- ReturnErrorOnFailure(writer.EndContainer(dummyType));
- ReturnErrorOnFailure(writer.Finalize());
- ReturnErrorOnFailure(ZCLcommand->AddCommand(cmdParams));
-
- return mDevice->SendCommands();
-#else
- uint8_t seqNum = mDevice->GetNextSequenceNumber();
- System::PacketBufferHandle encodedCommand = encodeContentLaunchClusterLaunchContentCommand(seqNum, mEndpoint);
- return SendCommand(seqNum, std::move(encodedCommand), onSuccessCallback, onFailureCallback);
-#endif
-}
-
-CHIP_ERROR ContentLaunchCluster::LaunchURL(Callback::Cancelable * onSuccessCallback, Callback::Cancelable * onFailureCallback)
-{
-#ifdef CHIP_APP_USE_INTERACTION_MODEL
- VerifyOrReturnError(mDevice != nullptr, CHIP_ERROR_INCORRECT_STATE);
- (void) onSuccessCallback;
- (void) onFailureCallback;
-
- app::Command::CommandParams cmdParams = { mEndpoint, /* group id */ 0, mClusterId, kLaunchURLCommandId,
- (chip::app::Command::CommandPathFlags::kEndpointIdValid) };
- app::Command * ZCLcommand = mDevice->GetCommandSender();
-
- TLV::TLVWriter writer = ZCLcommand->CreateCommandDataElementTLVWriter();
-
- TLV::TLVType dummyType = TLV::kTLVType_NotSpecified;
- ReturnErrorOnFailure(writer.StartContainer(TLV::AnonymousTag, TLV::kTLVType_Structure, dummyType));
-
- // Command takes no arguments.
-
- ReturnErrorOnFailure(writer.EndContainer(dummyType));
- ReturnErrorOnFailure(writer.Finalize());
- ReturnErrorOnFailure(ZCLcommand->AddCommand(cmdParams));
-
- return mDevice->SendCommands();
-#else
- uint8_t seqNum = mDevice->GetNextSequenceNumber();
- System::PacketBufferHandle encodedCommand = encodeContentLaunchClusterLaunchURLCommand(seqNum, mEndpoint);
- return SendCommand(seqNum, std::move(encodedCommand), onSuccessCallback, onFailureCallback);
-#endif
-}
-
-// ContentLaunch Cluster Attributes
-CHIP_ERROR ContentLaunchCluster::DiscoverAttributes(Callback::Cancelable * onSuccessCallback,
- Callback::Cancelable * onFailureCallback)
-{
- uint8_t seqNum = mDevice->GetNextSequenceNumber();
- System::PacketBufferHandle encodedCommand = encodeContentLaunchClusterDiscoverAttributes(seqNum, mEndpoint);
- return SendCommand(seqNum, std::move(encodedCommand), onSuccessCallback, onFailureCallback);
-}
-CHIP_ERROR ContentLaunchCluster::ReadAttributeClusterRevision(Callback::Cancelable * onSuccessCallback,
- Callback::Cancelable * onFailureCallback)
-{
- uint8_t seqNum = mDevice->GetNextSequenceNumber();
- System::PacketBufferHandle encodedCommand = encodeContentLaunchClusterReadClusterRevisionAttribute(seqNum, mEndpoint);
- return SendCommand(seqNum, std::move(encodedCommand), onSuccessCallback, onFailureCallback);
-}
-
// DoorLock Cluster Commands
CHIP_ERROR DoorLockCluster::ClearAllPins(Callback::Cancelable * onSuccessCallback, Callback::Cancelable * onFailureCallback)
{
return SendCommand(seqNum, std::move(encodedCommand), onSuccessCallback, onFailureCallback);
}
-// MediaPlayback Cluster Commands
-CHIP_ERROR MediaPlaybackCluster::FastForwardRequest(Callback::Cancelable * onSuccessCallback,
- Callback::Cancelable * onFailureCallback)
-{
-#ifdef CHIP_APP_USE_INTERACTION_MODEL
- VerifyOrReturnError(mDevice != nullptr, CHIP_ERROR_INCORRECT_STATE);
- (void) onSuccessCallback;
- (void) onFailureCallback;
-
- app::Command::CommandParams cmdParams = { mEndpoint, /* group id */ 0, mClusterId, kFastForwardRequestCommandId,
- (chip::app::Command::CommandPathFlags::kEndpointIdValid) };
- app::Command * ZCLcommand = mDevice->GetCommandSender();
-
- TLV::TLVWriter writer = ZCLcommand->CreateCommandDataElementTLVWriter();
-
- TLV::TLVType dummyType = TLV::kTLVType_NotSpecified;
- ReturnErrorOnFailure(writer.StartContainer(TLV::AnonymousTag, TLV::kTLVType_Structure, dummyType));
-
- // Command takes no arguments.
-
- ReturnErrorOnFailure(writer.EndContainer(dummyType));
- ReturnErrorOnFailure(writer.Finalize());
- ReturnErrorOnFailure(ZCLcommand->AddCommand(cmdParams));
-
- return mDevice->SendCommands();
-#else
- uint8_t seqNum = mDevice->GetNextSequenceNumber();
- System::PacketBufferHandle encodedCommand = encodeMediaPlaybackClusterFastForwardRequestCommand(seqNum, mEndpoint);
- return SendCommand(seqNum, std::move(encodedCommand), onSuccessCallback, onFailureCallback);
-#endif
-}
-
-CHIP_ERROR MediaPlaybackCluster::NextRequest(Callback::Cancelable * onSuccessCallback, Callback::Cancelable * onFailureCallback)
-{
-#ifdef CHIP_APP_USE_INTERACTION_MODEL
- VerifyOrReturnError(mDevice != nullptr, CHIP_ERROR_INCORRECT_STATE);
- (void) onSuccessCallback;
- (void) onFailureCallback;
-
- app::Command::CommandParams cmdParams = { mEndpoint, /* group id */ 0, mClusterId, kNextRequestCommandId,
- (chip::app::Command::CommandPathFlags::kEndpointIdValid) };
- app::Command * ZCLcommand = mDevice->GetCommandSender();
-
- TLV::TLVWriter writer = ZCLcommand->CreateCommandDataElementTLVWriter();
-
- TLV::TLVType dummyType = TLV::kTLVType_NotSpecified;
- ReturnErrorOnFailure(writer.StartContainer(TLV::AnonymousTag, TLV::kTLVType_Structure, dummyType));
-
- // Command takes no arguments.
-
- ReturnErrorOnFailure(writer.EndContainer(dummyType));
- ReturnErrorOnFailure(writer.Finalize());
- ReturnErrorOnFailure(ZCLcommand->AddCommand(cmdParams));
-
- return mDevice->SendCommands();
-#else
- uint8_t seqNum = mDevice->GetNextSequenceNumber();
- System::PacketBufferHandle encodedCommand = encodeMediaPlaybackClusterNextRequestCommand(seqNum, mEndpoint);
- return SendCommand(seqNum, std::move(encodedCommand), onSuccessCallback, onFailureCallback);
-#endif
-}
-
-CHIP_ERROR MediaPlaybackCluster::PauseRequest(Callback::Cancelable * onSuccessCallback, Callback::Cancelable * onFailureCallback)
-{
-#ifdef CHIP_APP_USE_INTERACTION_MODEL
- VerifyOrReturnError(mDevice != nullptr, CHIP_ERROR_INCORRECT_STATE);
- (void) onSuccessCallback;
- (void) onFailureCallback;
-
- app::Command::CommandParams cmdParams = { mEndpoint, /* group id */ 0, mClusterId, kPauseRequestCommandId,
- (chip::app::Command::CommandPathFlags::kEndpointIdValid) };
- app::Command * ZCLcommand = mDevice->GetCommandSender();
-
- TLV::TLVWriter writer = ZCLcommand->CreateCommandDataElementTLVWriter();
-
- TLV::TLVType dummyType = TLV::kTLVType_NotSpecified;
- ReturnErrorOnFailure(writer.StartContainer(TLV::AnonymousTag, TLV::kTLVType_Structure, dummyType));
-
- // Command takes no arguments.
-
- ReturnErrorOnFailure(writer.EndContainer(dummyType));
- ReturnErrorOnFailure(writer.Finalize());
- ReturnErrorOnFailure(ZCLcommand->AddCommand(cmdParams));
-
- return mDevice->SendCommands();
-#else
- uint8_t seqNum = mDevice->GetNextSequenceNumber();
- System::PacketBufferHandle encodedCommand = encodeMediaPlaybackClusterPauseRequestCommand(seqNum, mEndpoint);
- return SendCommand(seqNum, std::move(encodedCommand), onSuccessCallback, onFailureCallback);
-#endif
-}
-
-CHIP_ERROR MediaPlaybackCluster::PlayRequest(Callback::Cancelable * onSuccessCallback, Callback::Cancelable * onFailureCallback)
-{
-#ifdef CHIP_APP_USE_INTERACTION_MODEL
- VerifyOrReturnError(mDevice != nullptr, CHIP_ERROR_INCORRECT_STATE);
- (void) onSuccessCallback;
- (void) onFailureCallback;
-
- app::Command::CommandParams cmdParams = { mEndpoint, /* group id */ 0, mClusterId, kPlayRequestCommandId,
- (chip::app::Command::CommandPathFlags::kEndpointIdValid) };
- app::Command * ZCLcommand = mDevice->GetCommandSender();
-
- TLV::TLVWriter writer = ZCLcommand->CreateCommandDataElementTLVWriter();
-
- TLV::TLVType dummyType = TLV::kTLVType_NotSpecified;
- ReturnErrorOnFailure(writer.StartContainer(TLV::AnonymousTag, TLV::kTLVType_Structure, dummyType));
-
- // Command takes no arguments.
-
- ReturnErrorOnFailure(writer.EndContainer(dummyType));
- ReturnErrorOnFailure(writer.Finalize());
- ReturnErrorOnFailure(ZCLcommand->AddCommand(cmdParams));
-
- return mDevice->SendCommands();
-#else
- uint8_t seqNum = mDevice->GetNextSequenceNumber();
- System::PacketBufferHandle encodedCommand = encodeMediaPlaybackClusterPlayRequestCommand(seqNum, mEndpoint);
- return SendCommand(seqNum, std::move(encodedCommand), onSuccessCallback, onFailureCallback);
-#endif
-}
-
-CHIP_ERROR MediaPlaybackCluster::PreviousRequest(Callback::Cancelable * onSuccessCallback, Callback::Cancelable * onFailureCallback)
-{
-#ifdef CHIP_APP_USE_INTERACTION_MODEL
- VerifyOrReturnError(mDevice != nullptr, CHIP_ERROR_INCORRECT_STATE);
- (void) onSuccessCallback;
- (void) onFailureCallback;
-
- app::Command::CommandParams cmdParams = { mEndpoint, /* group id */ 0, mClusterId, kPreviousRequestCommandId,
- (chip::app::Command::CommandPathFlags::kEndpointIdValid) };
- app::Command * ZCLcommand = mDevice->GetCommandSender();
-
- TLV::TLVWriter writer = ZCLcommand->CreateCommandDataElementTLVWriter();
-
- TLV::TLVType dummyType = TLV::kTLVType_NotSpecified;
- ReturnErrorOnFailure(writer.StartContainer(TLV::AnonymousTag, TLV::kTLVType_Structure, dummyType));
-
- // Command takes no arguments.
-
- ReturnErrorOnFailure(writer.EndContainer(dummyType));
- ReturnErrorOnFailure(writer.Finalize());
- ReturnErrorOnFailure(ZCLcommand->AddCommand(cmdParams));
-
- return mDevice->SendCommands();
-#else
- uint8_t seqNum = mDevice->GetNextSequenceNumber();
- System::PacketBufferHandle encodedCommand = encodeMediaPlaybackClusterPreviousRequestCommand(seqNum, mEndpoint);
- return SendCommand(seqNum, std::move(encodedCommand), onSuccessCallback, onFailureCallback);
-#endif
-}
-
-CHIP_ERROR MediaPlaybackCluster::RewindRequest(Callback::Cancelable * onSuccessCallback, Callback::Cancelable * onFailureCallback)
-{
-#ifdef CHIP_APP_USE_INTERACTION_MODEL
- VerifyOrReturnError(mDevice != nullptr, CHIP_ERROR_INCORRECT_STATE);
- (void) onSuccessCallback;
- (void) onFailureCallback;
-
- app::Command::CommandParams cmdParams = { mEndpoint, /* group id */ 0, mClusterId, kRewindRequestCommandId,
- (chip::app::Command::CommandPathFlags::kEndpointIdValid) };
- app::Command * ZCLcommand = mDevice->GetCommandSender();
-
- TLV::TLVWriter writer = ZCLcommand->CreateCommandDataElementTLVWriter();
-
- TLV::TLVType dummyType = TLV::kTLVType_NotSpecified;
- ReturnErrorOnFailure(writer.StartContainer(TLV::AnonymousTag, TLV::kTLVType_Structure, dummyType));
-
- // Command takes no arguments.
-
- ReturnErrorOnFailure(writer.EndContainer(dummyType));
- ReturnErrorOnFailure(writer.Finalize());
- ReturnErrorOnFailure(ZCLcommand->AddCommand(cmdParams));
-
- return mDevice->SendCommands();
-#else
- uint8_t seqNum = mDevice->GetNextSequenceNumber();
- System::PacketBufferHandle encodedCommand = encodeMediaPlaybackClusterRewindRequestCommand(seqNum, mEndpoint);
- return SendCommand(seqNum, std::move(encodedCommand), onSuccessCallback, onFailureCallback);
-#endif
-}
-
-CHIP_ERROR MediaPlaybackCluster::SkipBackwardRequest(Callback::Cancelable * onSuccessCallback,
- Callback::Cancelable * onFailureCallback)
-{
-#ifdef CHIP_APP_USE_INTERACTION_MODEL
- VerifyOrReturnError(mDevice != nullptr, CHIP_ERROR_INCORRECT_STATE);
- (void) onSuccessCallback;
- (void) onFailureCallback;
-
- app::Command::CommandParams cmdParams = { mEndpoint, /* group id */ 0, mClusterId, kSkipBackwardRequestCommandId,
- (chip::app::Command::CommandPathFlags::kEndpointIdValid) };
- app::Command * ZCLcommand = mDevice->GetCommandSender();
-
- TLV::TLVWriter writer = ZCLcommand->CreateCommandDataElementTLVWriter();
-
- TLV::TLVType dummyType = TLV::kTLVType_NotSpecified;
- ReturnErrorOnFailure(writer.StartContainer(TLV::AnonymousTag, TLV::kTLVType_Structure, dummyType));
-
- // Command takes no arguments.
-
- ReturnErrorOnFailure(writer.EndContainer(dummyType));
- ReturnErrorOnFailure(writer.Finalize());
- ReturnErrorOnFailure(ZCLcommand->AddCommand(cmdParams));
-
- return mDevice->SendCommands();
-#else
- uint8_t seqNum = mDevice->GetNextSequenceNumber();
- System::PacketBufferHandle encodedCommand = encodeMediaPlaybackClusterSkipBackwardRequestCommand(seqNum, mEndpoint);
- return SendCommand(seqNum, std::move(encodedCommand), onSuccessCallback, onFailureCallback);
-#endif
-}
-
-CHIP_ERROR MediaPlaybackCluster::SkipForwardRequest(Callback::Cancelable * onSuccessCallback,
- Callback::Cancelable * onFailureCallback)
-{
-#ifdef CHIP_APP_USE_INTERACTION_MODEL
- VerifyOrReturnError(mDevice != nullptr, CHIP_ERROR_INCORRECT_STATE);
- (void) onSuccessCallback;
- (void) onFailureCallback;
-
- app::Command::CommandParams cmdParams = { mEndpoint, /* group id */ 0, mClusterId, kSkipForwardRequestCommandId,
- (chip::app::Command::CommandPathFlags::kEndpointIdValid) };
- app::Command * ZCLcommand = mDevice->GetCommandSender();
-
- TLV::TLVWriter writer = ZCLcommand->CreateCommandDataElementTLVWriter();
-
- TLV::TLVType dummyType = TLV::kTLVType_NotSpecified;
- ReturnErrorOnFailure(writer.StartContainer(TLV::AnonymousTag, TLV::kTLVType_Structure, dummyType));
-
- // Command takes no arguments.
-
- ReturnErrorOnFailure(writer.EndContainer(dummyType));
- ReturnErrorOnFailure(writer.Finalize());
- ReturnErrorOnFailure(ZCLcommand->AddCommand(cmdParams));
-
- return mDevice->SendCommands();
-#else
- uint8_t seqNum = mDevice->GetNextSequenceNumber();
- System::PacketBufferHandle encodedCommand = encodeMediaPlaybackClusterSkipForwardRequestCommand(seqNum, mEndpoint);
- return SendCommand(seqNum, std::move(encodedCommand), onSuccessCallback, onFailureCallback);
-#endif
-}
-
-CHIP_ERROR MediaPlaybackCluster::StartOverRequest(Callback::Cancelable * onSuccessCallback,
- Callback::Cancelable * onFailureCallback)
-{
-#ifdef CHIP_APP_USE_INTERACTION_MODEL
- VerifyOrReturnError(mDevice != nullptr, CHIP_ERROR_INCORRECT_STATE);
- (void) onSuccessCallback;
- (void) onFailureCallback;
-
- app::Command::CommandParams cmdParams = { mEndpoint, /* group id */ 0, mClusterId, kStartOverRequestCommandId,
- (chip::app::Command::CommandPathFlags::kEndpointIdValid) };
- app::Command * ZCLcommand = mDevice->GetCommandSender();
-
- TLV::TLVWriter writer = ZCLcommand->CreateCommandDataElementTLVWriter();
-
- TLV::TLVType dummyType = TLV::kTLVType_NotSpecified;
- ReturnErrorOnFailure(writer.StartContainer(TLV::AnonymousTag, TLV::kTLVType_Structure, dummyType));
-
- // Command takes no arguments.
-
- ReturnErrorOnFailure(writer.EndContainer(dummyType));
- ReturnErrorOnFailure(writer.Finalize());
- ReturnErrorOnFailure(ZCLcommand->AddCommand(cmdParams));
-
- return mDevice->SendCommands();
-#else
- uint8_t seqNum = mDevice->GetNextSequenceNumber();
- System::PacketBufferHandle encodedCommand = encodeMediaPlaybackClusterStartOverRequestCommand(seqNum, mEndpoint);
- return SendCommand(seqNum, std::move(encodedCommand), onSuccessCallback, onFailureCallback);
-#endif
-}
-
-CHIP_ERROR MediaPlaybackCluster::StopRequest(Callback::Cancelable * onSuccessCallback, Callback::Cancelable * onFailureCallback)
-{
-#ifdef CHIP_APP_USE_INTERACTION_MODEL
- VerifyOrReturnError(mDevice != nullptr, CHIP_ERROR_INCORRECT_STATE);
- (void) onSuccessCallback;
- (void) onFailureCallback;
-
- app::Command::CommandParams cmdParams = { mEndpoint, /* group id */ 0, mClusterId, kStopRequestCommandId,
- (chip::app::Command::CommandPathFlags::kEndpointIdValid) };
- app::Command * ZCLcommand = mDevice->GetCommandSender();
-
- TLV::TLVWriter writer = ZCLcommand->CreateCommandDataElementTLVWriter();
-
- TLV::TLVType dummyType = TLV::kTLVType_NotSpecified;
- ReturnErrorOnFailure(writer.StartContainer(TLV::AnonymousTag, TLV::kTLVType_Structure, dummyType));
-
- // Command takes no arguments.
-
- ReturnErrorOnFailure(writer.EndContainer(dummyType));
- ReturnErrorOnFailure(writer.Finalize());
- ReturnErrorOnFailure(ZCLcommand->AddCommand(cmdParams));
-
- return mDevice->SendCommands();
-#else
- uint8_t seqNum = mDevice->GetNextSequenceNumber();
- System::PacketBufferHandle encodedCommand = encodeMediaPlaybackClusterStopRequestCommand(seqNum, mEndpoint);
- return SendCommand(seqNum, std::move(encodedCommand), onSuccessCallback, onFailureCallback);
-#endif
-}
-
-// MediaPlayback Cluster Attributes
-CHIP_ERROR MediaPlaybackCluster::DiscoverAttributes(Callback::Cancelable * onSuccessCallback,
- Callback::Cancelable * onFailureCallback)
-{
- uint8_t seqNum = mDevice->GetNextSequenceNumber();
- System::PacketBufferHandle encodedCommand = encodeMediaPlaybackClusterDiscoverAttributes(seqNum, mEndpoint);
- return SendCommand(seqNum, std::move(encodedCommand), onSuccessCallback, onFailureCallback);
-}
-CHIP_ERROR MediaPlaybackCluster::ReadAttributeCurrentState(Callback::Cancelable * onSuccessCallback,
- Callback::Cancelable * onFailureCallback)
-{
- uint8_t seqNum = mDevice->GetNextSequenceNumber();
- System::PacketBufferHandle encodedCommand = encodeMediaPlaybackClusterReadCurrentStateAttribute(seqNum, mEndpoint);
- return SendCommand(seqNum, std::move(encodedCommand), onSuccessCallback, onFailureCallback);
-}
-
-CHIP_ERROR MediaPlaybackCluster::ReadAttributeClusterRevision(Callback::Cancelable * onSuccessCallback,
- Callback::Cancelable * onFailureCallback)
-{
- uint8_t seqNum = mDevice->GetNextSequenceNumber();
- System::PacketBufferHandle encodedCommand = encodeMediaPlaybackClusterReadClusterRevisionAttribute(seqNum, mEndpoint);
- return SendCommand(seqNum, std::move(encodedCommand), onSuccessCallback, onFailureCallback);
-}
-
// NetworkCommissioning Cluster Commands
CHIP_ERROR NetworkCommissioningCluster::AddThreadNetwork(Callback::Cancelable * onSuccessCallback,
Callback::Cancelable * onFailureCallback,
constexpr ClusterId kBasicClusterId = 0x0028;
constexpr ClusterId kBindingClusterId = 0xF000;
constexpr ClusterId kColorControlClusterId = 0x0300;
-constexpr ClusterId kContentLaunchClusterId = 0xF002;
constexpr ClusterId kDoorLockClusterId = 0x0101;
constexpr ClusterId kGeneralCommissioningClusterId = 0x0030;
constexpr ClusterId kGroupKeyManagementClusterId = 0xF004;
constexpr ClusterId kIdentifyClusterId = 0x0003;
constexpr ClusterId kLevelControlClusterId = 0x0008;
constexpr ClusterId kLowPowerClusterId = 0x0508;
-constexpr ClusterId kMediaPlaybackClusterId = 0xF001;
constexpr ClusterId kNetworkCommissioningClusterId = 0x0031;
constexpr ClusterId kOnOffClusterId = 0x0006;
constexpr ClusterId kScenesClusterId = 0x0005;
static constexpr CommandId kStopMoveStepCommandId = 0x47;
};
-class DLL_EXPORT ContentLaunchCluster : public ClusterBase
-{
-public:
- ContentLaunchCluster() : ClusterBase(kContentLaunchClusterId) {}
- ~ContentLaunchCluster() {}
-
- // Cluster Commands
- CHIP_ERROR LaunchContent(Callback::Cancelable * onSuccessCallback, Callback::Cancelable * onFailureCallback);
- CHIP_ERROR LaunchURL(Callback::Cancelable * onSuccessCallback, Callback::Cancelable * onFailureCallback);
-
- // Cluster Attributes
- CHIP_ERROR DiscoverAttributes(Callback::Cancelable * onSuccessCallback, Callback::Cancelable * onFailureCallback);
- CHIP_ERROR ReadAttributeClusterRevision(Callback::Cancelable * onSuccessCallback, Callback::Cancelable * onFailureCallback);
-
-private:
- static constexpr CommandId kLaunchContentCommandId = 0x00;
- static constexpr CommandId kLaunchURLCommandId = 0x01;
-};
-
class DLL_EXPORT DoorLockCluster : public ClusterBase
{
public:
static constexpr CommandId kSleepCommandId = 0x00;
};
-class DLL_EXPORT MediaPlaybackCluster : public ClusterBase
-{
-public:
- MediaPlaybackCluster() : ClusterBase(kMediaPlaybackClusterId) {}
- ~MediaPlaybackCluster() {}
-
- // Cluster Commands
- CHIP_ERROR FastForwardRequest(Callback::Cancelable * onSuccessCallback, Callback::Cancelable * onFailureCallback);
- CHIP_ERROR NextRequest(Callback::Cancelable * onSuccessCallback, Callback::Cancelable * onFailureCallback);
- CHIP_ERROR PauseRequest(Callback::Cancelable * onSuccessCallback, Callback::Cancelable * onFailureCallback);
- CHIP_ERROR PlayRequest(Callback::Cancelable * onSuccessCallback, Callback::Cancelable * onFailureCallback);
- CHIP_ERROR PreviousRequest(Callback::Cancelable * onSuccessCallback, Callback::Cancelable * onFailureCallback);
- CHIP_ERROR RewindRequest(Callback::Cancelable * onSuccessCallback, Callback::Cancelable * onFailureCallback);
- CHIP_ERROR SkipBackwardRequest(Callback::Cancelable * onSuccessCallback, Callback::Cancelable * onFailureCallback);
- CHIP_ERROR SkipForwardRequest(Callback::Cancelable * onSuccessCallback, Callback::Cancelable * onFailureCallback);
- CHIP_ERROR StartOverRequest(Callback::Cancelable * onSuccessCallback, Callback::Cancelable * onFailureCallback);
- CHIP_ERROR StopRequest(Callback::Cancelable * onSuccessCallback, Callback::Cancelable * onFailureCallback);
-
- // Cluster Attributes
- CHIP_ERROR DiscoverAttributes(Callback::Cancelable * onSuccessCallback, Callback::Cancelable * onFailureCallback);
- CHIP_ERROR ReadAttributeCurrentState(Callback::Cancelable * onSuccessCallback, Callback::Cancelable * onFailureCallback);
- CHIP_ERROR ReadAttributeClusterRevision(Callback::Cancelable * onSuccessCallback, Callback::Cancelable * onFailureCallback);
-
-private:
- static constexpr CommandId kFastForwardRequestCommandId = 0x07;
- static constexpr CommandId kNextRequestCommandId = 0x05;
- static constexpr CommandId kPauseRequestCommandId = 0x01;
- static constexpr CommandId kPlayRequestCommandId = 0x00;
- static constexpr CommandId kPreviousRequestCommandId = 0x04;
- static constexpr CommandId kRewindRequestCommandId = 0x06;
- static constexpr CommandId kSkipBackwardRequestCommandId = 0x09;
- static constexpr CommandId kSkipForwardRequestCommandId = 0x08;
- static constexpr CommandId kStartOverRequestCommandId = 0x03;
- static constexpr CommandId kStopRequestCommandId = 0x02;
-};
-
class DLL_EXPORT NetworkCommissioningCluster : public ClusterBase
{
public:
#include <support/CHIPMem.h>
#include <support/CodeUtils.h>
#include <support/ErrorStr.h>
-#include <support/ReturnMacros.h>
#include <support/SafeInt.h>
#include <support/logging/CHIPLogging.h>
#include <system/TLVPacketBufferBackingStore.h>
System::PacketBufferTLVWriter writer;
writer.Init(std::move(buf));
- writer.ImplicitProfileId = chip::Protocols::kProtocol_ServiceProvisioning;
+ writer.ImplicitProfileId = chip::Protocols::ServiceProvisioning::Id.ToTLVProfileId();
ReturnErrorOnFailure(writer.Put(TLV::ProfileTag(writer.ImplicitProfileId, 1), timeout));
PayloadHeader header;
- header.SetMessageType(chip::Protocols::kProtocol_ServiceProvisioning, 0);
+ header.SetMessageType(chip::Protocols::ServiceProvisioning::Id, 0);
ReturnErrorOnFailure(SendMessage(std::move(outBuffer), header));
#include <support/CHIPMem.h>
#include <support/CodeUtils.h>
#include <support/ErrorStr.h>
-#include <support/ReturnMacros.h>
#include <support/SafeInt.h>
#include <support/TimeUtils.h>
#include <support/logging/CHIPLogging.h>
return err;
}
-void DeviceController::OnPersistentStorageValue(const char * key, const char * value) {}
-
void DeviceController::OnPersistentStorageStatus(const char * key, Operation op, CHIP_ERROR err) {}
DeviceCommissioner::DeviceCommissioner()
void OnConnectionExpired(SecureSessionHandle session, SecureSessionMgr * mgr) override;
//////////// PersistentStorageResultDelegate Implementation ///////////////
- void OnPersistentStorageValue(const char * key, const char * value) override;
void OnPersistentStorageStatus(const char * key, Operation op, CHIP_ERROR err) override;
void ReleaseAllDevices();
#include "DeviceAddressUpdater.h"
#include <controller/CHIPDeviceController.h>
-#include <support/ReturnMacros.h>
namespace chip {
namespace Controller {
return env;
}
-AndroidDeviceControllerWrapper * AndroidDeviceControllerWrapper::AllocateNew(chip::NodeId nodeId, chip::System::Layer * systemLayer,
+AndroidDeviceControllerWrapper * AndroidDeviceControllerWrapper::AllocateNew(JavaVM * vm, jobject deviceControllerObj,
+ chip::NodeId nodeId, chip::System::Layer * systemLayer,
chip::Inet::InetLayer * inetLayer,
CHIP_ERROR * errInfoOnFailure)
{
}
std::unique_ptr<AndroidDeviceControllerWrapper> wrapper(new AndroidDeviceControllerWrapper(std::move(controller)));
+ wrapper->SetJavaObjectRef(vm, deviceControllerObj);
wrapper->Controller()->SetUdpListenPort(CHIP_PORT + 1);
*errInfoOnFailure = wrapper->Controller()->Init(nodeId, wrapper.get(), wrapper.get(), systemLayer, inetLayer);
mStorageResultDelegate = delegate;
}
-void AndroidDeviceControllerWrapper::AsyncGetKeyValue(const char * key)
-{
- jstring keyString = NULL;
- jstring valueString = NULL;
- const char * valueChars = nullptr;
- CHIP_ERROR err = CHIP_NO_ERROR;
- jclass storageCls = GetPersistentStorageClass();
- jmethodID method = GetJavaEnv()->GetStaticMethodID(storageCls, "getKeyValue", "(Ljava/lang/String;)Ljava/lang/String;");
-
- GetJavaEnv()->ExceptionClear();
-
- err = N2J_NewStringUTF(GetJavaEnv(), key, keyString);
- SuccessOrExit(err);
-
- valueString = (jstring) GetJavaEnv()->CallStaticObjectMethod(storageCls, method, keyString);
-
- if (mStorageResultDelegate)
- {
- valueChars = GetJavaEnv()->GetStringUTFChars(valueString, 0);
- mStorageResultDelegate->OnPersistentStorageValue(key, valueChars);
- }
-
-exit:
- GetJavaEnv()->ExceptionClear();
- if (valueChars != nullptr)
- {
- GetJavaEnv()->ReleaseStringUTFChars(valueString, valueChars);
- }
- GetJavaEnv()->DeleteLocalRef(keyString);
- GetJavaEnv()->DeleteLocalRef(valueString);
-}
-
CHIP_ERROR AndroidDeviceControllerWrapper::SyncGetKeyValue(const char * key, char * value, uint16_t & size)
{
jstring keyString = NULL;
// PersistentStorageDelegate implementation
void SetStorageDelegate(chip::PersistentStorageResultDelegate * delegate) override;
- void AsyncGetKeyValue(const char * key) override;
CHIP_ERROR SyncGetKeyValue(const char * key, char * value, uint16_t & size) override;
void AsyncSetKeyValue(const char * key, const char * value) override;
void AsyncDeleteKeyValue(const char * key) override;
return reinterpret_cast<AndroidDeviceControllerWrapper *>(handle);
}
- static AndroidDeviceControllerWrapper * AllocateNew(chip::NodeId nodeId, chip::System::Layer * systemLayer,
- chip::Inet::InetLayer * inetLayer, CHIP_ERROR * errInfoOnFailure);
+ static AndroidDeviceControllerWrapper * AllocateNew(JavaVM * vm, jobject deviceControllerObj, chip::NodeId nodeId,
+ chip::System::Layer * systemLayer, chip::Inet::InetLayer * inetLayer,
+ CHIP_ERROR * errInfoOnFailure);
private:
using ChipDeviceControllerPtr = std::unique_ptr<chip::Controller::DeviceCommissioner>;
#include <support/CHIPMem.h>
#include <support/CodeUtils.h>
#include <support/ErrorStr.h>
-#include <support/ReturnMacros.h>
#include <support/SafeInt.h>
#include <support/logging/CHIPLogging.h>
ChipLogProgress(Controller, "newDeviceController() called");
- wrapper = AndroidDeviceControllerWrapper::AllocateNew(kLocalDeviceId, &sSystemLayer, &sInetLayer, &err);
+ wrapper = AndroidDeviceControllerWrapper::AllocateNew(sJVM, self, kLocalDeviceId, &sSystemLayer, &sInetLayer, &err);
SuccessOrExit(err);
- wrapper->SetJavaObjectRef(sJVM, self);
result = wrapper->ToJNIHandle();
exit:
#include <app/CommandSender.h>
#include <app/InteractionModelEngine.h>
#include <lib/support/Span.h>
-#include <support/ReturnMacros.h>
#include <controller/CHIPClusters.h>
#include <controller/CHIPDevice.h>
}
// End of Cluster ColorControl
-// Cluster ContentLaunch
-CHIP_ERROR chip_ime_AppendCommand_ContentLaunch_LaunchContent(chip::Controller::Device * device, chip::EndpointId ZCLendpointId,
- chip::GroupId ZCLgroupId)
-{
- VerifyOrReturnError(device != nullptr, CHIP_ERROR_INVALID_ARGUMENT);
- chip::Controller::ContentLaunchCluster clusterContentLaunch;
- (void) ZCLgroupId;
- clusterContentLaunch.Associate(device, ZCLendpointId);
- return clusterContentLaunch.LaunchContent(nullptr, nullptr);
-}
-CHIP_ERROR chip_ime_AppendCommand_ContentLaunch_LaunchURL(chip::Controller::Device * device, chip::EndpointId ZCLendpointId,
- chip::GroupId ZCLgroupId)
-{
- VerifyOrReturnError(device != nullptr, CHIP_ERROR_INVALID_ARGUMENT);
- chip::Controller::ContentLaunchCluster clusterContentLaunch;
- (void) ZCLgroupId;
- clusterContentLaunch.Associate(device, ZCLendpointId);
- return clusterContentLaunch.LaunchURL(nullptr, nullptr);
-}
-// End of Cluster ContentLaunch
-
// Cluster DoorLock
CHIP_ERROR chip_ime_AppendCommand_DoorLock_ClearAllPins(chip::Controller::Device * device, chip::EndpointId ZCLendpointId,
chip::GroupId ZCLgroupId)
}
// End of Cluster LowPower
-// Cluster MediaPlayback
-CHIP_ERROR chip_ime_AppendCommand_MediaPlayback_FastForwardRequest(chip::Controller::Device * device,
- chip::EndpointId ZCLendpointId, chip::GroupId ZCLgroupId)
-{
- VerifyOrReturnError(device != nullptr, CHIP_ERROR_INVALID_ARGUMENT);
- chip::Controller::MediaPlaybackCluster clusterMediaPlayback;
- (void) ZCLgroupId;
- clusterMediaPlayback.Associate(device, ZCLendpointId);
- return clusterMediaPlayback.FastForwardRequest(nullptr, nullptr);
-}
-CHIP_ERROR chip_ime_AppendCommand_MediaPlayback_NextRequest(chip::Controller::Device * device, chip::EndpointId ZCLendpointId,
- chip::GroupId ZCLgroupId)
-{
- VerifyOrReturnError(device != nullptr, CHIP_ERROR_INVALID_ARGUMENT);
- chip::Controller::MediaPlaybackCluster clusterMediaPlayback;
- (void) ZCLgroupId;
- clusterMediaPlayback.Associate(device, ZCLendpointId);
- return clusterMediaPlayback.NextRequest(nullptr, nullptr);
-}
-CHIP_ERROR chip_ime_AppendCommand_MediaPlayback_PauseRequest(chip::Controller::Device * device, chip::EndpointId ZCLendpointId,
- chip::GroupId ZCLgroupId)
-{
- VerifyOrReturnError(device != nullptr, CHIP_ERROR_INVALID_ARGUMENT);
- chip::Controller::MediaPlaybackCluster clusterMediaPlayback;
- (void) ZCLgroupId;
- clusterMediaPlayback.Associate(device, ZCLendpointId);
- return clusterMediaPlayback.PauseRequest(nullptr, nullptr);
-}
-CHIP_ERROR chip_ime_AppendCommand_MediaPlayback_PlayRequest(chip::Controller::Device * device, chip::EndpointId ZCLendpointId,
- chip::GroupId ZCLgroupId)
-{
- VerifyOrReturnError(device != nullptr, CHIP_ERROR_INVALID_ARGUMENT);
- chip::Controller::MediaPlaybackCluster clusterMediaPlayback;
- (void) ZCLgroupId;
- clusterMediaPlayback.Associate(device, ZCLendpointId);
- return clusterMediaPlayback.PlayRequest(nullptr, nullptr);
-}
-CHIP_ERROR chip_ime_AppendCommand_MediaPlayback_PreviousRequest(chip::Controller::Device * device, chip::EndpointId ZCLendpointId,
- chip::GroupId ZCLgroupId)
-{
- VerifyOrReturnError(device != nullptr, CHIP_ERROR_INVALID_ARGUMENT);
- chip::Controller::MediaPlaybackCluster clusterMediaPlayback;
- (void) ZCLgroupId;
- clusterMediaPlayback.Associate(device, ZCLendpointId);
- return clusterMediaPlayback.PreviousRequest(nullptr, nullptr);
-}
-CHIP_ERROR chip_ime_AppendCommand_MediaPlayback_RewindRequest(chip::Controller::Device * device, chip::EndpointId ZCLendpointId,
- chip::GroupId ZCLgroupId)
-{
- VerifyOrReturnError(device != nullptr, CHIP_ERROR_INVALID_ARGUMENT);
- chip::Controller::MediaPlaybackCluster clusterMediaPlayback;
- (void) ZCLgroupId;
- clusterMediaPlayback.Associate(device, ZCLendpointId);
- return clusterMediaPlayback.RewindRequest(nullptr, nullptr);
-}
-CHIP_ERROR chip_ime_AppendCommand_MediaPlayback_SkipBackwardRequest(chip::Controller::Device * device,
- chip::EndpointId ZCLendpointId, chip::GroupId ZCLgroupId)
-{
- VerifyOrReturnError(device != nullptr, CHIP_ERROR_INVALID_ARGUMENT);
- chip::Controller::MediaPlaybackCluster clusterMediaPlayback;
- (void) ZCLgroupId;
- clusterMediaPlayback.Associate(device, ZCLendpointId);
- return clusterMediaPlayback.SkipBackwardRequest(nullptr, nullptr);
-}
-CHIP_ERROR chip_ime_AppendCommand_MediaPlayback_SkipForwardRequest(chip::Controller::Device * device,
- chip::EndpointId ZCLendpointId, chip::GroupId ZCLgroupId)
-{
- VerifyOrReturnError(device != nullptr, CHIP_ERROR_INVALID_ARGUMENT);
- chip::Controller::MediaPlaybackCluster clusterMediaPlayback;
- (void) ZCLgroupId;
- clusterMediaPlayback.Associate(device, ZCLendpointId);
- return clusterMediaPlayback.SkipForwardRequest(nullptr, nullptr);
-}
-CHIP_ERROR chip_ime_AppendCommand_MediaPlayback_StartOverRequest(chip::Controller::Device * device, chip::EndpointId ZCLendpointId,
- chip::GroupId ZCLgroupId)
-{
- VerifyOrReturnError(device != nullptr, CHIP_ERROR_INVALID_ARGUMENT);
- chip::Controller::MediaPlaybackCluster clusterMediaPlayback;
- (void) ZCLgroupId;
- clusterMediaPlayback.Associate(device, ZCLendpointId);
- return clusterMediaPlayback.StartOverRequest(nullptr, nullptr);
-}
-CHIP_ERROR chip_ime_AppendCommand_MediaPlayback_StopRequest(chip::Controller::Device * device, chip::EndpointId ZCLendpointId,
- chip::GroupId ZCLgroupId)
-{
- VerifyOrReturnError(device != nullptr, CHIP_ERROR_INVALID_ARGUMENT);
- chip::Controller::MediaPlaybackCluster clusterMediaPlayback;
- (void) ZCLgroupId;
- clusterMediaPlayback.Associate(device, ZCLendpointId);
- return clusterMediaPlayback.StopRequest(nullptr, nullptr);
-}
-// End of Cluster MediaPlayback
-
// Cluster NetworkCommissioning
CHIP_ERROR chip_ime_AppendCommand_NetworkCommissioning_AddThreadNetwork(chip::Controller::Device * device,
chip::EndpointId ZCLendpointId, chip::GroupId ZCLgroupId,
#include <support/CHIPMem.h>
#include <support/CodeUtils.h>
#include <support/DLLUtil.h>
-#include <support/ReturnMacros.h>
#include <support/logging/CHIPLogging.h>
using namespace chip;
mDelegate = delegate;
}
-void PythonPersistentStorageDelegate::AsyncGetKeyValue(const char * key)
-{
- auto val = mStorage.find(key);
- if (val == mStorage.end())
- {
- mDelegate->OnPersistentStorageStatus(key, PersistentStorageResultDelegate::Operation::kGET, CHIP_ERROR_KEY_NOT_FOUND);
- return;
- }
-
- mDelegate->OnPersistentStorageValue(key, val->second.c_str());
-}
-
CHIP_ERROR PythonPersistentStorageDelegate::SyncGetKeyValue(const char * key, char * value, uint16_t & size)
{
auto val = mStorage.find(key);
public:
PythonPersistentStorageDelegate() {}
void SetStorageDelegate(PersistentStorageResultDelegate * delegate) override;
- void AsyncGetKeyValue(const char * key) override;
CHIP_ERROR SyncGetKeyValue(const char * key, char * value, uint16_t & size) override;
void AsyncSetKeyValue(const char * key, const char * value) override;
void AsyncDeleteKeyValue(const char * key) override;
## Thread provisioning
1. Configure Thread border router. For example, follow
- [Configuring Thread network on a Linux machine](../../../docs/guides/linux_thread_connectivity.md)
+ [Setup OpenThread Border Router on Raspberry Pi / ubuntu](../../../docs/guides/openthread_border_router_pi.md)
instruction to configure OpenThread Border Router on a Linux workstation.
2. Run CHIP Device Controller
"optionsOverride": "int",
},
},
- "ContentLaunch": {
- "LaunchContent": {
- },
- "LaunchURL": {
- },
- },
"DoorLock": {
"ClearAllPins": {
},
"Sleep": {
},
},
- "MediaPlayback": {
- "FastForwardRequest": {
- },
- "NextRequest": {
- },
- "PauseRequest": {
- },
- "PlayRequest": {
- },
- "PreviousRequest": {
- },
- "RewindRequest": {
- },
- "SkipBackwardRequest": {
- },
- "SkipForwardRequest": {
- },
- "StartOverRequest": {
- },
- "StopRequest": {
- },
- },
"NetworkCommissioning": {
"AddThreadNetwork": {
"operationalDataset": "bytes",
)
)
- def ClusterContentLaunch_CommandLaunchContent(self, device: ctypes.c_void_p, ZCLendpoint: int, ZCLgroupid: int):
- self._ChipStack.Call(
- lambda: self._chipLib.chip_ime_AppendCommand_ContentLaunch_LaunchContent(
- device, ZCLendpoint, ZCLgroupid
- )
- )
-
- def ClusterContentLaunch_CommandLaunchURL(self, device: ctypes.c_void_p, ZCLendpoint: int, ZCLgroupid: int):
- self._ChipStack.Call(
- lambda: self._chipLib.chip_ime_AppendCommand_ContentLaunch_LaunchURL(
- device, ZCLendpoint, ZCLgroupid
- )
- )
-
def ClusterDoorLock_CommandClearAllPins(self, device: ctypes.c_void_p, ZCLendpoint: int, ZCLgroupid: int):
self._ChipStack.Call(
lambda: self._chipLib.chip_ime_AppendCommand_DoorLock_ClearAllPins(
)
)
- def ClusterMediaPlayback_CommandFastForwardRequest(self, device: ctypes.c_void_p, ZCLendpoint: int, ZCLgroupid: int):
- self._ChipStack.Call(
- lambda: self._chipLib.chip_ime_AppendCommand_MediaPlayback_FastForwardRequest(
- device, ZCLendpoint, ZCLgroupid
- )
- )
-
- def ClusterMediaPlayback_CommandNextRequest(self, device: ctypes.c_void_p, ZCLendpoint: int, ZCLgroupid: int):
- self._ChipStack.Call(
- lambda: self._chipLib.chip_ime_AppendCommand_MediaPlayback_NextRequest(
- device, ZCLendpoint, ZCLgroupid
- )
- )
-
- def ClusterMediaPlayback_CommandPauseRequest(self, device: ctypes.c_void_p, ZCLendpoint: int, ZCLgroupid: int):
- self._ChipStack.Call(
- lambda: self._chipLib.chip_ime_AppendCommand_MediaPlayback_PauseRequest(
- device, ZCLendpoint, ZCLgroupid
- )
- )
-
- def ClusterMediaPlayback_CommandPlayRequest(self, device: ctypes.c_void_p, ZCLendpoint: int, ZCLgroupid: int):
- self._ChipStack.Call(
- lambda: self._chipLib.chip_ime_AppendCommand_MediaPlayback_PlayRequest(
- device, ZCLendpoint, ZCLgroupid
- )
- )
-
- def ClusterMediaPlayback_CommandPreviousRequest(self, device: ctypes.c_void_p, ZCLendpoint: int, ZCLgroupid: int):
- self._ChipStack.Call(
- lambda: self._chipLib.chip_ime_AppendCommand_MediaPlayback_PreviousRequest(
- device, ZCLendpoint, ZCLgroupid
- )
- )
-
- def ClusterMediaPlayback_CommandRewindRequest(self, device: ctypes.c_void_p, ZCLendpoint: int, ZCLgroupid: int):
- self._ChipStack.Call(
- lambda: self._chipLib.chip_ime_AppendCommand_MediaPlayback_RewindRequest(
- device, ZCLendpoint, ZCLgroupid
- )
- )
-
- def ClusterMediaPlayback_CommandSkipBackwardRequest(self, device: ctypes.c_void_p, ZCLendpoint: int, ZCLgroupid: int):
- self._ChipStack.Call(
- lambda: self._chipLib.chip_ime_AppendCommand_MediaPlayback_SkipBackwardRequest(
- device, ZCLendpoint, ZCLgroupid
- )
- )
-
- def ClusterMediaPlayback_CommandSkipForwardRequest(self, device: ctypes.c_void_p, ZCLendpoint: int, ZCLgroupid: int):
- self._ChipStack.Call(
- lambda: self._chipLib.chip_ime_AppendCommand_MediaPlayback_SkipForwardRequest(
- device, ZCLendpoint, ZCLgroupid
- )
- )
-
- def ClusterMediaPlayback_CommandStartOverRequest(self, device: ctypes.c_void_p, ZCLendpoint: int, ZCLgroupid: int):
- self._ChipStack.Call(
- lambda: self._chipLib.chip_ime_AppendCommand_MediaPlayback_StartOverRequest(
- device, ZCLendpoint, ZCLgroupid
- )
- )
-
- def ClusterMediaPlayback_CommandStopRequest(self, device: ctypes.c_void_p, ZCLendpoint: int, ZCLgroupid: int):
- self._ChipStack.Call(
- lambda: self._chipLib.chip_ime_AppendCommand_MediaPlayback_StopRequest(
- device, ZCLendpoint, ZCLgroupid
- )
- )
-
def ClusterNetworkCommissioning_CommandAddThreadNetwork(self, device: ctypes.c_void_p, ZCLendpoint: int, ZCLgroupid: int, operationalDataset: bytes, breadcrumb: int, timeoutMs: int):
self._ChipStack.Call(
lambda: self._chipLib.chip_ime_AppendCommand_NetworkCommissioning_AddThreadNetwork(
# Cluster ColorControl Command StopMoveStep
self._chipLib.chip_ime_AppendCommand_ColorControl_StopMoveStep.argtypes = [ctypes.c_void_p, ctypes.c_uint8, ctypes.c_uint16, ctypes.c_uint8, ctypes.c_uint8]
self._chipLib.chip_ime_AppendCommand_ColorControl_StopMoveStep.restype = ctypes.c_uint32
- # Cluster ContentLaunch
- # Cluster ContentLaunch Command LaunchContent
- self._chipLib.chip_ime_AppendCommand_ContentLaunch_LaunchContent.argtypes = [ctypes.c_void_p, ctypes.c_uint8, ctypes.c_uint16]
- self._chipLib.chip_ime_AppendCommand_ContentLaunch_LaunchContent.restype = ctypes.c_uint32
- # Cluster ContentLaunch Command LaunchURL
- self._chipLib.chip_ime_AppendCommand_ContentLaunch_LaunchURL.argtypes = [ctypes.c_void_p, ctypes.c_uint8, ctypes.c_uint16]
- self._chipLib.chip_ime_AppendCommand_ContentLaunch_LaunchURL.restype = ctypes.c_uint32
# Cluster DoorLock
# Cluster DoorLock Command ClearAllPins
self._chipLib.chip_ime_AppendCommand_DoorLock_ClearAllPins.argtypes = [ctypes.c_void_p, ctypes.c_uint8, ctypes.c_uint16]
# Cluster LowPower Command Sleep
self._chipLib.chip_ime_AppendCommand_LowPower_Sleep.argtypes = [ctypes.c_void_p, ctypes.c_uint8, ctypes.c_uint16]
self._chipLib.chip_ime_AppendCommand_LowPower_Sleep.restype = ctypes.c_uint32
- # Cluster MediaPlayback
- # Cluster MediaPlayback Command FastForwardRequest
- self._chipLib.chip_ime_AppendCommand_MediaPlayback_FastForwardRequest.argtypes = [ctypes.c_void_p, ctypes.c_uint8, ctypes.c_uint16]
- self._chipLib.chip_ime_AppendCommand_MediaPlayback_FastForwardRequest.restype = ctypes.c_uint32
- # Cluster MediaPlayback Command NextRequest
- self._chipLib.chip_ime_AppendCommand_MediaPlayback_NextRequest.argtypes = [ctypes.c_void_p, ctypes.c_uint8, ctypes.c_uint16]
- self._chipLib.chip_ime_AppendCommand_MediaPlayback_NextRequest.restype = ctypes.c_uint32
- # Cluster MediaPlayback Command PauseRequest
- self._chipLib.chip_ime_AppendCommand_MediaPlayback_PauseRequest.argtypes = [ctypes.c_void_p, ctypes.c_uint8, ctypes.c_uint16]
- self._chipLib.chip_ime_AppendCommand_MediaPlayback_PauseRequest.restype = ctypes.c_uint32
- # Cluster MediaPlayback Command PlayRequest
- self._chipLib.chip_ime_AppendCommand_MediaPlayback_PlayRequest.argtypes = [ctypes.c_void_p, ctypes.c_uint8, ctypes.c_uint16]
- self._chipLib.chip_ime_AppendCommand_MediaPlayback_PlayRequest.restype = ctypes.c_uint32
- # Cluster MediaPlayback Command PreviousRequest
- self._chipLib.chip_ime_AppendCommand_MediaPlayback_PreviousRequest.argtypes = [ctypes.c_void_p, ctypes.c_uint8, ctypes.c_uint16]
- self._chipLib.chip_ime_AppendCommand_MediaPlayback_PreviousRequest.restype = ctypes.c_uint32
- # Cluster MediaPlayback Command RewindRequest
- self._chipLib.chip_ime_AppendCommand_MediaPlayback_RewindRequest.argtypes = [ctypes.c_void_p, ctypes.c_uint8, ctypes.c_uint16]
- self._chipLib.chip_ime_AppendCommand_MediaPlayback_RewindRequest.restype = ctypes.c_uint32
- # Cluster MediaPlayback Command SkipBackwardRequest
- self._chipLib.chip_ime_AppendCommand_MediaPlayback_SkipBackwardRequest.argtypes = [ctypes.c_void_p, ctypes.c_uint8, ctypes.c_uint16]
- self._chipLib.chip_ime_AppendCommand_MediaPlayback_SkipBackwardRequest.restype = ctypes.c_uint32
- # Cluster MediaPlayback Command SkipForwardRequest
- self._chipLib.chip_ime_AppendCommand_MediaPlayback_SkipForwardRequest.argtypes = [ctypes.c_void_p, ctypes.c_uint8, ctypes.c_uint16]
- self._chipLib.chip_ime_AppendCommand_MediaPlayback_SkipForwardRequest.restype = ctypes.c_uint32
- # Cluster MediaPlayback Command StartOverRequest
- self._chipLib.chip_ime_AppendCommand_MediaPlayback_StartOverRequest.argtypes = [ctypes.c_void_p, ctypes.c_uint8, ctypes.c_uint16]
- self._chipLib.chip_ime_AppendCommand_MediaPlayback_StartOverRequest.restype = ctypes.c_uint32
- # Cluster MediaPlayback Command StopRequest
- self._chipLib.chip_ime_AppendCommand_MediaPlayback_StopRequest.argtypes = [ctypes.c_void_p, ctypes.c_uint8, ctypes.c_uint16]
- self._chipLib.chip_ime_AppendCommand_MediaPlayback_StopRequest.restype = ctypes.c_uint32
# Cluster NetworkCommissioning
# Cluster NetworkCommissioning Command AddThreadNetwork
self._chipLib.chip_ime_AppendCommand_NetworkCommissioning_AddThreadNetwork.argtypes = [ctypes.c_void_p, ctypes.c_uint8, ctypes.c_uint16, ctypes.c_char_p, ctypes.c_uint32, ctypes.c_uint64, ctypes.c_uint32]
#include <platform/Linux/bluez/MainLoop.h>
#include <platform/internal/BLEManager.h>
#include <support/CHIPMem.h>
-#include <support/ReturnMacros.h>
using namespace chip::DeviceLayer::Internal;
#include <support/CHIPMem.h>
-#include <support/ReturnMacros.h>
#include <support/logging/CHIPLogging.h>
#import <CoreBluetooth/CoreBluetooth.h>
#include <ble/CHIPBleServiceData.h>
#include <platform/Darwin/UUIDHelper.h>
#include <support/CHIPMem.h>
-#include <support/ReturnMacros.h>
#include <support/logging/CHIPLogging.h>
#import <CoreBluetooth/CoreBluetooth.h>
public:
void SetStorageDelegate(chip::PersistentStorageResultDelegate * delegate) override { mAsyncDelegate = delegate; }
- void AsyncGetKeyValue(const char * key) override
- {
- // TODO: Async Get/Set are implemented synchronously here.
- // We need to figure out a standard way to implement this - this implementation
- // was based on an example that just returned and that seemed even less useful.
- uint8_t buffer[kMaxKeyValueSize];
- uint16_t bufferSize = sizeof(buffer) - 1;
- CHIP_ERROR err = SyncGetKeyValue(key, buffer, bufferSize);
-
- if (err == CHIP_NO_ERROR)
- {
- buffer[bufferSize] = 0;
- mAsyncDelegate->OnPersistentStorageValue(key, reinterpret_cast<const char *>(buffer));
- }
- else
- {
- mAsyncDelegate->OnPersistentStorageStatus(key, chip::PersistentStorageResultDelegate::Operation::kGET, err);
- }
- }
-
void AsyncSetKeyValue(const char * key, const char * value) override
{
void AsyncDeleteKeyValue(const char * key) override { chip::DeviceLayer::PersistedStorage::KeyValueStoreMgr().Delete(key); }
private:
- static constexpr size_t kMaxKeyValueSize = 1024;
-
chip::PersistentStorageResultDelegate * mAsyncDelegate = nullptr;
};
TLVReader reader;
reader.Init(chipCert, chipCertLen);
- reader.ImplicitProfileId = kProtocol_OpCredentials;
+ reader.ImplicitProfileId = Protocols::OpCredentials::Id.ToTLVProfileId();
- err = reader.Next(kTLVType_Structure, ProfileTag(kProtocol_OpCredentials, kTag_ChipCertificate));
+ err = reader.Next(kTLVType_Structure, ProfileTag(Protocols::OpCredentials::Id.ToTLVProfileId(), kTag_ChipCertificate));
SuccessOrExit(err);
err = LoadCert(reader, decodeFlags);
uint64_t tag;
reader.Init(chipCerts, chipCertsLen);
- reader.ImplicitProfileId = kProtocol_OpCredentials;
+ reader.ImplicitProfileId = Protocols::OpCredentials::Id.ToTLVProfileId();
err = reader.Next();
SuccessOrExit(err);
type = reader.GetType();
tag = reader.GetTag();
- VerifyOrExit((type == kTLVType_Structure && tag == ProfileTag(kProtocol_OpCredentials, kTag_ChipCertificate)) ||
- (type == kTLVType_Array && tag == ProfileTag(kProtocol_OpCredentials, kTag_ChipCertificateArray)),
- err = CHIP_ERROR_UNEXPECTED_TLV_ELEMENT);
+ VerifyOrExit(
+ (type == kTLVType_Structure && tag == ProfileTag(Protocols::OpCredentials::Id.ToTLVProfileId(), kTag_ChipCertificate)) ||
+ (type == kTLVType_Array && tag == ProfileTag(Protocols::OpCredentials::Id.ToTLVProfileId(), kTag_ChipCertificateArray)),
+ err = CHIP_ERROR_UNEXPECTED_TLV_ELEMENT);
err = LoadCerts(reader, decodeFlags);
OID sigAlgoOID;
TLVType containerType;
- err = writer.StartContainer(ProfileTag(kProtocol_OpCredentials, kTag_ChipCertificate), kTLVType_Structure, containerType);
+ err = writer.StartContainer(ProfileTag(Protocols::OpCredentials::Id.ToTLVProfileId(), kTag_ChipCertificate), kTLVType_Structure,
+ containerType);
SuccessOrExit(err);
// Certificate ::= SEQUENCE
}
VerifyOrExit(reader.GetType() == kTLVType_Structure, err = CHIP_ERROR_WRONG_TLV_TYPE);
tag = reader.GetTag();
- VerifyOrExit(tag == ProfileTag(kProtocol_OpCredentials, kTag_ChipCertificate) || tag == AnonymousTag,
+ VerifyOrExit(tag == ProfileTag(Protocols::OpCredentials::Id.ToTLVProfileId(), kTag_ChipCertificate) || tag == AnonymousTag,
err = CHIP_ERROR_UNEXPECTED_TLV_ELEMENT);
err = reader.EnterContainer(containerType);
typedef int32_t CHIP_ERROR;
typedef NS_ERROR_ENUM(CHIPErrorDomain, CHIPErrorCode) {
- CHIPErrorCodeUndefinedError = 0,
- CHIPErrorCodeInvalidStringLength = 1,
- CHIPErrorCodeInvalidIntegerValue = 2,
- CHIPErrorCodeInvalidArgument = 3,
- CHIPErrorCodeInvalidMessageLength = 4,
- CHIPErrorCodeInvalidState = 5,
- CHIPErrorCodeWrongAddressType = 6,
- CHIPErrorCodeIntegrityCheckFailed = 7,
- CHIPSuccess = 8,
+ CHIPSuccess = 0,
+ CHIPErrorCodeUndefinedError = 1,
+ CHIPErrorCodeInvalidStringLength = 2,
+ CHIPErrorCodeInvalidIntegerValue = 3,
+ CHIPErrorCodeInvalidArgument = 4,
+ CHIPErrorCodeInvalidMessageLength = 5,
+ CHIPErrorCodeInvalidState = 6,
+ CHIPErrorCodeWrongAddressType = 7,
+ CHIPErrorCodeIntegrityCheckFailed = 8,
+ CHIPErrorCodeDuplicateExists = 9,
};
@interface CHIPError : NSObject
#import "CHIPError.h"
+#import <app/util/af-enums.h>
#import <core/CHIPError.h>
#import <inet/InetError.h>
return [NSError errorWithDomain:CHIPErrorDomain
code:CHIPErrorCodeIntegrityCheckFailed
userInfo:@{ NSLocalizedDescriptionKey : NSLocalizedString(@"Integrity check failed.", nil) }];
+ case EMBER_ZCL_STATUS_DUPLICATE_EXISTS:
+ return [NSError
+ errorWithDomain:CHIPErrorDomain
+ code:CHIPErrorCodeDuplicateExists
+ userInfo:@{ NSLocalizedDescriptionKey : NSLocalizedString(@"A Duplicate entry or setting exists.", nil) }];
case CHIP_NO_ERROR:
return [NSError errorWithDomain:CHIPErrorDomain
code:CHIPSuccess
default:
return [NSError errorWithDomain:CHIPErrorDomain
code:CHIPErrorCodeUndefinedError
- userInfo:@{ NSLocalizedDescriptionKey : NSLocalizedString(@"Undefined error.", nil) }];
+ userInfo:@{
+ NSLocalizedDescriptionKey :
+ [NSString stringWithFormat:NSLocalizedString(@"Undefined error:%d.", nil), errorCode]
+ }];
;
}
}
}
switch (error.code) {
+ case CHIPErrorCodeDuplicateExists:
+ return EMBER_ZCL_STATUS_DUPLICATE_EXISTS;
case CHIPErrorCodeInvalidStringLength:
return CHIP_ERROR_INVALID_STRING_LENGTH;
case CHIPErrorCodeInvalidIntegerValue:
void SetStorageDelegate(chip::PersistentStorageResultDelegate * delegate) override;
- void AsyncGetKeyValue(const char * key) override;
-
CHIP_ERROR SyncGetKeyValue(const char * key, char * value, uint16_t & size) override;
void AsyncSetKeyValue(const char * key, const char * value) override;
dispatch_queue_t mQueue;
chip::PersistentStorageResultDelegate * mCallback;
- SendKeyValue mCompletionHandler;
CHIPSendSetStatus mSetStatusHandler;
CHIPSendDeleteStatus mDeleteStatusHandler;
NSUserDefaults * mDefaultPersistentStorage;
if (delegate) {
mCallback = delegate;
- mCompletionHandler = ^(NSString * key, NSString * value) {
- chip::PersistentStorageResultDelegate * callback = mCallback;
- if (callback) {
- dispatch_async(mWorkQueue, ^{
- callback->OnPersistentStorageValue([key UTF8String], [value UTF8String]);
- });
- }
- };
-
mSetStatusHandler = ^(NSString * key, NSError * status) {
chip::PersistentStorageResultDelegate * callback = mCallback;
if (callback) {
};
} else {
mCallback = nil;
- mCompletionHandler = nil;
mSetStatusHandler = nil;
mDeleteStatusHandler = nil;
}
});
}
-void CHIPPersistentStorageDelegateBridge::AsyncGetKeyValue(const char * key)
-{
- NSString * keyString = [NSString stringWithUTF8String:key];
- dispatch_async(mWorkQueue, ^{
- NSLog(@"PersistentStorageDelegate Get Value for Key: %@", keyString);
-
- id<CHIPPersistentStorageDelegate> strongDelegate = mDelegate;
- if (strongDelegate && mQueue) {
- dispatch_async(mQueue, ^{
- [strongDelegate CHIPGetKeyValue:keyString handler:mCompletionHandler];
- });
- } else {
- NSString * value = [mDefaultPersistentStorage objectForKey:keyString];
- NSLog(@"PersistentStorageDelegate Get Value for Key: %@, value %@", keyString, value);
- if (mCompletionHandler) {
- mCompletionHandler(keyString, value);
- }
- }
- });
-}
-
CHIP_ERROR CHIPPersistentStorageDelegateBridge::SyncGetKeyValue(const char * key, char * value, uint16_t & size)
{
__block CHIP_ERROR error = CHIP_NO_ERROR;
return true;
}
-bool emberAfContentLaunchClusterLaunchContentResponseCallback(uint8_t contentLaunchStatus)
-{
- ChipLogProgress(Zcl, "LaunchContentResponse:");
- ChipLogProgress(Zcl, " contentLaunchStatus: %" PRIu8 "", contentLaunchStatus);
-
- GET_RESPONSE_CALLBACKS("ContentLaunchClusterLaunchContentResponseCallback");
-
- Callback::Callback<ContentLaunchClusterLaunchContentResponseCallback> * cb =
- Callback::Callback<ContentLaunchClusterLaunchContentResponseCallback>::FromCancelable(onSuccessCallback);
- cb->mCall(cb->mContext, contentLaunchStatus);
- return true;
-}
-
-bool emberAfContentLaunchClusterLaunchURLResponseCallback(uint8_t contentLaunchStatus)
-{
- ChipLogProgress(Zcl, "LaunchURLResponse:");
- ChipLogProgress(Zcl, " contentLaunchStatus: %" PRIu8 "", contentLaunchStatus);
-
- GET_RESPONSE_CALLBACKS("ContentLaunchClusterLaunchURLResponseCallback");
-
- Callback::Callback<ContentLaunchClusterLaunchURLResponseCallback> * cb =
- Callback::Callback<ContentLaunchClusterLaunchURLResponseCallback>::FromCancelable(onSuccessCallback);
- cb->mCall(cb->mContext, contentLaunchStatus);
- return true;
-}
-
bool emberAfDoorLockClusterClearAllPinsResponseCallback(uint8_t status)
{
ChipLogProgress(Zcl, "ClearAllPinsResponse:");
typedef void (*ReadReportingConfigurationReceivedCallback)(void * context, uint16_t timeout);
// Cluster Specific Response Callbacks
-typedef void (*ContentLaunchClusterLaunchContentResponseCallback)(void * context, uint8_t contentLaunchStatus);
-typedef void (*ContentLaunchClusterLaunchURLResponseCallback)(void * context, uint8_t contentLaunchStatus);
typedef void (*DoorLockClusterClearAllPinsResponseCallback)(void * context);
typedef void (*DoorLockClusterClearAllRfidsResponseCallback)(void * context);
typedef void (*DoorLockClusterClearHolidayScheduleResponseCallback)(void * context);
typedef void (*GroupsClusterRemoveGroupResponseCallback)(void * context, uint16_t groupId);
typedef void (*GroupsClusterViewGroupResponseCallback)(void * context, uint16_t groupId, uint8_t * groupName);
typedef void (*IdentifyClusterIdentifyQueryResponseCallback)(void * context, uint16_t timeout);
-typedef void (*MediaPlaybackClusterPlaybackCallback)(void * context);
typedef void (*ScenesClusterAddSceneResponseCallback)(void * context, uint16_t groupId, uint8_t sceneId);
typedef void (*ScenesClusterGetSceneMembershipResponseCallback)(void * context, uint8_t capacity, uint16_t groupId,
uint8_t sceneCount,
@end
/**
- * Cluster Content Launch
- *
- */
-@interface CHIPContentLaunch : CHIPCluster
-
-- (void)launchContent:(ResponseHandler)completionHandler;
-- (void)launchURL:(ResponseHandler)completionHandler;
-
-- (void)readAttributeClusterRevision:(ResponseHandler)completionHandler;
-
-@end
-
-/**
* Cluster Door Lock
*
*/
@end
/**
- * Cluster Media Playback
- *
- */
-@interface CHIPMediaPlayback : CHIPCluster
-
-- (void)fastForwardRequest:(ResponseHandler)completionHandler;
-- (void)nextRequest:(ResponseHandler)completionHandler;
-- (void)pauseRequest:(ResponseHandler)completionHandler;
-- (void)playRequest:(ResponseHandler)completionHandler;
-- (void)previousRequest:(ResponseHandler)completionHandler;
-- (void)rewindRequest:(ResponseHandler)completionHandler;
-- (void)skipBackwardRequest:(ResponseHandler)completionHandler;
-- (void)skipForwardRequest:(ResponseHandler)completionHandler;
-- (void)startOverRequest:(ResponseHandler)completionHandler;
-- (void)stopRequest:(ResponseHandler)completionHandler;
-
-- (void)readAttributeCurrentState:(ResponseHandler)completionHandler;
-- (void)readAttributeClusterRevision:(ResponseHandler)completionHandler;
-
-@end
-
-/**
* Cluster On/off
*
*/
CHIPDefaultFailureCallbackBridge * callback = reinterpret_cast<CHIPDefaultFailureCallbackBridge *>(context);
if (callback && callback->mQueue) {
dispatch_async(callback->mQueue, ^{
- NSError * error = [NSError errorWithDomain:CHIPErrorDomain
- code:status
- userInfo:@ { NSLocalizedDescriptionKey : @"" }];
+ NSError * error = [CHIPError errorForCHIPErrorCode:status];
callback->mHandler(error, nil);
callback->Cancel();
delete callback;
bool mKeepAlive;
};
-class CHIPContentLaunchClusterLaunchContentResponseCallbackBridge
- : public Callback::Callback<ContentLaunchClusterLaunchContentResponseCallback> {
-public:
- CHIPContentLaunchClusterLaunchContentResponseCallbackBridge(ResponseHandler handler, dispatch_queue_t queue)
- : Callback::Callback<ContentLaunchClusterLaunchContentResponseCallback>(CallbackFn, this)
- , mHandler(handler)
- , mQueue(queue)
- {
- }
-
- ~CHIPContentLaunchClusterLaunchContentResponseCallbackBridge() {};
-
- static void CallbackFn(void * context, uint8_t contentLaunchStatus)
- {
- CHIPContentLaunchClusterLaunchContentResponseCallbackBridge * callback
- = reinterpret_cast<CHIPContentLaunchClusterLaunchContentResponseCallbackBridge *>(context);
- if (callback && callback->mQueue) {
- dispatch_async(callback->mQueue, ^{
- callback->mHandler(nil, @ {
- @"contentLaunchStatus" : [NSNumber numberWithUnsignedChar:contentLaunchStatus],
- });
- callback->Cancel();
- delete callback;
- });
- }
- };
-
-private:
- ResponseHandler mHandler;
- dispatch_queue_t mQueue;
-};
-
-class CHIPContentLaunchClusterLaunchURLResponseCallbackBridge
- : public Callback::Callback<ContentLaunchClusterLaunchURLResponseCallback> {
-public:
- CHIPContentLaunchClusterLaunchURLResponseCallbackBridge(ResponseHandler handler, dispatch_queue_t queue)
- : Callback::Callback<ContentLaunchClusterLaunchURLResponseCallback>(CallbackFn, this)
- , mHandler(handler)
- , mQueue(queue)
- {
- }
-
- ~CHIPContentLaunchClusterLaunchURLResponseCallbackBridge() {};
-
- static void CallbackFn(void * context, uint8_t contentLaunchStatus)
- {
- CHIPContentLaunchClusterLaunchURLResponseCallbackBridge * callback
- = reinterpret_cast<CHIPContentLaunchClusterLaunchURLResponseCallbackBridge *>(context);
- if (callback && callback->mQueue) {
- dispatch_async(callback->mQueue, ^{
- callback->mHandler(nil, @ {
- @"contentLaunchStatus" : [NSNumber numberWithUnsignedChar:contentLaunchStatus],
- });
- callback->Cancel();
- delete callback;
- });
- }
- };
-
-private:
- ResponseHandler mHandler;
- dispatch_queue_t mQueue;
-};
-
class CHIPDoorLockClusterClearAllPinsResponseCallbackBridge
: public Callback::Callback<DoorLockClusterClearAllPinsResponseCallback> {
public:
dispatch_queue_t mQueue;
};
-class CHIPMediaPlaybackClusterPlaybackCallbackBridge : public Callback::Callback<MediaPlaybackClusterPlaybackCallback> {
-public:
- CHIPMediaPlaybackClusterPlaybackCallbackBridge(ResponseHandler handler, dispatch_queue_t queue)
- : Callback::Callback<MediaPlaybackClusterPlaybackCallback>(CallbackFn, this)
- , mHandler(handler)
- , mQueue(queue)
- {
- }
-
- ~CHIPMediaPlaybackClusterPlaybackCallbackBridge() {};
-
- static void CallbackFn(void * context)
- {
- CHIPMediaPlaybackClusterPlaybackCallbackBridge * callback
- = reinterpret_cast<CHIPMediaPlaybackClusterPlaybackCallbackBridge *>(context);
- if (callback && callback->mQueue) {
- dispatch_async(callback->mQueue, ^{
- callback->mHandler(nil, @ {});
- callback->Cancel();
- delete callback;
- });
- }
- };
-
-private:
- ResponseHandler mHandler;
- dispatch_queue_t mQueue;
-};
-
class CHIPScenesClusterAddSceneResponseCallbackBridge : public Callback::Callback<ScenesClusterAddSceneResponseCallback> {
public:
CHIPScenesClusterAddSceneResponseCallbackBridge(ResponseHandler handler, dispatch_queue_t queue)
@end
-@interface CHIPContentLaunch ()
-@property (readonly) Controller::ContentLaunchCluster cppCluster;
-@end
-
-@implementation CHIPContentLaunch
-
-- (Controller::ClusterBase *)getCluster
-{
- return &_cppCluster;
-}
-
-- (void)launchContent:(ResponseHandler)completionHandler
-{
- CHIPContentLaunchClusterLaunchContentResponseCallbackBridge * onSuccess
- = new CHIPContentLaunchClusterLaunchContentResponseCallbackBridge(completionHandler, [self callbackQueue]);
- if (!onSuccess) {
- completionHandler([CHIPError errorForCHIPErrorCode:CHIP_ERROR_INCORRECT_STATE], nil);
- return;
- }
-
- CHIPDefaultFailureCallbackBridge * onFailure = new CHIPDefaultFailureCallbackBridge(completionHandler, [self callbackQueue]);
- if (!onFailure) {
- delete onSuccess;
- completionHandler([CHIPError errorForCHIPErrorCode:CHIP_ERROR_INCORRECT_STATE], nil);
- return;
- }
-
- CHIP_ERROR err = self.cppCluster.LaunchContent(onSuccess->Cancel(), onFailure->Cancel());
- if (err != CHIP_NO_ERROR) {
- delete onSuccess;
- delete onFailure;
- completionHandler([CHIPError errorForCHIPErrorCode:err], nil);
- }
-}
-- (void)launchURL:(ResponseHandler)completionHandler
-{
- CHIPContentLaunchClusterLaunchURLResponseCallbackBridge * onSuccess
- = new CHIPContentLaunchClusterLaunchURLResponseCallbackBridge(completionHandler, [self callbackQueue]);
- if (!onSuccess) {
- completionHandler([CHIPError errorForCHIPErrorCode:CHIP_ERROR_INCORRECT_STATE], nil);
- return;
- }
-
- CHIPDefaultFailureCallbackBridge * onFailure = new CHIPDefaultFailureCallbackBridge(completionHandler, [self callbackQueue]);
- if (!onFailure) {
- delete onSuccess;
- completionHandler([CHIPError errorForCHIPErrorCode:CHIP_ERROR_INCORRECT_STATE], nil);
- return;
- }
-
- CHIP_ERROR err = self.cppCluster.LaunchURL(onSuccess->Cancel(), onFailure->Cancel());
- if (err != CHIP_NO_ERROR) {
- delete onSuccess;
- delete onFailure;
- completionHandler([CHIPError errorForCHIPErrorCode:err], nil);
- }
-}
-
-- (void)readAttributeClusterRevision:(ResponseHandler)completionHandler
-{
- CHIPInt16uAttributeCallbackBridge * onSuccess = new CHIPInt16uAttributeCallbackBridge(completionHandler, [self callbackQueue]);
- if (!onSuccess) {
- completionHandler([CHIPError errorForCHIPErrorCode:CHIP_ERROR_INCORRECT_STATE], nil);
- return;
- }
-
- CHIPDefaultFailureCallbackBridge * onFailure = new CHIPDefaultFailureCallbackBridge(completionHandler, [self callbackQueue]);
- if (!onFailure) {
- delete onSuccess;
- completionHandler([CHIPError errorForCHIPErrorCode:CHIP_ERROR_INCORRECT_STATE], nil);
- return;
- }
-
- CHIP_ERROR err = self.cppCluster.ReadAttributeClusterRevision(onSuccess->Cancel(), onFailure->Cancel());
- if (err != CHIP_NO_ERROR) {
- delete onSuccess;
- delete onFailure;
- completionHandler([CHIPError errorForCHIPErrorCode:err], nil);
- }
-}
-
-@end
-
@interface CHIPDoorLock ()
@property (readonly) Controller::DoorLockCluster cppCluster;
@end
@end
-@interface CHIPMediaPlayback ()
-@property (readonly) Controller::MediaPlaybackCluster cppCluster;
-@end
-
-@implementation CHIPMediaPlayback
-
-- (Controller::ClusterBase *)getCluster
-{
- return &_cppCluster;
-}
-
-- (void)fastForwardRequest:(ResponseHandler)completionHandler
-{
- CHIPDefaultSuccessCallbackBridge * onSuccess = new CHIPDefaultSuccessCallbackBridge(completionHandler, [self callbackQueue]);
- if (!onSuccess) {
- completionHandler([CHIPError errorForCHIPErrorCode:CHIP_ERROR_INCORRECT_STATE], nil);
- return;
- }
-
- CHIPDefaultFailureCallbackBridge * onFailure = new CHIPDefaultFailureCallbackBridge(completionHandler, [self callbackQueue]);
- if (!onFailure) {
- delete onSuccess;
- completionHandler([CHIPError errorForCHIPErrorCode:CHIP_ERROR_INCORRECT_STATE], nil);
- return;
- }
-
- CHIP_ERROR err = self.cppCluster.FastForwardRequest(onSuccess->Cancel(), onFailure->Cancel());
- if (err != CHIP_NO_ERROR) {
- delete onSuccess;
- delete onFailure;
- completionHandler([CHIPError errorForCHIPErrorCode:err], nil);
- }
-}
-- (void)nextRequest:(ResponseHandler)completionHandler
-{
- CHIPDefaultSuccessCallbackBridge * onSuccess = new CHIPDefaultSuccessCallbackBridge(completionHandler, [self callbackQueue]);
- if (!onSuccess) {
- completionHandler([CHIPError errorForCHIPErrorCode:CHIP_ERROR_INCORRECT_STATE], nil);
- return;
- }
-
- CHIPDefaultFailureCallbackBridge * onFailure = new CHIPDefaultFailureCallbackBridge(completionHandler, [self callbackQueue]);
- if (!onFailure) {
- delete onSuccess;
- completionHandler([CHIPError errorForCHIPErrorCode:CHIP_ERROR_INCORRECT_STATE], nil);
- return;
- }
-
- CHIP_ERROR err = self.cppCluster.NextRequest(onSuccess->Cancel(), onFailure->Cancel());
- if (err != CHIP_NO_ERROR) {
- delete onSuccess;
- delete onFailure;
- completionHandler([CHIPError errorForCHIPErrorCode:err], nil);
- }
-}
-- (void)pauseRequest:(ResponseHandler)completionHandler
-{
- CHIPDefaultSuccessCallbackBridge * onSuccess = new CHIPDefaultSuccessCallbackBridge(completionHandler, [self callbackQueue]);
- if (!onSuccess) {
- completionHandler([CHIPError errorForCHIPErrorCode:CHIP_ERROR_INCORRECT_STATE], nil);
- return;
- }
-
- CHIPDefaultFailureCallbackBridge * onFailure = new CHIPDefaultFailureCallbackBridge(completionHandler, [self callbackQueue]);
- if (!onFailure) {
- delete onSuccess;
- completionHandler([CHIPError errorForCHIPErrorCode:CHIP_ERROR_INCORRECT_STATE], nil);
- return;
- }
-
- CHIP_ERROR err = self.cppCluster.PauseRequest(onSuccess->Cancel(), onFailure->Cancel());
- if (err != CHIP_NO_ERROR) {
- delete onSuccess;
- delete onFailure;
- completionHandler([CHIPError errorForCHIPErrorCode:err], nil);
- }
-}
-- (void)playRequest:(ResponseHandler)completionHandler
-{
- CHIPDefaultSuccessCallbackBridge * onSuccess = new CHIPDefaultSuccessCallbackBridge(completionHandler, [self callbackQueue]);
- if (!onSuccess) {
- completionHandler([CHIPError errorForCHIPErrorCode:CHIP_ERROR_INCORRECT_STATE], nil);
- return;
- }
-
- CHIPDefaultFailureCallbackBridge * onFailure = new CHIPDefaultFailureCallbackBridge(completionHandler, [self callbackQueue]);
- if (!onFailure) {
- delete onSuccess;
- completionHandler([CHIPError errorForCHIPErrorCode:CHIP_ERROR_INCORRECT_STATE], nil);
- return;
- }
-
- CHIP_ERROR err = self.cppCluster.PlayRequest(onSuccess->Cancel(), onFailure->Cancel());
- if (err != CHIP_NO_ERROR) {
- delete onSuccess;
- delete onFailure;
- completionHandler([CHIPError errorForCHIPErrorCode:err], nil);
- }
-}
-- (void)previousRequest:(ResponseHandler)completionHandler
-{
- CHIPDefaultSuccessCallbackBridge * onSuccess = new CHIPDefaultSuccessCallbackBridge(completionHandler, [self callbackQueue]);
- if (!onSuccess) {
- completionHandler([CHIPError errorForCHIPErrorCode:CHIP_ERROR_INCORRECT_STATE], nil);
- return;
- }
-
- CHIPDefaultFailureCallbackBridge * onFailure = new CHIPDefaultFailureCallbackBridge(completionHandler, [self callbackQueue]);
- if (!onFailure) {
- delete onSuccess;
- completionHandler([CHIPError errorForCHIPErrorCode:CHIP_ERROR_INCORRECT_STATE], nil);
- return;
- }
-
- CHIP_ERROR err = self.cppCluster.PreviousRequest(onSuccess->Cancel(), onFailure->Cancel());
- if (err != CHIP_NO_ERROR) {
- delete onSuccess;
- delete onFailure;
- completionHandler([CHIPError errorForCHIPErrorCode:err], nil);
- }
-}
-- (void)rewindRequest:(ResponseHandler)completionHandler
-{
- CHIPDefaultSuccessCallbackBridge * onSuccess = new CHIPDefaultSuccessCallbackBridge(completionHandler, [self callbackQueue]);
- if (!onSuccess) {
- completionHandler([CHIPError errorForCHIPErrorCode:CHIP_ERROR_INCORRECT_STATE], nil);
- return;
- }
-
- CHIPDefaultFailureCallbackBridge * onFailure = new CHIPDefaultFailureCallbackBridge(completionHandler, [self callbackQueue]);
- if (!onFailure) {
- delete onSuccess;
- completionHandler([CHIPError errorForCHIPErrorCode:CHIP_ERROR_INCORRECT_STATE], nil);
- return;
- }
-
- CHIP_ERROR err = self.cppCluster.RewindRequest(onSuccess->Cancel(), onFailure->Cancel());
- if (err != CHIP_NO_ERROR) {
- delete onSuccess;
- delete onFailure;
- completionHandler([CHIPError errorForCHIPErrorCode:err], nil);
- }
-}
-- (void)skipBackwardRequest:(ResponseHandler)completionHandler
-{
- CHIPDefaultSuccessCallbackBridge * onSuccess = new CHIPDefaultSuccessCallbackBridge(completionHandler, [self callbackQueue]);
- if (!onSuccess) {
- completionHandler([CHIPError errorForCHIPErrorCode:CHIP_ERROR_INCORRECT_STATE], nil);
- return;
- }
-
- CHIPDefaultFailureCallbackBridge * onFailure = new CHIPDefaultFailureCallbackBridge(completionHandler, [self callbackQueue]);
- if (!onFailure) {
- delete onSuccess;
- completionHandler([CHIPError errorForCHIPErrorCode:CHIP_ERROR_INCORRECT_STATE], nil);
- return;
- }
-
- CHIP_ERROR err = self.cppCluster.SkipBackwardRequest(onSuccess->Cancel(), onFailure->Cancel());
- if (err != CHIP_NO_ERROR) {
- delete onSuccess;
- delete onFailure;
- completionHandler([CHIPError errorForCHIPErrorCode:err], nil);
- }
-}
-- (void)skipForwardRequest:(ResponseHandler)completionHandler
-{
- CHIPDefaultSuccessCallbackBridge * onSuccess = new CHIPDefaultSuccessCallbackBridge(completionHandler, [self callbackQueue]);
- if (!onSuccess) {
- completionHandler([CHIPError errorForCHIPErrorCode:CHIP_ERROR_INCORRECT_STATE], nil);
- return;
- }
-
- CHIPDefaultFailureCallbackBridge * onFailure = new CHIPDefaultFailureCallbackBridge(completionHandler, [self callbackQueue]);
- if (!onFailure) {
- delete onSuccess;
- completionHandler([CHIPError errorForCHIPErrorCode:CHIP_ERROR_INCORRECT_STATE], nil);
- return;
- }
-
- CHIP_ERROR err = self.cppCluster.SkipForwardRequest(onSuccess->Cancel(), onFailure->Cancel());
- if (err != CHIP_NO_ERROR) {
- delete onSuccess;
- delete onFailure;
- completionHandler([CHIPError errorForCHIPErrorCode:err], nil);
- }
-}
-- (void)startOverRequest:(ResponseHandler)completionHandler
-{
- CHIPDefaultSuccessCallbackBridge * onSuccess = new CHIPDefaultSuccessCallbackBridge(completionHandler, [self callbackQueue]);
- if (!onSuccess) {
- completionHandler([CHIPError errorForCHIPErrorCode:CHIP_ERROR_INCORRECT_STATE], nil);
- return;
- }
-
- CHIPDefaultFailureCallbackBridge * onFailure = new CHIPDefaultFailureCallbackBridge(completionHandler, [self callbackQueue]);
- if (!onFailure) {
- delete onSuccess;
- completionHandler([CHIPError errorForCHIPErrorCode:CHIP_ERROR_INCORRECT_STATE], nil);
- return;
- }
-
- CHIP_ERROR err = self.cppCluster.StartOverRequest(onSuccess->Cancel(), onFailure->Cancel());
- if (err != CHIP_NO_ERROR) {
- delete onSuccess;
- delete onFailure;
- completionHandler([CHIPError errorForCHIPErrorCode:err], nil);
- }
-}
-- (void)stopRequest:(ResponseHandler)completionHandler
-{
- CHIPDefaultSuccessCallbackBridge * onSuccess = new CHIPDefaultSuccessCallbackBridge(completionHandler, [self callbackQueue]);
- if (!onSuccess) {
- completionHandler([CHIPError errorForCHIPErrorCode:CHIP_ERROR_INCORRECT_STATE], nil);
- return;
- }
-
- CHIPDefaultFailureCallbackBridge * onFailure = new CHIPDefaultFailureCallbackBridge(completionHandler, [self callbackQueue]);
- if (!onFailure) {
- delete onSuccess;
- completionHandler([CHIPError errorForCHIPErrorCode:CHIP_ERROR_INCORRECT_STATE], nil);
- return;
- }
-
- CHIP_ERROR err = self.cppCluster.StopRequest(onSuccess->Cancel(), onFailure->Cancel());
- if (err != CHIP_NO_ERROR) {
- delete onSuccess;
- delete onFailure;
- completionHandler([CHIPError errorForCHIPErrorCode:err], nil);
- }
-}
-
-- (void)readAttributeCurrentState:(ResponseHandler)completionHandler
-{
- CHIPInt16uAttributeCallbackBridge * onSuccess = new CHIPInt16uAttributeCallbackBridge(completionHandler, [self callbackQueue]);
- if (!onSuccess) {
- completionHandler([CHIPError errorForCHIPErrorCode:CHIP_ERROR_INCORRECT_STATE], nil);
- return;
- }
-
- CHIPDefaultFailureCallbackBridge * onFailure = new CHIPDefaultFailureCallbackBridge(completionHandler, [self callbackQueue]);
- if (!onFailure) {
- delete onSuccess;
- completionHandler([CHIPError errorForCHIPErrorCode:CHIP_ERROR_INCORRECT_STATE], nil);
- return;
- }
-
- CHIP_ERROR err = self.cppCluster.ReadAttributeCurrentState(onSuccess->Cancel(), onFailure->Cancel());
- if (err != CHIP_NO_ERROR) {
- delete onSuccess;
- delete onFailure;
- completionHandler([CHIPError errorForCHIPErrorCode:err], nil);
- }
-}
-
-- (void)readAttributeClusterRevision:(ResponseHandler)completionHandler
-{
- CHIPInt16uAttributeCallbackBridge * onSuccess = new CHIPInt16uAttributeCallbackBridge(completionHandler, [self callbackQueue]);
- if (!onSuccess) {
- completionHandler([CHIPError errorForCHIPErrorCode:CHIP_ERROR_INCORRECT_STATE], nil);
- return;
- }
-
- CHIPDefaultFailureCallbackBridge * onFailure = new CHIPDefaultFailureCallbackBridge(completionHandler, [self callbackQueue]);
- if (!onFailure) {
- delete onSuccess;
- completionHandler([CHIPError errorForCHIPErrorCode:CHIP_ERROR_INCORRECT_STATE], nil);
- return;
- }
-
- CHIP_ERROR err = self.cppCluster.ReadAttributeClusterRevision(onSuccess->Cancel(), onFailure->Cancel());
- if (err != CHIP_NO_ERROR) {
- delete onSuccess;
- delete onFailure;
- completionHandler([CHIPError errorForCHIPErrorCode:err], nil);
- }
-}
-
-@end
-
@interface CHIPOnOff ()
@property (readonly) Controller::OnOffCluster cppCluster;
@end
namespace clusters {
-namespace ContentLaunch {
-
-void DispatchClientCommand(app::Command * command, CommandId commandId, EndpointId endpointId, TLV::TLVReader & dataTlv)
-{
- {
- switch (commandId)
- {
- case ZCL_LAUNCH_CONTENT_RESPONSE_COMMAND_ID: {
- CHIP_ERROR TLVError = CHIP_NO_ERROR;
- uint8_t contentLaunchStatus;
-
- while ((TLVError = dataTlv.Next()) == CHIP_NO_ERROR)
- {
- switch (TLV::TagNumFromTag(dataTlv.GetTag()))
- {
- case 0:
- TLVError = dataTlv.Get(contentLaunchStatus);
- break;
- default:
- // Unsupported tag, ignore it.
- ChipLogProgress(Zcl, "Unknown TLV tag during processing.");
- break;
- }
- if (TLVError != CHIP_NO_ERROR)
- {
- ChipLogProgress(Zcl, "Failed to decode TLV data with tag %" PRIx32 ": %" PRId32,
- TLV::TagNumFromTag(dataTlv.GetTag()), TLVError);
- }
- }
- // TODO(#5098) We should pass the Command Object and EndpointId to the cluster callbacks.
- emberAfContentLaunchClusterLaunchContentResponseCallback(contentLaunchStatus);
- break;
- }
- case ZCL_LAUNCH_URL_RESPONSE_COMMAND_ID: {
- CHIP_ERROR TLVError = CHIP_NO_ERROR;
- uint8_t contentLaunchStatus;
-
- while ((TLVError = dataTlv.Next()) == CHIP_NO_ERROR)
- {
- switch (TLV::TagNumFromTag(dataTlv.GetTag()))
- {
- case 0:
- TLVError = dataTlv.Get(contentLaunchStatus);
- break;
- default:
- // Unsupported tag, ignore it.
- ChipLogProgress(Zcl, "Unknown TLV tag during processing.");
- break;
- }
- if (TLVError != CHIP_NO_ERROR)
- {
- ChipLogProgress(Zcl, "Failed to decode TLV data with tag %" PRIx32 ": %" PRId32,
- TLV::TagNumFromTag(dataTlv.GetTag()), TLVError);
- }
- }
- // TODO(#5098) We should pass the Command Object and EndpointId to the cluster callbacks.
- emberAfContentLaunchClusterLaunchURLResponseCallback(contentLaunchStatus);
- break;
- }
- default: {
- // Unrecognized command ID, error status will apply.
- // TODO: Encode response for command not found
- ChipLogError(Zcl, "Unknown command %" PRIx16 " for cluster %" PRIx16, commandId, ZCL_CONTENT_LAUNCH_CLUSTER_ID);
- break;
- }
- }
- }
-}
-
-} // namespace ContentLaunch
-
namespace DoorLock {
void DispatchClientCommand(app::Command * command, CommandId commandId, EndpointId endpointId, TLV::TLVReader & dataTlv)
} // namespace Identify
-namespace MediaPlayback {
-
-void DispatchClientCommand(app::Command * command, CommandId commandId, EndpointId endpointId, TLV::TLVReader & dataTlv)
-{
- {
- switch (commandId)
- {
- case ZCL_PLAYBACK_COMMAND_ID: {
- // TODO(#5098) We should pass the Command Object and EndpointId to the cluster callbacks.
- emberAfMediaPlaybackClusterPlaybackCallback();
- break;
- }
- default: {
- // Unrecognized command ID, error status will apply.
- // TODO: Encode response for command not found
- ChipLogError(Zcl, "Unknown command %" PRIx16 " for cluster %" PRIx16, commandId, ZCL_MEDIA_PLAYBACK_CLUSTER_ID);
- break;
- }
- }
- }
-}
-
-} // namespace MediaPlayback
-
namespace Scenes {
void DispatchClientCommand(app::Command * command, CommandId commandId, EndpointId endpointId, TLV::TLVReader & dataTlv)
// Server attributes
#define ZCL_MAX_DURATION_ATTRIBUTE_ID (0x0000)
+// Attribute ids for cluster: Media Playback
+
+// Client attributes
+
+// Server attributes
+#define ZCL_CURRENT_STATE_ATTRIBUTE_ID (0x0000)
+
// Attribute ids for cluster: Low Power
// Client attributes
// Server attributes
+// Attribute ids for cluster: Content Launch
+
+// Client attributes
+
+// Server attributes
+
// Attribute ids for cluster: Application Basic
// Client attributes
// Server attributes
-// Attribute ids for cluster: Media Playback
-
-// Client attributes
-
-// Server attributes
-#define ZCL_CURRENT_STATE_ATTRIBUTE_ID (0x0000)
-
-// Attribute ids for cluster: Content Launch
-
-// Client attributes
-
-// Server attributes
-
// Attribute ids for cluster: Group Key Management
// Client attributes
EmberAfStatus emberAfBasicClusterClientCommandParse(EmberAfClusterCommand * cmd);
EmberAfStatus emberAfBindingClusterClientCommandParse(EmberAfClusterCommand * cmd);
EmberAfStatus emberAfColorControlClusterClientCommandParse(EmberAfClusterCommand * cmd);
-EmberAfStatus emberAfContentLaunchClusterClientCommandParse(EmberAfClusterCommand * cmd);
EmberAfStatus emberAfDoorLockClusterClientCommandParse(EmberAfClusterCommand * cmd);
EmberAfStatus emberAfGeneralCommissioningClusterClientCommandParse(EmberAfClusterCommand * cmd);
EmberAfStatus emberAfGroupsClusterClientCommandParse(EmberAfClusterCommand * cmd);
EmberAfStatus emberAfIdentifyClusterClientCommandParse(EmberAfClusterCommand * cmd);
EmberAfStatus emberAfLevelControlClusterClientCommandParse(EmberAfClusterCommand * cmd);
EmberAfStatus emberAfLowPowerClusterClientCommandParse(EmberAfClusterCommand * cmd);
-EmberAfStatus emberAfMediaPlaybackClusterClientCommandParse(EmberAfClusterCommand * cmd);
EmberAfStatus emberAfOnOffClusterClientCommandParse(EmberAfClusterCommand * cmd);
EmberAfStatus emberAfScenesClusterClientCommandParse(EmberAfClusterCommand * cmd);
EmberAfStatus emberAfTemperatureMeasurementClusterClientCommandParse(EmberAfClusterCommand * cmd);
// No commands are enabled for cluster Color Control
result = status(false, true, cmd->mfgSpecific);
break;
- case ZCL_CONTENT_LAUNCH_CLUSTER_ID:
- result = emberAfContentLaunchClusterClientCommandParse(cmd);
- break;
case ZCL_DOOR_LOCK_CLUSTER_ID:
result = emberAfDoorLockClusterClientCommandParse(cmd);
break;
// No commands are enabled for cluster Low Power
result = status(false, true, cmd->mfgSpecific);
break;
- case ZCL_MEDIA_PLAYBACK_CLUSTER_ID:
- result = emberAfMediaPlaybackClusterClientCommandParse(cmd);
- break;
case ZCL_ON_OFF_CLUSTER_ID:
// No commands are enabled for cluster On/off
result = status(false, true, cmd->mfgSpecific);
// Cluster specific command parsing
-EmberAfStatus emberAfContentLaunchClusterClientCommandParse(EmberAfClusterCommand * cmd)
-{
- bool wasHandled = false;
-
- if (!cmd->mfgSpecific)
- {
- switch (cmd->commandId)
- {
- case ZCL_LAUNCH_CONTENT_RESPONSE_COMMAND_ID: {
- uint16_t payloadOffset = cmd->payloadStartIndex;
- uint8_t contentLaunchStatus;
-
- if (cmd->bufLen < payloadOffset + 1)
- {
- return EMBER_ZCL_STATUS_MALFORMED_COMMAND;
- }
- contentLaunchStatus = emberAfGetInt8u(cmd->buffer, payloadOffset, cmd->bufLen);
-
- wasHandled = emberAfContentLaunchClusterLaunchContentResponseCallback(contentLaunchStatus);
- break;
- }
- case ZCL_LAUNCH_URL_RESPONSE_COMMAND_ID: {
- uint16_t payloadOffset = cmd->payloadStartIndex;
- uint8_t contentLaunchStatus;
-
- if (cmd->bufLen < payloadOffset + 1)
- {
- return EMBER_ZCL_STATUS_MALFORMED_COMMAND;
- }
- contentLaunchStatus = emberAfGetInt8u(cmd->buffer, payloadOffset, cmd->bufLen);
-
- wasHandled = emberAfContentLaunchClusterLaunchURLResponseCallback(contentLaunchStatus);
- break;
- }
- default: {
- // Unrecognized command ID, error status will apply.
- break;
- }
- }
- }
- return status(wasHandled, true, cmd->mfgSpecific);
-}
EmberAfStatus emberAfDoorLockClusterClientCommandParse(EmberAfClusterCommand * cmd)
{
bool wasHandled = false;
}
return status(wasHandled, true, cmd->mfgSpecific);
}
-EmberAfStatus emberAfMediaPlaybackClusterClientCommandParse(EmberAfClusterCommand * cmd)
-{
- bool wasHandled = false;
-
- if (!cmd->mfgSpecific)
- {
- switch (cmd->commandId)
- {
- case ZCL_PLAYBACK_COMMAND_ID: {
- wasHandled = emberAfMediaPlaybackClusterPlaybackCallback();
- break;
- }
- default: {
- // Unrecognized command ID, error status will apply.
- break;
- }
- }
- }
- return status(wasHandled, true, cmd->mfgSpecific);
-}
EmberAfStatus emberAfScenesClusterClientCommandParse(EmberAfClusterCommand * cmd)
{
bool wasHandled = false;
case ZCL_COLOR_CONTROL_CLUSTER_ID:
emberAfColorControlClusterInitCallback(endpoint);
break;
- case ZCL_CONTENT_LAUNCH_CLUSTER_ID:
- emberAfContentLaunchClusterInitCallback(endpoint);
- break;
case ZCL_DOOR_LOCK_CLUSTER_ID:
emberAfDoorLockClusterInitCallback(endpoint);
break;
case ZCL_LOW_POWER_CLUSTER_ID:
emberAfLowPowerClusterInitCallback(endpoint);
break;
- case ZCL_MEDIA_PLAYBACK_CLUSTER_ID:
- emberAfMediaPlaybackClusterInitCallback(endpoint);
- break;
case ZCL_ON_OFF_CLUSTER_ID:
emberAfOnOffClusterInitCallback(endpoint);
break;
// To prevent warning
(void) endpoint;
}
-void __attribute__((weak)) emberAfContentLaunchClusterInitCallback(EndpointId endpoint)
-{
- // To prevent warning
- (void) endpoint;
-}
void __attribute__((weak)) emberAfDoorLockClusterInitCallback(EndpointId endpoint)
{
// To prevent warning
// To prevent warning
(void) endpoint;
}
-void __attribute__((weak)) emberAfMediaPlaybackClusterInitCallback(EndpointId endpoint)
-{
- // To prevent warning
- (void) endpoint;
-}
void __attribute__((weak)) emberAfOnOffClusterInitCallback(EndpointId endpoint)
{
// To prevent warning
*/
void emberAfColorControlClusterInitCallback(chip::EndpointId endpoint);
-/** @brief Content Launch Cluster Init
- *
- * Cluster Init
- *
- * @param endpoint Endpoint that is being initialized
- */
-void emberAfContentLaunchClusterInitCallback(chip::EndpointId endpoint);
-
/** @brief Door Lock Cluster Init
*
* Cluster Init
*/
void emberAfLowPowerClusterInitCallback(chip::EndpointId endpoint);
-/** @brief Media Playback Cluster Init
- *
- * Cluster Init
- *
- * @param endpoint Endpoint that is being initialized
- */
-void emberAfMediaPlaybackClusterInitCallback(chip::EndpointId endpoint);
-
/** @brief On/off Cluster Init
*
* Cluster Init
void emberAfColorControlClusterClientTickCallback(chip::EndpointId endpoint);
//
-// Content Launch Cluster client
-//
-
-/** @brief Content Launch Cluster Client Init
- *
- * Client Init
- *
- * @param endpoint Endpoint that is being initialized
- */
-void emberAfContentLaunchClusterClientInitCallback(chip::EndpointId endpoint);
-
-/** @brief Content Launch Cluster Client Attribute Changed
- *
- * Client Attribute Changed
- *
- * @param endpoint Endpoint that is being initialized
- * @param attributeId Attribute that changed
- */
-void emberAfContentLaunchClusterClientAttributeChangedCallback(chip::EndpointId endpoint, chip::AttributeId attributeId);
-
-/** @brief Content Launch Cluster Client Manufacturer Specific Attribute Changed
- *
- * Client Manufacturer Specific Attribute Changed
- *
- * @param endpoint Endpoint that is being initialized
- * @param attributeId Attribute that changed
- * @param manufacturerCode Manufacturer Code of the attribute that changed
- */
-void emberAfContentLaunchClusterClientManufacturerSpecificAttributeChangedCallback(chip::EndpointId endpoint,
- chip::AttributeId attributeId,
- uint16_t manufacturerCode);
-
-/** @brief Content Launch Cluster Client Message Sent
- *
- * Client Message Sent
- *
- * @param type The type of message sent
- * @param indexOrDestination The destination or address to which the message was sent
- * @param apsFrame The APS frame for the message
- * @param msgLen The length of the message
- * @param message The message that was sent
- * @param status The status of the sent message
- */
-void emberAfContentLaunchClusterClientMessageSentCallback(EmberOutgoingMessageType type, uint64_t indexOrDestination,
- EmberApsFrame * apsFrame, uint16_t msgLen, uint8_t * message,
- EmberStatus status);
-
-/** @brief Content Launch Cluster Client Pre Attribute Changed
- *
- * client Pre Attribute Changed
- *
- * @param endpoint Endpoint that is being initialized
- * @param attributeId Attribute to be changed
- * @param attributeType Attribute type
- * @param size Attribute size
- * @param value Attribute value
- */
-EmberAfStatus emberAfContentLaunchClusterClientPreAttributeChangedCallback(chip::EndpointId endpoint, chip::AttributeId attributeId,
- EmberAfAttributeType attributeType, uint8_t size,
- uint8_t * value);
-
-/** @brief Content Launch Cluster Client Tick
- *
- * client Tick
- *
- * @param endpoint Endpoint that is being served
- */
-void emberAfContentLaunchClusterClientTickCallback(chip::EndpointId endpoint);
-
-//
// Door Lock Cluster client
//
void emberAfLowPowerClusterClientTickCallback(chip::EndpointId endpoint);
//
-// Media Playback Cluster client
-//
-
-/** @brief Media Playback Cluster Client Init
- *
- * Client Init
- *
- * @param endpoint Endpoint that is being initialized
- */
-void emberAfMediaPlaybackClusterClientInitCallback(chip::EndpointId endpoint);
-
-/** @brief Media Playback Cluster Client Attribute Changed
- *
- * Client Attribute Changed
- *
- * @param endpoint Endpoint that is being initialized
- * @param attributeId Attribute that changed
- */
-void emberAfMediaPlaybackClusterClientAttributeChangedCallback(chip::EndpointId endpoint, chip::AttributeId attributeId);
-
-/** @brief Media Playback Cluster Client Manufacturer Specific Attribute Changed
- *
- * Client Manufacturer Specific Attribute Changed
- *
- * @param endpoint Endpoint that is being initialized
- * @param attributeId Attribute that changed
- * @param manufacturerCode Manufacturer Code of the attribute that changed
- */
-void emberAfMediaPlaybackClusterClientManufacturerSpecificAttributeChangedCallback(chip::EndpointId endpoint,
- chip::AttributeId attributeId,
- uint16_t manufacturerCode);
-
-/** @brief Media Playback Cluster Client Message Sent
- *
- * Client Message Sent
- *
- * @param type The type of message sent
- * @param indexOrDestination The destination or address to which the message was sent
- * @param apsFrame The APS frame for the message
- * @param msgLen The length of the message
- * @param message The message that was sent
- * @param status The status of the sent message
- */
-void emberAfMediaPlaybackClusterClientMessageSentCallback(EmberOutgoingMessageType type, uint64_t indexOrDestination,
- EmberApsFrame * apsFrame, uint16_t msgLen, uint8_t * message,
- EmberStatus status);
-
-/** @brief Media Playback Cluster Client Pre Attribute Changed
- *
- * client Pre Attribute Changed
- *
- * @param endpoint Endpoint that is being initialized
- * @param attributeId Attribute to be changed
- * @param attributeType Attribute type
- * @param size Attribute size
- * @param value Attribute value
- */
-EmberAfStatus emberAfMediaPlaybackClusterClientPreAttributeChangedCallback(chip::EndpointId endpoint, chip::AttributeId attributeId,
- EmberAfAttributeType attributeType, uint8_t size,
- uint8_t * value);
-
-/** @brief Media Playback Cluster Client Tick
- *
- * client Tick
- *
- * @param endpoint Endpoint that is being served
- */
-void emberAfMediaPlaybackClusterClientTickCallback(chip::EndpointId endpoint);
-
-//
// On/off Cluster client
//
// Cluster Commands Callback
/**
- * @brief Content Launch Cluster LaunchContentResponse Command callback
- * @param contentLaunchStatus
- */
-
-bool emberAfContentLaunchClusterLaunchContentResponseCallback(uint8_t contentLaunchStatus);
-
-/**
- * @brief Content Launch Cluster LaunchURLResponse Command callback
- * @param contentLaunchStatus
- */
-
-bool emberAfContentLaunchClusterLaunchURLResponseCallback(uint8_t contentLaunchStatus);
-
-/**
* @brief Door Lock Cluster ClearAllPinsResponse Command callback
* @param status
*/
bool emberAfIdentifyClusterIdentifyQueryResponseCallback(uint16_t timeout);
/**
- * @brief Media Playback Cluster Playback Command callback
- */
-
-bool emberAfMediaPlaybackClusterPlaybackCallback();
-
-/**
* @brief Scenes Cluster AddSceneResponse Command callback
* @param status
* @param groupId
\
ZCL_SQUAWK_COMMAND_ID, "u", squawkInfo);
+/** @brief Command description for PlayRequest
+ *
+ * Command: PlayRequest
+ */
+#define emberAfFillCommandMedia \
+ PlaybackClusterPlayRequest() emberAfFillExternalBuffer(mask, \
+ \
+ ZCL_PLAY_REQUEST_COMMAND_ID, "", );
+
+/** @brief Command description for PauseRequest
+ *
+ * Command: PauseRequest
+ */
+#define emberAfFillCommandMedia \
+ PlaybackClusterPauseRequest() emberAfFillExternalBuffer(mask, \
+ \
+ ZCL_PAUSE_REQUEST_COMMAND_ID, "", );
+
+/** @brief Command description for StopRequest
+ *
+ * Command: StopRequest
+ */
+#define emberAfFillCommandMedia \
+ PlaybackClusterStopRequest() emberAfFillExternalBuffer(mask, \
+ \
+ ZCL_STOP_REQUEST_COMMAND_ID, "", );
+
+/** @brief Command description for StartOverRequest
+ *
+ * Command: StartOverRequest
+ */
+#define emberAfFillCommandMedia \
+ PlaybackClusterStartOverRequest() emberAfFillExternalBuffer(mask, \
+ \
+ ZCL_START_OVER_REQUEST_COMMAND_ID, "", );
+
+/** @brief Command description for PreviousRequest
+ *
+ * Command: PreviousRequest
+ */
+#define emberAfFillCommandMedia \
+ PlaybackClusterPreviousRequest() emberAfFillExternalBuffer(mask, \
+ \
+ ZCL_PREVIOUS_REQUEST_COMMAND_ID, "", );
+
+/** @brief Command description for NextRequest
+ *
+ * Command: NextRequest
+ */
+#define emberAfFillCommandMedia \
+ PlaybackClusterNextRequest() emberAfFillExternalBuffer(mask, \
+ \
+ ZCL_NEXT_REQUEST_COMMAND_ID, "", );
+
+/** @brief Command description for RewindRequest
+ *
+ * Command: RewindRequest
+ */
+#define emberAfFillCommandMedia \
+ PlaybackClusterRewindRequest() emberAfFillExternalBuffer(mask, \
+ \
+ ZCL_REWIND_REQUEST_COMMAND_ID, "", );
+
+/** @brief Command description for FastForwardRequest
+ *
+ * Command: FastForwardRequest
+ */
+#define emberAfFillCommandMedia \
+ PlaybackClusterFastForwardRequest() emberAfFillExternalBuffer(mask, \
+ \
+ ZCL_FAST_FORWARD_REQUEST_COMMAND_ID, "", );
+
+/** @brief Command description for SkipForwardRequest
+ *
+ * Command: SkipForwardRequest
+ */
+#define emberAfFillCommandMedia \
+ PlaybackClusterSkipForwardRequest() emberAfFillExternalBuffer(mask, \
+ \
+ ZCL_SKIP_FORWARD_REQUEST_COMMAND_ID, "", );
+
+/** @brief Command description for SkipBackwardRequest
+ *
+ * Command: SkipBackwardRequest
+ */
+#define emberAfFillCommandMedia \
+ PlaybackClusterSkipBackwardRequest() emberAfFillExternalBuffer(mask, \
+ \
+ ZCL_SKIP_BACKWARD_REQUEST_COMMAND_ID, "", );
+
/** @brief Command description for Sleep
*
* Command: Sleep
\
ZCL_SLEEP_COMMAND_ID, "", );
+/** @brief Command description for LaunchContent
+ *
+ * Command: LaunchContent
+ * @param contentLaunchStatus ContentLaunchStatus
+ */
+#define emberAfFillCommandContent \
+ LaunchClusterLaunchContent(contentLaunchStatus) \
+ emberAfFillExternalBuffer(mask, \
+ \
+ ZCL_LAUNCH_CONTENT_COMMAND_ID, "u", contentLaunchStatus);
+
+/** @brief Command description for LaunchURL
+ *
+ * Command: LaunchURL
+ * @param contentLaunchStatus ContentLaunchStatus
+ */
+#define emberAfFillCommandContent \
+ LaunchClusterLaunchURL(contentLaunchStatus) emberAfFillExternalBuffer(mask, \
+ \
+ ZCL_LAUNCH_URL_COMMAND_ID, "u", contentLaunchStatus);
+
/** @brief Command description for MatchProtocolAddress
*
* Command: MatchProtocolAddress
\
ZCL_UNBIND_COMMAND_ID, "uuuu", nodeId, groupId, endpointId, clusterId);
-/** @brief Command description for PlayRequest
- *
- * Command: PlayRequest
- */
-#define emberAfFillCommandMedia \
- PlaybackClusterPlayRequest() emberAfFillExternalBuffer(mask, \
- \
- ZCL_PLAY_REQUEST_COMMAND_ID, "", );
-
-/** @brief Command description for PauseRequest
- *
- * Command: PauseRequest
- */
-#define emberAfFillCommandMedia \
- PlaybackClusterPauseRequest() emberAfFillExternalBuffer(mask, \
- \
- ZCL_PAUSE_REQUEST_COMMAND_ID, "", );
-
-/** @brief Command description for StopRequest
- *
- * Command: StopRequest
- */
-#define emberAfFillCommandMedia \
- PlaybackClusterStopRequest() emberAfFillExternalBuffer(mask, \
- \
- ZCL_STOP_REQUEST_COMMAND_ID, "", );
-
-/** @brief Command description for StartOverRequest
- *
- * Command: StartOverRequest
- */
-#define emberAfFillCommandMedia \
- PlaybackClusterStartOverRequest() emberAfFillExternalBuffer(mask, \
- \
- ZCL_START_OVER_REQUEST_COMMAND_ID, "", );
-
-/** @brief Command description for PreviousRequest
- *
- * Command: PreviousRequest
- */
-#define emberAfFillCommandMedia \
- PlaybackClusterPreviousRequest() emberAfFillExternalBuffer(mask, \
- \
- ZCL_PREVIOUS_REQUEST_COMMAND_ID, "", );
-
-/** @brief Command description for NextRequest
- *
- * Command: NextRequest
- */
-#define emberAfFillCommandMedia \
- PlaybackClusterNextRequest() emberAfFillExternalBuffer(mask, \
- \
- ZCL_NEXT_REQUEST_COMMAND_ID, "", );
-
-/** @brief Command description for RewindRequest
- *
- * Command: RewindRequest
- */
-#define emberAfFillCommandMedia \
- PlaybackClusterRewindRequest() emberAfFillExternalBuffer(mask, \
- \
- ZCL_REWIND_REQUEST_COMMAND_ID, "", );
-
-/** @brief Command description for FastForwardRequest
- *
- * Command: FastForwardRequest
- */
-#define emberAfFillCommandMedia \
- PlaybackClusterFastForwardRequest() emberAfFillExternalBuffer(mask, \
- \
- ZCL_FAST_FORWARD_REQUEST_COMMAND_ID, "", );
-
-/** @brief Command description for SkipForwardRequest
- *
- * Command: SkipForwardRequest
- */
-#define emberAfFillCommandMedia \
- PlaybackClusterSkipForwardRequest() emberAfFillExternalBuffer(mask, \
- \
- ZCL_SKIP_FORWARD_REQUEST_COMMAND_ID, "", );
-
-/** @brief Command description for SkipBackwardRequest
- *
- * Command: SkipBackwardRequest
- */
-#define emberAfFillCommandMedia \
- PlaybackClusterSkipBackwardRequest() emberAfFillExternalBuffer(mask, \
- \
- ZCL_SKIP_BACKWARD_REQUEST_COMMAND_ID, "", );
-
-/** @brief Command description for LaunchContent
- *
- * Command: LaunchContent
- * @param contentLaunchStatus ContentLaunchStatus
- */
-#define emberAfFillCommandContent \
- LaunchClusterLaunchContent(contentLaunchStatus) \
- emberAfFillExternalBuffer(mask, \
- \
- ZCL_LAUNCH_CONTENT_COMMAND_ID, "u", contentLaunchStatus);
-
-/** @brief Command description for LaunchURL
- *
- * Command: LaunchURL
- * @param contentLaunchStatus ContentLaunchStatus
- */
-#define emberAfFillCommandContent \
- LaunchClusterLaunchURL(contentLaunchStatus) emberAfFillExternalBuffer(mask, \
- \
- ZCL_LAUNCH_URL_COMMAND_ID, "u", contentLaunchStatus);
-
/** @brief Command description for CommandOne
*
* Command: CommandOne
// Definitions for cluster: IAS WD
#define ZCL_IAS_WD_CLUSTER_ID (0x0502)
+// Definitions for cluster: Media Playback
+#define ZCL_MEDIA_PLAYBACK_CLUSTER_ID (0x0506)
+
// Definitions for cluster: Low Power
#define ZCL_LOW_POWER_CLUSTER_ID (0x0508)
+// Definitions for cluster: Content Launch
+#define ZCL_CONTENT_LAUNCH_CLUSTER_ID (0x050A)
+
// Definitions for cluster: Application Basic
#define ZCL_APPLICATION_BASIC_CLUSTER_ID (0x050D)
// Definitions for cluster: Binding
#define ZCL_BINDING_CLUSTER_ID (0xF000)
-// Definitions for cluster: Media Playback
-#define ZCL_MEDIA_PLAYBACK_CLUSTER_ID (0xF001)
-
-// Definitions for cluster: Content Launch
-#define ZCL_CONTENT_LAUNCH_CLUSTER_ID (0xF002)
-
// Definitions for cluster: Group Key Management
#define ZCL_GROUP_KEY_MANAGEMENT_CLUSTER_ID (0xF004)
#define ZCL_START_WARNING_COMMAND_ID (0x00)
#define ZCL_SQUAWK_COMMAND_ID (0x01)
+// Commands for cluster: Media Playback
+#define ZCL_PLAY_REQUEST_COMMAND_ID (0x00)
+#define ZCL_PLAYBACK_COMMAND_ID (0x00)
+#define ZCL_PAUSE_REQUEST_COMMAND_ID (0x01)
+#define ZCL_STOP_REQUEST_COMMAND_ID (0x02)
+#define ZCL_START_OVER_REQUEST_COMMAND_ID (0x03)
+#define ZCL_PREVIOUS_REQUEST_COMMAND_ID (0x04)
+#define ZCL_NEXT_REQUEST_COMMAND_ID (0x05)
+#define ZCL_REWIND_REQUEST_COMMAND_ID (0x06)
+#define ZCL_FAST_FORWARD_REQUEST_COMMAND_ID (0x07)
+#define ZCL_SKIP_FORWARD_REQUEST_COMMAND_ID (0x08)
+#define ZCL_SKIP_BACKWARD_REQUEST_COMMAND_ID (0x09)
+
// Commands for cluster: Low Power
#define ZCL_SLEEP_COMMAND_ID (0x00)
+// Commands for cluster: Content Launch
+#define ZCL_LAUNCH_CONTENT_COMMAND_ID (0x00)
+#define ZCL_LAUNCH_CONTENT_RESPONSE_COMMAND_ID (0x00)
+#define ZCL_LAUNCH_URL_COMMAND_ID (0x01)
+#define ZCL_LAUNCH_URL_RESPONSE_COMMAND_ID (0x01)
+
// Commands for cluster: Generic Tunnel
#define ZCL_MATCH_PROTOCOL_ADDRESS_COMMAND_ID (0x00)
#define ZCL_MATCH_PROTOCOL_ADDRESS_RESPONSE_COMMAND_ID (0x00)
#define ZCL_BIND_COMMAND_ID (0x00)
#define ZCL_UNBIND_COMMAND_ID (0x01)
-// Commands for cluster: Media Playback
-#define ZCL_PLAY_REQUEST_COMMAND_ID (0x00)
-#define ZCL_PLAYBACK_COMMAND_ID (0x00)
-#define ZCL_PAUSE_REQUEST_COMMAND_ID (0x01)
-#define ZCL_STOP_REQUEST_COMMAND_ID (0x02)
-#define ZCL_START_OVER_REQUEST_COMMAND_ID (0x03)
-#define ZCL_PREVIOUS_REQUEST_COMMAND_ID (0x04)
-#define ZCL_NEXT_REQUEST_COMMAND_ID (0x05)
-#define ZCL_REWIND_REQUEST_COMMAND_ID (0x06)
-#define ZCL_FAST_FORWARD_REQUEST_COMMAND_ID (0x07)
-#define ZCL_SKIP_FORWARD_REQUEST_COMMAND_ID (0x08)
-#define ZCL_SKIP_BACKWARD_REQUEST_COMMAND_ID (0x09)
-
-// Commands for cluster: Content Launch
-#define ZCL_LAUNCH_CONTENT_COMMAND_ID (0x00)
-#define ZCL_LAUNCH_CONTENT_RESPONSE_COMMAND_ID (0x00)
-#define ZCL_LAUNCH_URL_COMMAND_ID (0x01)
-#define ZCL_LAUNCH_URL_RESPONSE_COMMAND_ID (0x01)
-
// Commands for cluster: Sample Mfg Specific Cluster
#define ZCL_COMMAND_ONE_COMMAND_ID (0x00)
#define ZAP_ATTRIBUTE_MASK(mask) ATTRIBUTE_MASK_##mask
// This is an array of EmberAfAttributeMetadata structures.
-#define GENERATED_ATTRIBUTE_COUNT 16
+#define GENERATED_ATTRIBUTE_COUNT 14
#define GENERATED_ATTRIBUTES \
{ \
{ 0xFFFD, ZAP_TYPE(INT16U), 2, ZAP_ATTRIBUTE_MASK(CLIENT), \
ZAP_SIMPLE_DEFAULT(0x0001) }, /* Application Basic (client): cluster revision */ \
{ 0xFFFD, ZAP_TYPE(INT16U), 2, ZAP_ATTRIBUTE_MASK(CLIENT), \
ZAP_SIMPLE_DEFAULT(0x0001) }, /* Binding (client): cluster revision */ \
- { 0xFFFD, ZAP_TYPE(INT16U), 2, ZAP_ATTRIBUTE_MASK(CLIENT), \
- ZAP_SIMPLE_DEFAULT(0x0001) }, /* Media Playback (client): cluster revision */ \
- { 0xFFFD, ZAP_TYPE(INT16U), 2, ZAP_ATTRIBUTE_MASK(CLIENT), \
- ZAP_SIMPLE_DEFAULT(0x0001) }, /* Content Launch (client): cluster revision */ \
}
// This is an array of EmberAfCluster structures.
#define GENERATED_FUNCTION_ARRAYS
#define ZAP_CLUSTER_MASK(mask) CLUSTER_MASK_##mask
-#define GENERATED_CLUSTER_COUNT 16
+#define GENERATED_CLUSTER_COUNT 14
#define GENERATED_CLUSTERS \
{ \
{ 0x0003, ZAP_ATTRIBUTE_INDEX(0), 1, 2, ZAP_CLUSTER_MASK(CLIENT), NULL }, /* Endpoint: 1, Cluster: Identify (client) */ \
{ \
0xF000, ZAP_ATTRIBUTE_INDEX(13), 1, 2, ZAP_CLUSTER_MASK(CLIENT), NULL \
}, /* Endpoint: 1, Cluster: Binding (client) */ \
- { \
- 0xF001, ZAP_ATTRIBUTE_INDEX(14), 1, 2, ZAP_CLUSTER_MASK(CLIENT), NULL \
- }, /* Endpoint: 1, Cluster: Media Playback (client) */ \
- { \
- 0xF002, ZAP_ATTRIBUTE_INDEX(15), 1, 2, ZAP_CLUSTER_MASK(CLIENT), NULL \
- }, /* Endpoint: 1, Cluster: Content Launch (client) */ \
}
#define ZAP_CLUSTER_INDEX(index) ((EmberAfCluster *) (&generatedClusters[index]))
// This is an array of EmberAfEndpointType structures.
#define GENERATED_ENDPOINT_TYPES \
{ \
- { ZAP_CLUSTER_INDEX(0), 16, 32 }, \
+ { ZAP_CLUSTER_INDEX(0), 14, 28 }, \
}
// Largest attribute size is needed for various buffers
#define ATTRIBUTE_SINGLETONS_SIZE (2)
// Total size of attribute storage
-#define ATTRIBUTE_MAX_SIZE (32)
+#define ATTRIBUTE_MAX_SIZE (28)
// Number of fixed endpoints
#define FIXED_ENDPOINT_COUNT (1)
// Array of EmberAfCommandMetadata structs.
#define ZAP_COMMAND_MASK(mask) COMMAND_MASK_##mask
-#define EMBER_AF_GENERATED_COMMAND_COUNT (129)
+#define EMBER_AF_GENERATED_COMMAND_COUNT (114)
#define GENERATED_COMMANDS \
{ \
{ 0x0003, 0x00, ZAP_COMMAND_MASK(INCOMING_SERVER) }, /* Identify (client): Identify */ \
{ 0x0508, 0x00, ZAP_COMMAND_MASK(INCOMING_SERVER) }, /* Low Power (client): Sleep */ \
{ 0xF000, 0x00, ZAP_COMMAND_MASK(INCOMING_SERVER) }, /* Binding (client): Bind */ \
{ 0xF000, 0x01, ZAP_COMMAND_MASK(INCOMING_SERVER) }, /* Binding (client): Unbind */ \
- { 0xF001, 0x00, ZAP_COMMAND_MASK(INCOMING_SERVER) }, /* Media Playback (client): PlayRequest */ \
- { 0xF001, 0x00, ZAP_COMMAND_MASK(INCOMING_CLIENT) }, /* Media Playback (client): Playback */ \
- { 0xF001, 0x01, ZAP_COMMAND_MASK(INCOMING_SERVER) }, /* Media Playback (client): PauseRequest */ \
- { 0xF001, 0x02, ZAP_COMMAND_MASK(INCOMING_SERVER) }, /* Media Playback (client): StopRequest */ \
- { 0xF001, 0x03, ZAP_COMMAND_MASK(INCOMING_SERVER) }, /* Media Playback (client): StartOverRequest */ \
- { 0xF001, 0x04, ZAP_COMMAND_MASK(INCOMING_SERVER) }, /* Media Playback (client): PreviousRequest */ \
- { 0xF001, 0x05, ZAP_COMMAND_MASK(INCOMING_SERVER) }, /* Media Playback (client): NextRequest */ \
- { 0xF001, 0x06, ZAP_COMMAND_MASK(INCOMING_SERVER) }, /* Media Playback (client): RewindRequest */ \
- { 0xF001, 0x07, ZAP_COMMAND_MASK(INCOMING_SERVER) }, /* Media Playback (client): FastForwardRequest */ \
- { 0xF001, 0x08, ZAP_COMMAND_MASK(INCOMING_SERVER) }, /* Media Playback (client): SkipForwardRequest */ \
- { 0xF001, 0x09, ZAP_COMMAND_MASK(INCOMING_SERVER) }, /* Media Playback (client): SkipBackwardRequest */ \
- { 0xF002, 0x00, ZAP_COMMAND_MASK(INCOMING_SERVER) }, /* Content Launch (client): LaunchContent */ \
- { 0xF002, 0x00, ZAP_COMMAND_MASK(INCOMING_CLIENT) }, /* Content Launch (client): LaunchContentResponse */ \
- { 0xF002, 0x01, ZAP_COMMAND_MASK(INCOMING_SERVER) }, /* Content Launch (client): LaunchURL */ \
- { 0xF002, 0x01, ZAP_COMMAND_MASK(INCOMING_CLIENT) }, /* Content Launch (client): LaunchURLResponse */ \
}
// Array of EmberAfManufacturerCodeEntry structures for commands.
#define EMBER_AF_BASIC_CLUSTER_CLIENT_ENDPOINT_COUNT (1)
#define EMBER_AF_BINDING_CLUSTER_CLIENT_ENDPOINT_COUNT (1)
#define EMBER_AF_COLOR_CONTROL_CLUSTER_CLIENT_ENDPOINT_COUNT (1)
-#define EMBER_AF_CONTENT_LAUNCH_CLUSTER_CLIENT_ENDPOINT_COUNT (1)
#define EMBER_AF_DOOR_LOCK_CLUSTER_CLIENT_ENDPOINT_COUNT (1)
#define EMBER_AF_GENERAL_COMMISSIONING_CLUSTER_CLIENT_ENDPOINT_COUNT (1)
#define EMBER_AF_GROUPS_CLUSTER_CLIENT_ENDPOINT_COUNT (1)
#define EMBER_AF_IDENTIFY_CLUSTER_CLIENT_ENDPOINT_COUNT (1)
#define EMBER_AF_LEVEL_CONTROL_CLUSTER_CLIENT_ENDPOINT_COUNT (1)
#define EMBER_AF_LOW_POWER_CLUSTER_CLIENT_ENDPOINT_COUNT (1)
-#define EMBER_AF_MEDIA_PLAYBACK_CLUSTER_CLIENT_ENDPOINT_COUNT (1)
#define EMBER_AF_ON_OFF_CLUSTER_CLIENT_ENDPOINT_COUNT (1)
#define EMBER_AF_SCENES_CLUSTER_CLIENT_ENDPOINT_COUNT (1)
#define EMBER_AF_TEMP_MEASUREMENT_CLUSTER_CLIENT_ENDPOINT_COUNT (1)
#define ZCL_USING_COLOR_CONTROL_CLUSTER_CLIENT
#define EMBER_AF_PLUGIN_COLOR_CONTROL_CLIENT
-// Use this macro to check if the client side of the Content Launch cluster is included
-#define ZCL_USING_CONTENT_LAUNCH_CLUSTER_CLIENT
-#define EMBER_AF_PLUGIN_CONTENT_LAUNCH_CLIENT
-
// Use this macro to check if the client side of the Door Lock cluster is included
#define ZCL_USING_DOOR_LOCK_CLUSTER_CLIENT
#define EMBER_AF_PLUGIN_DOOR_LOCK_CLIENT
#define ZCL_USING_LOW_POWER_CLUSTER_CLIENT
#define EMBER_AF_PLUGIN_LOW_POWER_CLIENT
-// Use this macro to check if the client side of the Media Playback cluster is included
-#define ZCL_USING_MEDIA_PLAYBACK_CLUSTER_CLIENT
-#define EMBER_AF_PLUGIN_MEDIA_PLAYBACK_CLIENT
-
// Use this macro to check if the client side of the On/off cluster is included
#define ZCL_USING_ON_OFF_CLUSTER_CLIENT
#define EMBER_AF_PLUGIN_ON_OFF_CLIENT
#define CHIP_PRINTCLUSTER_IAS_WD_CLUSTER
#endif
+#if defined(ZCL_USING_MEDIA_PLAYBACK_CLUSTER_SERVER) || defined(ZCL_USING_MEDIA_PLAYBACK_CLUSTER_CLIENT)
+#define CHIP_PRINTCLUSTER_MEDIA_PLAYBACK_CLUSTER { ZCL_MEDIA_PLAYBACK_CLUSTER_ID, 1286, "Media Playback" },
+#else
+#define CHIP_PRINTCLUSTER_MEDIA_PLAYBACK_CLUSTER
+#endif
+
#if defined(ZCL_USING_LOW_POWER_CLUSTER_SERVER) || defined(ZCL_USING_LOW_POWER_CLUSTER_CLIENT)
#define CHIP_PRINTCLUSTER_LOW_POWER_CLUSTER { ZCL_LOW_POWER_CLUSTER_ID, 1288, "Low Power" },
#else
#define CHIP_PRINTCLUSTER_LOW_POWER_CLUSTER
#endif
+#if defined(ZCL_USING_CONTENT_LAUNCH_CLUSTER_SERVER) || defined(ZCL_USING_CONTENT_LAUNCH_CLUSTER_CLIENT)
+#define CHIP_PRINTCLUSTER_CONTENT_LAUNCH_CLUSTER { ZCL_CONTENT_LAUNCH_CLUSTER_ID, 1290, "Content Launch" },
+#else
+#define CHIP_PRINTCLUSTER_CONTENT_LAUNCH_CLUSTER
+#endif
+
#if defined(ZCL_USING_APPLICATION_BASIC_CLUSTER_SERVER) || defined(ZCL_USING_APPLICATION_BASIC_CLUSTER_CLIENT)
#define CHIP_PRINTCLUSTER_APPLICATION_BASIC_CLUSTER { ZCL_APPLICATION_BASIC_CLUSTER_ID, 1293, "Application Basic" },
#else
#define CHIP_PRINTCLUSTER_BINDING_CLUSTER
#endif
-#if defined(ZCL_USING_MEDIA_PLAYBACK_CLUSTER_SERVER) || defined(ZCL_USING_MEDIA_PLAYBACK_CLUSTER_CLIENT)
-#define CHIP_PRINTCLUSTER_MEDIA_PLAYBACK_CLUSTER { ZCL_MEDIA_PLAYBACK_CLUSTER_ID, 61441, "Media Playback" },
-#else
-#define CHIP_PRINTCLUSTER_MEDIA_PLAYBACK_CLUSTER
-#endif
-
-#if defined(ZCL_USING_CONTENT_LAUNCH_CLUSTER_SERVER) || defined(ZCL_USING_CONTENT_LAUNCH_CLUSTER_CLIENT)
-#define CHIP_PRINTCLUSTER_CONTENT_LAUNCH_CLUSTER { ZCL_CONTENT_LAUNCH_CLUSTER_ID, 61442, "Content Launch" },
-#else
-#define CHIP_PRINTCLUSTER_CONTENT_LAUNCH_CLUSTER
-#endif
-
#if defined(ZCL_USING_GROUP_KEY_MANAGEMENT_CLUSTER_SERVER) || defined(ZCL_USING_GROUP_KEY_MANAGEMENT_CLUSTER_CLIENT)
#define CHIP_PRINTCLUSTER_GROUP_KEY_MANAGEMENT_CLUSTER { ZCL_GROUP_KEY_MANAGEMENT_CLUSTER_ID, 61444, "Group Key Management" },
#else
CHIP_PRINTCLUSTER_IAS_ZONE_CLUSTER \
CHIP_PRINTCLUSTER_IAS_ACE_CLUSTER \
CHIP_PRINTCLUSTER_IAS_WD_CLUSTER \
+ CHIP_PRINTCLUSTER_MEDIA_PLAYBACK_CLUSTER \
CHIP_PRINTCLUSTER_LOW_POWER_CLUSTER \
+ CHIP_PRINTCLUSTER_CONTENT_LAUNCH_CLUSTER \
CHIP_PRINTCLUSTER_APPLICATION_BASIC_CLUSTER \
CHIP_PRINTCLUSTER_GENERIC_TUNNEL_CLUSTER \
CHIP_PRINTCLUSTER_BACNET_PROTOCOL_TUNNEL_CLUSTER \
CHIP_PRINTCLUSTER_DIAGNOSTICS_CLUSTER \
CHIP_PRINTCLUSTER_ZLL_COMMISSIONING_CLUSTER \
CHIP_PRINTCLUSTER_BINDING_CLUSTER \
- CHIP_PRINTCLUSTER_MEDIA_PLAYBACK_CLUSTER \
- CHIP_PRINTCLUSTER_CONTENT_LAUNCH_CLUSTER \
CHIP_PRINTCLUSTER_GROUP_KEY_MANAGEMENT_CLUSTER \
CHIP_PRINTCLUSTER_SAMPLE_MFG_SPECIFIC_CLUSTER \
CHIP_PRINTCLUSTER_SAMPLE_MFG_SPECIFIC_CLUSTER_2 \
// Acknowledgement is done after handling the buffers to allow the
// application processing to throttle flow.
uint16_t ackLength = mRcvQueue->TotalLength();
- OnDataReceived(this, std::move(mRcvQueue));
+ INET_ERROR err = OnDataReceived(this, std::move(mRcvQueue));
+ if (err != INET_NO_ERROR)
+ {
+ DoClose(err, false);
+ return;
+ }
AckReceive(ackLength);
}
/**
* @brief Type of data reception event handling function.
*
- * @param[in] endPoint The TCP endpoint associated with the event.
- * @param[in] data The data received.
+ * @param[in] endPoint The TCP endpoint associated with the event.
+ * @param[in] data The data received.
+ *
+ * @retval INET_NO_ERROR If the received data can be handled by higher layers.
+ * @retval other If the received data can not be used, and higher layers will not see it.
*
* @details
* Provide a function of this type to the \c OnDataReceived delegate
* member to process data reception events on \c endPoint where \c data
* is the message text received.
*
- * A data reception event handler must acknowledge data processed using
- * the \c AckReceive method. The \c Free method on the data buffer must
- * also be invoked unless the \c PutBackReceivedData is used instead.
+ * If this function returns an error, the connection will be closed, since higher layers
+ * are not able to process the data for a better response.
*/
- typedef void (*OnDataReceivedFunct)(TCPEndPoint * endPoint, chip::System::PacketBufferHandle data);
+ typedef INET_ERROR (*OnDataReceivedFunct)(TCPEndPoint * endPoint, chip::System::PacketBufferHandle data);
/**
* The endpoint's message text reception event handling function delegate.
static void HandleTCPDataSent(TCPEndPoint * aEndPoint, uint16_t len) {}
-static void HandleTCPDataReceived(TCPEndPoint * aEndPoint, PacketBufferHandle aBuffer)
+static INET_ERROR HandleTCPDataReceived(TCPEndPoint * aEndPoint, PacketBufferHandle aBuffer)
{
const uint32_t lFirstValueReceived = sTestState.mStats.mReceive.mActual;
const uint8_t lFirstValue = uint8_t(lFirstValueReceived);
{
SetStatusFailed(sTestState.mStatus);
}
+ return lStatus;
}
static void HandleTCPAcceptError(TCPEndPoint * aEndPoint, INET_ERROR aError)
#include <core/CHIPEncoding.h>
#include <core/CHIPTLV.h>
#include <support/CodeUtils.h>
-#include <support/ReturnMacros.h>
namespace chip {
namespace ASN1 {
#include <core/CHIPTLV.h>
#include <support/CodeUtils.h>
-#include <support/ReturnMacros.h>
#include <stdint.h>
#include <core/CHIPCore.h>
#include <support/CodeUtils.h>
-#include <support/ReturnMacros.h>
namespace chip {
/**
* @brief
- * Called when a value is returned from the storage.
- * This is useful for AsyncGetKeyValue() API call.
- *
- * @param[in] key Key for which the value is being returned
- * @param[in] value Value or nullptr if not found.
- */
- virtual void OnPersistentStorageValue(const char * key, const char * value) = 0;
-
- /**
- * @brief
* Called on completion of an operation in PersistentStorageDelegate API
*
* @param[in] key Key for which the status is being returned
/**
* @brief
- * Lookup the key and call delegate object with it's stringified value
- *
- * @param[in] key Key to lookup
- */
- virtual void AsyncGetKeyValue(const char * key) = 0;
-
- /**
- * @brief
* This is a synchronous Get API, where the value is returned via the output
* buffer. This API should be used sparingly, since it may block for
* some duration.
#include <core/CHIPTLVDebug.hpp>
#include <core/CHIPTLVUtilities.hpp>
#include <support/CodeUtils.h>
-#include <support/ReturnMacros.h>
#include <support/logging/CHIPLogging.h>
namespace chip {
#include <core/CHIPTLV.h>
#include <support/CHIPMem.h>
#include <support/CodeUtils.h>
-#include <support/ReturnMacros.h>
#include <support/SafeInt.h>
namespace chip {
#include <core/CHIPEncoding.h>
#include <core/CHIPTLV.h>
#include <support/CodeUtils.h>
-#include <support/ReturnMacros.h>
namespace chip {
namespace TLV {
#include <support/CHIPMem.h>
#include <support/CodeUtils.h>
-#include <support/ReturnMacros.h>
#include <support/SafeInt.h>
#include <stdarg.h>
#pragma once
+#include <cstdint>
+
namespace chip {
//
// CHIP Vendor Identifiers (16 bits max)
//
-enum ChipVendorId
+enum VendorId : uint16_t
{
- kChipVendor_Common = 0x0000,
- kChipVendor_NestLabs = 0x235A,
- kChipVendor_NotSpecified = 0xFFFF
+ Common = 0x0000u,
+ NestLabs = 0x235Au,
+ NotSpecified = 0xFFFFu
};
} // namespace chip
class Optional
{
public:
- Optional() : mHasValue(false) {}
+ constexpr Optional() : mHasValue(false) {}
explicit Optional(const T & value) : mValue(value), mHasValue(true) {}
constexpr Optional(const Optional & other) = default;
* NOTE: Manually implemented instead of =default since other::mValue may not be initialized
* if it has no value.
*/
- Optional & operator=(const Optional & other)
+ constexpr Optional & operator=(const Optional & other)
{
if (other.HasValue())
{
}
/** Make the optional contain a specific value */
- void SetValue(const T & value)
+ constexpr void SetValue(const T & value)
{
mValue = value;
mHasValue = true;
}
/** Invalidate the value inside the optional. Optional now has no value */
- void ClearValue() { mHasValue = false; }
+ constexpr void ClearValue() { mHasValue = false; }
/** Gets the current value of the optional. Valid IFF `HasValue`. */
const T & Value() const
}
/** Checks if the optional contains a value or not */
- bool HasValue() const { return mHasValue; }
+ constexpr bool HasValue() const { return mHasValue; }
/** Comparison operator, handling missing values. */
bool operator==(const Optional & other) const
#include <support/CHIPMem.h>
#include <support/CodeUtils.h>
#include <support/RandUtils.h>
-#include <support/ReturnMacros.h>
#include <support/ScopedBuffer.h>
#include <support/UnitTestRegistration.h>
#include <inttypes.h>
#include <stdio.h>
+#include "ServiceNaming.h"
#include <mdns/minimal/ResponseSender.h>
#include <mdns/minimal/Server.h>
#include <mdns/minimal/core/FlatAllocatedQName.h>
#include <mdns/minimal/responders/Txt.h>
#include <support/CHIPMem.h>
#include <support/RandUtils.h>
-#include <support/ReturnMacros.h>
#include <support/StringBuilder.h>
// Enable detailed mDNS logging for received queries
char uniqueName[64] = "";
/// need to set server name
- size_t len = snprintf(uniqueName, sizeof(uniqueName), "%" PRIX64 "-%" PRIX64, params.GetFabricId(), params.GetNodeId());
- if (len >= sizeof(uniqueName))
- {
- ChipLogError(Discovery, "Failed to allocate QNames.");
- return CHIP_ERROR_NO_MEMORY;
- }
+ ReturnErrorOnFailure(MakeInstanceName(uniqueName, sizeof(uniqueName), params.GetFabricId(), params.GetNodeId()));
FullQName operationalServiceName = AllocateQName("_chip", "_tcp", "local");
FullQName operationalServerName = AllocateQName(uniqueName, "_chip", "_tcp", "local");
"${chip_root}/src/lib/support",
]
- sources = [ "Advertiser.h" ]
+ sources = [
+ "Advertiser.h",
+ "Resolver.h",
+ "ServiceNaming.cpp",
+ "ServiceNaming.h",
+ ]
if (chip_mdns == "none") {
sources += [
#include <inttypes.h>
+#include "ServiceNaming.h"
#include "lib/core/CHIPSafeCasts.h"
#include "lib/mdns/platform/Mdns.h"
-#include "lib/support/ReturnMacros.h"
#include "lib/support/logging/CHIPLogging.h"
#include "platform/CHIPDeviceConfig.h"
#include "platform/CHIPDeviceLayer.h"
mOperationalAdvertisingParams = params;
// TODO: There may be multilple device/fabrid ids after multi-admin.
- snprintf(service.mName, sizeof(service.mName), "%08X%08X-%08X%08X", (uint32_t)(params.GetNodeId() >> 32),
- (uint32_t)(params.GetNodeId()), (uint32_t)(params.GetFabricId() >> 32), (uint32_t)(params.GetFabricId()));
+
+ ReturnErrorOnFailure(MakeInstanceName(service.mName, sizeof(service.mName), params.GetFabricId(), params.GetNodeId()));
strncpy(service.mType, "_chip", sizeof(service.mType));
service.mProtocol = MdnsServiceProtocol::kMdnsProtocolTcp;
service.mPort = CHIP_PORT;
MdnsService service;
- snprintf(service.mName, sizeof(service.mName), "%" PRIX64 "-%" PRIX64, nodeId, fabricId);
+ ReturnErrorOnFailure(MakeInstanceName(service.mName, sizeof(service.mName), fabricId, nodeId));
strncpy(service.mType, "_chip", sizeof(service.mType));
service.mProtocol = MdnsServiceProtocol::kMdnsProtocolTcp;
service.mAddressType = type;
--- /dev/null
+/*
+ *
+ * Copyright (c) 2021 Project CHIP Authors
+ *
+ * Licensed under the Apache License, Version 2.0 (the "License");
+ * you may not use this file except in compliance with the License.
+ * You may obtain a copy of the License at
+ *
+ * http://www.apache.org/licenses/LICENSE-2.0
+ *
+ * Unless required by applicable law or agreed to in writing, software
+ * distributed under the License is distributed on an "AS IS" BASIS,
+ * WITHOUT WARRANTIES OR CONDITIONS OF ANY KIND, either express or implied.
+ * See the License for the specific language governing permissions and
+ * limitations under the License.
+ */
+
+#include "ServiceNaming.h"
+
+#include <support/CodeUtils.h>
+
+#include <cstdio>
+#include <inttypes.h>
+
+namespace chip {
+namespace Mdns {
+
+CHIP_ERROR MakeInstanceName(char * buffer, size_t bufferLen, uint64_t fabricId, uint64_t nodeId)
+{
+ constexpr size_t kServiceNameLen = 16 + 1 + 16; // 2 * 64-bit value in HEX + hyphen
+
+ ReturnErrorCodeIf(bufferLen <= kServiceNameLen, CHIP_ERROR_BUFFER_TOO_SMALL);
+
+ snprintf(buffer, bufferLen, "%08" PRIX32 "%08" PRIX32 "-%08" PRIX32 "%08" PRIX32, static_cast<uint32_t>(fabricId >> 32),
+ static_cast<uint32_t>(fabricId), static_cast<uint32_t>(nodeId >> 32), static_cast<uint32_t>(nodeId));
+
+ return CHIP_NO_ERROR;
+}
+
+} // namespace Mdns
+} // namespace chip
--- /dev/null
+/*
+ *
+ * Copyright (c) 2021 Project CHIP Authors
+ *
+ * Licensed under the Apache License, Version 2.0 (the "License");
+ * you may not use this file except in compliance with the License.
+ * You may obtain a copy of the License at
+ *
+ * http://www.apache.org/licenses/LICENSE-2.0
+ *
+ * Unless required by applicable law or agreed to in writing, software
+ * distributed under the License is distributed on an "AS IS" BASIS,
+ * WITHOUT WARRANTIES OR CONDITIONS OF ANY KIND, either express or implied.
+ * See the License for the specific language governing permissions and
+ * limitations under the License.
+ */
+
+#pragma once
+
+#include <core/CHIPError.h>
+
+#include <cstddef>
+#include <cstdint>
+
+namespace chip {
+namespace Mdns {
+
+CHIP_ERROR MakeInstanceName(char * buffer, size_t bufferLen, uint64_t fabricId, uint64_t nodeId);
+
+} // namespace Mdns
+} // namespace chip
#include "QueryReplyFilter.h"
-#include <support/ReturnMacros.h>
#include <system/SystemClock.h>
#define RETURN_IF_ERROR(err) \
#include <utility>
#include <mdns/minimal/core/DnsHeader.h>
-#include <support/ReturnMacros.h>
namespace mdns {
namespace Minimal {
"PersistedCounter.h",
"Pool.cpp",
"Pool.h",
+ "PrivateHeap.cpp",
+ "PrivateHeap.h",
"RandUtils.cpp",
"RandUtils.h",
- "ReturnMacros.h",
"SafeInt.h",
"SerializableIntegerSet.cpp",
"SerializableIntegerSet.h",
static_assert(sizeof(StorageType) >= sizeof(FlagsEnum), "All flags should fit in the storage type");
using IntegerType = StorageType;
- BitFlags() : mValue(0) {}
+ constexpr BitFlags() : mValue(0) {}
BitFlags(const BitFlags & other) = default;
BitFlags & operator=(const BitFlags &) = default;
*
* @param flag Typed flag(s) to set. Any flags not in @a v are unaffected.
*/
- BitFlags & Set(FlagsEnum flag)
+ constexpr BitFlags & Set(FlagsEnum flag)
{
mValue |= static_cast<IntegerType>(flag);
return *this;
* @param flag Typed flag(s) to set or clear. Any flags not in @a flag are unaffected.
* @param isSet If true, set the flag; if false, clear it.
*/
- BitFlags & Set(FlagsEnum flag, bool isSet) { return isSet ? Set(flag) : Clear(flag); }
+ constexpr BitFlags & Set(FlagsEnum flag, bool isSet) { return isSet ? Set(flag) : Clear(flag); }
/**
* Clear flag(s).
*
* @param flag Typed flag(s) to clear. Any flags not in @a flag are unaffected.
*/
- BitFlags & Clear(FlagsEnum flag)
+ constexpr BitFlags & Clear(FlagsEnum flag)
{
mValue &= static_cast<IntegerType>(~static_cast<IntegerType>(flag));
return *this;
#define IgnoreUnusedVariable(aVariable) ((void) (aVariable))
/**
+ * @def ReturnErrorOnFailure(expr)
+ *
+ * @brief
+ * Returns the error code if the expression returns something different
+ * than CHIP_NO_ERROR.
+ *
+ * Example usage:
+ *
+ * @code
+ * ReturnErrorOnFailure(channel->SendMsg(msg));
+ * @endcode
+ *
+ * @param[in] expr A scalar expression to be evaluated against CHIP_NO_ERROR.
+ */
+#define ReturnErrorOnFailure(expr) \
+ do \
+ { \
+ CHIP_ERROR __err = (expr); \
+ if (__err != CHIP_NO_ERROR) \
+ { \
+ return __err; \
+ } \
+ } while (false)
+
+/**
+ * @def ReturnOnFailure(expr)
+ *
+ * @brief
+ * Returns if the expression returns something different than CHIP_NO_ERROR
+ *
+ * Example usage:
+ *
+ * @code
+ * ReturnOnFailure(channel->SendMsg(msg));
+ * @endcode
+ *
+ * @param[in] expr A scalar expression to be evaluated against CHIP_NO_ERROR.
+ */
+#define ReturnOnFailure(expr) \
+ do \
+ { \
+ CHIP_ERROR __err = (expr); \
+ if (__err != CHIP_NO_ERROR) \
+ { \
+ return; \
+ } \
+ } while (false)
+
+/**
+ * @def VerifyOrReturn(expr, ...)
+ *
+ * @brief
+ * Returns from the void function if expression evaluates to false
+ *
+ * Example usage:
+ *
+ * @code
+ * VerifyOrReturn(param != nullptr, LogError("param is nullptr"));
+ * @endcode
+ *
+ * @param[in] expr A Boolean expression to be evaluated.
+ */
+#define VerifyOrReturn(expr, ...) \
+ do \
+ { \
+ if (!(expr)) \
+ { \
+ __VA_ARGS__; \
+ return; \
+ } \
+ } while (false)
+
+/**
+ * @def VerifyOrReturnError(expr, code)
+ *
+ * @brief
+ * Returns a specified error code if expression evaluates to false
+ *
+ * Example usage:
+ *
+ * @code
+ * VerifyOrReturnError(param != nullptr, CHIP_ERROR_INVALID_ARGUMENT);
+ * @endcode
+ *
+ * @param[in] expr A Boolean expression to be evaluated.
+ * @param[in] code A value to return if @a expr is false.
+ */
+#define VerifyOrReturnError(expr, code) \
+ do \
+ { \
+ if (!(expr)) \
+ { \
+ return code; \
+ } \
+ } while (false)
+
+/**
+ * @def ReturnErrorCodeIf(expr, code)
+ *
+ * @brief
+ * Returns a specified error code if expression evaluates to true
+ *
+ * Example usage:
+ *
+ * @code
+ * ReturnErrorCodeIf(state == kInitialized, CHIP_NO_ERROR);
+ * ReturnErrorCodeIf(state == kInitialized, CHIP_ERROR_INVALID_STATE);
+ * @endcode
+ *
+ * @param[in] expr A Boolean expression to be evaluated.
+ * @param[in] code A value to return if @a expr is false.
+ */
+#define ReturnErrorCodeIf(expr, code) \
+ do \
+ { \
+ if (expr) \
+ { \
+ return code; \
+ } \
+ } while (false)
+
+/**
* @def SuccessOrExit(aStatus)
*
* @brief
--- /dev/null
+/*
+ *
+ * Copyright (c) 2021 Project CHIP Authors
+ * Copyright 2019 Google Inc. All Rights Reserved.
+ *
+ * Licensed under the Apache License, Version 2.0 (the "License");
+ * you may not use this file except in compliance with the License.
+ * You may obtain a copy of the License at
+ *
+ * http://www.apache.org/licenses/LICENSE-2.0
+ *
+ * Unless required by applicable law or agreed to in writing, software
+ * distributed under the License is distributed on an "AS IS" BASIS,
+ * WITHOUT WARRANTIES OR CONDITIONS OF ANY KIND, either express or implied.
+ * See the License for the specific language governing permissions and
+ * limitations under the License.
+ */
+
+#include "PrivateHeap.h"
+
+#include <support/CodeUtils.h>
+#include <support/logging/CHIPLogging.h>
+
+namespace {
+
+constexpr uint32_t kInvalidHeapBlockSize = 0xFFFFFFFF;
+constexpr int32_t kHeapBlockInUse = 0x01;
+constexpr int32_t kHeapBlockFree = 0x10;
+constexpr int32_t kInvalidHeaderState = 0xff;
+
+using internal::PrivateHeapBlockHeader;
+
+// this makes life easier, no need to add align offsets.
+static_assert(sizeof(PrivateHeapBlockHeader) % kPrivateHeapAllocationAlignment == 0, "Invalid block size.");
+
+uint32_t ComputeHeapBlockChecksum(const PrivateHeapBlockHeader * header)
+{
+ uint32_t checksum = header->prevBytes;
+ checksum *= 31;
+ checksum += header->nextBytes;
+ checksum *= 31;
+ checksum += header->state;
+ return checksum;
+}
+
+// Advances the heap block to the next value
+PrivateHeapBlockHeader * NextHeader(PrivateHeapBlockHeader * start)
+{
+ if (start->nextBytes == kInvalidHeapBlockSize)
+ {
+ return nullptr;
+ }
+
+ if (start->checksum != ComputeHeapBlockChecksum(start))
+ {
+ ChipLogError(Support, "Corrupted heap: checksum is invalid");
+ chipDie();
+ }
+
+ return reinterpret_cast<PrivateHeapBlockHeader *>(reinterpret_cast<char *>(start) + sizeof(PrivateHeapBlockHeader) +
+ start->nextBytes);
+}
+
+// Advances the heap block to the previous value
+PrivateHeapBlockHeader * PreviousHeader(PrivateHeapBlockHeader * start)
+{
+ if (start->prevBytes == kInvalidHeapBlockSize)
+ {
+ return nullptr;
+ }
+
+ if (start->checksum != ComputeHeapBlockChecksum(start))
+ {
+ ChipLogError(Support, "Corrupted heap: checksum is invalid");
+ chipDie();
+ }
+
+ return reinterpret_cast<PrivateHeapBlockHeader *>(reinterpret_cast<char *>(start) - sizeof(PrivateHeapBlockHeader) -
+ start->prevBytes);
+}
+
+void ValidateHeader(const PrivateHeapBlockHeader * header)
+{
+ if (header->state != kHeapBlockFree && header->state != kHeapBlockInUse)
+ {
+ ChipLogError(Support, "Invalid header state (neither free nor in use) at %p", header);
+ chipDie();
+ }
+
+ if (header->checksum != ComputeHeapBlockChecksum(header))
+ {
+ ChipLogError(Support, "Corrupted heap: checksum is invalid at %p", header);
+ chipDie();
+ }
+}
+
+} // namespace
+
+extern "C" void PrivateHeapInit(void * heap, size_t size)
+{
+ if (heap == nullptr)
+ {
+ ChipLogError(Support, "Cannot initialize null heap");
+ chipDie();
+ }
+
+ if (size < 2 * sizeof(PrivateHeapBlockHeader))
+ {
+ ChipLogError(Support, "Insufficient space in private heap");
+ chipDie();
+ }
+
+ if (reinterpret_cast<uintptr_t>(heap) % kPrivateHeapAllocationAlignment != 0)
+ {
+ ChipLogError(Support, "Invalid alignment for private heap initialization");
+ chipDie();
+ }
+
+ PrivateHeapBlockHeader * header = reinterpret_cast<PrivateHeapBlockHeader *>(heap);
+
+ header->prevBytes = kInvalidHeapBlockSize;
+ header->nextBytes = static_cast<uint32_t>(size - 2 * sizeof(PrivateHeapBlockHeader));
+ header->state = kHeapBlockFree;
+ header->checksum = ComputeHeapBlockChecksum(header);
+
+ header = NextHeader(header);
+ header->nextBytes = kInvalidHeapBlockSize;
+ header->prevBytes = static_cast<uint32_t>(size - 2 * sizeof(PrivateHeapBlockHeader));
+ header->state = kHeapBlockFree; // does not matter really
+ header->checksum = ComputeHeapBlockChecksum(header);
+}
+
+extern "C" void * PrivateHeapAlloc(void * heap, size_t size)
+{
+ PrivateHeapBlockHeader * header = reinterpret_cast<PrivateHeapBlockHeader *>(heap);
+
+ // we allocate aligned, no matter what
+ if (size % kPrivateHeapAllocationAlignment != 0)
+ {
+ size += kPrivateHeapAllocationAlignment - (size % kPrivateHeapAllocationAlignment);
+ }
+
+ for (; header != nullptr; header = NextHeader(header))
+ {
+ ValidateHeader(header);
+
+ if (header->nextBytes == kInvalidHeapBlockSize)
+ {
+ continue;
+ }
+
+ if (header->state != kHeapBlockFree)
+ {
+ continue; // not free
+ }
+
+ if (header->nextBytes < size)
+ {
+ continue; // insufficient space
+ }
+
+ if (header->nextBytes - size < sizeof(PrivateHeapBlockHeader) + kPrivateHeapAllocationAlignment)
+ {
+ // allocate the entire block
+ header->state = kHeapBlockInUse;
+ header->checksum = ComputeHeapBlockChecksum(header);
+ }
+ else
+ {
+ // splits the block into two
+ //
+ // +--------+ +--------+ +------+
+ // | header | ---> | middle | ---> | next |
+ // +--------+ +--------+ +------+
+ //
+ PrivateHeapBlockHeader * next = NextHeader(header);
+ PrivateHeapBlockHeader * middle =
+ reinterpret_cast<PrivateHeapBlockHeader *>(reinterpret_cast<char *>(header + 1) + size);
+
+ // middle is a new block
+ middle->nextBytes = static_cast<uint32_t>(header->nextBytes - size - sizeof(PrivateHeapBlockHeader));
+ middle->prevBytes = static_cast<uint32_t>(size);
+ middle->state = kHeapBlockFree;
+ middle->checksum = ComputeHeapBlockChecksum(middle);
+
+ // fix up the header
+ header->nextBytes = static_cast<uint32_t>(size);
+ header->state = kHeapBlockInUse;
+ header->checksum = ComputeHeapBlockChecksum(header);
+
+ // fix up the final block
+ if (next != nullptr)
+ {
+ next->prevBytes = middle->nextBytes;
+ next->checksum = ComputeHeapBlockChecksum(next);
+ }
+ }
+
+ // we can now use the header
+ return header + 1; // data right after the header
+ }
+
+ // no space found
+ return nullptr;
+}
+
+extern "C" void PrivateHeapFree(void * ptr)
+{
+ if (ptr == nullptr)
+ {
+ // freeing NULL pointers is always acceptable and a noop
+ return;
+ }
+
+ PrivateHeapBlockHeader * header =
+ reinterpret_cast<PrivateHeapBlockHeader *>(static_cast<char *>(ptr) - sizeof(PrivateHeapBlockHeader));
+
+ ValidateHeader(header);
+ header->state = kHeapBlockFree;
+ header->checksum = ComputeHeapBlockChecksum(header);
+
+ // Merge with previous
+ //
+ // +-------+ +--------+
+ // | other | ----- nextBytes -----> | header |
+ // +-------+ +--------+
+ //
+ PrivateHeapBlockHeader * other = PreviousHeader(header);
+ if (other != nullptr && other->state == kHeapBlockFree && other->nextBytes != kInvalidHeapBlockSize)
+ {
+ // includes the free bytes in this block in the previous
+ other->nextBytes += static_cast<uint32_t>(header->nextBytes + sizeof(PrivateHeapBlockHeader));
+ other->checksum = ComputeHeapBlockChecksum(other);
+ header->state = kInvalidHeaderState;
+ header = other;
+
+ // fixes up the next block
+ other = NextHeader(header);
+ if (other != nullptr)
+ {
+ other->prevBytes = header->nextBytes;
+ other->checksum = ComputeHeapBlockChecksum(other);
+ }
+ }
+
+ // Merge with next
+ //
+ // +--------+ +-------+
+ // | header | ----- nextBytes -----> | other |
+ // +--------+ +-------+
+ //
+ other = NextHeader(header);
+ if (other != nullptr && other->state == kHeapBlockFree && other->nextBytes != kInvalidHeapBlockSize)
+ {
+ // includes the free bytes in the next block
+ other->state = kInvalidHeaderState;
+ header->nextBytes += static_cast<uint32_t>(other->nextBytes + sizeof(PrivateHeapBlockHeader));
+ header->checksum = ComputeHeapBlockChecksum(header);
+
+ // fixes up the next block
+ other = NextHeader(header);
+ if (other != nullptr)
+ {
+ other->prevBytes = header->nextBytes;
+ other->checksum = ComputeHeapBlockChecksum(other);
+ }
+ }
+}
+
+extern "C" void PrivateHeapDump(void * top)
+{
+ PrivateHeapBlockHeader * header = reinterpret_cast<PrivateHeapBlockHeader *>(top);
+
+ ChipLogProgress(Support, "========= HEAP ===========");
+ while (header->nextBytes != kInvalidHeapBlockSize)
+ {
+ intptr_t offset = reinterpret_cast<char *>(header) - reinterpret_cast<char *>(top);
+ ChipLogProgress(Support, " %ld: size: %d, state: %d", static_cast<long>(offset), static_cast<int>(header->nextBytes),
+ static_cast<int>(header->state));
+
+ header = NextHeader(header);
+ }
+}
--- /dev/null
+/*
+ *
+ * Copyright (c) 2021 Project CHIP Authors
+ * Copyright 2019 Google Inc. All Rights Reserved.
+ *
+ * Licensed under the Apache License, Version 2.0 (the "License");
+ * you may not use this file except in compliance with the License.
+ * You may obtain a copy of the License at
+ *
+ * http://www.apache.org/licenses/LICENSE-2.0
+ *
+ * Unless required by applicable law or agreed to in writing, software
+ * distributed under the License is distributed on an "AS IS" BASIS,
+ * WITHOUT WARRANTIES OR CONDITIONS OF ANY KIND, either express or implied.
+ * See the License for the specific language governing permissions and
+ * limitations under the License.
+ */
+
+#pragma once
+
+#include <stddef.h>
+#include <stdint.h>
+#include <sys/types.h>
+
+#include <cstddef>
+#include <type_traits>
+
+#ifdef __cplusplus
+extern "C" {
+#endif // __cplusplus
+
+// Initializes the heap (set start and end blocks)
+void PrivateHeapInit(void * heap, size_t size);
+
+// Allocates a new block on the specified heap
+void * PrivateHeapAlloc(void * heap, size_t size);
+
+// Marks the specified block as free
+void PrivateHeapFree(void * ptr);
+
+void PrivateHeapDump(void * ptr);
+
+#ifdef __cplusplus
+} // extern "C"
+
+namespace internal {
+
+// Heap structure, exposed for tests
+//
+// +---------+---------+-----+ +---------+-----------+
+// | prev: 0 | next: n | ... | ....<n_bytes> .... | prev: n | next: ... |
+// +---------+---------+-----+ +---------+-----------+
+//
+struct PrivateHeapBlockHeader
+{
+ uint32_t prevBytes;
+ uint32_t nextBytes;
+ uint32_t state;
+ uint32_t checksum; // super-basic attempt to detect errors
+};
+
+} // namespace internal
+
+constexpr size_t kPrivateHeapAllocationAlignment = std::alignment_of<max_align_t>::value;
+
+#endif // ifdef __cplusplus
+++ /dev/null
-/*
- *
- * Copyright (c) 2020 Project CHIP Authors
- *
- * Licensed under the Apache License, Version 2.0 (the "License");
- * you may not use this file except in compliance with the License.
- * You may obtain a copy of the License at
- *
- * http://www.apache.org/licenses/LICENSE-2.0
- *
- * Unless required by applicable law or agreed to in writing, software
- * distributed under the License is distributed on an "AS IS" BASIS,
- * WITHOUT WARRANTIES OR CONDITIONS OF ANY KIND, either express or implied.
- * See the License for the specific language governing permissions and
- * limitations under the License.
- */
-
-#pragma once
-
-#include <core/CHIPError.h>
-
-/// Returns the error code if the expression returns something different
-/// than CHIP_NO_ERROR
-///
-/// Use like:
-/// ReturnErrorOnFailure(channel->SendMsg(msg));
-#define ReturnErrorOnFailure(expr) \
- do \
- { \
- CHIP_ERROR __err = (expr); \
- if (__err != CHIP_NO_ERROR) \
- { \
- return __err; \
- } \
- } while (false)
-
-/// Returns if the expression returns something different than CHIP_NO_ERROR
-///
-/// Use like:
-/// ReturnOnFailure(channel->SendMsg(msg));
-#define ReturnOnFailure(expr) \
- do \
- { \
- CHIP_ERROR __err = (expr); \
- if (__err != CHIP_NO_ERROR) \
- { \
- return; \
- } \
- } while (false)
-
-/// Returns from the void function if expression evaluates to false
-///
-/// Use like:
-/// VerifyOrReturn(param != nullptr, LogError("param is nullptr"));
-#define VerifyOrReturn(expr, ...) \
- do \
- { \
- if (!(expr)) \
- { \
- __VA_ARGS__; \
- return; \
- } \
- } while (false)
-
-/// Returns a specified error code if expression evaluates to false
-///
-/// Use like:
-/// VerifyOrReturnError(param != nullptr, CHIP_ERROR_INVALID_ARGUMENT);
-#define VerifyOrReturnError(expr, code) \
- do \
- { \
- if (!(expr)) \
- { \
- return code; \
- } \
- } while (false)
-
-/// Returns a specified error code if expression evaluates to true
-///
-/// Use like:
-/// ReturnErrorCodeIf(state == kInitialized, CHIP_NO_ERROR);
-/// ReturnErrorCodeIf(state == kInitialized, CHIP_ERROR_INVALID_STATE);
-#define ReturnErrorCodeIf(expr, code) \
- do \
- { \
- if (expr) \
- { \
- return code; \
- } \
- } while (false)
"TestCHIPMem.cpp",
"TestErrorStr.cpp",
"TestPool.cpp",
+ "TestPrivateHeap.cpp",
"TestSafeInt.cpp",
"TestSafeString.cpp",
"TestScopedBuffer.cpp",
--- /dev/null
+/*
+ *
+ * Copyright (c) 2021 Project CHIP Authors
+ * Copyright 2019 Google Inc. All Rights Reserved.
+ *
+ * Licensed under the Apache License, Version 2.0 (the "License");
+ * you may not use this file except in compliance with the License.
+ * You may obtain a copy of the License at
+ *
+ * http://www.apache.org/licenses/LICENSE-2.0
+ *
+ * Unless required by applicable law or agreed to in writing, software
+ * distributed under the License is distributed on an "AS IS" BASIS,
+ * WITHOUT WARRANTIES OR CONDITIONS OF ANY KIND, either express or implied.
+ * See the License for the specific language governing permissions and
+ * limitations under the License.
+ */
+
+#include <support/PrivateHeap.h>
+#include <support/UnitTestRegistration.h>
+
+#include <string.h>
+
+#include <nlunit-test.h>
+
+namespace {
+
+constexpr size_t kBlockHeaderSize = sizeof(internal::PrivateHeapBlockHeader);
+
+// Splitting block tests assume we know the size
+static_assert(kBlockHeaderSize == 16, "Test assumes block size of 16");
+
+// helper class for allocating things
+template <size_t kSize>
+class PrivateHeapAllocator
+{
+public:
+ PrivateHeapAllocator() { PrivateHeapInit(mHeap.buffer, kSize); }
+ void * HeapAlloc(size_t size) { return PrivateHeapAlloc(mHeap.buffer, size); }
+ void HeapFree(void * buffer) { PrivateHeapFree(buffer); }
+
+private:
+ struct alignas(kPrivateHeapAllocationAlignment)
+ {
+ uint8_t buffer[kSize];
+ } mHeap;
+};
+
+void SingleHeapAllocAndFree(nlTestSuite * inSuite, void * inContext)
+{
+ PrivateHeapAllocator<16 + 2 * kBlockHeaderSize> allocator;
+
+ NL_TEST_ASSERT(inSuite, nullptr == allocator.HeapAlloc(17)); // insufficient size
+ void * ptr = allocator.HeapAlloc(16);
+ NL_TEST_ASSERT(inSuite, nullptr != ptr);
+ NL_TEST_ASSERT(inSuite, nullptr == allocator.HeapAlloc(1)); // insufficient size
+ memset(ptr, 0xab, 16);
+ allocator.HeapFree(ptr);
+
+ // allocate different sizes on this heap, see how that goes
+ for (size_t i = 1; i < 17; ++i)
+ {
+ ptr = allocator.HeapAlloc(i);
+ NL_TEST_ASSERT(inSuite, nullptr != ptr);
+ NL_TEST_ASSERT(inSuite, nullptr == allocator.HeapAlloc(17 - i)); // insufficient size
+ allocator.HeapFree(ptr);
+ }
+}
+
+void SplitHeapAllocAndFree(nlTestSuite * inSuite, void * inContext)
+{
+ PrivateHeapAllocator<128> allocator;
+ // allocator state:
+ // <HDR-FREE> 96 <HDR-END>
+
+ void * p1 = allocator.HeapAlloc(30);
+ NL_TEST_ASSERT(inSuite, nullptr != p1);
+ // allocator state:
+ // <HDR-IN_USE> 32 <HRD-FREE> 48 <HDR-END>
+
+ void * p2 = allocator.HeapAlloc(4);
+ NL_TEST_ASSERT(inSuite, nullptr != p2);
+ // allocator state:
+ // <HDR-IN_USE> 32 <HRD-IN_USE> 8 <HDR-FREE> 24 <HDR-END>
+
+ allocator.HeapFree(p1);
+ // allocator state:
+ // <HDR-FREE> 32 <HRD-IN_USE> 8 <HDR-FREE> 24 <HDR-END>
+
+ allocator.HeapFree(p2);
+ // allocator state:
+ // <HDR-FREE> 96 <HDR-END>
+
+ p1 = allocator.HeapAlloc(90);
+ NL_TEST_ASSERT(inSuite, nullptr != p1);
+ allocator.HeapFree(p1);
+}
+
+void FreeMergeNext(nlTestSuite * inSuite, void * inContext)
+{
+ PrivateHeapAllocator<5 * 16> allocator;
+
+ void * p1 = allocator.HeapAlloc(16);
+ void * p2 = allocator.HeapAlloc(16);
+
+ NL_TEST_ASSERT(inSuite, nullptr != p1);
+ NL_TEST_ASSERT(inSuite, nullptr != p2);
+ NL_TEST_ASSERT(inSuite, nullptr == allocator.HeapAlloc(1));
+
+ memset(p1, 0xab, 16);
+ memset(p2, 0xcd, 16);
+
+ // freeing 1,2 should clear space
+ allocator.HeapFree(p1);
+ allocator.HeapFree(p2);
+
+ p1 = allocator.HeapAlloc(3 * 16);
+ NL_TEST_ASSERT(inSuite, nullptr != p1);
+ allocator.HeapFree(p1);
+}
+
+void FreeMergePrevious(nlTestSuite * inSuite, void * inContext)
+{
+ PrivateHeapAllocator<5 * 16> allocator;
+
+ void * p1 = allocator.HeapAlloc(16);
+ void * p2 = allocator.HeapAlloc(16);
+
+ NL_TEST_ASSERT(inSuite, nullptr != p1);
+ NL_TEST_ASSERT(inSuite, nullptr != p2);
+ NL_TEST_ASSERT(inSuite, nullptr == allocator.HeapAlloc(1));
+
+ memset(p1, 0xab, 16);
+ memset(p2, 0xcd, 16);
+
+ // freeing 2,1 should clear space
+ allocator.HeapFree(p2);
+ allocator.HeapFree(p1);
+ p1 = allocator.HeapAlloc(3 * 16);
+ NL_TEST_ASSERT(inSuite, nullptr != p1);
+ allocator.HeapFree(p1);
+}
+
+void FreeMergePreviousAndNext(nlTestSuite * inSuite, void * inContext)
+{
+
+ PrivateHeapAllocator<7 * 16> allocator;
+
+ void * p1 = allocator.HeapAlloc(16);
+ void * p2 = allocator.HeapAlloc(16);
+ void * p3 = allocator.HeapAlloc(16);
+
+ NL_TEST_ASSERT(inSuite, nullptr != p1);
+ NL_TEST_ASSERT(inSuite, nullptr != p2);
+ NL_TEST_ASSERT(inSuite, nullptr != p3);
+ NL_TEST_ASSERT(inSuite, nullptr == allocator.HeapAlloc(1));
+
+ memset(p1, 0xab, 16);
+ memset(p2, 0xcd, 16);
+ memset(p3, 0xef, 16);
+
+ allocator.HeapFree(p1);
+ allocator.HeapFree(p3);
+ // we have 2 slots of size 16 available now
+ NL_TEST_ASSERT(inSuite, nullptr == allocator.HeapAlloc(17));
+
+ // Freeing p2 makes enoug space
+ allocator.HeapFree(p2);
+ p1 = allocator.HeapAlloc(5 * 16);
+ NL_TEST_ASSERT(inSuite, nullptr != p1);
+ allocator.HeapFree(p1);
+}
+
+void MultipleMerge(nlTestSuite * inSuite, void * inContext)
+{
+ PrivateHeapAllocator<32 * kBlockHeaderSize> allocator;
+
+ // 31 blocks available for alloc
+ void * p1 = allocator.HeapAlloc(2 * kBlockHeaderSize); // uses up 3 blocks
+ void * p2 = allocator.HeapAlloc(5 * kBlockHeaderSize); // uses up 6 blocks
+ void * p3 = allocator.HeapAlloc(8 * kBlockHeaderSize); // uses up 9 blocks
+ void * p4 = allocator.HeapAlloc(1 * kBlockHeaderSize); // uses up 2 blocks
+ void * p5 = allocator.HeapAlloc(7 * kBlockHeaderSize); // uses up 8 blocks
+ void * p6 = allocator.HeapAlloc(2 * kBlockHeaderSize); // uses up 2 (last given)
+
+ NL_TEST_ASSERT(inSuite, nullptr != p1);
+ NL_TEST_ASSERT(inSuite, nullptr != p2);
+ NL_TEST_ASSERT(inSuite, nullptr != p3);
+ NL_TEST_ASSERT(inSuite, nullptr != p4);
+ NL_TEST_ASSERT(inSuite, nullptr != p5);
+ NL_TEST_ASSERT(inSuite, nullptr != p6);
+
+ allocator.HeapFree(p3);
+ allocator.HeapFree(p4);
+ // 10 blocks available (9 from p3 without HDR and 2 from p4 + HDR)
+ p3 = allocator.HeapAlloc(10 * kBlockHeaderSize);
+ NL_TEST_ASSERT(inSuite, nullptr != p3);
+ NL_TEST_ASSERT(inSuite, nullptr == allocator.HeapAlloc(1)); // full
+
+ allocator.HeapFree(p6);
+ allocator.HeapFree(p5);
+ allocator.HeapFree(p3);
+ allocator.HeapFree(p2);
+ allocator.HeapFree(p1);
+
+ p1 = allocator.HeapAlloc(30 * kBlockHeaderSize);
+ NL_TEST_ASSERT(inSuite, nullptr != p1);
+ allocator.HeapFree(p1);
+}
+
+void ForwardFreeAndRealloc(nlTestSuite * inSuite, void * inContext)
+{
+ constexpr int kNumBlocks = 16;
+ PrivateHeapAllocator<(2 * kNumBlocks + 1) * kBlockHeaderSize> allocator;
+ void * ptrs[kNumBlocks];
+
+ for (int i = 0; i < kNumBlocks; ++i)
+ {
+ ptrs[i] = allocator.HeapAlloc(kBlockHeaderSize);
+ NL_TEST_ASSERT(inSuite, nullptr != ptrs[i]);
+ memset(ptrs[i], 0xab, kBlockHeaderSize);
+ }
+
+ // heap looks like:
+ /// |HDR| 16 |HDR| 16 |HDR| ..... |HDR| 16 |HDR|
+
+ // free each block from the start and re-allocate into a bigger block
+ for (size_t i = 1; i < kNumBlocks; ++i)
+ {
+ allocator.HeapFree(ptrs[0]);
+ allocator.HeapFree(ptrs[i]);
+
+ ptrs[0] = allocator.HeapAlloc((1 + 2 * i) * kBlockHeaderSize);
+ NL_TEST_ASSERT(inSuite, nullptr != ptrs[0]);
+ }
+ allocator.HeapFree(ptrs[0]);
+}
+
+void BackwardFreeAndRealloc(nlTestSuite * inSuite, void * inContext)
+{
+ constexpr int kNumBlocks = 16;
+ PrivateHeapAllocator<(2 * kNumBlocks + 1) * kBlockHeaderSize> allocator;
+ void * ptrs[kNumBlocks];
+
+ for (int i = 0; i < kNumBlocks; ++i)
+ {
+ ptrs[i] = allocator.HeapAlloc(kBlockHeaderSize);
+ NL_TEST_ASSERT(inSuite, nullptr != ptrs[i]);
+ memset(ptrs[i], 0xab, kBlockHeaderSize);
+ }
+
+ // heap looks like:
+ /// |HDR| 16 |HDR| 16 |HDR| ..... |HDR| 16 |HDR|
+
+ // free each block from the send and re-allocate into a bigger block
+ for (size_t i = 1; i < kNumBlocks; ++i)
+ {
+ allocator.HeapFree(ptrs[kNumBlocks - 1]);
+ allocator.HeapFree(ptrs[kNumBlocks - i - 1]);
+
+ ptrs[kNumBlocks - 1] = allocator.HeapAlloc((1 + 2 * i) * kBlockHeaderSize);
+ NL_TEST_ASSERT(inSuite, nullptr != ptrs[kNumBlocks - 1]);
+ }
+ allocator.HeapFree(ptrs[kNumBlocks - 1]);
+}
+
+const nlTest sTests[] = {
+ NL_TEST_DEF("SingleHeapAllocAndFree", SingleHeapAllocAndFree), //
+ NL_TEST_DEF("SplitHeapAllocAndFree", SplitHeapAllocAndFree), //
+ NL_TEST_DEF("FreeMergeNext", FreeMergeNext), //
+ NL_TEST_DEF("FreeMergePrevious", FreeMergePrevious), //
+ NL_TEST_DEF("FreeMergePreviousAndNext", FreeMergePreviousAndNext), //
+ NL_TEST_DEF("MultipleMerge", MultipleMerge), //
+ NL_TEST_DEF("ForwardFreeAndRealloc", ForwardFreeAndRealloc), //
+ NL_TEST_DEF("BackwardFreeAndRealloc", BackwardFreeAndRealloc), //
+ NL_TEST_SENTINEL() //
+};
+
+} // namespace
+
+int TestPrivateHeap(void)
+{
+ nlTestSuite theSuite = { "PrivateHeap", sTests, nullptr, nullptr };
+ nlTestRunner(&theSuite, nullptr);
+ return nlTestRunnerStats(&theSuite);
+}
+
+CHIP_REGISTER_TEST_SUITE(TestPrivateHeap)
#pragma once
#include <app/util/basic-types.h>
-#include <support/ReturnMacros.h>
#include <transport/AdminPairingTable.h>
namespace chip {
mResponseTimeout = timeout;
}
-CHIP_ERROR ExchangeContext::SendMessage(uint16_t protocolId, uint8_t msgType, PacketBufferHandle msgBuf,
+CHIP_ERROR ExchangeContext::SendMessage(Protocols::Id protocolId, uint8_t msgType, PacketBufferHandle msgBuf,
const SendFlags & sendFlags)
{
CHIP_ERROR err = CHIP_NO_ERROR;
return err;
}
-CHIP_ERROR ExchangeContext::SendMessageImpl(uint16_t protocolId, uint8_t msgType, PacketBufferHandle msgBuf,
+CHIP_ERROR ExchangeContext::SendMessageImpl(Protocols::Id protocolId, uint8_t msgType, PacketBufferHandle msgBuf,
const SendFlags & sendFlags, Transport::PeerConnectionState * state)
{
CHIP_ERROR err = CHIP_NO_ERROR;
#include <messaging/ExchangeDelegate.h>
#include <messaging/Flags.h>
#include <messaging/ReliableMessageContext.h>
+#include <protocols/Protocols.h>
#include <support/BitFlags.h>
#include <support/DLLUtil.h>
#include <system/SystemTimer.h>
* @retval #CHIP_NO_ERROR if the CHIP layer successfully sent the message down to the
* network layer.
*/
- CHIP_ERROR SendMessage(uint16_t protocolId, uint8_t msgType, System::PacketBufferHandle msgPayload,
+ CHIP_ERROR SendMessage(Protocols::Id protocolId, uint8_t msgType, System::PacketBufferHandle msgPayload,
const SendFlags & sendFlags);
/**
CHIP_ERROR SendMessage(MessageType msgType, System::PacketBufferHandle && msgPayload, const SendFlags & sendFlags)
{
static_assert(std::is_same<std::underlying_type_t<MessageType>, uint8_t>::value, "Enum is wrong size; cast is not safe");
- return SendMessage(Protocols::MessageTypeTraits<MessageType>::ProtocolId, static_cast<uint8_t>(msgType),
+ return SendMessage(Protocols::MessageTypeTraits<MessageType>::ProtocolId(), static_cast<uint8_t>(msgType),
std::move(msgPayload), sendFlags);
}
* A subset of SendMessage functionality that does not perform message
* counter sync for group keys.
*/
- CHIP_ERROR SendMessageImpl(uint16_t protocolId, uint8_t msgType, System::PacketBufferHandle msgBuf, const SendFlags & sendFlags,
- Transport::PeerConnectionState * state = nullptr);
+ CHIP_ERROR SendMessageImpl(Protocols::Id protocolId, uint8_t msgType, System::PacketBufferHandle msgBuf,
+ const SendFlags & sendFlags, Transport::PeerConnectionState * state = nullptr);
void CancelResponseTimer();
static void HandleResponseTimeout(System::Layer * aSystemLayer, void * aAppState, System::Error aError);
#include <support/CHIPFaultInjection.h>
#include <support/CodeUtils.h>
#include <support/RandUtils.h>
-#include <support/ReturnMacros.h>
#include <support/logging/CHIPLogging.h>
using namespace chip::Encoding;
mContextsInUse = 0;
- memset(UMHandlerPool, 0, sizeof(UMHandlerPool));
+ for (auto & handler : UMHandlerPool)
+ {
+ // Mark all handlers as unallocated. This handles both initial
+ // initialization and the case when the consumer shuts us down and
+ // then re-initializes without removing registered handlers.
+ handler.Delegate = nullptr;
+ }
mTransportMgr->SetRendezvousSession(this);
return AllocContext(mNextExchangeId++, session, true, delegate);
}
-CHIP_ERROR ExchangeManager::RegisterUnsolicitedMessageHandlerForProtocol(uint32_t protocolId, ExchangeDelegate * delegate)
+CHIP_ERROR ExchangeManager::RegisterUnsolicitedMessageHandlerForProtocol(Protocols::Id protocolId, ExchangeDelegate * delegate)
{
return RegisterUMH(protocolId, kAnyMessageType, delegate);
}
-CHIP_ERROR ExchangeManager::RegisterUnsolicitedMessageHandlerForType(uint32_t protocolId, uint8_t msgType,
+CHIP_ERROR ExchangeManager::RegisterUnsolicitedMessageHandlerForType(Protocols::Id protocolId, uint8_t msgType,
ExchangeDelegate * delegate)
{
return RegisterUMH(protocolId, static_cast<int16_t>(msgType), delegate);
}
-CHIP_ERROR ExchangeManager::UnregisterUnsolicitedMessageHandlerForProtocol(uint32_t protocolId)
+CHIP_ERROR ExchangeManager::UnregisterUnsolicitedMessageHandlerForProtocol(Protocols::Id protocolId)
{
return UnregisterUMH(protocolId, kAnyMessageType);
}
-CHIP_ERROR ExchangeManager::UnregisterUnsolicitedMessageHandlerForType(uint32_t protocolId, uint8_t msgType)
+CHIP_ERROR ExchangeManager::UnregisterUnsolicitedMessageHandlerForType(Protocols::Id protocolId, uint8_t msgType)
{
return UnregisterUMH(protocolId, static_cast<int16_t>(msgType));
}
return nullptr;
}
-CHIP_ERROR ExchangeManager::RegisterUMH(uint32_t protocolId, int16_t msgType, ExchangeDelegate * delegate)
+CHIP_ERROR ExchangeManager::RegisterUMH(Protocols::Id protocolId, int16_t msgType, ExchangeDelegate * delegate)
{
UnsolicitedMessageHandler * umh = UMHandlerPool;
UnsolicitedMessageHandler * selected = nullptr;
return CHIP_NO_ERROR;
}
-CHIP_ERROR ExchangeManager::UnregisterUMH(uint32_t protocolId, int16_t msgType)
+CHIP_ERROR ExchangeManager::UnregisterUMH(Protocols::Id protocolId, int16_t msgType)
{
UnsolicitedMessageHandler * umh = UMHandlerPool;
for (int i = 0; i < CHIP_CONFIG_MAX_UNSOLICITED_MESSAGE_HANDLERS; i++, umh++)
{
- if (umh->Delegate != nullptr && umh->ProtocolId == payloadHeader.GetProtocolID())
+ if (umh->Delegate != nullptr && payloadHeader.HasProtocol(umh->ProtocolId))
{
if (umh->MessageType == payloadHeader.GetMessageType())
{
#include <messaging/ExchangeContext.h>
#include <messaging/MessageCounterSync.h>
#include <messaging/ReliableMessageMgr.h>
+#include <protocols/Protocols.h>
#include <support/DLLUtil.h>
#include <support/Pool.h>
#include <transport/SecureSessionMgr.h>
* is full and a new one cannot be allocated.
* @retval #CHIP_NO_ERROR On success.
*/
- CHIP_ERROR RegisterUnsolicitedMessageHandlerForProtocol(uint32_t protocolId, ExchangeDelegate * delegate);
+ CHIP_ERROR RegisterUnsolicitedMessageHandlerForProtocol(Protocols::Id protocolId, ExchangeDelegate * delegate);
/**
* Register an unsolicited message handler for a given protocol identifier and message type.
* is full and a new one cannot be allocated.
* @retval #CHIP_NO_ERROR On success.
*/
- CHIP_ERROR RegisterUnsolicitedMessageHandlerForType(uint32_t protocolId, uint8_t msgType, ExchangeDelegate * delegate);
+ CHIP_ERROR RegisterUnsolicitedMessageHandlerForType(Protocols::Id protocolId, uint8_t msgType, ExchangeDelegate * delegate);
/**
* A strongly-message-typed version of RegisterUnsolicitedMessageHandlerForType.
CHIP_ERROR RegisterUnsolicitedMessageHandlerForType(MessageType msgType, ExchangeDelegate * delegate)
{
static_assert(std::is_same<std::underlying_type_t<MessageType>, uint8_t>::value, "Enum is wrong size; cast is not safe");
- return RegisterUnsolicitedMessageHandlerForType(Protocols::MessageTypeTraits<MessageType>::ProtocolId,
+ return RegisterUnsolicitedMessageHandlerForType(Protocols::MessageTypeTraits<MessageType>::ProtocolId(),
static_cast<uint8_t>(msgType), delegate);
}
* is not found.
* @retval #CHIP_NO_ERROR On success.
*/
- CHIP_ERROR UnregisterUnsolicitedMessageHandlerForProtocol(uint32_t protocolId);
+ CHIP_ERROR UnregisterUnsolicitedMessageHandlerForProtocol(Protocols::Id protocolId);
/**
* Unregister an unsolicited message handler for a given protocol identifier and message type.
* is not found.
* @retval #CHIP_NO_ERROR On success.
*/
- CHIP_ERROR UnregisterUnsolicitedMessageHandlerForType(uint32_t protocolId, uint8_t msgType);
+ CHIP_ERROR UnregisterUnsolicitedMessageHandlerForType(Protocols::Id protocolId, uint8_t msgType);
/**
* A strongly-message-typed version of UnregisterUnsolicitedMessageHandlerForType.
CHIP_ERROR UnregisterUnsolicitedMessageHandlerForType(MessageType msgType)
{
static_assert(std::is_same<std::underlying_type_t<MessageType>, uint8_t>::value, "Enum is wrong size; cast is not safe");
- return UnregisterUnsolicitedMessageHandlerForType(Protocols::MessageTypeTraits<MessageType>::ProtocolId,
+ return UnregisterUnsolicitedMessageHandlerForType(Protocols::MessageTypeTraits<MessageType>::ProtocolId(),
static_cast<uint8_t>(msgType));
}
struct UnsolicitedMessageHandler
{
+ UnsolicitedMessageHandler() : ProtocolId(Protocols::NotSpecified) {}
ExchangeDelegate * Delegate;
- uint32_t ProtocolId;
+ Protocols::Id ProtocolId;
int16_t MessageType;
};
ExchangeContext * AllocContext(uint16_t ExchangeId, SecureSessionHandle session, bool Initiator, ExchangeDelegate * delegate);
- CHIP_ERROR RegisterUMH(uint32_t protocolId, int16_t msgType, ExchangeDelegate * delegate);
- CHIP_ERROR UnregisterUMH(uint32_t protocolId, int16_t msgType);
+ CHIP_ERROR RegisterUMH(Protocols::Id protocolId, int16_t msgType, ExchangeDelegate * delegate);
+ CHIP_ERROR UnregisterUMH(Protocols::Id protocolId, int16_t msgType);
static bool IsMsgCounterSyncMessage(const PayloadHeader & payloadHeader);
#include <protocols/Protocols.h>
#include <support/BufferWriter.h>
#include <support/CodeUtils.h>
-#include <support/ReturnMacros.h>
#include <support/logging/CHIPLogging.h>
namespace chip {
mExchangeMgr = exchangeMgr;
// Register to receive unsolicited Secure Channel Request messages from the exchange manager.
- err = mExchangeMgr->RegisterUnsolicitedMessageHandlerForProtocol(Protocols::kProtocol_SecureChannel, this);
+ err = mExchangeMgr->RegisterUnsolicitedMessageHandlerForProtocol(Protocols::SecureChannel::Id, this);
ReturnErrorOnFailure(err);
{
if (mExchangeMgr != nullptr)
{
- mExchangeMgr->UnregisterUnsolicitedMessageHandlerForProtocol(Protocols::kProtocol_SecureChannel);
+ mExchangeMgr->UnregisterUnsolicitedMessageHandlerForProtocol(Protocols::SecureChannel::Id);
mExchangeMgr = nullptr;
}
}
exchangeContext->Close();
}
-CHIP_ERROR MessageCounterSyncMgr::AddToRetransmissionTable(uint16_t protocolId, uint8_t msgType, const SendFlags & sendFlags,
+CHIP_ERROR MessageCounterSyncMgr::AddToRetransmissionTable(Protocols::Id protocolId, uint8_t msgType, const SendFlags & sendFlags,
System::PacketBufferHandle msgBuf,
Messaging::ExchangeContext * exchangeContext)
{
exchangeContext->SetResponseTimeout(kMsgCounterSyncTimeout);
// Send the message counter synchronization request in a Secure Channel Protocol::MsgCounterSyncReq message.
- err = exchangeContext->SendMessageImpl(Protocols::kProtocol_SecureChannel,
+ err = exchangeContext->SendMessageImpl(Protocols::SecureChannel::Id,
static_cast<uint8_t>(Protocols::SecureChannel::MsgType::MsgCounterSyncReq),
std::move(msgBuf), sendFlags);
SuccessOrExit(err);
msgBuf->SetDataLength(kMsgCounterSyncRespMsgSize);
// Send message counter synchronization response message.
- err = exchangeContext->SendMessageImpl(Protocols::kProtocol_SecureChannel,
+ err = exchangeContext->SendMessageImpl(Protocols::SecureChannel::Id,
static_cast<uint8_t>(Protocols::SecureChannel::MsgType::MsgCounterSyncRsp),
std::move(msgBuf), Messaging::SendFlags(Messaging::SendMessageFlags::kNoAutoRequestAck));
#pragma once
+#include <protocols/Protocols.h>
#include <system/SystemPacketBuffer.h>
namespace chip {
* @retval #CHIP_ERROR_NO_MEMORY If there is no empty slot left in the table for addition.
* @retval #CHIP_NO_ERROR On success.
*/
- CHIP_ERROR AddToRetransmissionTable(uint16_t protocolId, uint8_t msgType, const SendFlags & sendFlags,
+ CHIP_ERROR AddToRetransmissionTable(Protocols::Id protocolId, uint8_t msgType, const SendFlags & sendFlags,
System::PacketBufferHandle msgBuf, Messaging::ExchangeContext * exchangeContext);
/**
*/
struct RetransTableEntry
{
+ RetransTableEntry() : protocolId(Protocols::NotSpecified) {}
ExchangeContext * exchangeContext; /**< The ExchangeContext for the stored CHIP message.
Non-null if and only if this entry is in use. */
System::PacketBufferHandle msgBuf; /**< A handle to the PacketBuffer object holding the CHIP message. */
SendFlags sendFlags; /**< Flags set by the application for the CHIP message being sent. */
- uint16_t protocolId; /**< The protocol identifier of the CHIP message to be sent. */
+ Protocols::Id protocolId; /**< The protocol identifier of the CHIP message to be sent. */
uint8_t msgType; /**< The message type of the CHIP message to be sent. */
};
#include <support/CodeUtils.h>
#include <support/ErrorStr.h>
-#include <support/ReturnMacros.h>
namespace chip {
namespace Test {
// create unsolicited exchange
MockAppDelegate mockUnsolicitedAppDelegate;
- CHIP_ERROR err = ctx.GetExchangeManager().RegisterUnsolicitedMessageHandlerForType(0x0001, 0x0001, &mockUnsolicitedAppDelegate);
+ CHIP_ERROR err = ctx.GetExchangeManager().RegisterUnsolicitedMessageHandlerForType(Protocols::Id(VendorId::Common, 0x0001),
+ 0x0001, &mockUnsolicitedAppDelegate);
NL_TEST_ASSERT(inSuite, err == CHIP_NO_ERROR);
// create the channel
CHIP_ERROR err;
MockAppDelegate mockAppDelegate;
- err = ctx.GetExchangeManager().RegisterUnsolicitedMessageHandlerForProtocol(0x0001, &mockAppDelegate);
+ err = ctx.GetExchangeManager().RegisterUnsolicitedMessageHandlerForProtocol(Protocols::Id(VendorId::Common, 0x0001),
+ &mockAppDelegate);
NL_TEST_ASSERT(inSuite, err == CHIP_NO_ERROR);
- err = ctx.GetExchangeManager().RegisterUnsolicitedMessageHandlerForType(0x0002, 0x0001, &mockAppDelegate);
+ err = ctx.GetExchangeManager().RegisterUnsolicitedMessageHandlerForType(Protocols::Id(VendorId::Common, 0x0002), 0x0001,
+ &mockAppDelegate);
NL_TEST_ASSERT(inSuite, err == CHIP_NO_ERROR);
- err = ctx.GetExchangeManager().UnregisterUnsolicitedMessageHandlerForProtocol(0x0001);
+ err = ctx.GetExchangeManager().UnregisterUnsolicitedMessageHandlerForProtocol(Protocols::Id(VendorId::Common, 0x0001));
NL_TEST_ASSERT(inSuite, err == CHIP_NO_ERROR);
- err = ctx.GetExchangeManager().UnregisterUnsolicitedMessageHandlerForProtocol(0x0002);
+ err = ctx.GetExchangeManager().UnregisterUnsolicitedMessageHandlerForProtocol(Protocols::Id(VendorId::Common, 0x0002));
NL_TEST_ASSERT(inSuite, err != CHIP_NO_ERROR);
- err = ctx.GetExchangeManager().UnregisterUnsolicitedMessageHandlerForType(0x0002, 0x0001);
+ err = ctx.GetExchangeManager().UnregisterUnsolicitedMessageHandlerForType(Protocols::Id(VendorId::Common, 0x0002), 0x0001);
NL_TEST_ASSERT(inSuite, err == CHIP_NO_ERROR);
- err = ctx.GetExchangeManager().UnregisterUnsolicitedMessageHandlerForType(0x0002, 0x0002);
+ err = ctx.GetExchangeManager().UnregisterUnsolicitedMessageHandlerForType(Protocols::Id(VendorId::Common, 0x0002), 0x0002);
NL_TEST_ASSERT(inSuite, err != CHIP_NO_ERROR);
}
// create unsolicited exchange
MockAppDelegate mockUnsolicitedAppDelegate;
- err = ctx.GetExchangeManager().RegisterUnsolicitedMessageHandlerForType(0x0001, 0x0001, &mockUnsolicitedAppDelegate);
+ err = ctx.GetExchangeManager().RegisterUnsolicitedMessageHandlerForType(Protocols::Id(VendorId::Common, 0x0001), 0x0001,
+ &mockUnsolicitedAppDelegate);
NL_TEST_ASSERT(inSuite, err == CHIP_NO_ERROR);
// send a malicious packet
NL_TEST_ASSERT(inSuite, !mockUnsolicitedAppDelegate.IsOnMessageReceivedCalled);
// send a good packet
- ec1->SendMessage(0x0001, 0x0001, System::PacketBufferHandle::New(System::PacketBuffer::kMaxSize),
+ ec1->SendMessage(Protocols::Id(VendorId::Common, 0x0001), 0x0001,
+ System::PacketBufferHandle::New(System::PacketBuffer::kMaxSize),
SendFlags(Messaging::SendMessageFlags::kNone));
NL_TEST_ASSERT(inSuite, mockUnsolicitedAppDelegate.IsOnMessageReceivedCalled);
}
#include <protocols/Protocols.h>
#include <protocols/echo/Echo.h>
#include <support/CodeUtils.h>
-#include <support/ReturnMacros.h>
#include <transport/SecureSessionMgr.h>
#include <transport/TransportMgr.h>
NL_TEST_ASSERT(inSuite, sm != nullptr);
// Register to receive unsolicited Secure Channel Request messages from the exchange manager.
- err =
- ctx.GetExchangeManager().RegisterUnsolicitedMessageHandlerForProtocol(Protocols::kProtocol_SecureChannel, &mockAppDelegate);
+ err = ctx.GetExchangeManager().RegisterUnsolicitedMessageHandlerForProtocol(Protocols::SecureChannel::Id, &mockAppDelegate);
NL_TEST_ASSERT(inSuite, err == CHIP_NO_ERROR);
Optional<Transport::PeerAddress> peer(Transport::PeerAddress::UDP(addr, CHIP_PORT));
NL_TEST_ASSERT(inSuite, !buffer.IsNull());
CHIP_ERROR err =
- sm->AddToRetransmissionTable(Protocols::kProtocol_Echo, static_cast<uint8_t>(Protocols::Echo::MsgType::EchoRequest),
+ sm->AddToRetransmissionTable(Protocols::Echo::Id, static_cast<uint8_t>(Protocols::Echo::MsgType::EchoRequest),
Messaging::SendFlags(Messaging::SendMessageFlags::kNone), std::move(buffer), exchange);
NL_TEST_ASSERT(inSuite, err == CHIP_NO_ERROR);
}
#include <protocols/Protocols.h>
#include <protocols/echo/Echo.h>
#include <support/CodeUtils.h>
-#include <support/ReturnMacros.h>
#include <transport/SecureSessionMgr.h>
#include <transport/TransportMgr.h>
"Darwin/ConnectivityManagerImpl.h",
"Darwin/InetPlatformConfig.h",
"Darwin/Logging.cpp",
+ "Darwin/MdnsError.cpp",
+ "Darwin/MdnsError.h",
+ "Darwin/MdnsImpl.cpp",
+ "Darwin/MdnsImpl.h",
"Darwin/PlatformManagerImpl.cpp",
"Darwin/PlatformManagerImpl.h",
"Darwin/PosixConfig.cpp",
--- /dev/null
+/*
+ *
+ * Copyright (c) 2021 Project CHIP Authors
+ *
+ * Licensed under the Apache License, Version 2.0 (the "License");
+ * you may not use this file except in compliance with the License.
+ * You may obtain a copy of the License at
+ *
+ * http://www.apache.org/licenses/LICENSE-2.0
+ *
+ * Unless required by applicable law or agreed to in writing, software
+ * distributed under the License is distributed on an "AS IS" BASIS,
+ * WITHOUT WARRANTIES OR CONDITIONS OF ANY KIND, either express or implied.
+ * See the License for the specific language governing permissions and
+ * limitations under the License.
+ */
+
+#include "MdnsImpl.h"
+
+namespace chip {
+namespace Mdns {
+namespace Error {
+
+const char * ToString(DNSServiceErrorType errorCode)
+{
+ switch (errorCode)
+ {
+ case kDNSServiceErr_NoError:
+ return "kDNSServiceErr_NoError";
+ case kDNSServiceErr_Unknown:
+ return "kDNSServiceErr_Unknown";
+ case kDNSServiceErr_NoSuchName:
+ return "kDNSServiceErr_NoSuchName";
+ case kDNSServiceErr_NoMemory:
+ return "kDNSServiceErr_NoMemory";
+ case kDNSServiceErr_BadParam:
+ return "kDNSServiceErr_BadParam";
+ case kDNSServiceErr_BadReference:
+ return "kDNSServiceErr_BadReference";
+ case kDNSServiceErr_BadState:
+ return "kDNSServiceErr_BadState";
+ case kDNSServiceErr_BadFlags:
+ return "kDNSServiceErr_BadFlags";
+ case kDNSServiceErr_Unsupported:
+ return "kDNSServiceErr_Unsupported";
+ case kDNSServiceErr_NotInitialized:
+ return "kDNSServiceErr_NotInitialized";
+ case kDNSServiceErr_AlreadyRegistered:
+ return "kDNSServiceErr_AlreadyRegistered";
+ case kDNSServiceErr_NameConflict:
+ return "kDNSServiceErr_NameConflict";
+ case kDNSServiceErr_Invalid:
+ return "kDNSServiceErr_Invalid";
+ case kDNSServiceErr_Firewall:
+ return "kDNSServiceErr_Firewall";
+ case kDNSServiceErr_Incompatible:
+ return "kDNSServiceErr_Incompatible";
+ case kDNSServiceErr_BadInterfaceIndex:
+ return "kDNSServiceErr_BadInterfaceIndex";
+ case kDNSServiceErr_Refused:
+ return "kDNSServiceErr_Refused";
+ case kDNSServiceErr_NoSuchRecord:
+ return "kDNSServiceErr_NoSuchRecord";
+ case kDNSServiceErr_NoAuth:
+ return "kDNSServiceErr_NoAuth";
+ case kDNSServiceErr_NoSuchKey:
+ return "kDNSServiceErr_NoSuchKey";
+ case kDNSServiceErr_NATTraversal:
+ return "kDNSServiceErr_NATTraversal";
+ case kDNSServiceErr_DoubleNAT:
+ return "kDNSServiceErr_DoubleNAT";
+ case kDNSServiceErr_BadTime:
+ return "kDNSServiceErr_BadTime";
+ case kDNSServiceErr_BadSig:
+ return "kDNSServiceErr_BadSig";
+ case kDNSServiceErr_BadKey:
+ return "kDNSServiceErr_BadKey";
+ case kDNSServiceErr_Transient:
+ return "kDNSServiceErr_Transient";
+ case kDNSServiceErr_ServiceNotRunning:
+ return "kDNSServiceErr_ServiceNotRunning";
+ case kDNSServiceErr_NATPortMappingUnsupported:
+ return "kDNSServiceErr_NATPortMappingUnsupported";
+ case kDNSServiceErr_NATPortMappingDisabled:
+ return "kDNSServiceErr_NATPortMappingDisabled";
+ case kDNSServiceErr_NoRouter:
+ return "kDNSServiceErr_NoRouter";
+ case kDNSServiceErr_PollingMode:
+ return "kDNSServiceErr_PollingMode";
+ case kDNSServiceErr_Timeout:
+ return "kDNSServiceErr_Timeout";
+ default:
+ return "Unknown DNSService error code";
+ }
+}
+
+} // namespace Error
+} // namespace Mdns
+} // namespace chip
--- /dev/null
+/*
+ *
+ * Copyright (c) 2021 Project CHIP Authors
+ *
+ * Licensed under the Apache License, Version 2.0 (the "License");
+ * you may not use this file except in compliance with the License.
+ * You may obtain a copy of the License at
+ *
+ * http://www.apache.org/licenses/LICENSE-2.0
+ *
+ * Unless required by applicable law or agreed to in writing, software
+ * distributed under the License is distributed on an "AS IS" BASIS,
+ * WITHOUT WARRANTIES OR CONDITIONS OF ANY KIND, either express or implied.
+ * See the License for the specific language governing permissions and
+ * limitations under the License.
+ */
+
+#include "MdnsImpl.h"
+
+namespace chip {
+namespace Mdns {
+namespace Error {
+
+const char * ToString(DNSServiceErrorType errorCode);
+
+} // namespace Error
+} // namespace Mdns
+} // namespace chip
--- /dev/null
+/*
+ *
+ * Copyright (c) 2021 Project CHIP Authors
+ *
+ * Licensed under the Apache License, Version 2.0 (the "License");
+ * you may not use this file except in compliance with the License.
+ * You may obtain a copy of the License at
+ *
+ * http://www.apache.org/licenses/LICENSE-2.0
+ *
+ * Unless required by applicable law or agreed to in writing, software
+ * distributed under the License is distributed on an "AS IS" BASIS,
+ * WITHOUT WARRANTIES OR CONDITIONS OF ANY KIND, either express or implied.
+ * See the License for the specific language governing permissions and
+ * limitations under the License.
+ */
+#include "MdnsImpl.h"
+
+#include "MdnsError.h"
+
+#include <cstdio>
+#include <sstream>
+#include <string.h>
+
+#include <platform/CHIPDeviceLayer.h>
+#include <support/CHIPMem.h>
+#include <support/CodeUtils.h>
+#include <support/SafeInt.h>
+#include <support/logging/CHIPLogging.h>
+
+using namespace chip::Mdns;
+
+namespace {
+
+constexpr const char * kLocalDomain = "local.";
+constexpr const char * kProtocolTcp = "._tcp";
+constexpr const char * kProtocolUdp = "._udp";
+constexpr uint8_t kMdnsKeyMaxSize = 32;
+
+bool IsSupportedProtocol(MdnsServiceProtocol protocol)
+{
+ return (protocol == MdnsServiceProtocol::kMdnsProtocolUdp) || (protocol == MdnsServiceProtocol::kMdnsProtocolTcp);
+}
+
+uint32_t GetInterfaceId(chip::Inet::InterfaceId interfaceId)
+{
+ return INET_NULL_INTERFACEID ? 0 : interfaceId;
+}
+
+std::string GetFullType(const char * type, MdnsServiceProtocol protocol)
+{
+ std::ostringstream typeBuilder;
+ typeBuilder << type;
+ typeBuilder << (protocol == MdnsServiceProtocol::kMdnsProtocolUdp ? kProtocolUdp : kProtocolTcp);
+ return typeBuilder.str();
+}
+
+} // namespace
+
+namespace chip {
+namespace Mdns {
+
+MdnsContexts MdnsContexts::sInstance;
+
+void MdnsContexts::Delete(GenericContext * context)
+{
+ if (context->type == ContextType::GetAddrInfo)
+ {
+ GetAddrInfoContext * addrInfoContext = reinterpret_cast<GetAddrInfoContext *>(context);
+ std::vector<TextEntry>::iterator textEntry;
+ for (textEntry = addrInfoContext->textEntries.begin(); textEntry != addrInfoContext->textEntries.end(); textEntry++)
+ {
+ free(const_cast<char *>(textEntry->mKey));
+ free(const_cast<uint8_t *>(textEntry->mData));
+ }
+ }
+
+ DNSServiceRefDeallocate(context->serviceRef);
+ chip::Platform::Delete(context);
+}
+
+MdnsContexts::~MdnsContexts()
+{
+ std::vector<GenericContext *>::const_iterator iter = mContexts.cbegin();
+ while (iter != mContexts.cend())
+ {
+ Delete(*iter);
+ mContexts.erase(iter);
+ }
+}
+
+CHIP_ERROR MdnsContexts::Add(GenericContext * context, DNSServiceRef sdRef)
+{
+ VerifyOrReturnError(context != nullptr, CHIP_ERROR_INVALID_ARGUMENT);
+ VerifyOrReturnError(sdRef != nullptr, CHIP_ERROR_INVALID_ARGUMENT);
+
+ context->serviceRef = sdRef;
+ mContexts.push_back(context);
+
+ return CHIP_NO_ERROR;
+}
+
+CHIP_ERROR MdnsContexts::Remove(GenericContext * context)
+{
+ bool found = false;
+
+ std::vector<GenericContext *>::const_iterator iter = mContexts.cbegin();
+ while (iter != mContexts.cend())
+ {
+ if (*iter != context)
+ {
+ iter++;
+ continue;
+ }
+
+ Delete(*iter);
+ mContexts.erase(iter);
+ found = true;
+ break;
+ }
+
+ return found ? CHIP_NO_ERROR : CHIP_ERROR_KEY_NOT_FOUND;
+}
+
+CHIP_ERROR MdnsContexts::Removes(ContextType type)
+{
+ bool found = false;
+
+ std::vector<GenericContext *>::const_iterator iter = mContexts.cbegin();
+ while (iter != mContexts.cend())
+ {
+ if ((*iter)->type != type)
+ {
+ iter++;
+ continue;
+ }
+
+ Delete(*iter);
+ mContexts.erase(iter);
+ found = true;
+ }
+
+ return found ? CHIP_NO_ERROR : CHIP_ERROR_KEY_NOT_FOUND;
+}
+
+CHIP_ERROR MdnsContexts::Get(ContextType type, GenericContext * context)
+{
+ bool found = false;
+ std::vector<GenericContext *>::iterator iter;
+
+ for (iter = mContexts.begin(); iter != mContexts.end(); iter++)
+ {
+ if ((*iter)->type == type)
+ {
+ context = *iter;
+ found = true;
+ break;
+ }
+ }
+
+ return found ? CHIP_NO_ERROR : CHIP_ERROR_KEY_NOT_FOUND;
+}
+
+void MdnsContexts::PrepareSelect(fd_set & readFdSet, fd_set & writeFdSet, fd_set & errorFdSet, int & maxFd, timeval & timeout)
+{
+ std::vector<DNSServiceRef> serviceRefs(mContexts.size());
+ std::transform(mContexts.begin(), mContexts.end(), serviceRefs.begin(),
+ [](GenericContext * context) { return context->serviceRef; });
+
+ std::vector<DNSServiceRef>::iterator iter;
+ for (iter = serviceRefs.begin(); iter != serviceRefs.end(); iter++)
+ {
+ int fd = DNSServiceRefSockFD(*iter);
+ FD_SET(fd, &readFdSet);
+ if (maxFd < fd)
+ {
+ maxFd = fd;
+ }
+ }
+}
+
+void MdnsContexts::HandleSelectResult(fd_set & readFdSet, fd_set & writeFdSet, fd_set & errorFdSet)
+{
+ std::vector<DNSServiceRef> serviceRefs(mContexts.size());
+ std::transform(mContexts.begin(), mContexts.end(), serviceRefs.begin(),
+ [](GenericContext * context) { return context->serviceRef; });
+
+ std::vector<DNSServiceRef>::iterator iter;
+ for (iter = serviceRefs.begin(); iter != serviceRefs.end(); iter++)
+ {
+ int fd = DNSServiceRefSockFD(*iter);
+ if (FD_ISSET(fd, &readFdSet))
+ {
+ DNSServiceProcessResult(*iter);
+ }
+ }
+}
+
+CHIP_ERROR PopulateTextRecord(TXTRecordRef * record, char * buffer, uint16_t bufferLen, TextEntry * textEntries,
+ size_t textEntrySize)
+{
+ VerifyOrReturnError(textEntrySize <= kMdnsTextMaxSize, CHIP_ERROR_INVALID_ARGUMENT);
+
+ DNSServiceErrorType err;
+ TXTRecordCreate(record, bufferLen, buffer);
+
+ for (size_t i = 0; i < textEntrySize; i++)
+ {
+ TextEntry entry = textEntries[i];
+ VerifyOrReturnError(chip::CanCastTo<uint8_t>(entry.mDataSize), CHIP_ERROR_INVALID_ARGUMENT);
+
+ err = TXTRecordSetValue(record, entry.mKey, static_cast<uint8_t>(entry.mDataSize), entry.mData);
+ VerifyOrReturnError(err == kDNSServiceErr_NoError, CHIP_ERROR_INVALID_ARGUMENT);
+ }
+
+ return CHIP_NO_ERROR;
+}
+
+bool CheckForSuccess(GenericContext * context, const char * name, DNSServiceErrorType err, bool useCallback = false)
+{
+ if (context == nullptr)
+ {
+ ChipLogError(DeviceLayer, "%s (%s)", name, "Mdns context is null.");
+ return false;
+ }
+
+ if (kDNSServiceErr_NoError != err)
+ {
+ ChipLogError(DeviceLayer, "%s (%s)", name, Error::ToString(err));
+
+ if (useCallback)
+ {
+ switch (context->type)
+ {
+ case ContextType::Register:
+ // Nothing special to do. Maybe ChipMdnsPublishService should take a callback ?
+ break;
+ case ContextType::Browse: {
+ BrowseContext * browseContext = reinterpret_cast<BrowseContext *>(context);
+ browseContext->callback(browseContext->context, nullptr, 0, CHIP_ERROR_INTERNAL);
+ break;
+ }
+ case ContextType::Resolve: {
+ ResolveContext * resolveContext = reinterpret_cast<ResolveContext *>(context);
+ resolveContext->callback(resolveContext->context, nullptr, CHIP_ERROR_INTERNAL);
+ break;
+ }
+ case ContextType::GetAddrInfo: {
+ GetAddrInfoContext * resolveContext = reinterpret_cast<GetAddrInfoContext *>(context);
+ resolveContext->callback(resolveContext->context, nullptr, CHIP_ERROR_INTERNAL);
+ break;
+ }
+ }
+ }
+
+ if (CHIP_ERROR_KEY_NOT_FOUND == MdnsContexts::GetInstance().Remove(context))
+ {
+ chip::Platform::Delete(context);
+ }
+
+ return false;
+ }
+
+ return true;
+}
+
+static void OnRegister(DNSServiceRef sdRef, DNSServiceFlags flags, DNSServiceErrorType err, const char * name, const char * type,
+ const char * domain, void * context)
+{
+ RegisterContext * sdCtx = reinterpret_cast<RegisterContext *>(context);
+ VerifyOrReturn(CheckForSuccess(sdCtx, __func__, err));
+
+ ChipLogDetail(DeviceLayer, "Mdns: %s name: %s, type: %s, domain: %s, flags: %d", __func__, name, type, domain, flags);
+};
+
+CHIP_ERROR Register(uint32_t interfaceId, const char * type, const char * name, uint16_t port, TXTRecordRef * recordRef)
+{
+ DNSServiceErrorType err;
+ DNSServiceRef sdRef;
+ RegisterContext * sdCtx = nullptr;
+
+ uint16_t recordLen = TXTRecordGetLength(recordRef);
+ const void * recordBytesPtr = TXTRecordGetBytesPtr(recordRef);
+
+ if (CHIP_NO_ERROR == MdnsContexts::GetInstance().Get(ContextType::Register, sdCtx))
+ {
+ err = DNSServiceUpdateRecord(sdCtx->serviceRef, NULL, 0 /* flags */, recordLen, recordBytesPtr, 0 /* ttl */);
+ TXTRecordDeallocate(recordRef);
+ VerifyOrReturnError(CheckForSuccess(sdCtx, __func__, err), CHIP_ERROR_INTERNAL);
+ return CHIP_NO_ERROR;
+ }
+
+ sdCtx = chip::Platform::New<RegisterContext>(nullptr);
+ err = DNSServiceRegister(&sdRef, 0 /* flags */, interfaceId, name, type, kLocalDomain, NULL, port, recordLen, recordBytesPtr,
+ OnRegister, sdCtx);
+ TXTRecordDeallocate(recordRef);
+
+ VerifyOrReturnError(CheckForSuccess(sdCtx, __func__, err), CHIP_ERROR_INTERNAL);
+
+ return MdnsContexts::GetInstance().Add(sdCtx, sdRef);
+}
+
+void OnBrowseAdd(BrowseContext * context, const char * name, const char * type, const char * domain, uint32_t interfaceId)
+{
+ ChipLogDetail(DeviceLayer, "Mdns: %s name: %s, type: %s, domain: %s, interface: %d", __func__, name, type, domain,
+ interfaceId);
+
+ VerifyOrReturn(strcmp(kLocalDomain, domain) == 0);
+
+ char * tokens = strdup(type);
+ char * regtype = strtok(tokens, ".");
+ free(tokens);
+
+ MdnsService service = {};
+ service.mInterface = interfaceId;
+ service.mProtocol = context->protocol;
+
+ strncpy(service.mName, name, sizeof(service.mName));
+ service.mName[kMdnsNameMaxSize] = 0;
+
+ strncpy(service.mType, regtype, sizeof(service.mType));
+ service.mType[kMdnsTypeMaxSize] = 0;
+
+ context->services.push_back(service);
+}
+
+void OnBrowseRemove(BrowseContext * context, const char * name, const char * type, const char * domain, uint32_t interfaceId)
+{
+ ChipLogDetail(DeviceLayer, "Mdns: %s name: %s, type: %s, domain: %s, interface: %d", __func__, name, type, domain,
+ interfaceId);
+
+ VerifyOrReturn(strcmp(kLocalDomain, domain) == 0);
+
+ std::remove_if(context->services.begin(), context->services.end(), [name, type, interfaceId](const MdnsService & service) {
+ return strcmp(name, service.mName) == 0 && type == GetFullType(service.mType, service.mProtocol) &&
+ service.mInterface == interfaceId;
+ });
+}
+
+static void OnBrowse(DNSServiceRef sdRef, DNSServiceFlags flags, uint32_t interfaceId, DNSServiceErrorType err, const char * name,
+ const char * type, const char * domain, void * context)
+{
+ BrowseContext * sdCtx = reinterpret_cast<BrowseContext *>(context);
+ VerifyOrReturn(CheckForSuccess(sdCtx, __func__, err, true));
+
+ (flags & kDNSServiceFlagsAdd) ? OnBrowseAdd(sdCtx, name, type, domain, interfaceId)
+ : OnBrowseRemove(sdCtx, name, type, domain, interfaceId);
+
+ if (!(flags & kDNSServiceFlagsMoreComing))
+ {
+ sdCtx->callback(sdCtx->context, sdCtx->services.data(), sdCtx->services.size(), CHIP_NO_ERROR);
+ MdnsContexts::GetInstance().Remove(sdCtx);
+ }
+}
+
+CHIP_ERROR Browse(void * context, MdnsBrowseCallback callback, uint32_t interfaceId, const char * type,
+ MdnsServiceProtocol protocol)
+{
+ DNSServiceErrorType err;
+ DNSServiceRef sdRef;
+ BrowseContext * sdCtx;
+
+ sdCtx = chip::Platform::New<BrowseContext>(context, callback, protocol);
+ err = DNSServiceBrowse(&sdRef, 0 /* flags */, interfaceId, type, kLocalDomain, OnBrowse, sdCtx);
+ VerifyOrReturnError(CheckForSuccess(sdCtx, __func__, err), CHIP_ERROR_INTERNAL);
+
+ return MdnsContexts::GetInstance().Add(sdCtx, sdRef);
+}
+
+static void OnGetAddrInfo(DNSServiceRef sdRef, DNSServiceFlags flags, uint32_t interfaceId, DNSServiceErrorType err,
+ const char * hostname, const struct sockaddr * address, uint32_t ttl, void * context)
+{
+ GetAddrInfoContext * sdCtx = reinterpret_cast<GetAddrInfoContext *>(context);
+ VerifyOrReturn(CheckForSuccess(sdCtx, __func__, err, true));
+
+ ChipLogDetail(DeviceLayer, "Mdns: %s hostname:%s", __func__, hostname);
+
+ MdnsService service = {};
+ service.mPort = sdCtx->port;
+ service.mTextEntries = sdCtx->textEntries.empty() ? nullptr : sdCtx->textEntries.data();
+ service.mTextEntrySize = sdCtx->textEntries.empty() ? 0 : sdCtx->textEntries.size();
+ service.mAddress.SetValue(chip::Inet::IPAddress::FromSockAddr(*address));
+
+ sdCtx->callback(sdCtx->context, &service, CHIP_NO_ERROR);
+ MdnsContexts::GetInstance().Remove(sdCtx);
+}
+
+CHIP_ERROR GetAddrInfo(void * context, MdnsResolveCallback callback, uint32_t interfaceId, const char * hostname, uint16_t port,
+ uint16_t txtLen, const unsigned char * txtRecord)
+{
+ DNSServiceErrorType err;
+ DNSServiceRef sdRef;
+ GetAddrInfoContext * sdCtx;
+
+ sdCtx = chip::Platform::New<GetAddrInfoContext>(context, callback, port);
+
+ char key[kMdnsKeyMaxSize];
+ char value[kMdnsTextMaxSize];
+ uint8_t valueLen;
+ const void * valuePtr;
+
+ uint16_t recordCount = TXTRecordGetCount(txtLen, txtRecord);
+ for (uint16_t i = 0; i < recordCount; i++)
+ {
+ err = TXTRecordGetItemAtIndex(txtLen, txtRecord, i, kMdnsKeyMaxSize, key, &valueLen, &valuePtr);
+ VerifyOrReturnError(CheckForSuccess(sdCtx, __func__, err, true), CHIP_ERROR_INTERNAL);
+
+ strncpy(value, reinterpret_cast<const char *>(valuePtr), valueLen);
+ value[valueLen] = 0;
+
+ sdCtx->textEntries.push_back(TextEntry{ strdup(key), reinterpret_cast<const uint8_t *>(strdup(value)), valueLen });
+ }
+
+ err = DNSServiceGetAddrInfo(&sdRef, 0 /* flags */, interfaceId, kDNSServiceProtocol_IPv4, hostname, OnGetAddrInfo, sdCtx);
+ VerifyOrReturnError(CheckForSuccess(sdCtx, __func__, err, true), CHIP_ERROR_INTERNAL);
+
+ return MdnsContexts::GetInstance().Add(sdCtx, sdRef);
+}
+
+static void OnResolve(DNSServiceRef sdRef, DNSServiceFlags flags, uint32_t interfaceId, DNSServiceErrorType err,
+ const char * fullname, const char * hostname, uint16_t port, uint16_t txtLen, const unsigned char * txtRecord,
+ void * context)
+{
+ ResolveContext * sdCtx = reinterpret_cast<ResolveContext *>(context);
+ VerifyOrReturn(CheckForSuccess(sdCtx, __func__, err, true));
+
+ GetAddrInfo(sdCtx->context, sdCtx->callback, interfaceId, hostname, port, txtLen, txtRecord);
+ MdnsContexts::GetInstance().Remove(sdCtx);
+}
+
+CHIP_ERROR Resolve(void * context, MdnsResolveCallback callback, uint32_t interfaceId, const char * type, const char * name)
+{
+ DNSServiceErrorType err;
+ DNSServiceRef sdRef;
+ ResolveContext * sdCtx;
+
+ sdCtx = chip::Platform::New<ResolveContext>(context, callback);
+ err = DNSServiceResolve(&sdRef, 0 /* flags */, interfaceId, name, type, kLocalDomain, OnResolve, sdCtx);
+ VerifyOrReturnError(CheckForSuccess(sdCtx, __func__, err), CHIP_ERROR_INTERNAL);
+
+ return MdnsContexts::GetInstance().Add(sdCtx, sdRef);
+}
+
+CHIP_ERROR ChipMdnsInit(MdnsAsyncReturnCallback successCallback, MdnsAsyncReturnCallback errorCallback, void * context)
+{
+ VerifyOrReturnError(successCallback != nullptr, CHIP_ERROR_INVALID_ARGUMENT);
+ VerifyOrReturnError(errorCallback != nullptr, CHIP_ERROR_INVALID_ARGUMENT);
+
+ successCallback(context, CHIP_NO_ERROR);
+ return CHIP_NO_ERROR;
+}
+
+CHIP_ERROR ChipMdnsSetHostname(const char * hostname)
+{
+ MdnsContexts::GetInstance().SetHostname(hostname);
+ return CHIP_NO_ERROR;
+}
+
+CHIP_ERROR ChipMdnsPublishService(const MdnsService * service)
+{
+ VerifyOrReturnError(service != nullptr, CHIP_ERROR_INVALID_ARGUMENT);
+ VerifyOrReturnError(IsSupportedProtocol(service->mProtocol), CHIP_ERROR_INVALID_ARGUMENT);
+
+ std::string regtype = GetFullType(service->mType, service->mProtocol);
+ uint32_t interfaceId = GetInterfaceId(service->mInterface);
+
+ TXTRecordRef record;
+ char buffer[kMdnsTextMaxSize];
+ ReturnErrorOnFailure(PopulateTextRecord(&record, buffer, sizeof(buffer), service->mTextEntries, service->mTextEntrySize));
+
+ return Register(interfaceId, regtype.c_str(), service->mName, service->mPort, &record);
+}
+
+CHIP_ERROR ChipMdnsStopPublish()
+{
+ return MdnsContexts::GetInstance().Removes(ContextType::Register);
+}
+
+CHIP_ERROR ChipMdnsBrowse(const char * type, MdnsServiceProtocol protocol, chip::Inet::IPAddressType addressType,
+ chip::Inet::InterfaceId interface, MdnsBrowseCallback callback, void * context)
+{
+ VerifyOrReturnError(type != nullptr, CHIP_ERROR_INVALID_ARGUMENT);
+ VerifyOrReturnError(callback != nullptr, CHIP_ERROR_INVALID_ARGUMENT);
+ VerifyOrReturnError(IsSupportedProtocol(protocol), CHIP_ERROR_INVALID_ARGUMENT);
+
+ std::string regtype = GetFullType(type, protocol);
+ uint32_t interfaceId = GetInterfaceId(interface);
+
+ return Browse(context, callback, interfaceId, regtype.c_str(), protocol);
+}
+
+CHIP_ERROR ChipMdnsResolve(MdnsService * service, chip::Inet::InterfaceId interface, MdnsResolveCallback callback, void * context)
+{
+ VerifyOrReturnError(service != nullptr, CHIP_ERROR_INVALID_ARGUMENT);
+ VerifyOrReturnError(IsSupportedProtocol(service->mProtocol), CHIP_ERROR_INVALID_ARGUMENT);
+
+ std::string regtype = GetFullType(service->mType, service->mProtocol);
+ uint32_t interfaceId = GetInterfaceId(service->mInterface);
+
+ return Resolve(context, callback, interfaceId, regtype.c_str(), service->mName);
+}
+
+void UpdateMdnsDataset(fd_set & readFdSet, fd_set & writeFdSet, fd_set & errorFdSet, int & maxFd, timeval & timeout)
+{
+ MdnsContexts::GetInstance().PrepareSelect(readFdSet, writeFdSet, errorFdSet, maxFd, timeout);
+}
+
+void ProcessMdns(fd_set & readFdSet, fd_set & writeFdSet, fd_set & errorFdSet)
+{
+ MdnsContexts::GetInstance().HandleSelectResult(readFdSet, writeFdSet, errorFdSet);
+}
+
+} // namespace Mdns
+} // namespace chip
--- /dev/null
+/*
+ *
+ * Copyright (c) 2021 Project CHIP Authors
+ *
+ * Licensed under the Apache License, Version 2.0 (the "License");
+ * you may not use this file except in compliance with the License.
+ * You may obtain a copy of the License at
+ *
+ * http://www.apache.org/licenses/LICENSE-2.0
+ *
+ * Unless required by applicable law or agreed to in writing, software
+ * distributed under the License is distributed on an "AS IS" BASIS,
+ * WITHOUT WARRANTIES OR CONDITIONS OF ANY KIND, either express or implied.
+ * See the License for the specific language governing permissions and
+ * limitations under the License.
+ */
+
+#pragma once
+
+#include <dns_sd.h>
+#include <lib/mdns/platform/Mdns.h>
+#include <string>
+#include <vector>
+
+namespace chip {
+namespace Mdns {
+
+enum class ContextType
+{
+ Register,
+ Browse,
+ Resolve,
+ GetAddrInfo,
+};
+
+struct GenericContext
+{
+ ContextType type;
+ void * context;
+ DNSServiceRef serviceRef;
+};
+
+struct RegisterContext : public GenericContext
+{
+ RegisterContext(void * cbContext)
+ {
+ type = ContextType::Register;
+ context = cbContext;
+ }
+};
+
+struct BrowseContext : public GenericContext
+{
+ MdnsBrowseCallback callback;
+ std::vector<MdnsService> services;
+ MdnsServiceProtocol protocol;
+
+ BrowseContext(void * cbContext, MdnsBrowseCallback cb, MdnsServiceProtocol cbContextProtocol)
+ {
+ type = ContextType::Browse;
+ context = cbContext;
+ callback = cb;
+ protocol = cbContextProtocol;
+ }
+};
+
+struct ResolveContext : public GenericContext
+{
+ MdnsResolveCallback callback;
+
+ ResolveContext(void * cbContext, MdnsResolveCallback cb)
+ {
+ type = ContextType::Resolve;
+ context = cbContext;
+ callback = cb;
+ }
+};
+
+struct GetAddrInfoContext : public GenericContext
+{
+ MdnsResolveCallback callback;
+ std::vector<TextEntry> textEntries;
+ uint16_t port;
+
+ GetAddrInfoContext(void * cbContext, MdnsResolveCallback cb, uint16_t cbContextPort)
+ {
+ type = ContextType::GetAddrInfo;
+ context = cbContext;
+ callback = cb;
+ port = cbContextPort;
+ }
+};
+
+class MdnsContexts
+{
+public:
+ MdnsContexts(const MdnsContexts &) = delete;
+ MdnsContexts & operator=(const MdnsContexts &) = delete;
+ ~MdnsContexts();
+ static MdnsContexts & GetInstance() { return sInstance; }
+
+ void PrepareSelect(fd_set & readFdSet, fd_set & writeFdSet, fd_set & errorFdSet, int & maxFd, timeval & timeout);
+ void HandleSelectResult(fd_set & readFdSet, fd_set & writeFdSet, fd_set & errorFdSet);
+
+ CHIP_ERROR Add(GenericContext * context, DNSServiceRef sdRef);
+ CHIP_ERROR Remove(GenericContext * context);
+ CHIP_ERROR Removes(ContextType type);
+ CHIP_ERROR Get(ContextType type, GenericContext * context);
+
+ void SetHostname(const char * name) { mHostname = name; }
+ const char * GetHostname() { return mHostname.c_str(); }
+
+private:
+ MdnsContexts(){};
+ static MdnsContexts sInstance;
+ std::string mHostname;
+
+ void Delete(GenericContext * context);
+ std::vector<GenericContext *> mContexts;
+};
+
+} // namespace Mdns
+} // namespace chip
#include <platform/internal/BLEManager.h>
+#include "FreeRTOS.h"
#include "sl_bt_api.h"
#include "sl_bt_stack_config.h"
#include "sl_bt_stack_init.h"
+#include "timers.h"
#include <ble/CHIPBleServiceData.h>
#include <platform/EFR32/freertos_bluetooth.h>
#include <support/CodeUtils.h>
#define BLE_CONFIG_RF_PATH_GAIN_TX (0)
#define BLE_CONFIG_RF_PATH_GAIN_RX (0)
+TimerHandle_t sbleAdvTimeoutTimer; // FreeRTOS sw timer.
+
/* Bluetooth stack configuration parameters (see "UG136: Silicon Labs Bluetooth C Application Developer's Guide" for
* details on each parameter) */
static sl_bt_configuration_t config;
CHIP_DEVICE_CONFIG_BLE_APP_TASK_PRIORITY, /* Priority at which the task is created. */
NULL); /* Variable to hold the task's data structure. */
+ // Create FreeRTOS sw timer for BLE timeouts and interval change.
+ sbleAdvTimeoutTimer = xTimerCreate("BleAdvTimer", // Just a text name, not used by the RTOS kernel
+ 1, // == default timer period (mS)
+ false, // no timer reload (==one-shot)
+ (void *) this, // init timer id = ble obj context
+ BleAdvTimeoutHandler // timer callback handler
+ );
+
mFlags.ClearAll().Set(Flags::kAdvertisingEnabled, CHIP_DEVICE_CONFIG_CHIPOBLE_ENABLE_ADVERTISING_AUTOSTART);
mFlags.Set(Flags::kFastAdvertisingEnabled, true);
PlatformMgr().ScheduleWork(DriveBLEState, 0);
{
CHIP_ERROR err;
sl_status_t ret;
+ const uint8_t kResolvableRandomAddrType = 2; // Private resolvable random address type
+ bd_addr unusedBdAddr; // We can ignore this field when setting random address.
uint32_t interval_min;
uint32_t interval_max;
uint16_t numConnectionss = NumConnections();
err = ConfigureAdvertisingData();
SuccessOrExit(err);
+ sl_bt_advertiser_set_random_address(advertising_set_handle, kResolvableRandomAddrType, unusedBdAddr, &unusedBdAddr);
+ (void) unusedBdAddr;
+
mFlags.Clear(Flags::kRestartAdvertising);
if ((numConnectionss == 0 && !ConfigurationMgr().IsPairedToAccount()) || mFlags.Has(Flags::kFastAdvertisingEnabled))
if (SL_STATUS_OK == ret)
{
+ uint32_t BleAdvTimeoutMs = (mFlags.Has(Flags::kFastAdvertisingEnabled) ? CHIP_DEVICE_CONFIG_BLE_FAST_ADVERTISING_TIMEOUT
+ : CHIP_DEVICE_CONFIG_BLE_ADVERTISING_TIMEOUT);
+ StartBleAdvTimeoutTimer(BleAdvTimeoutMs);
mFlags.Set(Flags::kAdvertising);
}
advertising_set_handle = 0xff;
err = MapBLEError(ret);
SuccessOrExit(err);
+
+ CancelBleAdvTimeoutTimer();
}
exit:
// Arrange to re-enable connectable advertising in case it was disabled due to the
// maximum connection limit being reached.
mFlags.Set(Flags::kRestartAdvertising);
+ mFlags.Set(Flags::kFastAdvertisingEnabled);
PlatformMgr().ScheduleWork(DriveBLEState, 0);
}
}
return freeIndex;
}
+void BLEManagerImpl::BleAdvTimeoutHandler(TimerHandle_t xTimer)
+{
+ CHIP_ERROR err;
+ sl_status_t ret;
+
+ if (sInstance.mFlags.Has(Flags::kFastAdvertisingEnabled))
+ {
+ ChipLogDetail(DeviceLayer, "bleAdv Timeout : Start slow advertissment");
+
+ sInstance.mFlags.Clear(Flags::kFastAdvertisingEnabled);
+
+ // stop advertiser, change interval and restart it;
+ sl_bt_advertiser_stop(sInstance.advertising_set_handle);
+ ret = sl_bt_advertiser_set_timing(sInstance.advertising_set_handle, CHIP_DEVICE_CONFIG_BLE_SLOW_ADVERTISING_INTERVAL,
+ CHIP_DEVICE_CONFIG_BLE_SLOW_ADVERTISING_INTERVAL, 0, 0);
+
+ err = sInstance.MapBLEError(ret);
+ SuccessOrExit(err);
+
+ uint8_t connectableAdv = (sInstance.NumConnections() < kMaxConnections) ? sl_bt_advertiser_connectable_scannable
+ : sl_bt_advertiser_scannable_non_connectable;
+ ret = sl_bt_advertiser_start(sInstance.advertising_set_handle, sl_bt_advertiser_user_data, connectableAdv);
+ err = sInstance.MapBLEError(ret);
+ SuccessOrExit(err);
+
+ sInstance.StartBleAdvTimeoutTimer(CHIP_DEVICE_CONFIG_BLE_ADVERTISING_TIMEOUT); // Slow advertise for 15 Minutesß
+ }
+ else if (sInstance._IsAdvertisingEnabled())
+ {
+ // advertissement expired. we stop advertissing
+ ChipLogDetail(DeviceLayer, "bleAdv Timeout : Stop advertissement");
+ sInstance.StopAdvertising();
+ }
+
+exit:
+ if (err != CHIP_NO_ERROR)
+ {
+ ChipLogError(DeviceLayer, "Changing Bl advertiser interval failed %s", ErrorStr(err));
+ }
+}
+
+void BLEManagerImpl::CancelBleAdvTimeoutTimer(void)
+{
+ if (xTimerStop(sbleAdvTimeoutTimer, 0) == pdFAIL)
+ {
+ ChipLogError(DeviceLayer, "Failed to stop BledAdv timeout timer");
+ }
+}
+
+void BLEManagerImpl::StartBleAdvTimeoutTimer(uint32_t aTimeoutInMs)
+{
+ if (xTimerIsTimerActive(sbleAdvTimeoutTimer))
+ {
+ CancelBleAdvTimeoutTimer();
+ }
+
+ // timer is not active, change its period to required value (== restart).
+ // FreeRTOS- Block for a maximum of 100 ticks if the change period command
+ // cannot immediately be sent to the timer command queue.
+ if (xTimerChangePeriod(sbleAdvTimeoutTimer, aTimeoutInMs / portTICK_PERIOD_MS, 100) != pdPASS)
+ {
+ ChipLogError(DeviceLayer, "Failed to start BledAdv timeout timer");
+ }
+}
+
void BLEManagerImpl::DriveBLEState(intptr_t arg)
{
sInstance.DriveBLEState();
#pragma once
#if CHIP_DEVICE_CONFIG_ENABLE_CHIPOBLE
+#include "FreeRTOS.h"
#include "gatt_db.h"
#include "sl_bgapi.h"
#include "sl_bt_api.h"
+#include "timers.h"
namespace chip {
namespace DeviceLayer {
void HandleSoftTimerEvent(volatile sl_bt_msg_t * evt);
bool RemoveConnection(uint8_t connectionHandle);
void AddConnection(uint8_t connectionHandle, uint8_t bondingHandle);
+ void StartBleAdvTimeoutTimer(uint32_t aTimeoutInMs);
+ void CancelBleAdvTimeoutTimer(void);
CHIPoBLEConState * GetConnectionState(uint8_t conId, bool allocate = false);
uint8_t GetTimerHandle(uint8_t connectionHandle, bool allocate = false);
static void DriveBLEState(intptr_t arg);
static void bluetoothStackEventHandler(void * p_arg);
+ static void BleAdvTimeoutHandler(TimerHandle_t xTimer);
};
/**
CHIP_ERROR err;
wifi_init_config_t cfg;
uint8_t ap_mac[6];
-
- esp_fill_random(ap_mac, sizeof(ap_mac));
- /* Bit 0 of the first octet of MAC Address should always be 0 */
- ap_mac[0] &= (uint8_t) ~0x01;
+ wifi_mode_t mode;
// Make sure the LwIP core lock has been initialized
err = Internal::InitLwIPCoreLock();
err = esp_wifi_init(&cfg);
SuccessOrExit(err);
- err = esp_wifi_set_mac(ESP_IF_WIFI_AP, ap_mac);
- SuccessOrExit(err);
+ esp_wifi_get_mode(&mode);
+ if ((mode == WIFI_MODE_AP) || (mode == WIFI_MODE_APSTA))
+ {
+ esp_fill_random(ap_mac, sizeof(ap_mac));
+ /* Bit 0 of the first octet of MAC Address should always be 0 */
+ ap_mac[0] &= (uint8_t) ~0x01;
+ err = esp_wifi_set_mac(ESP_IF_WIFI_AP, ap_mac);
+ SuccessOrExit(err);
+ }
// Call _InitChipStack() on the generic implementation base class
// to finish the initialization process.
memset(&adv_params, 0, sizeof(adv_params));
uint8_t own_addr_type = BLE_OWN_ADDR_RANDOM;
- ret = ble_hs_pvcy_rpa_config(NIMBLE_HOST_ENABLE_RPA);
- if (ret != 0)
- {
- ChipLogError(DeviceLayer, "RPA not set: %d", ret);
- return CHIP_ERROR_INTERNAL;
- }
-
adv_params.disc_mode = BLE_GAP_DISC_MODE_GEN;
// Inform the ThreadStackManager that CHIPoBLE advertising is about to start.
bool connectable = (numCons < kMaxConnections);
adv_params.conn_mode = connectable ? BLE_GAP_CONN_MODE_UND : BLE_GAP_CONN_MODE_NON;
- // Advertise in fast mode if not fully provisioned and there are no CHIPoBLE connections, or
- // if the application has expressly requested fast advertising.
- if ((numCons == 0 && !ConfigurationMgr().IsPairedToAccount()) || mFlags.Has(Flags::kFastAdvertisingEnabled))
+ // Advertise in fast mode if it is connectable advertisement and
+ // the application has expressly requested fast advertising.
+ if (connectable && mFlags.Has(Flags::kFastAdvertisingEnabled))
{
adv_params.itvl_min = CHIP_DEVICE_CONFIG_BLE_FAST_ADVERTISING_INTERVAL_MIN;
adv_params.itvl_max = CHIP_DEVICE_CONFIG_BLE_FAST_ADVERTISING_INTERVAL_MAX;
(((uint32_t) adv_params.itvl_min) * 10) / 16, (connectable) ? "" : "non-", mDeviceName);
{
- ret = ble_gap_adv_start(own_addr_type, NULL, BLE_HS_FOREVER, &adv_params, ble_svr_gap_event, NULL);
- if (ret == BLE_HS_EALREADY)
+ if (ble_gap_adv_active())
{
- /* This error code indicates that the advertising is already active. Stop and restart with the new parameters */
+ /* Advertising is already active. Stop and restart with the new parameters */
ChipLogProgress(DeviceLayer, "Device already advertising, stop active advertisement and restart");
ret = ble_gap_adv_stop();
if (ret != 0)
ChipLogError(DeviceLayer, "ble_gap_adv_stop() failed: %d, cannot restart", ret);
return CHIP_ERROR_INTERNAL;
}
- else
+ }
+ else
+ {
+ ret = ble_hs_pvcy_rpa_config(NIMBLE_HOST_ENABLE_RPA);
+ if (ret != 0)
{
- ret = ble_gap_adv_start(own_addr_type, NULL, BLE_HS_FOREVER, &adv_params, ble_svr_gap_event, NULL);
+ ChipLogError(DeviceLayer, "RPA not set: %d", ret);
+ return CHIP_ERROR_INTERNAL;
}
}
+ ret = ble_gap_adv_start(own_addr_type, NULL, BLE_HS_FOREVER, &adv_params, ble_svr_gap_event, NULL);
if (ret == 0)
{
#include <support/CodeUtils.h>
#include <support/SafeInt.h>
+#include <cassert>
#include <type_traits>
#include <utility>
namespace {
static constexpr unsigned kNewConnectionScanTimeoutMs = 10000;
+static constexpr unsigned kConnectTimeoutMs = 5000;
const ChipBleUUID ChipUUID_CHIPoBLEChar_RX = { { 0x18, 0xEE, 0x2E, 0xF5, 0x26, 0x3D, 0x45, 0x59, 0x95, 0x9F, 0x4F, 0x9C, 0x42, 0x9F,
0x9D, 0x11 } };
const ChipBleUUID ChipUUID_CHIPoBLEChar_TX = { { 0x18, 0xEE, 0x2E, 0xF5, 0x26, 0x3D, 0x45, 0x59, 0x95, 0x9F, 0x4F, 0x9C, 0x42, 0x9F,
0x9D, 0x12 } };
+void HandleConnectTimeout(chip::System::Layer *, void * apEndpoint, chip::System::Error)
+{
+ assert(apEndpoint != nullptr);
+
+ CancelConnect(static_cast<BluezEndpoint *>(apEndpoint));
+ BLEManagerImpl::HandleConnectFailed(CHIP_ERROR_TIMEOUT);
+}
+
} // namespace
BLEManagerImpl BLEManagerImpl::sInstance;
switch (apEvent->Type)
{
case DeviceEventType::kPlatformLinuxBLECentralConnected:
- if (OnConnectionComplete != nullptr)
+ if (mBLEScanConfig.mBleScanState == BleScanState::kConnecting)
+ {
OnConnectionComplete(mBLEScanConfig.mAppState, apEvent->Platform.BLECentralConnected.mConnection);
+ CleanScanConfig();
+ }
+ break;
+ case DeviceEventType::kPlatformLinuxBLECentralConnectFailed:
+ if (mBLEScanConfig.mBleScanState == BleScanState::kConnecting)
+ {
+ OnConnectionError(mBLEScanConfig.mAppState, apEvent->Platform.BLECentralConnectFailed.mError);
+ CleanScanConfig();
+ }
break;
case DeviceEventType::kPlatformLinuxBLEWriteComplete:
HandleWriteConfirmation(apEvent->Platform.BLEWriteComplete.mConnection, &CHIP_BLE_SVC_ID, &ChipUUID_CHIPoBLEChar_RX);
}
}
+void BLEManagerImpl::HandleConnectFailed(CHIP_ERROR error)
+{
+ if (sInstance.mIsCentral)
+ {
+ ChipDeviceEvent event;
+ event.Type = DeviceEventType::kPlatformLinuxBLECentralConnectFailed;
+ event.Platform.BLECentralConnectFailed.mError = error;
+ PlatformMgr().PostEvent(&event);
+ }
+}
+
void BLEManagerImpl::HandleWriteComplete(BLE_CONNECTION_OBJECT conId)
{
ChipDeviceEvent event;
return;
}
- mDeviceScanner = Internal::ChipDeviceScanner::Create(mpEndpoint->mpAdapter, this);
-
- mBLEScanConfig.bleScanState = BleScanState::kScanForDiscriminator;
+ mDeviceScanner = Internal::ChipDeviceScanner::Create(mpEndpoint->mpAdapter, this);
+ mBLEScanConfig.mBleScanState = scanType;
if (!mDeviceScanner)
{
- mBLEScanConfig.bleScanState = BleScanState::kNotScanning;
+ mBLEScanConfig.mBleScanState = BleScanState::kNotScanning;
OnConnectionError(mBLEScanConfig.mAppState, CHIP_ERROR_INTERNAL);
ChipLogError(Ble, "Failed to create a BLE device scanner");
return;
CHIP_ERROR err = mDeviceScanner->StartScan(kNewConnectionScanTimeoutMs);
if (err != CHIP_NO_ERROR)
{
- mBLEScanConfig.bleScanState = BleScanState::kNotScanning;
+ mBLEScanConfig.mBleScanState = BleScanState::kNotScanning;
ChipLogError(Ble, "Failed to start a BLE can: %s", chip::ErrorStr(err));
OnConnectionError(mBLEScanConfig.mAppState, err);
return;
}
}
+void BLEManagerImpl::CleanScanConfig()
+{
+ if (mBLEScanConfig.mBleScanState == BleScanState::kConnecting)
+ DeviceLayer::SystemLayer.CancelTimer(HandleConnectTimeout, mpEndpoint);
+
+ mBLEScanConfig.mBleScanState = BleScanState::kNotScanning;
+}
+
void BLEManagerImpl::InitiateScan(intptr_t arg)
{
sInstance.InitiateScan(static_cast<BleScanState>(arg));
{
ChipLogProgress(Ble, "New device scanned: %s", bluez_device1_get_address(device));
- if (mBLEScanConfig.bleScanState == BleScanState::kScanForDiscriminator)
+ if (mBLEScanConfig.mBleScanState == BleScanState::kScanForDiscriminator)
{
if (info.GetDeviceDiscriminator() != mBLEScanConfig.mDiscriminator)
{
}
ChipLogProgress(Ble, "Device discriminator match. Attempting to connect.");
}
- else if (mBLEScanConfig.bleScanState == BleScanState::kScanForAddress)
+ else if (mBLEScanConfig.mBleScanState == BleScanState::kScanForAddress)
{
if (strcmp(bluez_device1_get_address(device), mBLEScanConfig.mAddress.c_str()) != 0)
{
return;
}
- mBLEScanConfig.bleScanState = BleScanState::kNotScanning;
+ mBLEScanConfig.mBleScanState = BleScanState::kConnecting;
+ DeviceLayer::SystemLayer.StartTimer(kConnectTimeoutMs, HandleConnectTimeout, mpEndpoint);
mDeviceScanner->StopScan();
- ConnectDevice(device);
+ ConnectDevice(device, mpEndpoint);
}
void BLEManagerImpl::OnScanComplete()
{
- if (mBLEScanConfig.bleScanState == BleScanState::kNotScanning)
+ if (mBLEScanConfig.mBleScanState != BleScanState::kScanForDiscriminator &&
+ mBLEScanConfig.mBleScanState != BleScanState::kScanForAddress)
{
- ChipLogError(Ble, "Scan complete notification without an active scan.");
+ ChipLogProgress(Ble, "Scan complete notification without an active scan.");
return;
}
OnConnectionError(mBLEScanConfig.mAppState, CHIP_ERROR_TIMEOUT);
- mBLEScanConfig.bleScanState = BleScanState::kNotScanning;
+ mBLEScanConfig.mBleScanState = BleScanState::kNotScanning;
}
} // namespace Internal
const char * mpAdvertisingUUID;
};
-enum class BleScanState
+enum class BleScanState : uint8_t
{
kNotScanning,
kScanForDiscriminator,
kScanForAddress,
+ kConnecting,
};
struct BLEScanConfig
{
- // If a active scan for connection is being performed
- BleScanState bleScanState = BleScanState::kNotScanning;
+ // If an active scan for connection is being performed
+ BleScanState mBleScanState = BleScanState::kNotScanning;
// If scanning by discriminator, what are we scanning for
uint16_t mDiscriminator = 0;
// Driven by BlueZ IO
static void HandleNewConnection(BLE_CONNECTION_OBJECT conId);
+ static void HandleConnectFailed(CHIP_ERROR error);
static void HandleWriteComplete(BLE_CONNECTION_OBJECT conId);
static void HandleSubscribeOpComplete(BLE_CONNECTION_OBJECT conId, bool subscribed);
static void HandleTXCharChanged(BLE_CONNECTION_OBJECT conId, const uint8_t * value, size_t len);
static void CHIPoBluez_ConnectionClosed(BLE_CONNECTION_OBJECT user_data);
static void HandleTXCharCCCDWrite(BLE_CONNECTION_OBJECT user_data);
static void HandleTXComplete(BLE_CONNECTION_OBJECT user_data);
- static bool WoBLEz_TimerCb(BLE_CONNECTION_OBJECT user_data);
static void NotifyBLEPeripheralRegisterAppComplete(bool aIsSuccess, void * apAppstate);
static void NotifyBLEPeripheralAdvConfiguredComplete(bool aIsSuccess, void * apAppstate);
void InitiateScan(BleScanState scanType);
static void InitiateScan(intptr_t arg);
+ void CleanScanConfig();
CHIPoBLEServiceMode mServiceMode;
BLEAdvConfig mBLEAdvConfig;
{
kPlatformLinuxEvent = kRange_InternalPlatformSpecific,
kPlatformLinuxBLECentralConnected,
+ kPlatformLinuxBLECentralConnectFailed,
kPlatformLinuxBLEWriteComplete,
kPlatformLinuxBLESubscribeOpComplete,
kPlatformLinuxBLEIndicationReceived,
} BLECentralConnected;
struct
{
+ CHIP_ERROR mError;
+ } BLECentralConnectFailed;
+ struct
+ {
BLE_CONNECTION_OBJECT mConnection;
} BLEWriteComplete;
struct
#include <thread>
-#include "MdnsImpl.h"
-
#include <arpa/inet.h>
#include <linux/netlink.h>
#include <linux/rtnetlink.h>
} \
} while (0)
+constexpr int kDBusConnectionPollingTimeoutMS = 10;
+
namespace chip {
namespace DeviceLayer {
DBusConnection * dispatchConnection;
dbus_error_init(&dbusError);
- mConnection = UniqueDBusConnection(dbus_bus_get(DBUS_BUS_SYSTEM, &dbusError));
- VerifyOrExit(dbus_bus_register(mConnection.get(), &dbusError), error = ClientError::ERROR_DBUS);
+ mConnection = UniqueDBusConnection(dbus_bus_get_private(DBUS_BUS_SYSTEM, &dbusError));
VerifyOrExit(mConnection != nullptr, error = ClientError::ERROR_DBUS);
mThreadApi = std::unique_ptr<otbr::DBus::ThreadApiDBus>(new otbr::DBus::ThreadApiDBus(mConnection.get()));
mDBusEventLoop = std::thread([dispatchConnection]() {
while (true)
{
- dbus_connection_read_write_dispatch(dispatchConnection, -1);
+ // The dbus_connection_read_write will lock the connection until new message comes or timeout.
+ // This will block ot-br-posix APIs. Set timeout to 10ms so it can work.
+ // TODO: we should have a global event loop for dbus to take care of this.
+ dbus_connection_read_write_dispatch(dispatchConnection, kDBusConnectionPollingTimeoutMS);
}
});
mDBusEventLoop.detach();
#include <errno.h>
#include <pthread.h>
-#include <support/ReturnMacros.h>
#include <support/logging/CHIPLogging.h>
namespace chip {
#include <protocols/Protocols.h>
#include <setup_payload/AdditionalDataPayloadGenerator.h>
#include <support/BitFlags.h>
+#include <support/CHIPMem.h>
#include <support/CHIPMemString.h>
#if CHIP_DEVICE_CONFIG_ENABLE_CHIPOBLE
+#include <cassert>
#include <errno.h>
#include <gio/gunixfdlist.h>
#include <limits>
#include <platform/Linux/BLEManagerImpl.h>
#include <support/CodeUtils.h>
-#include <support/ReturnMacros.h>
#include <system/TLVPacketBufferBackingStore.h>
#include "BluezObjectIterator.h"
g_free(apEndpoint->mpPeerDevicePath);
apEndpoint->mpPeerDevicePath = nullptr;
}
-
+ g_free(apEndpoint->mpConnectCancellable);
g_free(apEndpoint);
}
}
}
else
{
- endpoint->mAdapterId = aBleAdvConfig.mAdapterId;
+ endpoint->mAdapterId = aBleAdvConfig.mAdapterId;
+ endpoint->mpConnectCancellable = g_cancellable_new();
}
err = MainLoop::Instance().EnsureStarted();
// ConnectDevice callbacks
+struct ConnectParams
+{
+ ConnectParams(BluezDevice1 * device, BluezEndpoint * endpoint) : mDevice(device), mEndpoint(endpoint) {}
+ BluezDevice1 * mDevice;
+ BluezEndpoint * mEndpoint;
+};
+
static void ConnectDeviceDone(GObject * aObject, GAsyncResult * aResult, gpointer)
{
BluezDevice1 * device = BLUEZ_DEVICE1(aObject);
GError * error = nullptr;
gboolean success = bluez_device1_call_connect_finish(device, aResult, &error);
- VerifyOrExit(success == TRUE, ChipLogError(DeviceLayer, "FAIL: ConnectDevice : %s", error->message));
+ if (!success)
+ {
+ ChipLogError(DeviceLayer, "FAIL: ConnectDevice : %s", error->message);
+ BLEManagerImpl::HandleConnectFailed(CHIP_ERROR_INTERNAL);
+ ExitNow();
+ }
+
ChipLogDetail(DeviceLayer, "ConnectDevice complete");
exit:
g_error_free(error);
}
-static gboolean ConnectDeviceImpl(BluezDevice1 * device)
+static gboolean ConnectDeviceImpl(ConnectParams * apParams)
{
- VerifyOrExit(device != nullptr, ChipLogError(DeviceLayer, "device is NULL in %s", __func__));
+ BluezDevice1 * device = apParams->mDevice;
+ BluezEndpoint * endpoint = apParams->mEndpoint;
+
+ assert(device != nullptr);
+ assert(endpoint != nullptr);
- bluez_device1_call_connect(device, nullptr, ConnectDeviceDone, nullptr);
+ g_cancellable_reset(endpoint->mpConnectCancellable);
+ bluez_device1_call_connect(device, endpoint->mpConnectCancellable, ConnectDeviceDone, nullptr);
g_object_unref(device);
+ chip::Platform::Delete(apParams);
-exit:
return G_SOURCE_REMOVE;
}
-CHIP_ERROR ConnectDevice(BluezDevice1 * apDevice)
+CHIP_ERROR ConnectDevice(BluezDevice1 * apDevice, BluezEndpoint * apEndpoint)
{
- CHIP_ERROR error = CHIP_NO_ERROR;
+ auto params = chip::Platform::New<ConnectParams>(apDevice, apEndpoint);
g_object_ref(apDevice);
- if (!MainLoop::Instance().Schedule(ConnectDeviceImpl, apDevice))
+ if (!MainLoop::Instance().Schedule(ConnectDeviceImpl, params))
{
ChipLogError(Ble, "Failed to schedule ConnectDeviceImpl() on CHIPoBluez thread");
g_object_unref(apDevice);
- error = CHIP_ERROR_INCORRECT_STATE;
+ chip::Platform::Delete(params);
+ return CHIP_ERROR_INCORRECT_STATE;
}
- return error;
+ return CHIP_NO_ERROR;
+}
+
+void CancelConnect(BluezEndpoint * apEndpoint)
+{
+ assert(apEndpoint->mpConnectCancellable != nullptr);
+ g_cancellable_cancel(apEndpoint->mpConnectCancellable);
}
} // namespace Internal
/// Unsubscribe from the CHIP TX characteristic on the remote peripheral device
bool BluezUnsubscribeCharacteristic(BLE_CONNECTION_OBJECT apConn);
-CHIP_ERROR ConnectDevice(BluezDevice1 * apDevice);
+CHIP_ERROR ConnectDevice(BluezDevice1 * apDevice, BluezEndpoint * apEndpoint);
+void CancelConnect(BluezEndpoint * apEndpoint);
} // namespace Internal
} // namespace DeviceLayer
uint16_t mDuration; ///< Advertisement interval (in ms).
bool mIsAdvertising;
char * mpPeerDevicePath;
+ GCancellable * mpConnectCancellable = nullptr;
};
struct BluezConnection
#include <platform/internal/CHIPDeviceLayerInternal.h>
#include <platform/internal/DeviceNetworkInfo.h>
#include <support/CodeUtils.h>
-#include <support/ReturnMacros.h>
#include <support/logging/CHIPLogging.h>
extern "C" void otSysProcessDrivers(otInstance * aInstance);
VerifyOrExit(aHostName, error = CHIP_ERROR_INVALID_ARGUMENT);
VerifyOrExit(strlen(aHostName) < SrpClient::kMaxHostNameSize, error = CHIP_ERROR_INVALID_STRING_LENGTH);
- memcpy(mSrpClient.mHostName, aHostName, strlen(aHostName) + 1);
- error = MapOpenThreadError(otSrpClientSetHostName(mOTInst, aHostName));
- SuccessOrExit(error);
+ // Avoid adding the same host name multiple times
+ if (strcmp(mSrpClient.mHostName, aHostName) != 0)
+ {
+ strcpy(mSrpClient.mHostName, aHostName);
+ error = MapOpenThreadError(otSrpClientSetHostName(mOTInst, aHostName));
+ SuccessOrExit(error);
+ }
// Check if device has any external IPv6 assigned. If not, host will be set without IPv6 addresses
// and updated later on.
#include <platform/KeyValueStoreManager.h>
#include <support/CodeUtils.h>
-#include <support/ReturnMacros.h>
#include <support/logging/CHIPLogging.h>
#include <logging/log.h>
if (chip_device_platform == "linux" || chip_device_platform == "esp32") {
chip_mdns = "minimal"
+ } else if (chip_device_platform == "darwin") {
+ chip_mdns = "platform"
} else {
chip_mdns = "none"
}
}
if (chip_mdns != "none" && chip_enable_happy_tests &&
- chip_device_platform == "linux") {
+ (chip_device_platform == "linux" || chip_device_platform == "darwin")) {
test_sources += [ "TestMdns.cpp" ]
}
"${chip_root}/src/lib/support",
"${chip_root}/src/messaging",
"${chip_root}/src/protocols/bdx",
+ "${chip_root}/src/protocols/secure_channel",
]
}
//
// CHIP Protocol Ids (32-bits max)
//
-
-enum CHIPProtocolId
+class Id
{
- // Common Protocols
- //
- // NOTE: Do not attempt to allocate these values yourself.
-
- kProtocol_SecureChannel = (kChipVendor_Common << 16) | 0x0000, // Secure Channel Protocol
- kProtocol_Echo = (kChipVendor_Common << 16) | 0x0002, // Echo Protocol
- kProtocol_BDX = (kChipVendor_Common << 16) | 0x0003, // Bulk Data Exchange Protocol
- kProtocol_NetworkProvisioning = (kChipVendor_Common << 16) | 0x0004, // Network Provisioning Protocol
- kProtocol_InteractionModel = (kChipVendor_Common << 16) | 0x0005, // Interaction Model Protocol
- kProtocol_FabricProvisioning = (kChipVendor_Common << 16) | 0x0006, // Fabric Provisioning Protocol
- kProtocol_ServiceProvisioning = (kChipVendor_Common << 16) | 0x0007, // Service Provisioning Protocol
- kProtocol_OpCredentials = (kChipVendor_Common << 16) | 0x0008, // Operational Credentials
-
- // Protocols reserved for internal protocol use
-
- kProtocol_NotSpecified = (kChipVendor_NotSpecified << 16) | 0xFFFF, // The profile ID is either not specified or a wildcard
+public:
+ constexpr Id(VendorId aVendorId, uint16_t aProtocolId) : mVendorId(aVendorId), mProtocolId(aProtocolId) {}
+
+ constexpr bool operator==(const Id & aOther) { return mVendorId == aOther.mVendorId && mProtocolId == aOther.mProtocolId; }
+
+ // Convert the Protocols::Id to a TLV profile id.
+ // NOTE: We may want to change the TLV reader/writer to take Protocols::Id
+ // directly later on and get rid of this method.
+ constexpr uint32_t ToTLVProfileId() const { return ToUint32(); }
+
+ // Convert the protocol id to a 32-bit unsigned integer "fully qualified"
+ // form as defined in the spec. This should only be used in the places
+ // where the spec defines a 32-bit unsigned in as a wire representation of
+ // protocol id.
+ constexpr uint32_t ToFullyQualifiedSpecForm() const { return ToUint32(); }
+
+ constexpr VendorId GetVendorId() const { return mVendorId; }
+ constexpr uint16_t GetProtocolId() const { return mProtocolId; }
+
+private:
+ constexpr uint32_t ToUint32() const { return (static_cast<uint32_t>(mVendorId) << 16) | mProtocolId; }
+
+ chip::VendorId mVendorId;
+ uint16_t mProtocolId;
};
+// Common Protocols
+//
+// NOTE: Do not attempt to allocate these values yourself.
+#define CHIP_STANDARD_PROTOCOL(name, id) \
+ namespace name { \
+ static constexpr Protocols::Id Id(VendorId::Common, id); \
+ } // namespace name.
+
+CHIP_STANDARD_PROTOCOL(SecureChannel, 0x0000) // Secure Channel Protocol
+CHIP_STANDARD_PROTOCOL(Echo, 0x0002) // Echo Protocol
+CHIP_STANDARD_PROTOCOL(BDX, 0x0003) // Bulk Data Exchange Protocol
+CHIP_STANDARD_PROTOCOL(NetworkProvisioning, 0x0004) // Network Provisioning Protocol
+CHIP_STANDARD_PROTOCOL(InteractionModel, 0x0005) // Interaction Model Protocol
+CHIP_STANDARD_PROTOCOL(FabricProvisioning, 0x0006) // Fabric Provisioning Protocol
+CHIP_STANDARD_PROTOCOL(ServiceProvisioning, 0x0007) // Service Provisioning Protocol
+CHIP_STANDARD_PROTOCOL(OpCredentials, 0x0008) // Operational Credentials
+
+#undef CHIP_STANDARD_PROTOCOL
+
+// Protocols reserved for internal protocol use
+static constexpr Id NotSpecified(VendorId::NotSpecified, 0xFFFF); // The profile ID is either not specified or a wildcard
+
// Pre-delare our MessageTypeTraits so message type headers know what they are
// specializing.
template <typename T>
public_deps = [
"${chip_root}/src/lib/core",
"${chip_root}/src/lib/support",
+ "${chip_root}/src/protocols/secure_channel",
"${chip_root}/src/system",
"${chip_root}/src/transport",
]
kLengthRequired = 0x0015,
kBadMessageContents = 0x0016,
kBadBlockCounter = 0x0017,
+ kUnexpectedMessage = 0x0018,
kTransferFailedUnknownError = 0x001F,
- kServerBadState = 0x0020,
kFailureToSend = 0x0021,
kTransferMethodNotSupported = 0x0050,
kFileDesignatorUnknown = 0x0051,
template <>
struct MessageTypeTraits<bdx::MessageType>
{
- static constexpr uint16_t ProtocolId = chip::Protocols::kProtocol_BDX;
+ static constexpr const Protocols::Id & ProtocolId() { return BDX::Id; }
};
} // namespace Protocols
#include <protocols/Protocols.h>
#include <protocols/bdx/BdxMessages.h>
#include <protocols/secure_channel/Constants.h>
+#include <protocols/secure_channel/StatusReport.h>
#include <support/BufferReader.h>
#include <support/CodeUtils.h>
-#include <support/ReturnMacros.h>
#include <system/SystemPacketBuffer.h>
#include <transport/SecureSessionMgr.h>
+#include <type_traits>
+
namespace {
-constexpr uint8_t kBdxVersion = 0; ///< The version of this implementation of the BDX spec
-constexpr size_t kStatusReportMinSize = 2 + 4 + 2; ///< 16 bits for GeneralCode, 32 bits for ProtocolId, 16 bits for ProtocolCode
+constexpr uint8_t kBdxVersion = 0; ///< The version of this implementation of the BDX spec
/**
* @brief
// We could make this whole method a template, but it's probably smaller code to
// share the implementation across all message types.
-CHIP_ERROR AttachHeader(uint16_t protocolId, uint8_t msgType, ::chip::System::PacketBufferHandle & msgBuf)
+CHIP_ERROR AttachHeader(chip::Protocols::Id protocolId, uint8_t msgType, ::chip::System::PacketBufferHandle & msgBuf)
{
::chip::PayloadHeader payloadHeader;
template <typename MessageType>
inline CHIP_ERROR AttachHeader(MessageType msgType, ::chip::System::PacketBufferHandle & msgBuf)
{
- return AttachHeader(chip::Protocols::MessageTypeTraits<MessageType>::ProtocolId, static_cast<uint8_t>(msgType), msgBuf);
+ return AttachHeader(chip::Protocols::MessageTypeTraits<MessageType>::ProtocolId(), static_cast<uint8_t>(msgType), msgBuf);
}
} // anonymous namespace
err = payloadHeader.DecodeAndConsume(msg);
SuccessOrExit(err);
- if (payloadHeader.GetProtocolID() == Protocols::kProtocol_BDX)
+ if (payloadHeader.HasProtocol(Protocols::BDX::Id))
{
err = HandleBdxMessage(payloadHeader, std::move(msg));
SuccessOrExit(err);
mState = TransferState::kErrorState;
mAwaitingResponse = false;
- uint16_t generalCode = 0;
- uint32_t protocolId = 0;
- uint16_t protocolCode = 0;
- Encoding::LittleEndian::Reader reader(msg->Start(), msg->DataLength());
- ReturnErrorOnFailure(reader.Read16(&generalCode).Read32(&protocolId).Read16(&protocolCode).StatusCode());
- VerifyOrReturnError((protocolId == Protocols::kProtocol_BDX), CHIP_ERROR_INVALID_MESSAGE_TYPE);
+ Protocols::SecureChannel::StatusReport report;
+ ReturnErrorOnFailure(report.Parse(std::move(msg)));
+ VerifyOrReturnError((report.GetProtocolId() == Protocols::BDX::Id.ToFullyQualifiedSpecForm()), CHIP_ERROR_INVALID_MESSAGE_TYPE);
- mStatusReportData.statusCode = static_cast<StatusCode>(protocolCode);
+ mStatusReportData.statusCode = static_cast<StatusCode>(report.GetProtocolCode());
mPendingOutput = OutputEventType::kStatusReceived;
CHIP_ERROR err = CHIP_NO_ERROR;
TransferInit transferInit;
- VerifyOrExit(mState == TransferState::kAwaitingInitMsg, PrepareStatusReport(StatusCode::kServerBadState));
+ VerifyOrExit(mState == TransferState::kAwaitingInitMsg, PrepareStatusReport(StatusCode::kUnexpectedMessage));
if (mRole == TransferRole::kSender)
{
- VerifyOrExit(msgType == MessageType::ReceiveInit, PrepareStatusReport(StatusCode::kServerBadState));
+ VerifyOrExit(msgType == MessageType::ReceiveInit, PrepareStatusReport(StatusCode::kUnexpectedMessage));
}
else
{
- VerifyOrExit(msgType == MessageType::SendInit, PrepareStatusReport(StatusCode::kServerBadState));
+ VerifyOrExit(msgType == MessageType::SendInit, PrepareStatusReport(StatusCode::kUnexpectedMessage));
}
err = transferInit.Parse(msgData.Retain());
CHIP_ERROR err = CHIP_NO_ERROR;
ReceiveAccept rcvAcceptMsg;
- VerifyOrExit(mRole == TransferRole::kReceiver, PrepareStatusReport(StatusCode::kServerBadState));
- VerifyOrExit(mState == TransferState::kAwaitingAccept, PrepareStatusReport(StatusCode::kServerBadState));
+ VerifyOrExit(mRole == TransferRole::kReceiver, PrepareStatusReport(StatusCode::kUnexpectedMessage));
+ VerifyOrExit(mState == TransferState::kAwaitingAccept, PrepareStatusReport(StatusCode::kUnexpectedMessage));
err = rcvAcceptMsg.Parse(msgData.Retain());
VerifyOrExit(err == CHIP_NO_ERROR, PrepareStatusReport(StatusCode::kBadMessageContents));
CHIP_ERROR err = CHIP_NO_ERROR;
SendAccept sendAcceptMsg;
- VerifyOrExit(mRole == TransferRole::kSender, PrepareStatusReport(StatusCode::kServerBadState));
- VerifyOrExit(mState == TransferState::kAwaitingAccept, PrepareStatusReport(StatusCode::kServerBadState));
+ VerifyOrExit(mRole == TransferRole::kSender, PrepareStatusReport(StatusCode::kUnexpectedMessage));
+ VerifyOrExit(mState == TransferState::kAwaitingAccept, PrepareStatusReport(StatusCode::kUnexpectedMessage));
err = sendAcceptMsg.Parse(msgData.Retain());
VerifyOrExit(err == CHIP_NO_ERROR, PrepareStatusReport(StatusCode::kBadMessageContents));
CHIP_ERROR err = CHIP_NO_ERROR;
BlockQuery query;
- VerifyOrExit(mRole == TransferRole::kSender, PrepareStatusReport(StatusCode::kServerBadState));
- VerifyOrExit(mState == TransferState::kTransferInProgress, PrepareStatusReport(StatusCode::kServerBadState));
- VerifyOrExit(mAwaitingResponse, PrepareStatusReport(StatusCode::kServerBadState));
+ VerifyOrExit(mRole == TransferRole::kSender, PrepareStatusReport(StatusCode::kUnexpectedMessage));
+ VerifyOrExit(mState == TransferState::kTransferInProgress, PrepareStatusReport(StatusCode::kUnexpectedMessage));
+ VerifyOrExit(mAwaitingResponse, PrepareStatusReport(StatusCode::kUnexpectedMessage));
err = query.Parse(std::move(msgData));
VerifyOrExit(err == CHIP_NO_ERROR, PrepareStatusReport(StatusCode::kBadMessageContents));
CHIP_ERROR err = CHIP_NO_ERROR;
Block blockMsg;
- VerifyOrExit(mRole == TransferRole::kReceiver, PrepareStatusReport(StatusCode::kServerBadState));
- VerifyOrExit(mState == TransferState::kTransferInProgress, PrepareStatusReport(StatusCode::kServerBadState));
- VerifyOrExit(mAwaitingResponse, PrepareStatusReport(StatusCode::kServerBadState));
+ VerifyOrExit(mRole == TransferRole::kReceiver, PrepareStatusReport(StatusCode::kUnexpectedMessage));
+ VerifyOrExit(mState == TransferState::kTransferInProgress, PrepareStatusReport(StatusCode::kUnexpectedMessage));
+ VerifyOrExit(mAwaitingResponse, PrepareStatusReport(StatusCode::kUnexpectedMessage));
err = blockMsg.Parse(msgData.Retain());
VerifyOrExit(err == CHIP_NO_ERROR, PrepareStatusReport(StatusCode::kBadMessageContents));
CHIP_ERROR err = CHIP_NO_ERROR;
BlockEOF blockEOFMsg;
- VerifyOrExit(mRole == TransferRole::kReceiver, PrepareStatusReport(StatusCode::kServerBadState));
- VerifyOrExit(mState == TransferState::kTransferInProgress, PrepareStatusReport(StatusCode::kServerBadState));
- VerifyOrExit(mAwaitingResponse, PrepareStatusReport(StatusCode::kServerBadState));
+ VerifyOrExit(mRole == TransferRole::kReceiver, PrepareStatusReport(StatusCode::kUnexpectedMessage));
+ VerifyOrExit(mState == TransferState::kTransferInProgress, PrepareStatusReport(StatusCode::kUnexpectedMessage));
+ VerifyOrExit(mAwaitingResponse, PrepareStatusReport(StatusCode::kUnexpectedMessage));
err = blockEOFMsg.Parse(msgData.Retain());
VerifyOrExit(err == CHIP_NO_ERROR, PrepareStatusReport(StatusCode::kBadMessageContents));
CHIP_ERROR err = CHIP_NO_ERROR;
BlockAck ackMsg;
- VerifyOrExit(mRole == TransferRole::kSender, PrepareStatusReport(StatusCode::kServerBadState));
- VerifyOrExit(mState == TransferState::kTransferInProgress, PrepareStatusReport(StatusCode::kServerBadState));
- VerifyOrExit(mAwaitingResponse, PrepareStatusReport(StatusCode::kServerBadState));
+ VerifyOrExit(mRole == TransferRole::kSender, PrepareStatusReport(StatusCode::kUnexpectedMessage));
+ VerifyOrExit(mState == TransferState::kTransferInProgress, PrepareStatusReport(StatusCode::kUnexpectedMessage));
+ VerifyOrExit(mAwaitingResponse, PrepareStatusReport(StatusCode::kUnexpectedMessage));
err = ackMsg.Parse(std::move(msgData));
VerifyOrExit(err == CHIP_NO_ERROR, PrepareStatusReport(StatusCode::kBadMessageContents));
CHIP_ERROR err = CHIP_NO_ERROR;
BlockAckEOF ackMsg;
- VerifyOrExit(mRole == TransferRole::kSender, PrepareStatusReport(StatusCode::kServerBadState));
- VerifyOrExit(mState == TransferState::kAwaitingEOFAck, PrepareStatusReport(StatusCode::kServerBadState));
- VerifyOrExit(mAwaitingResponse, PrepareStatusReport(StatusCode::kServerBadState));
+ VerifyOrExit(mRole == TransferRole::kSender, PrepareStatusReport(StatusCode::kUnexpectedMessage));
+ VerifyOrExit(mState == TransferState::kAwaitingEOFAck, PrepareStatusReport(StatusCode::kUnexpectedMessage));
+ VerifyOrExit(mAwaitingResponse, PrepareStatusReport(StatusCode::kUnexpectedMessage));
err = ackMsg.Parse(std::move(msgData));
VerifyOrExit(err == CHIP_NO_ERROR, PrepareStatusReport(StatusCode::kBadMessageContents));
void TransferSession::PrepareStatusReport(StatusCode code)
{
- mStatusReportData.statusCode = code;
+ static_assert(std::is_same<std::underlying_type_t<decltype(code)>, uint16_t>::value, "Cast is not safe");
- Encoding::LittleEndian::PacketBufferWriter bbuf(chip::MessagePacketBuffer::New(kStatusReportMinSize), kStatusReportMinSize);
- VerifyOrReturn(!bbuf.IsNull());
+ mStatusReportData.statusCode = code;
- bbuf.Put16(static_cast<uint16_t>(Protocols::SecureChannel::GeneralStatusCode::kFailure));
- bbuf.Put32(Protocols::kProtocol_BDX);
- bbuf.Put16(static_cast<uint16_t>(mStatusReportData.statusCode));
+ Protocols::SecureChannel::StatusReport report(Protocols::SecureChannel::GeneralStatusCode::kFailure,
+ Protocols::BDX::Id.ToFullyQualifiedSpecForm(), static_cast<uint16_t>(code));
+ size_t msgSize = report.Size();
+ Encoding::LittleEndian::PacketBufferWriter bbuf(chip::MessagePacketBuffer::New(msgSize), msgSize);
+ VerifyOrExit(!bbuf.IsNull(), mPendingOutput = OutputEventType::kInternalError);
+ report.WriteToBuffer(bbuf);
mPendingMsgHandle = bbuf.Finalize();
if (mPendingMsgHandle.IsNull())
{
else
{
CHIP_ERROR err = AttachHeader(Protocols::SecureChannel::MsgType::StatusReport, mPendingMsgHandle);
- VerifyOrReturn(err == CHIP_NO_ERROR);
-
+ VerifyOrExit(err == CHIP_NO_ERROR, mPendingOutput = OutputEventType::kInternalError);
mPendingOutput = OutputEventType::kMsgToSend;
}
+exit:
mState = TransferState::kErrorState;
mAwaitingResponse = false; // Prevent triggering timeout
}
#include <core/CHIPTLV.h>
#include <protocols/secure_channel/Constants.h>
+#include <protocols/secure_channel/StatusReport.h>
#include <support/BufferReader.h>
#include <support/CHIPMem.h>
#include <support/CodeUtils.h>
-#include <support/ReturnMacros.h>
#include <support/UnitTestRegistration.h>
#include <system/SystemPacketBuffer.h>
using namespace ::chip;
using namespace ::chip::bdx;
+using namespace ::chip::Protocols;
namespace {
// Use this as a timestamp if not needing to test BDX timeouts.
// Helper method for verifying that a PacketBufferHandle contains a valid StatusReport message and contains a specific StatusCode.
void VerifyStatusReport(nlTestSuite * inSuite, void * inContext, const System::PacketBufferHandle & msg, StatusCode code)
{
- CHIP_ERROR err = CHIP_NO_ERROR;
- uint16_t headerSize = 0;
+ CHIP_ERROR err = CHIP_NO_ERROR;
PayloadHeader payloadHeader;
- uint16_t generalCode = 0;
- uint32_t protocolId = 0;
- BitFlags<StatusCode> protocolCode;
if (msg.IsNull())
{
return;
}
- err = payloadHeader.Decode(msg->Start(), msg->DataLength(), &headerSize);
- NL_TEST_ASSERT(inSuite, err == CHIP_NO_ERROR);
- NL_TEST_ASSERT(inSuite, payloadHeader.HasMessageType(Protocols::SecureChannel::MsgType::StatusReport));
- if (headerSize > msg->DataLength())
+ System::PacketBufferHandle msgCopy = msg.CloneData();
+ if (msgCopy.IsNull())
{
NL_TEST_ASSERT(inSuite, false);
return;
}
- Encoding::LittleEndian::Reader reader(msg->Start(), msg->DataLength());
- err = reader.Skip(headerSize).Read16(&generalCode).Read32(&protocolId).Read16(protocolCode.RawStorage()).StatusCode();
+ err = payloadHeader.DecodeAndConsume(msgCopy);
+ NL_TEST_ASSERT(inSuite, err == CHIP_NO_ERROR);
+ NL_TEST_ASSERT(inSuite, payloadHeader.HasMessageType(SecureChannel::MsgType::StatusReport));
+
+ SecureChannel::StatusReport report;
+ err = report.Parse(std::move(msgCopy));
NL_TEST_ASSERT(inSuite, err == CHIP_NO_ERROR);
- NL_TEST_ASSERT(inSuite, generalCode == static_cast<uint16_t>(Protocols::SecureChannel::GeneralStatusCode::kFailure));
- NL_TEST_ASSERT(inSuite, protocolId == Protocols::kProtocol_BDX);
- NL_TEST_ASSERT(inSuite, protocolCode == code);
+ NL_TEST_ASSERT(inSuite, report.GetGeneralCode() == SecureChannel::GeneralStatusCode::kFailure);
+ NL_TEST_ASSERT(inSuite, report.GetProtocolId() == Protocols::BDX::Id.ToFullyQualifiedSpecForm());
+ NL_TEST_ASSERT(inSuite, report.GetProtocolCode() == static_cast<uint16_t>(code));
}
void VerifyNoMoreOutput(nlTestSuite * inSuite, void * inContext, TransferSession & transferSession)
template <>
struct MessageTypeTraits<Echo::MsgType>
{
- static constexpr uint16_t ProtocolId = chip::Protocols::kProtocol_Echo;
+ static constexpr const Protocols::Id & ProtocolId() { return Echo::Id; }
};
} // namespace Protocols
template <>
struct MessageTypeTraits<InteractionModel::MsgType>
{
- static constexpr uint16_t ProtocolId = chip::Protocols::kProtocol_InteractionModel;
+ static constexpr const Protocols::Id & ProtocolId() { return InteractionModel::Id; }
};
} // namespace Protocols
--- /dev/null
+import("//build_overrides/chip.gni")
+
+static_library("secure_channel") {
+ output_name = "libSecureChannel"
+
+ sources = [
+ "StatusReport.cpp",
+ "StatusReport.h",
+ ]
+
+ cflags = [ "-Wconversion" ]
+
+ public_deps = [
+ "${chip_root}/src/lib/core",
+ "${chip_root}/src/lib/support",
+ "${chip_root}/src/system",
+ ]
+}
template <>
struct MessageTypeTraits<SecureChannel::MsgType>
{
- static constexpr uint16_t ProtocolId = chip::Protocols::kProtocol_SecureChannel;
+ static constexpr const Protocols::Id & ProtocolId() { return SecureChannel::Id; }
};
} // namespace Protocols
--- /dev/null
+/*
+ *
+ * Copyright (c) 2021 Project CHIP Authors
+ * All rights reserved.
+ *
+ * Licensed under the Apache License, Version 2.0 (the "License");
+ * you may not use this file except in compliance with the License.
+ * You may obtain a copy of the License at
+ *
+ * http://www.apache.org/licenses/LICENSE-2.0
+ *
+ * Unless required by applicable law or agreed to in writing, software
+ * distributed under the License is distributed on an "AS IS" BASIS,
+ * WITHOUT WARRANTIES OR CONDITIONS OF ANY KIND, either express or implied.
+ * See the License for the specific language governing permissions and
+ * limitations under the License.
+ */
+
+#include <protocols/secure_channel/Constants.h>
+#include <protocols/secure_channel/StatusReport.h>
+
+#include <support/BufferReader.h>
+#include <support/CodeUtils.h>
+
+#include <type_traits>
+
+using namespace chip::Encoding;
+using GeneralStatusCode = chip::Protocols::SecureChannel::GeneralStatusCode;
+
+namespace chip {
+namespace Protocols {
+namespace SecureChannel {
+
+StatusReport::StatusReport() : mGeneralCode(GeneralStatusCode::kSuccess), mProtocolId(0), mProtocolCode(0), mProtocolData(nullptr)
+{}
+
+StatusReport::StatusReport(GeneralStatusCode generalCode, uint32_t protocolId, uint16_t protocolCode) :
+ mGeneralCode(generalCode), mProtocolId(protocolId), mProtocolCode(protocolCode), mProtocolData(nullptr)
+{}
+
+StatusReport::StatusReport(GeneralStatusCode generalCode, uint32_t protocolId, uint16_t protocolCode,
+ System::PacketBufferHandle protocolData) :
+ mGeneralCode(generalCode),
+ mProtocolId(protocolId), mProtocolCode(protocolCode), mProtocolData(std::move(protocolData))
+{}
+
+CHIP_ERROR StatusReport::Parse(System::PacketBufferHandle buf)
+{
+ uint16_t tempGeneralCode = 0;
+
+ ReturnErrorCodeIf(buf.IsNull(), CHIP_ERROR_INVALID_ARGUMENT);
+
+ uint8_t * bufStart = buf->Start();
+ LittleEndian::Reader bufReader(bufStart, buf->DataLength());
+
+ ReturnErrorOnFailure(bufReader.Read16(&tempGeneralCode).Read32(&mProtocolId).Read16(&mProtocolCode).StatusCode());
+ mGeneralCode = static_cast<GeneralStatusCode>(tempGeneralCode);
+
+ // Any data that exists after the required fields is considered protocol-specific data.
+ if (bufReader.OctetsRead() < buf->DataLength())
+ {
+ mProtocolData = System::PacketBufferHandle::NewWithData(buf->Start() + bufReader.OctetsRead(),
+ buf->DataLength() - bufReader.OctetsRead(),
+ /* aAdditionalSize = */ 0, /* aReservedSize = */ 0);
+ if (mProtocolData.IsNull())
+ {
+ return CHIP_ERROR_NO_MEMORY;
+ }
+ }
+ else
+ {
+ mProtocolData = nullptr;
+ }
+
+ return CHIP_NO_ERROR;
+}
+
+Encoding::LittleEndian::BufferWriter & StatusReport::WriteToBuffer(Encoding::LittleEndian::BufferWriter & buf) const
+{
+ static_assert(std::is_same<std::underlying_type_t<decltype(mGeneralCode)>, uint16_t>::value, "Cast is not safe");
+ buf.Put16(static_cast<uint16_t>(mGeneralCode)).Put32(mProtocolId).Put16(mProtocolCode);
+ if (!mProtocolData.IsNull())
+ {
+ buf.Put(mProtocolData->Start(), mProtocolData->DataLength());
+ }
+ return buf;
+}
+
+size_t StatusReport::Size() const
+{
+ LittleEndian::BufferWriter emptyBuf(nullptr, 0);
+ return WriteToBuffer(emptyBuf).Needed();
+}
+
+} // namespace SecureChannel
+} // namespace Protocols
+} // namespace chip
--- /dev/null
+/*
+ *
+ * Copyright (c) 2021 Project CHIP Authors
+ * All rights reserved.
+ *
+ * Licensed under the Apache License, Version 2.0 (the "License");
+ * you may not use this file except in compliance with the License.
+ * You may obtain a copy of the License at
+ *
+ * http://www.apache.org/licenses/LICENSE-2.0
+ *
+ * Unless required by applicable law or agreed to in writing, software
+ * distributed under the License is distributed on an "AS IS" BASIS,
+ * WITHOUT WARRANTIES OR CONDITIONS OF ANY KIND, either express or implied.
+ * See the License for the specific language governing permissions and
+ * limitations under the License.
+ */
+
+#pragma once
+
+#include <support/BufferWriter.h>
+#include <system/SystemPacketBuffer.h>
+
+namespace chip {
+namespace Protocols {
+namespace SecureChannel {
+
+/**
+ * Encapsulates the data included in a StatusReport message, and provides methods for writing to and reading from PacketBuffers
+ * that contain StatusReport messages.
+ */
+class DLL_EXPORT StatusReport
+{
+public:
+ /**
+ * Construct a StatusReport with zero-d out fields (for use before calling \c Parse() ).
+ */
+ StatusReport();
+
+ /**
+ * Construct a StatusReport with no additional ProtocolData.
+ *
+ * @param generalCode Required, one of the \c GeneralStatusCode values listed in \c secure_channel/Constants.h
+ * @param protocolId Must specify a ProtocolId which consists of Vendor Id (upper 16 bits) and ProtocolId (lower 16 bits)
+ * @param protocolCode A code defined by the specified protocol which provides more information about the status
+ */
+ StatusReport(GeneralStatusCode generalCode, uint32_t protocolId, uint16_t protocolCode);
+
+ //
+ /**
+ * Construct a StatusReport with additional ProtocolData.
+ *
+ * @param generalCode Must specify a GeneralCode (see \c GeneralStatusCode )
+ * @param protocolId Must specify a ProtocolId which consists of Vendor Id (upper 16 bits) and ProtocolId (lower 16 bits)
+ * @param protocolCode A code defined by the specified protocol which provides more information about the status
+ * @param protocolData A \c PacketBufferHandle containing the protocol-specific data
+ */
+ StatusReport(GeneralStatusCode generalCode, uint32_t protocolId, uint16_t protocolCode,
+ System::PacketBufferHandle protocolData);
+
+ /**
+ * Read the contents of a \c PacketBuffer containing a StatusReport message and store the field values in this object.
+ *
+ * @note If there is additional data after the Protocol Code field in the message, it is assumed to be protocol-specific data.
+ *
+ * @note This method assumes that the Header of the message has already been consumed, and that \c PacketBuffer::Start() points
+ * to the beginning of the StatusReport data.
+ *
+ * @param[in] buf A \c PacketBufferHandle containing the StatusReport message. This method will take ownership, and will
+ * allocate a new PacketBuffer if any protocol-specific data exists.
+ *
+ * @return CHIP_ERROR Return an error if the message is malformed or buf is \c NULL
+ */
+ CHIP_ERROR Parse(System::PacketBufferHandle buf);
+
+ /**
+ * Write the StatusReport contents into a buffer using a \c BufferWriter
+ *
+ * @param[out] buf A \c BufferWriter which contains the buffer that will store the message fields.
+ *
+ * @return BufferWriter Return a reference to the \c BufferWriter
+ */
+ Encoding::LittleEndian::BufferWriter & WriteToBuffer(Encoding::LittleEndian::BufferWriter & buf) const;
+
+ /**
+ * Returns the minimum size of the buffer needed to write the message.
+ */
+ size_t Size() const;
+
+ GeneralStatusCode GetGeneralCode() const { return mGeneralCode; }
+ uint32_t GetProtocolId() const { return mProtocolId; }
+ uint16_t GetProtocolCode() const { return mProtocolCode; }
+ const System::PacketBufferHandle & GetProtocolData() const { return mProtocolData; }
+
+private:
+ GeneralStatusCode mGeneralCode;
+ uint32_t mProtocolId;
+ uint16_t mProtocolCode;
+
+ System::PacketBufferHandle mProtocolData;
+};
+
+} // namespace SecureChannel
+} // namespace Protocols
+} // namespace chip
--- /dev/null
+import("//build_overrides/build.gni")
+import("//build_overrides/chip.gni")
+import("//build_overrides/nlio.gni")
+import("//build_overrides/nlunit_test.gni")
+
+import("${chip_root}/build/chip/chip_test_suite.gni")
+
+chip_test_suite("tests") {
+ output_name = "libSecureChannelTests"
+
+ test_sources = [ "TestStatusReport.cpp" ]
+
+ public_deps = [
+ "${chip_root}/src/lib/core",
+ "${chip_root}/src/lib/support",
+ "${chip_root}/src/protocols/secure_channel",
+ "${nlio_root}:nlio",
+ "${nlunit_test_root}:nlunit-test",
+ ]
+
+ cflags = [ "-Wconversion" ]
+}
--- /dev/null
+/*
+ *
+ * Copyright (c) 2021 Project CHIP Authors
+ * All rights reserved.
+ *
+ * Licensed under the Apache License, Version 2.0 (the "License");
+ * you may not use this file except in compliance with the License.
+ * You may obtain a copy of the License at
+ *
+ * http://www.apache.org/licenses/LICENSE-2.0
+ *
+ * Unless required by applicable law or agreed to in writing, software
+ * distributed under the License is distributed on an "AS IS" BASIS,
+ * WITHOUT WARRANTIES OR CONDITIONS OF ANY KIND, either express or implied.
+ * See the License for the specific language governing permissions and
+ * limitations under the License.
+ */
+
+#include <protocols/Protocols.h>
+#include <protocols/secure_channel/Constants.h>
+#include <protocols/secure_channel/StatusReport.h>
+#include <support/BufferWriter.h>
+#include <support/CHIPMem.h>
+#include <support/UnitTestRegistration.h>
+#include <system/SystemPacketBuffer.h>
+
+#include <nlunit-test.h>
+
+using namespace chip;
+using namespace chip::Protocols;
+using namespace chip::Protocols::SecureChannel;
+
+void TestStatusReport_NoData(nlTestSuite * inSuite, void * inContext)
+{
+ GeneralStatusCode generalCode = GeneralStatusCode::kSuccess;
+ uint32_t protocolId = SecureChannel::Id.ToFullyQualifiedSpecForm();
+ uint16_t protocolCode = kProtocolCodeSuccess;
+
+ StatusReport testReport(generalCode, protocolId, protocolCode);
+
+ size_t msgSize = testReport.Size();
+ Encoding::LittleEndian::PacketBufferWriter bbuf(System::PacketBufferHandle::New(msgSize));
+ testReport.WriteToBuffer(bbuf);
+
+ System::PacketBufferHandle msgBuf = bbuf.Finalize();
+ NL_TEST_ASSERT(inSuite, !msgBuf.IsNull());
+
+ StatusReport reportToParse;
+ CHIP_ERROR err = reportToParse.Parse(std::move(msgBuf));
+ NL_TEST_ASSERT(inSuite, err == CHIP_NO_ERROR);
+ NL_TEST_ASSERT(inSuite, reportToParse.GetGeneralCode() == generalCode);
+ NL_TEST_ASSERT(inSuite, reportToParse.GetProtocolId() == protocolId);
+ NL_TEST_ASSERT(inSuite, reportToParse.GetProtocolCode() == protocolCode);
+
+ const System::PacketBufferHandle & data = reportToParse.GetProtocolData();
+ NL_TEST_ASSERT(inSuite, data.IsNull());
+}
+
+void TestStatusReport_WithData(nlTestSuite * inSuite, void * inContext)
+{
+ GeneralStatusCode generalCode = GeneralStatusCode::kFailure;
+ uint32_t protocolId = SecureChannel::Id.ToFullyQualifiedSpecForm();
+ uint16_t protocolCode = static_cast<uint16_t>(StatusCode::InvalidFabricConfig);
+ uint8_t data[6] = { 42, 19, 3, 1, 3, 0 };
+ const uint16_t dataLen = 6;
+ System::PacketBufferHandle dataBuf = System::PacketBufferHandle::NewWithData(data, dataLen);
+
+ StatusReport testReport(generalCode, protocolId, protocolCode, std::move(dataBuf));
+
+ size_t msgSize = testReport.Size();
+ Encoding::LittleEndian::PacketBufferWriter bbuf(System::PacketBufferHandle::New(msgSize));
+ testReport.WriteToBuffer(bbuf);
+
+ System::PacketBufferHandle msgBuf = bbuf.Finalize();
+ NL_TEST_ASSERT(inSuite, !msgBuf.IsNull());
+
+ StatusReport reportToParse;
+ CHIP_ERROR err = reportToParse.Parse(std::move(msgBuf));
+ NL_TEST_ASSERT(inSuite, err == CHIP_NO_ERROR);
+ NL_TEST_ASSERT(inSuite, reportToParse.GetGeneralCode() == generalCode);
+ NL_TEST_ASSERT(inSuite, reportToParse.GetProtocolId() == protocolId);
+ NL_TEST_ASSERT(inSuite, reportToParse.GetProtocolCode() == protocolCode);
+
+ const System::PacketBufferHandle & rcvData = reportToParse.GetProtocolData();
+ if (rcvData.IsNull())
+ {
+ NL_TEST_ASSERT(inSuite, false);
+ return;
+ }
+ NL_TEST_ASSERT(inSuite, rcvData->DataLength() == dataLen);
+ NL_TEST_ASSERT(inSuite, !memcmp(rcvData->Start(), data, dataLen));
+}
+
+void TestBadStatusReport(nlTestSuite * inSuite, void * inContext)
+{
+ StatusReport report;
+ System::PacketBufferHandle badMsg = System::PacketBufferHandle::New(10);
+ CHIP_ERROR err = report.Parse(std::move(badMsg));
+ NL_TEST_ASSERT(inSuite, err != CHIP_NO_ERROR);
+
+ StatusReport report2;
+ badMsg = nullptr;
+ err = report2.Parse(std::move(badMsg));
+ NL_TEST_ASSERT(inSuite, err != CHIP_NO_ERROR);
+}
+
+// Test Suite
+
+/**
+ * Test Suite that lists all the test functions.
+ */
+// clang-format off
+static const nlTest sTests[] =
+{
+ NL_TEST_DEF("TestStatusReport_NoData", TestStatusReport_NoData),
+ NL_TEST_DEF("TestStatusReport_WithData", TestStatusReport_WithData),
+ NL_TEST_DEF("TestBadStatusReport", TestBadStatusReport),
+
+ NL_TEST_SENTINEL()
+};
+// clang-format on
+
+/**
+ * Set up the test suite.
+ */
+static int TestSetup(void * inContext)
+{
+ CHIP_ERROR error = chip::Platform::MemoryInit();
+ if (error != CHIP_NO_ERROR)
+ return FAILURE;
+ return SUCCESS;
+}
+
+/**
+ * Tear down the test suite.
+ */
+static int TestTeardown(void * inContext)
+{
+ chip::Platform::MemoryShutdown();
+ return SUCCESS;
+}
+
+// clang-format off
+static nlTestSuite sSuite =
+{
+ "Test-CHIP-StatusReport",
+ &sTests[0],
+ TestSetup,
+ TestTeardown,
+};
+// clang-format on
+
+/**
+ * Main
+ */
+int TestStatusReport()
+{
+ // Run test suit against one context
+ nlTestRunner(&sSuite, nullptr);
+
+ return (nlTestRunnerStats(&sSuite));
+}
+
+CHIP_REGISTER_TEST_SUITE(TestStatusReport)
#include <protocols/Protocols.h>
#include <support/CodeUtils.h>
#include <support/RandUtils.h>
-#include <support/ReturnMacros.h>
#include <support/SafeInt.h>
#include <support/ScopedBuffer.h>
return PacketBufferHandle(head);
}
-PacketBufferHandle PacketBufferHandle::CloneData()
+PacketBufferHandle PacketBufferHandle::CloneData() const
{
PacketBufferHandle cloneHead;
*
* @returns empty handle on allocation failure. Otherwise, the returned buffer has the same sizes and contents as the original.
*/
- PacketBufferHandle CloneData();
+ PacketBufferHandle CloneData() const;
/**
* Perform an implementation-defined check on the validity of a PacketBufferHandle.
#include <core/CHIPEncoding.h>
#include <support/CHIPMem.h>
-#include <support/ReturnMacros.h>
#include <support/SafeInt.h>
#include <transport/AdminPairingTable.h>
#include <transport/BLE.h>
#include <support/CodeUtils.h>
-#include <support/ReturnMacros.h>
#include <support/logging/CHIPLogging.h>
#include <transport/raw/MessageHeader.h>
#include <protocols/Protocols.h>
#include <support/CHIPMem.h>
#include <support/CodeUtils.h>
-#include <support/ReturnMacros.h>
#include <support/SafeInt.h>
#include <transport/SecureSessionMgr.h>
err = payloadHeader.DecodeAndConsume(msg);
SuccessOrExit(err);
- VerifyOrExit(payloadHeader.GetProtocolID() == Protocols::kProtocol_SecureChannel, err = CHIP_ERROR_INVALID_MESSAGE_TYPE);
+ VerifyOrExit(payloadHeader.HasProtocol(Protocols::SecureChannel::Id), err = CHIP_ERROR_INVALID_MESSAGE_TYPE);
msgType = static_cast<Protocols::SecureChannel::MsgType>(payloadHeader.GetMessageType());
VerifyOrExit(msgType == mNextExpectedMsg, err = CHIP_ERROR_INVALID_MESSAGE_TYPE);
VerifyOrExit(mDelegate != nullptr, err = CHIP_ERROR_INCORRECT_STATE);
VerifyOrExit(addrStr != nullptr, err = CHIP_ERROR_INVALID_ADDRESS);
- err = mDelegate->SendSecureMessage(Protocols::kProtocol_NetworkProvisioning, NetworkProvisioning::MsgTypes::kIPAddressAssigned,
+ err = mDelegate->SendSecureMessage(Protocols::NetworkProvisioning::Id, NetworkProvisioning::MsgTypes::kIPAddressAssigned,
std::move(buffer));
SuccessOrExit(err);
SuccessOrExit(EncodeString(passwd, bbuf));
VerifyOrExit(bbuf.Fit(), err = CHIP_ERROR_BUFFER_TOO_SMALL);
- err = mDelegate->SendSecureMessage(Protocols::kProtocol_NetworkProvisioning,
+ err = mDelegate->SendSecureMessage(Protocols::NetworkProvisioning::Id,
NetworkProvisioning::MsgTypes::kWiFiAssociationRequest, bbuf.Finalize());
SuccessOrExit(err);
}
bbuf.Put(static_cast<uint8_t>(threadData.FieldPresent.ThreadPSKc));
VerifyOrExit(bbuf.Fit(), err = CHIP_ERROR_BUFFER_TOO_SMALL);
- err = mDelegate->SendSecureMessage(Protocols::kProtocol_NetworkProvisioning,
- NetworkProvisioning::MsgTypes::kThreadAssociationRequest, bbuf.Finalize());
+ err = mDelegate->SendSecureMessage(Protocols::NetworkProvisioning::Id, NetworkProvisioning::MsgTypes::kThreadAssociationRequest,
+ bbuf.Finalize());
exit:
if (CHIP_NO_ERROR != err)
* @param msgBuf the new message that should be sent to the peer
* @return CHIP_ERROR Error thrown when sending the message
*/
- virtual CHIP_ERROR SendSecureMessage(Protocols::CHIPProtocolId protocol, uint8_t msgType, System::PacketBufferHandle msgBuf)
+ virtual CHIP_ERROR SendSecureMessage(Protocols::Id protocol, uint8_t msgType, System::PacketBufferHandle msgBuf)
{
return CHIP_NO_ERROR;
}
#include <core/CHIPEncoding.h>
#include <core/CHIPSafeCasts.h>
#include <protocols/Protocols.h>
+#include <protocols/secure_channel/Constants.h>
#include <setup_payload/SetupPayload.h>
#include <support/BufferWriter.h>
#include <support/CHIPMem.h>
#include <support/CodeUtils.h>
-#include <support/ReturnMacros.h>
#include <support/SafeInt.h>
#include <transport/SecureSessionMgr.h>
err = payloadHeader.DecodeAndConsume(msg);
SuccessOrExit(err);
- VerifyOrExit(payloadHeader.GetProtocolID() == Protocols::kProtocol_SecureChannel, err = CHIP_ERROR_INVALID_MESSAGE_TYPE);
- VerifyOrExit(payloadHeader.GetMessageType() == (uint8_t) mNextExpectedMsg, err = CHIP_ERROR_INVALID_MESSAGE_TYPE);
+ VerifyOrExit(payloadHeader.HasMessageType(mNextExpectedMsg), err = CHIP_ERROR_INVALID_MESSAGE_TYPE);
mConnectionState.SetPeerAddress(peerAddress);
#include <support/CHIPMem.h>
#include <support/CodeUtils.h>
#include <support/ErrorStr.h>
-#include <support/ReturnMacros.h>
#include <support/SafeInt.h>
#include <transport/RendezvousSession.h>
#include <transport/SecureMessageCodec.h>
}
}
-CHIP_ERROR RendezvousSession::SendSecureMessage(Protocols::CHIPProtocolId protocol, uint8_t msgType,
- System::PacketBufferHandle msgBuf)
+CHIP_ERROR RendezvousSession::SendSecureMessage(Protocols::Id protocol, uint8_t msgType, System::PacketBufferHandle msgBuf)
{
VerifyOrReturnError(mPairingSessionHandle != nullptr, CHIP_ERROR_INCORRECT_STATE);
PayloadHeader payloadHeader;
- payloadHeader.SetMessageType(static_cast<uint16_t>(protocol), msgType);
+ payloadHeader.SetMessageType(protocol, msgType);
return mSecureSessionMgr->SendMessage(*mPairingSessionHandle, payloadHeader, std::move(msgBuf));
}
mParams.SetRemoteNodeId(packetHeader.GetSourceNodeId().Value());
}
- if (payloadHeader.GetProtocolID() == Protocols::kProtocol_NetworkProvisioning)
+ if (payloadHeader.HasProtocol(Protocols::NetworkProvisioning::Id))
{
ReturnErrorOnFailure(mNetworkProvision.HandleNetworkProvisioningMessage(payloadHeader.GetMessageType(), msgBuf));
}
void SendOperationalCredentials() override;
//////////// NetworkProvisioningDelegate Implementation ///////////////
- CHIP_ERROR SendSecureMessage(Protocols::CHIPProtocolId protocol, uint8_t msgType, System::PacketBufferHandle msgBug) override;
+ CHIP_ERROR SendSecureMessage(Protocols::Id protocol, uint8_t msgType, System::PacketBufferHandle msgBug) override;
void OnNetworkProvisioningError(CHIP_ERROR error) override;
void OnNetworkProvisioningComplete() override;
*/
#include <support/CodeUtils.h>
-#include <support/ReturnMacros.h>
#include <support/SafeInt.h>
#include <transport/SecureMessageCodec.h>
#include <core/CHIPEncoding.h>
#include <support/BufferWriter.h>
#include <support/CodeUtils.h>
-#include <support/ReturnMacros.h>
#include <transport/SecureSession.h>
#include <transport/raw/MessageHeader.h>
#include <core/CHIPKeyIds.h>
#include <platform/CHIPDeviceLayer.h>
#include <support/CodeUtils.h>
-#include <support/ReturnMacros.h>
#include <support/SafeInt.h>
#include <support/logging/CHIPLogging.h>
#include <transport/AdminPairingTable.h>
*/
#include <core/CHIPEncoding.h>
-#include <support/ReturnMacros.h>
#include <support/SafeInt.h>
#include <transport/StorablePeerConnection.h>
#include <core/CHIPError.h>
#include <support/BufferReader.h>
#include <support/CodeUtils.h>
-#include <support/ReturnMacros.h>
/**********************************************
* Header format (little endian):
class PayloadHeader
{
public:
+ constexpr PayloadHeader() { SetProtocol(Protocols::NotSpecified); }
PayloadHeader & operator=(const PayloadHeader &) = default;
/**
uint16_t GetExchangeID() const { return mExchangeID; }
/** Get the Protocol ID from this header. */
+ // TODO: We should probably get rid of GetProtocolId and the
+ // current form of the mVendorId accessors.
uint16_t GetProtocolID() const { return mProtocolID; }
+ /** Check whether the header has a given protocol */
+ bool HasProtocol(Protocols::Id protocol) const
+ {
+ static_assert(std::is_same<std::underlying_type_t<VendorId>, uint16_t>::value, "Wrong type for VendorId");
+ return mProtocolID == protocol.GetProtocolId() && mVendorId.ValueOr(VendorId::Common) == protocol.GetVendorId();
+ }
+
/** Get the secure msg type from this header. */
uint8_t GetMessageType() const { return mMessageType; }
bool HasMessageType(MessageType type) const
{
static_assert(std::is_same<std::underlying_type_t<MessageType>, uint8_t>::value, "Enum is wrong size; cast is not safe");
- return mProtocolID == Protocols::MessageTypeTraits<MessageType>::ProtocolId && HasMessageType(static_cast<uint8_t>(type));
+ return HasProtocol(Protocols::MessageTypeTraits<MessageType>::ProtocolId()) && HasMessageType(static_cast<uint8_t>(type));
}
/**
}
/** Set the vendor id for this header. */
- PayloadHeader & SetVendorId(Optional<uint16_t> id)
+ constexpr PayloadHeader & SetVendorId(Optional<uint16_t> id)
{
mVendorId = id;
mExchangeFlags.Set(Header::ExFlagValues::kExchangeFlag_VendorIdPresent, id.HasValue());
}
/** Clear the vendor id for this header. */
- PayloadHeader & ClearVendorId()
+ constexpr PayloadHeader & ClearVendorId()
{
mVendorId.ClearValue();
+ mExchangeFlags.Clear(Header::ExFlagValues::kExchangeFlag_VendorIdPresent);
return *this;
}
* message type and hence can't automatically determine the protocol from
* the message type.
*/
- PayloadHeader & SetMessageType(uint16_t protocol, uint8_t type)
+ PayloadHeader & SetMessageType(Protocols::Id protocol, uint8_t type)
{
- mProtocolID = protocol;
+ SetProtocol(protocol);
mMessageType = type;
return *this;
}
PayloadHeader & SetMessageType(MessageType type)
{
static_assert(std::is_same<std::underlying_type_t<MessageType>, uint8_t>::value, "Enum is wrong size; cast is not safe");
- mMessageType = static_cast<uint8_t>(type);
- mProtocolID = Protocols::MessageTypeTraits<MessageType>::ProtocolId;
+ SetMessageType(Protocols::MessageTypeTraits<MessageType>::ProtocolId(), static_cast<uint8_t>(type));
return *this;
}
}
private:
+ constexpr void SetProtocol(Protocols::Id protocol)
+ {
+ if (protocol.GetVendorId() == VendorId::Common)
+ {
+ ClearVendorId();
+ }
+ else
+ {
+ SetVendorId(protocol.GetVendorId());
+ }
+ mProtocolID = protocol.GetProtocolId();
+ }
+
/// Packet type (application data, security control packets, e.g. pairing,
/// configuration, rekey etc)
uint8_t mMessageType = 0;
Optional<uint16_t> mVendorId;
/// Protocol identifier
- uint16_t mProtocolID = static_cast<uint16_t>(Protocols::kProtocol_NotSpecified);
+ uint16_t mProtocolID = 0xFFFF;
/// Bit flag indicators for CHIP Exchange header
Header::ExFlags mExchangeFlags;
#include <core/CHIPEncoding.h>
#include <support/CodeUtils.h>
-#include <support/ReturnMacros.h>
#include <support/logging/CHIPLogging.h>
#include <transport/raw/MessageHeader.h>
// Packets start with a 16-bit size
constexpr size_t kPacketSizeBytes = 2;
+// TODO: Actual limit may be lower (spec issue #2119)
+constexpr uint16_t kMaxMessageSize = static_cast<uint16_t>(System::PacketBuffer::kMaxSizeWithoutReserve - kPacketSizeBytes);
+
constexpr int kListenBacklogSize = 2;
} // namespace
VerifyOrReturnError(state != nullptr, CHIP_ERROR_INTERNAL);
state->mReceived.AddToEnd(std::move(buffer));
- if (state->mDiscardSize != 0)
- {
- CHIP_ERROR err = state->Discard();
- if ((err != CHIP_NO_ERROR) || (state->mDiscardSize != 0))
- {
- return err;
- }
- }
-
while (!state->mReceived.IsNull())
{
uint8_t messageSizeBuf[kPacketSizeBytes];
return err;
}
uint16_t messageSize = LittleEndian::Get16(messageSizeBuf);
- if (messageSize >= System::PacketBuffer::kMaxSizeWithoutReserve)
+ if (messageSize >= kMaxMessageSize)
{
- // This message is too long for upper layers, which require a contiguous buffer.
- // TODO: Actual limit may be lower (spec issue #2119)
- state->mReceived.Consume(kPacketSizeBytes);
- state->mDiscardSize = messageSize;
- ReturnErrorOnFailure(state->Discard());
+ // This message is too long for upper layers.
return CHIP_ERROR_MESSAGE_TOO_LONG;
}
// The subtraction will not underflow because we successfully read kPacketSizeBytes.
return CHIP_NO_ERROR;
}
-void TCPBase::OnTcpReceive(Inet::TCPEndPoint * endPoint, System::PacketBufferHandle buffer)
+INET_ERROR TCPBase::OnTcpReceive(Inet::TCPEndPoint * endPoint, System::PacketBufferHandle buffer)
{
Inet::IPAddress ipAddress;
uint16_t port;
if (err != CHIP_NO_ERROR)
{
// Connection could need to be closed at this point
- ChipLogError(Inet, "Failed to handle received TCP message: %s", ErrorStr(err));
+ ChipLogError(Inet, "Failed to accept received TCP message: %s", ErrorStr(err));
+ return INET_ERROR_UNEXPECTED_EVENT;
}
+ return INET_NO_ERROR;
}
void TCPBase::OnConnectionComplete(Inet::TCPEndPoint * endPoint, INET_ERROR inetErr)
#include <inet/InetInterface.h>
#include <inet/TCPEndPoint.h>
#include <support/CodeUtils.h>
-#include <support/ReturnMacros.h>
#include <transport/raw/Base.h>
namespace chip {
{
void Init(Inet::TCPEndPoint * endPoint)
{
- mEndPoint = endPoint;
- mReceived = nullptr;
- mDiscardSize = 0;
+ mEndPoint = endPoint;
+ mReceived = nullptr;
}
void Free()
{
mEndPoint->Free();
- mEndPoint = nullptr;
- mReceived = nullptr;
- mDiscardSize = 0;
+ mEndPoint = nullptr;
+ mReceived = nullptr;
}
bool InUse() const { return mEndPoint != nullptr; }
// Buffers received but not yet consumed.
System::PacketBufferHandle mReceived;
-
- // Length of incoming data that must be discard to resynchronize.
- // TODO: This can be removed once issue #5438 guarantees that the
- // connection is closed on any error.
- uint16_t mDiscardSize;
- CHIP_ERROR Discard()
- {
- VerifyOrReturnError((mDiscardSize != 0) && !mReceived.IsNull(), CHIP_NO_ERROR);
- uint16_t initialLength = mReceived->TotalLength();
- mReceived.Consume(mDiscardSize);
- uint16_t remainingLength = mReceived.IsNull() ? 0 : mReceived->TotalLength();
- VerifyOrReturnError(remainingLength <= initialLength, CHIP_ERROR_INTERNAL);
- uint16_t discardedLength = static_cast<uint16_t>(initialLength - remainingLength);
- VerifyOrReturnError(discardedLength <= mDiscardSize, CHIP_ERROR_INTERNAL);
- mDiscardSize = static_cast<uint16_t>(mDiscardSize - discardedLength);
- return CHIP_NO_ERROR;
- }
};
public:
// Callback handler for TCPEndPoint. TCP message receive handler.
// @see TCPEndpoint::OnDataReceivedFunct
- static void OnTcpReceive(Inet::TCPEndPoint * endPoint, System::PacketBufferHandle buffer);
+ static INET_ERROR OnTcpReceive(Inet::TCPEndPoint * endPoint, System::PacketBufferHandle buffer);
// Callback handler for TCPEndPoint. Called when a connection has been completed.
// @see TCPEndpoint::OnConnectCompleteFunct
#include <transport/raw/UDP.h>
#include <support/CodeUtils.h>
-#include <support/ReturnMacros.h>
#include <support/logging/CHIPLogging.h>
#include <transport/raw/MessageHeader.h>
* the Message Header class within the transport layer
*
*/
+#include <protocols/Protocols.h>
#include <support/CodeUtils.h>
#include <support/ErrorStr.h>
#include <support/UnitTestRegistration.h>
NL_TEST_ASSERT(inSuite, header.GetMessageType() == 0);
NL_TEST_ASSERT(inSuite, header.GetExchangeID() == 0);
- NL_TEST_ASSERT(inSuite, header.GetProtocolID() == static_cast<uint16_t>(Protocols::kProtocol_NotSpecified));
- NL_TEST_ASSERT(inSuite, !header.GetVendorId().HasValue());
+ NL_TEST_ASSERT(inSuite, header.HasProtocol(Protocols::NotSpecified));
}
void TestPacketHeaderEncodeDecode(nlTestSuite * inSuite, void * inContext)
uint16_t encodeLen;
uint16_t decodeLen;
- header.SetMessageType(0, 112).SetExchangeID(2233);
+ header.SetMessageType(Protocols::Id(VendorId::Common, 0), 112).SetExchangeID(2233);
NL_TEST_ASSERT(inSuite, !header.GetVendorId().HasValue());
- header.SetMessageType(1221, 112).SetExchangeID(2233).SetInitiator(true);
+ header.SetMessageType(Protocols::Id(VendorId::Common, 1221), 112).SetExchangeID(2233).SetInitiator(true);
NL_TEST_ASSERT(inSuite, header.Encode(buffer, &encodeLen) == CHIP_NO_ERROR);
- header.SetMessageType(4567, 221).SetExchangeID(3322);
+ header.SetMessageType(Protocols::Id(VendorId::Common, 4567), 221).SetExchangeID(3322);
NL_TEST_ASSERT(inSuite, header.Decode(buffer, &decodeLen) == CHIP_NO_ERROR);
NL_TEST_ASSERT(inSuite, encodeLen == decodeLen);
NL_TEST_ASSERT(inSuite, header.GetMessageType() == 112);
NL_TEST_ASSERT(inSuite, !header.GetVendorId().HasValue());
NL_TEST_ASSERT(inSuite, header.IsInitiator());
- header.SetMessageType(1221, 112).SetExchangeID(2233);
+ header.SetMessageType(Protocols::Id(VendorId::Common, 1221), 112).SetExchangeID(2233);
header.SetVendorId(6789);
NL_TEST_ASSERT(inSuite, header.Encode(buffer, &encodeLen) == CHIP_NO_ERROR);
- header.SetMessageType(0, 111).SetExchangeID(222);
+ header.SetMessageType(Protocols::Id(VendorId::Common, 0), 111).SetExchangeID(222);
NL_TEST_ASSERT(inSuite, header.Decode(buffer, &decodeLen) == CHIP_NO_ERROR);
NL_TEST_ASSERT(inSuite, encodeLen == decodeLen);
NL_TEST_ASSERT(inSuite, header.GetExchangeID() == 2233);
NL_TEST_ASSERT(inSuite, header.GetVendorId() == Optional<uint16_t>::Value(6789));
- header.SetMessageType(4567, 221).SetExchangeID(3322);
+ header.SetMessageType(Protocols::Id(VendorId::Common, 4567), 221).SetExchangeID(3322);
header.SetVendorId(8976);
NL_TEST_ASSERT(inSuite, header.Decode(buffer, &decodeLen) == CHIP_NO_ERROR);
int TestDataCallbackCheck(const uint8_t * message, size_t length, int count, void * data)
{
- printf("--> callback %p %zu %d %p\n", message, length, count, data);
if (data == nullptr)
{
- printf(" -> callback data null\n");
return -1;
}
TestData * currentData = static_cast<TestData *>(data) + count;
- printf(" -> payload %p total=%zu message=%zu\n", currentData->mPayload, currentData->mTotalLength, currentData->mMessageLength);
if (currentData->mPayload == nullptr)
{
- printf(" -> payload null\n");
return -2;
}
if (currentData->mMessageLength != length)
{
- printf(" -> length expect %zu got %zu\n", currentData->mMessageLength, length);
return -3;
}
if (memcmp(currentData->mPayload + currentData->mMessageOffset, message, length) != 0)
{
- printf(" -> payload mismatch\n");
return -4;
}
return 0;
NL_TEST_ASSERT(inSuite, err == CHIP_NO_ERROR);
NL_TEST_ASSERT(inSuite, gMockTransportMgrDelegate.mReceiveHandlerCallCount == 2);
- // Test a chain that is too large to coalesce into a single packet buffer, followed by a normal message.
- // We expect to receive only the latter.
+ // Test a message that is too large to coalesce into a single packet buffer.
gMockTransportMgrDelegate.mReceiveHandlerCallCount = 0;
gMockTransportMgrDelegate.SetCallback(TestDataCallbackCheck, &testData[1]);
NL_TEST_ASSERT(inSuite, testData[0].Init((const uint16_t[]){ 51, System::PacketBuffer::kMaxSizeWithoutReserve, 0 }));
- NL_TEST_ASSERT(inSuite, testData[1].Init((const uint16_t[]){ 153, 154, 0 }));
- testData[0].mHandle->AddToEnd(std::move(testData[1].mHandle));
- // Start by sending only the first buffer of the long chain. This should be enough to trigger the error.
+ // Sending only the first buffer of the long chain. This should be enough to trigger the error.
System::PacketBufferHandle head = testData[0].mHandle.PopHead();
err = tcp.ProcessReceivedBuffer(lEndPoint, lPeerAddress, std::move(head));
NL_TEST_ASSERT(inSuite, err == CHIP_ERROR_MESSAGE_TOO_LONG);
NL_TEST_ASSERT(inSuite, gMockTransportMgrDelegate.mReceiveHandlerCallCount == 0);
- // Now send the rest, confirming that the second message arrives.
- err = tcp.ProcessReceivedBuffer(lEndPoint, lPeerAddress, std::move(testData[0].mHandle));
- NL_TEST_ASSERT(inSuite, err == CHIP_NO_ERROR);
- NL_TEST_ASSERT(inSuite, gMockTransportMgrDelegate.mReceiveHandlerCallCount == 1);
gMockTransportMgrDelegate.FinalizeMessageTest(tcp, addr);
}
#include <protocols/Protocols.h>
#include <protocols/echo/Echo.h>
#include <support/CodeUtils.h>
-#include <support/ReturnMacros.h>
#include <support/UnitTestRegistration.h>
#include <transport/SecureSessionMgr.h>
#include <transport/TransportMgr.h>